Cyberwarfare & Social Engineering
Explore Social Engineering
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Apr 08 2024
Apr 08 2024
Malware Data Science: Attack Detection and Attribution
The open-source XZ Utils compression utility has been backdoored by a skilled threat actor who tried to get the malicious packages included in mainstream Linux distributions, to allow them unfettered, covert SSH access to Linux systems around the world.
“The author intentionally obfuscated the backdoor in distribution tarballs, intended for Linux distributions to use for building their packages. When the xz build system is instructed to create an RPM or DEB for the x86-64 architecture using gcc and gnu linker, the backdoor is included in the liblzma as part of the build process. This backdoor is then shipped as part of the binary within the RPM or DEB,” the Open Source Security Foundation succinctly explained.
The backdoor was discovered by Andres Freund, a software engineer at Microsoft, and its existence was publicly revealed a little over a week ago. Stable versions of a few Linux distros have been affected but widespread compromise has been avoided.
Threat researchers are still working on analyzing the backdoor and are revealing their findings daily.
It has become clear that is the work of a sophisticated threat actor who used many tricks to:
Triggering/using the backdoor requires authentication via a private SSH key owned by the attacker, so exploitation – if it ever happens – will be limited. The fact that the vulnerable library versions haven’t ended up in many production systems is a huge blessing.
That said, a number of scripts and tools have been released allowing users to check for the presence of the backdoor.
Freund’s post on the OSS mailing list includes a script to detect vulnerable SSH binaries on systems, which has then been repurposed and extended to also check whether a system uses a backdoored version of the liblzma library.
Binarly, a firmware security firm, has set up an online scanner that allows users to analyze any binary for the backdoor implant.
“Such a complex and professionally designed comprehensive implantation framework is not developed for a one-shot operation. It could already be deployed elsewhere or partially reused in other operations. That’s exactly why we started focusing on more generic detection for this complex backdoor,” they noted.
Late last week, Bitdefender released another scanner, that must be deployed on systems that need testing. (Since the scanner requires root privileges to be effective, the company has released the source code.)
It can search for all infected liblzma libraries, even if they are not used by the Secure Shell Daemon application (sshd), as well as for a unique byte sequence injected by the backdoor during library compilation.
Elastic Security Labs researchers have published their analysis of the backdoor, as well as YARA signatures, detection rules, and osquery queries that Linux admins can use to find vulnerable liblzma libraries and identify potentially suspicious sshd behavior.

Malware Data Science: Attack Detection and Attribution
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Apr 05 2024
2024 has already seen dozens of local governments slammed by ransomware incidents and cyberattacks, limiting services for millions of people across the United States.
The latest high-profile incident involves New York City, which was forced to take a city payroll website offline and remove it from public view after dealing with a phishing incident.

The incident was first reported by Politico, which spoke to city workers who complained of the New York City Automated Personnel System, Employee Self Service (NYCAPS/ESS) being offline right as many tried to file their taxes.
New York City’s Office of Technology and Innovation and told Recorded Future News that NYC Cyber Command “was made aware of a smishing campaign targeting NYCAPS users.” Smishing is essentially phishing via text messages instead of emails.
“NYC Cyber Command has been advising and working with FISA-OPA and DCAS to implement enhancements to security measures,” the office said. “City employees have been advised to remain vigilant and confirm the legitimacy of any NYCAPS and payroll-related communications and activity.”
A city official reiterated that the NYCAPS website is still online and accessible to all employees through the city’s secure internal network.
The smishing campaign allegedly involved messages sent to city workers asking them to activate multi-factor authentication, with a link to a phishing domain.
Shashi Prakash, CTO at security firm Bolster.AI, told Recorded Future News that his team saw the domain “essnyc{.}online” the day it was registered. Other researchers said the domain was registered in Lithuania.
Prakash explained that his team’s data shows it has been live since December 9 and shared a screenshot of the page, which looks exactly like the NYCAPS website.
“There is one additional domain cityofanaheim{.}online on the same infrastructure which does make it look like they were targeting other cities,” Prakash said.
Keeper Security’s Teresa Rothaar said more than 80 percent of breaches happen because of weak or stolen passwords, credentials and secrets, much of which is acquired through the kind of phishing and smishing attacks New York City is currently dealing with.
To make matters worse, the New York City attackers clearly knew that multi-factor authentication is a critical layer of security and played on that concept while trying to steal credentials.
“Often, innocent people who are not trained on phishing prevention will focus on the ‘pinstripes’ of the email or illegitimate site, meaning the aesthetics that they are familiar with, such as the logo or colors of their banking site,” she said.
“Cybercriminals spend a lot of time making ‘lookalike’ sites appear authentic so that users are tricked into entering login credentials. Employees should always err on the side of caution and assume that all of their work-related (and even personal) passwords have been compromised – especially if they reuse the same passwords across accounts (a big no-no, and this situation illustrates why).”
The campaign targeting New York City is one of many specifically going after city, county and state-level governments across the United States.
Just in the last week, the cities of Birmingham, Alabama, and East Baton Rouge, Louisiana, have announced security incidents affecting public services. Jackson County in Missouri was forced to declare a state of emergency after discovering a ransomware attack last month.
On Thursday, the Florida Department of Juvenile Justice in Tallahassee admitted to local news outlets that it was dealing with a cyberattack that forced some systems offline.
Florida’s Hernando County similarly announced a cyberattack on Thursday, warning that while 911, police and EMS systems were still operational, several other government services would be down for an unknown amount of time. Local news outlets reported that the FBI is involved in the response to the incident.
Rebecca Moody, head of data research at Comparitech, has been looking into ransomware attacks on U.S. government offices and said she has found 18 confirmed ransomware attacks so far this year.
Other researchers have tracked at least 25 ransomware attacks on U.S. government offices.
While several states have banned government organizations from paying ransoms to groups, the offices continue to be ripe targets for ransomware gangs and hackers. Washington County in Pennsylvania recently revealed that it paid a $350,000 ransom to hackers following a January ransomware attack.
James Turgal, who spent 22 years working at the FBI, told Recorded Future News that attacks against state, local and tribal governments have accelerated over the last year.
“From the threat actors’ point of view, these municipalities are a target-rich environment with an abundant source of victims. By my estimation, with just around 95,000 soft targets nationwide, there are 40,000 cities, towns and municipalities, approximately 50,000 special government districts nationwide, and then the additional tribal governments that round out the numbers,” he said.
“There needs to be a sense of urgency on the part of state and local governments and municipalities to get ahead of the threat, as these local entities have the most direct impact on our citizens, and a cyber focused disruption can be potentially life-threatening when considering the health and public safety services our local governments control.”
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Apr 05 2024
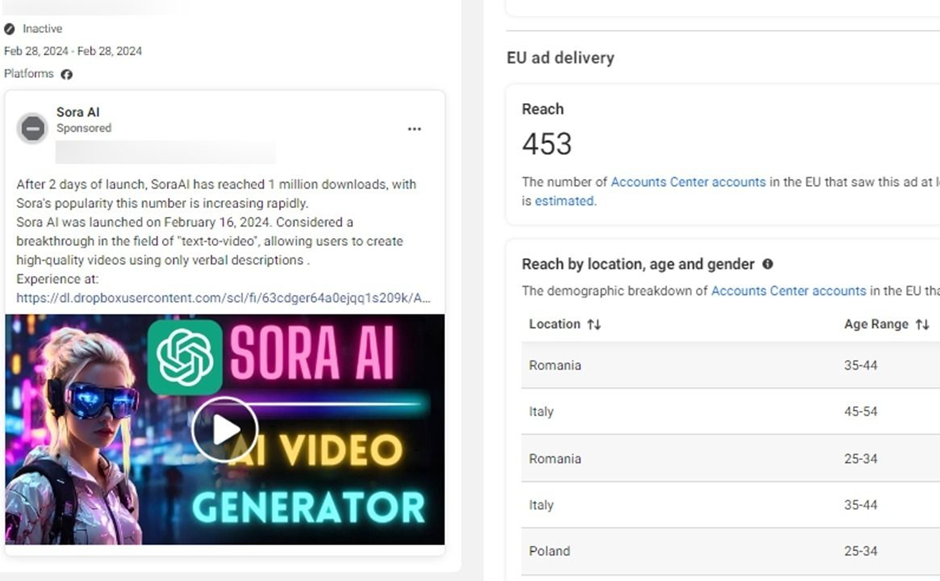
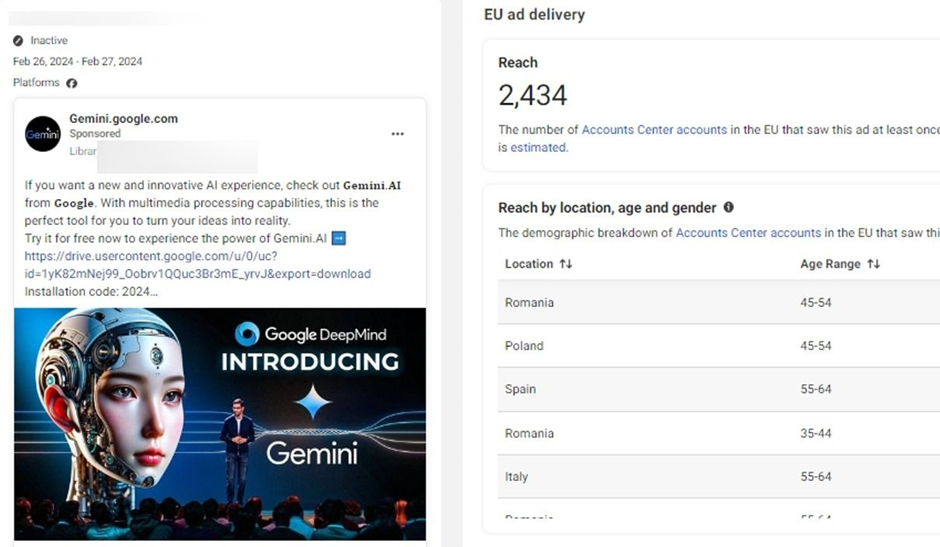
Hackers have been found hijacking Facebook pages to impersonate popular AI brands, thereby injecting malware into the devices of unsuspecting users.
This revelation comes from a detailed investigation by Bitdefender Labs, which has been closely monitoring these malicious campaigns since June 2023.
Recent analyses of malvertising campaigns have revealed a disturbing trend.
Ads are distributing an assortment of malicious software, which poses severe risks to consumers’ devices, data, and identity.
Unwitting interactions with these malware-serving ads could lead to downloading and deploying harmful files, including Rilide Stealer, Vidar Stealer, IceRAT, and Nova Stealer, onto users’ devices.
Bitdefender Labs has spotlighted an updated version of the Rilide Stealer (V4) lurking within sponsored ad campaigns that impersonate popular AI-based software and photo editors such as Sora, CapCut, Gemini AI, Photo Effects Pro, and CapCut Pro.
This malicious extension, targeting Chromium-based browsers, is designed to monitor browsing history, capture login credentials, and even facilitate the withdrawal of crypto funds by bypassing two-factor authentication through script injections.
Key Updates in Rilide V4:
Malicious hashes
Vidar Stealer, another prolific info stealer, is marketed through the same MaaS model via dark web ads, forums, and Telegram groups.
Capable of exfiltrating personal information and crypto from compromised devices, Vidar’s distribution has evolved from spam campaigns and cracked software to malicious Google Search ads and social media platforms, mainly through sponsored ads on Meta’s platform.
Malicious hashes
Despite its name, IceRAT functions more as a backdoor on compromised devices. It acts as a gateway for secondary infections, such as crypto miners and information stealers that target login credentials and other sensitive data.
Malicious hashes
Nova Stealer emerges as a highly proficient info stealer with capabilities including password exfiltration, screen recordings, discord injections, and crypto wallet hijacking.
Nova Stealer, offered as MaaS by the threat actor known as Sordeal, represents a significant threat to digital security.
Malicious hashes
The addition of AI tools on the internet, from free offerings and trials to subscription-based services, has not gone unnoticed by cybercriminals.
Midjourney, a leading generative AI tool with a user base exceeding 16 million as of November 2023, has become a favored tool among cyber gangs over the past year, highlighting the intersection of cutting-edge technology and cybercrime.

As the digital landscape continues to evolve, so does the nature of the threats it maintains.
The rise of Malware-as-a-Service represents a significant shift in the cyber threat paradigm that requires vigilant and proactive measures to combat.
Key Updates in Rilide V4:
Malicious hashes
Vidar Stealer, another prolific info stealer, is marketed through the same MaaS model via dark web ads, forums, and Telegram groups.
Capable of exfiltrating personal information and crypto from compromised devices, Vidar’s distribution has evolved from spam campaigns and cracked software to malicious Google Search ads and social media platforms, mainly through sponsored ads on Meta’s platform.
Malicious hashes
Despite its name, IceRAT functions more as a backdoor on compromised devices. It acts as a gateway for secondary infections, such as crypto miners and information stealers that target login credentials and other sensitive data.
Malicious hashes
Nova Stealer emerges as a highly proficient info stealer with capabilities including password exfiltration, screen recordings, discord injections, and crypto wallet hijacking.
Nova Stealer, offered as MaaS by the threat actor known as Sordeal, represents a significant threat to digital security.
Malicious hashes
The addition of AI tools on the internet, from free offerings and trials to subscription-based services, has not gone unnoticed by cybercriminals.
Midjourney, a leading generative AI tool with a user base exceeding 16 million as of November 2023, has become a favored tool among cyber gangs over the past year, highlighting the intersection of cutting-edge technology and cybercrime.

As the digital landscape continues to evolve, so does the nature of the threats it maintains.
The rise of Malware-as-a-Service represents a significant shift in the cyber threat paradigm that requires vigilant and proactive measures to combat.
The Complete Guide to Software as a Service: Everything you need to know about SaaS
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Apr 04 2024
The framework conducts reconnaissance on active assets and completes its operation with a scan for vulnerabilities, secrets, misconfigurations, and potential phishing domains, utilizing open-source and proprietary tools.
Some of the features that make Mantis stand out are:
“Last year, we explored open-source frameworks our organization can use to monitor assets. We wanted to set up an asset discovery framework that allows us to add custom scripts, enable or disable tools to run based on configs, scale, and deploy the framework across a cluster of VMs. We also wanted to find a way to ingest domains from DNS services into our databases. This led us to create Mantis, an asset discovery framework that could help bug bounty hunters as well as security teams,” Prateek Thakare, lead developer of Mantis, told Help Net Security.
Mantis is CPU intensive, so it’s advisable to run it on a dedicated virtual machine.
“We are planning to have our dashboard making it easier to view and monitor the assets. We will also work on improvising the discovery, recon, and scan process by adding new tools and custom scripts,” Thakare concluded.
Mantis is available for free on GitHub.
The OSINT Handbook: A practical guide to gathering and analyzing online information
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Apr 03 2024
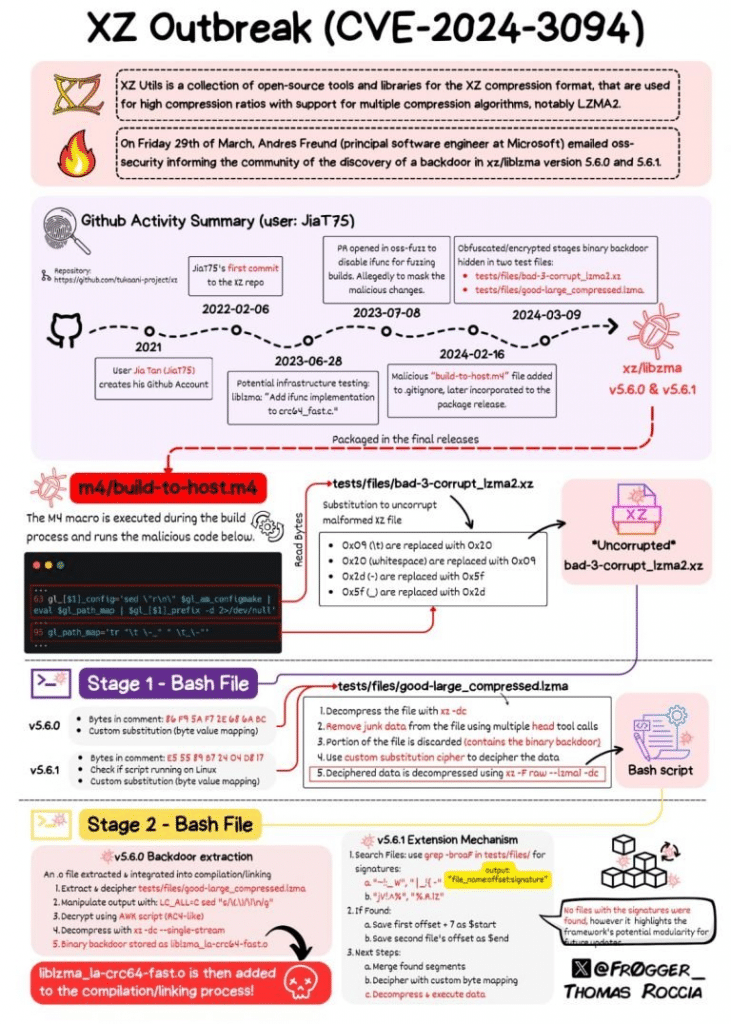
In an unsettling development that emerged late last week, the open-source community was thrust into a state of high alert following the disclosure that XZ Utils, a fundamental compression utility widespread across Linux distributions, had been compromised. This startling revelation has left a significant mark on the open-source ecosystem, prompting a swift and coordinated response from maintainers and security professionals alike.
Discovery of the Backdoor
The initial discovery of the backdoor was made by Andres Freund, a Microsoft software engineer, during routine diagnostics on Debian sid (development) installations. Freund’s investigation, sparked by unusually high CPU usage during SSH logins and accompanying error alerts, led to the identification of the culprit: a malicious insertion within the liblzma library, a core component of the XZ package. This finding was subsequently designated with the vulnerability identifier CVE-2024-3094. Attribution for this calculated insertion has been directed at an individual known as “Jia Tan” (JiaT75 on GitHub), who, through an elaborate scheme of social engineering and the use of sock puppet accounts, gained the trust of the XZ Utils maintainer community. This long-term infiltration underscores the advanced nature of the threat actor involved, pointing towards a highly skilled and resourceful adversary.
Affected Distributions and Response
| STATUS | DISTRIBUTION | RESPONSE |
|---|---|---|
| Affected | Fedora Rawhide and Fedora Linux 40 beta | Confirmed by Red Hat |
| Affected | openSUSE Tumbleweed and openSUSE MicroOS | Confirmed by openSUSE maintainers |
| Affected | Debian testing, unstable, experimental distributions | Confirmed by Debian maintainers |
| Affected | Kali Linux (updates between March 26th to March 29th) | Confirmed by OffSec |
| Affected | Some Arch Linux virtual machine and container images | Confirmed by Arch Linux maintainers |
| Not Affected | Red Hat Enterprise Linux (RHEL) | Confirmed by Red Hat |
| Not Affected | Ubuntu | Confirmed by Ubuntu |
| Not Affected | Linux Mint | Confirmed by Linux Mint |
| Not Affected | Gentoo Linux | Confirmed by Gentoo Linux |
| Not Affected | Amazon Linux and Alpine Linux | Confirmed by Amazon Linux and Alpine Linux maintainers |
Guidance and Recommendations
In light of these disclosures, affected parties have been advised to approach the situation as a definitive security incident, necessitating a comprehensive review and mitigation process. This includes the diligent examination for any unauthorized access or misuse, the rotation of exposed credentials, and a thorough security audit of systems that might have been compromised during the exposure window.
Insight into the Backdoor Mechanism
The intricacy of the backdoor, embedded within the xz-utils’ liblzma library and manifesting under precise conditions, notably through remote, unprivileged connections to public SSH ports, speaks volumes about the sophistication of the threat actors behind this maneuver. This backdoor not only raises concerns over performance degradation but also poses a significant risk to the integrity and security of the affected systems.
In light of the recent discovery of the CVE-2024-3094 backdoor in XZ Utils versions 5.6.0 and 5.6.1, the cybersecurity community has been on high alert. Binarly has introduced a free scanner to identify the presence of this backdoor in affected systems. Below is a detailed tutorial, including examples, on how to use the Binarly Free Scanner to detect the CVE-2024-3094 backdoor in your systems.
The CVE-2024-3094 backdoor in XZ Utils versions 5.6.0 and 5.6.1 poses a significant security risk, potentially allowing unauthorized remote access. It’s crucial to grasp the severity of this issue before proceeding.
Example: Imagine a scenario where an organization’s critical systems are running on a compromised version of XZ Utils, leaving the network vulnerable to attackers who could gain unauthorized access through the backdoor.
Navigate to XZ.fail, the dedicated website Binarly set up for the scanner.
Example: Open your web browser and type “https://xz.fail” in the address bar to access the Binarly Free Scanner’s homepage.
The Binarly Free Scanner uses advanced static analysis to detect the backdoor by examining ifunc transition behaviors in the binaries.
Example: After accessing XZ.fail, you’ll be prompted to upload or specify the path to the binary files you wish to scan. Suppose you want to check a file named example.xz; you would select this file for scanning through the web interface or command line, depending on the tool’s usage options provided.
Once the scan completes, the scanner will report back on whether the CVE-2024-3094 backdoor was detected in the scanned files.
Example: If the scanner finds the backdoor in example.xz, it might display a message such as “Backdoor Detected: CVE-2024-3094 present in example.xz”. If no backdoor is found, a message like “No Backdoor Detected: Your files are clean” would appear.
If the scanner detects the backdoor, immediate action is required to remove the compromised binaries and replace them with secure versions.
Example: For a system administrator who finds the backdoor in example.xz, the next steps would involve removing this file, downloading a secure version of XZ Utils from a trusted source, and replacing the compromised file with this clean version.
Regularly scan your systems with the Binarly Free Scanner and other security tools to ensure no new threats have compromised your binaries.
Example: Set a monthly reminder to use the Binarly Free Scanner on all critical systems, especially after installing updates or adding new software packages, to catch any instances of the CVE-2024-3094 backdoor or other vulnerabilities.
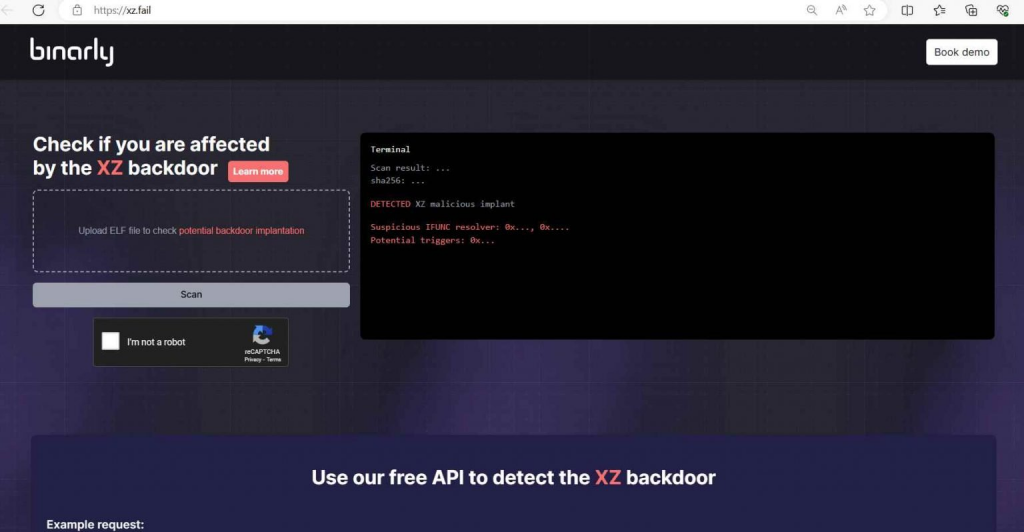
The Binarly Free Scanner is a powerful tool in the fight against the CVE-2024-3094 backdoor, offering a reliable method for detecting and addressing this significant threat. By following these steps and incorporating the examples provided, users can effectively safeguard their systems from potential compromise.
The accidental discovery of this backdoor by Freund represents a crucial turning point, underscoring the importance of vigilant and proactive security practices within the open-source domain. This incident serves as a stark reminder of the vulnerabilities that can arise in even the most trusted components of the digital infrastructure. It has sparked a renewed debate on the necessity for enhanced security protocols and collaborative efforts to safeguard crucial open-source projects against increasingly sophisticated threats.
In the aftermath, the open-source community and its stewards are called upon to reassess their security posture, emphasizing the need for comprehensive auditing, transparent communication, and the adoption of robust security measures to prevent future compromises. This incident not only highlights the vulnerabilities inherent in the digital landscape but also the resilience and collaborative spirit of the open-source community in responding to and mitigating such threats.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Apr 02 2024
Cloud Active Defense is an open-source solution that integrates decoys into cloud infrastructure. It creates a dilemma for attackers: risk attacking and being detected immediately, or avoid the traps and reduce their effectiveness. Anyone, including small companies, can use it at no cost and start receiving high-signal alerts.
Where honeypots are good at detecting lateral movement once the initial application has been compromised, Cloud Active Defense brings the deception directly into that initial application.
“We do this by injecting decoys into HTTP responses. These decoys are invisible to regular users and very tempting to attackers. This creates a situation where attackers must constantly guess: is that a trap or an exploitation path? This guessing slows down the attack operation and can lead attackers to ignore valid attack vectors as they suspect them to be traps. Furthermore, since the application’s replies cannot be 100% trusted anymore, find-tuning your exploit payload becomes painful,” Cédric Hébert, CISO – Innovation at SAP and developer of Cloud Active Defense, told Help Net Security.
“In the short term, we plan to make it easy to ingest the generated alerts to a SIEM system for faster response. We also plan to release code to make it simple to deploy on a Kubernetes cluster, where each application can be configured independently. In the mid-term, we want to work on proposing response strategies: surely, banning the IP address can be an option, but what we envision is, upon detection, to give the possibility to route the active session to a clone of the application where no more harm can be done,” Hebert concluded.
Cloud Active Defense is available for free on GitHub.

Must read:
Deep Dive: Exploring the Real-world Value of Open Source Intelligence
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Apr 01 2024
One of the primary concerns regarding data privacy is the potential for breaches and unauthorized access. Whether it’s financial records, medical histories, or personal communications, individuals have a right to control who can access their data and for what purposes.
In this Help Net Security round-up, we present parts of previously recorded videos in which security experts discuss various aspects of data privacy and protection.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 29 2024

Businesses increasingly rely on Software as a Service (SaaS) applications to drive efficiency, innovation, and growth.
However, this shift towards a more interconnected digital ecosystem has not come without its risks.
According to the “2024 State of SaaS Security Report” by Wing Security, a staggering 97% of organizations faced exposure to attacks through compromised SaaS supply chain applications in 2023, highlighting a critical vulnerability in the digital infrastructure of modern businesses.
The report, which analyzed data from 493 companies in the fourth quarter of 2023, illuminates the multifaceted nature of SaaS security threats.
From supply chain attacks taking center stage to the alarming trend of exploiting exposed credentials, the findings underscore the urgent need for robust security measures.
Supply chain attacks have emerged as a significant threat, with 96.7% of organizations using at least one app that had a security incident in the past year.
The MOVEit breach, which directly and indirectly impacted over 2,500 organizations, and North Korean actors’ targeted attack on JumpCloud’s clients are stark reminders of the cascading effects a single vulnerability can have across the supply chain.
The simplicity of credential stuffing attacks and the widespread issue of unsecured credentials continue to pose a significant risk.
The report highlights several high-profile incidents, including breaches affecting Norton LifeLock and PayPal customers, where attackers exploited stolen credentials to gain unauthorized access to sensitive information.
Despite adopting Multi-Factor Authentication (MFA) as a security measure, attackers have found ways to bypass these defenses, targeting high-ranking executives in sophisticated phishing campaigns.
Additionally, the report points to a concerning trend of token theft, with many unused tokens creating unnecessary risk exposure for many organizations.
As we move into 2024, the SaaS threat landscape is expected to evolve, with AI posing a new threat.
The report identifies two primary risks associated with AI in the SaaS domain: the vast volume of AI models in SaaS applications and the potential for data mismanagement.
Furthermore, the persistence of credential-based attacks and the rise of interconnected threats across different domains underscore the need for a holistic cybersecurity approach.
The report offers eight practical tips for organizations to combat these growing threats, including discovering and managing the risk of third-party applications, leveraging threat intelligence, and enforcing MFA.
Additionally, regaining control of the AI-SaaS landscape and establishing an effective offboarding procedure are crucial steps in bolstering an organization’s SaaS security.
The “2024 State of SaaS Security Report” by Wing Security serves as a wake-up call for businesses to reassess their SaaS security strategies.
With 97% of organizations exposed to attacks via compromised SaaS supply chain apps, the need for vigilance and proactive security measures has never been more critical.
As the digital landscape continues to evolve, so must our approaches to protect it.
Mitigating Supply Chain Attacks in the Digital Age
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 28 2024
Wireshark stands as the undisputed leader, offering unparalleled tools for troubleshooting, analysis, development, and education.
The latest update, Wireshark 4.2.4, includes a host of fixes and updates to further cement its position as the go-to tool for network professionals and enthusiasts alike.
This release underscores the Wireshark Foundation’s commitment to advancing protocol analysis education, a mission supported by contributions from the global community.
The Wireshark team has diligently addressed several vulnerabilities in this release, notably:
Wireshark has also been the subject of CVEs assigned without coordination with the project, specifically CVE-2024-24478, CVE-2024-24479, and CVE-2024-24476.
The Wireshark team has contested these, stating they are based on invalid assumptions, and has requested their rejection, showcasing the team’s proactive stance on security matters.
The 4.2.4 update addresses a variety of bugs, improving user experience and software reliability:
While this release does not introduce new features or protocols, it significantly updates support for many existing protocols, including but not limited to 5GLI, BGP, DHCPv6, and ZigBee ZCL.
This comprehensive update ensures that Wireshark remains at the forefront of protocol analysis, capable of handling the latest network communication standards.
Wireshark 4.2.4 can be downloaded from the official Wireshark website, and detailed instructions for installation across various platforms are available.
Manual installation of this update is required for users upgrading from versions 4.2.0 or 4.2.1 on Windows.
Most Linux and Unix distributions provide Wireshark packages through their native package management systems, making installation or upgrade seamless.
For specific file locations for preference files, plugins, SNMP MIBS, and RADIUS dictionaries, users can refer to the Help section within Wireshark or use the tshark -G folders command.
Wireshark 4.2.4 exemplifies the ongoing dedication of the Wireshark Foundation and its global community to enhance the utility and security of the world’s premier network protocol analyzer.
This release ensures that Wireshark remains an indispensable tool for network professionals and enthusiasts by addressing critical vulnerabilities, fixing bugs, and updating protocol support.
As the project continues to evolve, the support and contributions from the community remain vital to its success.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 27 2024
On an unexpected Tuesday, the collision of a container ship with the Francis Scott Key Bridge in Baltimore not only disrupted the normal flow of traffic and commerce but also sparked a vigorous debate on the potential causes of this incident. Among the various theories proposed, the role of cybersecurity—or the lack thereof—has emerged as a focal point of discussion. This event has served as a catalyst for a broader examination of cybersecurity practices within the maritime industry, revealing both vulnerabilities and the sometimes-overlooked factors that suggest other causes for such incidents. In the digital age, the maritime industry’s reliance on technology for navigation, communication, and operational functions has grown exponentially. This shift towards digitalization, while beneficial in terms of efficiency and connectivity, has also increased the sector’s exposure to cyber threats. Systems that control navigation, cargo handling, and engine operations are all potential targets for cyberattacks, which can lead to severe safety and financial risks.

In recent years, the maritime industry has increasingly embraced technology, relying on digital systems for navigation, communication, and operational functions. This digital transformation has enhanced efficiency and connectivity but has also exposed the sector to cyber threats. Cyberattacks can target systems controlling navigation, cargo handling, and even the engines of these colossal vessels, posing a significant risk to safety and commerce.
Could Cybersecurity Have Been a Factor in the Baltimore Incident?
To understand whether a cybersecurity breach could have led to the collision with the Francis Scott Key Bridge, it is essential to consider several factors:
While the possibility of a cybersecurity breach cannot be dismissed outright, several arguments suggest that other factors could be more plausible:
Technical Safeguards and Redundancies
Maritime vessels are equipped with numerous technical safeguards and redundant systems designed to prevent total system failure in case of a cyber intrusion. These include manual overrides for navigation and control systems, allowing crew members to maintain control over the vessel even if digital systems are compromised. Such safeguards can mitigate the impact of a cyber attack on a ship’s operational capabilities.
Cybersecurity Protocols and Training
The maritime industry has been increasingly aware of the potential cyber threats and has implemented stringent cybersecurity protocols and training for crew members. These measures are aimed at preventing unauthorized access and ensuring the integrity of the ship’s systems. Crews are trained to recognize and respond to cybersecurity threats, reducing the likelihood of a successful cyber attack impacting vessel navigation or control systems.
Physical Factors and Human Error
Many maritime incidents are the result of physical factors or human error rather than cyber attacks. These can include adverse weather conditions, navigational errors, mechanical failures, and miscommunication among crew members. Such factors have historically been the most common causes of maritime accidents and cannot be overlooked in any thorough investigation.
Complexity of Executing a Targeted Cyber Attack
Executing a cyber attack that leads to a specific outcome, such as causing a ship to collide with a bridge, requires an intimate knowledge of the vessel’s systems, current position, and intended course. It also necessitates overcoming the vessel’s cybersecurity measures without detection. The complexity and specificity of such an attack make it a less likely cause of maritime incidents compared to more conventional explanations.
Lack of Evidence Indicating a Cyber Attack
In the absence of specific evidence pointing to a cyber intrusion, such as anomalies in the ship’s digital systems, unauthorized access logs, or the presence of malware, it is prudent to consider other more likely causes. Cybersecurity investigations involve detailed analysis of digital footprints and system logs, and without concrete evidence suggesting a cyber attack, attributing the incident to such a cause would be speculative.
Regardless of whether a cyberattack played a role in the Baltimore bridge incident, this event underscores the importance of robust cybersecurity practices in the maritime industry. Enhancing cyber defenses, conducting regular security assessments, and training personnel in cybersecurity awareness are crucial steps in safeguarding maritime operations.
However, it is equally important to recognize and mitigate the non-cyber risks that ships face. A comprehensive approach to safety and security, encompassing both cyber and traditional factors, is essential for protecting the maritime industry against a wide range of threats.
The collision of a container ship with the Francis Scott Key Bridge has highlighted the critical role of cybersecurity in modern maritime operations, while also reminding us of the myriad other factors that can lead to such incidents. As the investigation into this event continues, the maritime industry must take a holistic view of security, embracing both digital and physical measures to ensure the safety of its operations in an increasingly complex and interconnected world.
“Our thoughts and prayers are with the U.S. Coast Guard Sector NCR, multiple first responders, and all those affected by the tragic incident at the Francis Scott Key Bridge in Baltimore. According to reports, a 948-foot Singapore-flagged containership collided with the bridge causing it to collapse, with persons reported to be in the water.”
Next Level Cybersecurity: Detect the Signals, Stop the Hack
Maritime Cybersecurity: A Guide for Leaders and Managers
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 26 2024
Eliminating SQL Injection Vulnerabilities in Software
SQL Injection Strategies: Practical techniques to secure old vulnerabilities against modern attacks
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 25 2024
Over 170,000 users have fallen victim to a meticulously orchestrated scheme exploiting the Python software supply chain.
The Checkmarx Research team has uncovered a multi-faceted attack campaign that leverages fake Python infrastructure to distribute malware, compromising the security of countless developers and organizations.
This article delves into the attack campaign, its impact on victims, the tactics, techniques, and procedures (TTPs) employed by the threat actors, and the critical findings from Checkmarx’s investigation.
The core of this malicious campaign revolves around an attacker’s ability to combine several TTPs to launch a silent attack on the software supply chain, specifically targeting the Python ecosystem.
By creating multiple malicious open-source tools with enticing descriptions, the attackers lured victims into their trap, primarily through search engines.
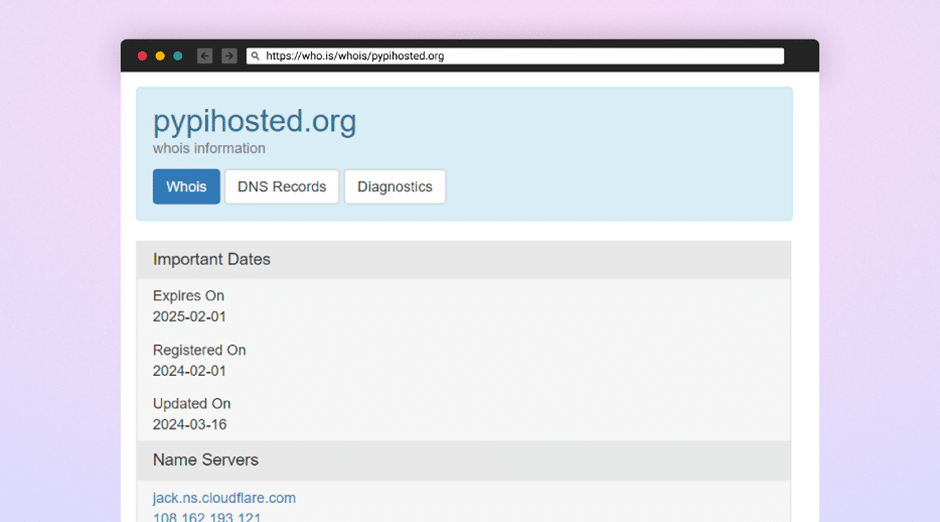
The campaign’s sophistication is evident in distributing a malicious dependency hosted on a fake Python infrastructure, which was then linked to popular projects on GitHub and legitimate Python packages.
A chilling account from Mohammed Dief, a Python developer and one of the campaign’s victims, highlights the stealth and impact of the attack.
Dief encountered a suspicious error message while working on his laptop, the first sign of the compromise, leading to the realization that his system had been hacked.
Among the notable victims of this campaign is the Top.gg GitHub organization, a community boasting over 170,000 members.
The attackers managed to hijack GitHub accounts with high reputations, including that of “editor-syntax,” a maintainer with write permissions to Top.gg’s repositories.
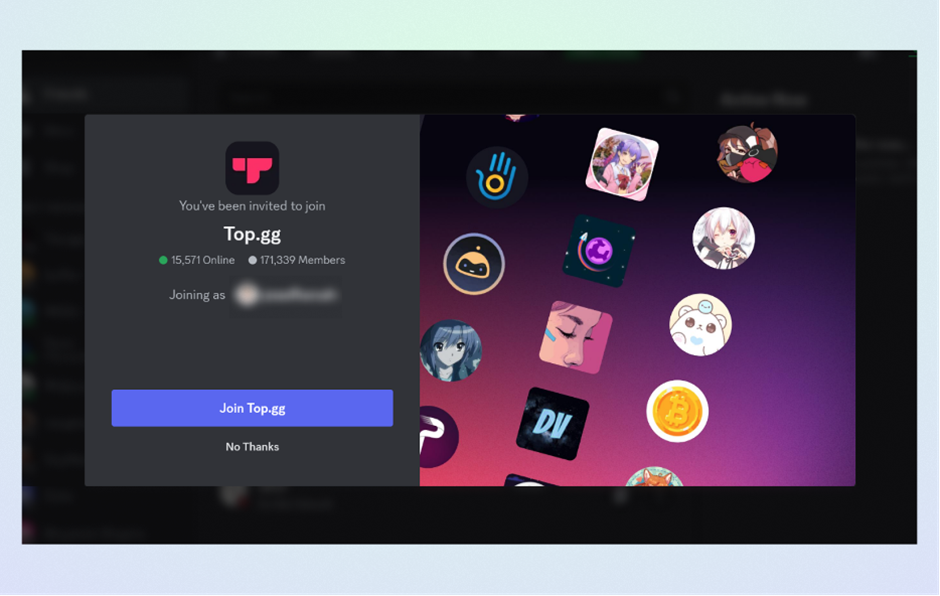
This allowed them to commit malicious acts and increase the visibility and credibility of their malicious repositories.
The attack’s impact is far-reaching, affecting individual developers and larger communities alike.
Social engineering schemes, account takeovers, and malicious packages published on the PyPi registry have underscored the software supply chain’s vulnerability to such sophisticated attacks.
The Checkmarx Research team has uncovered an attack campaign aimed at the software supply chain.
The campaign appears to have successfully exploited multiple victims.
The threat actors behind this campaign demonstrated high sophistication and planning.
They employed a range of TTPs, including:
By deploying a fake Python package mirror and utilizing typosquatting techniques, the attackers could deceive users and systems into downloading poisoned versions of popular packages like “Colorama.
“The malicious payload delivered through these packages is designed to harvest sensitive information, including passwords, credentials, and data from various software applications.

The malware targets web browsers, Discord, cryptocurrency wallets, and Telegram, and even includes a keylogging component to capture victims’ keystrokes.
The final stage of the malware reveals its data-stealing capabilities, targeting not only personal and financial information but also attempting to gain unauthorized access to victims’ social media and communication platforms.
This attack campaign highlights the critical vulnerabilities within the software supply chain, particularly in open-source ecosystems like Python’s.
The sophistication and success of the attackers in exploiting these vulnerabilities underscore the need for heightened vigilance and robust security practices among developers and organizations.
Through continuous monitoring, collaboration, and information sharing, the cybersecurity community can mitigate risks and protect the integrity of open-source software.
Python for Cybersecurity: Using Python for Cyber Offense and Defense
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 24 2024
During the month of Ramadan, Resecurity observed a significant increase in fraudulent activities and scams, coinciding with a surge in retail and online transactions. Middle Eastern enterprises, facing this heightened risk, are urged to bolster consumer protection and reinforce their brand security.
Notably, in the Kingdom of Saudi Arabia (KSA), consumer spending topped regional charts, exceeding $16 billion. This spike in e-commerce activity has, unfortunately, drawn the attention of cybercriminals who exploit these platforms to execute scams, leading to substantial financial repercussions for both consumers and businesses. The estimated total financial impact of these activities ranges between $70 and $100 million, accounting for frauds perpetrated against expatriates, residents, and foreign visitors.
Due to continued efforts in brand protection for many clients in the Middle East, Resecurity has effectively blocked over 320 fraudulent resources that were impersonating key logistics providers and e-government services. Cybercriminals are aggressively exploiting platforms such as Sadad, Musaned, Ajeer, Ejar, and well-known logistics services to deceive internet users and draw them into different scams. It is strongly advised to refrain from sharing personal and payment information on questionable sites or with individuals posing as bank or government employees.
The malicious actors utilize cloud-based hosting services like Softr, Netlify, and Vercel, which offer pre-defined templates, to create websites using AI. This method allows them to scale their operations efficiently, saving time and effort while rapidly generating new fraudulent sites at an unprecedented rate.

The full report published by Resecurity is available here:

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 22 2024
Are you interested in cybersecurity?
Interested in discovering how Python can bolster your abilities in safeguarding digital assets? Delve into the potential of Python for cybersecurity.
In the current digital era, cybersecurity holds greater significance than ever before. Python, renowned for its versatility and resilience, has emerged as a fundamental tool for cybersecurity professionals globally.
🔹 How Python can streamline threat detection and analysis.
🔹 Practical examples of Python scripts for automating security tasks.
🔹 Resources and tools to kickstart your journey into Python for cybersecurity.
Regardless of whether you’re an experienced cybersecurity professional or new to the field, Python has the potential to transform your approach to security challenges.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 21 2024
Mar 21 2024
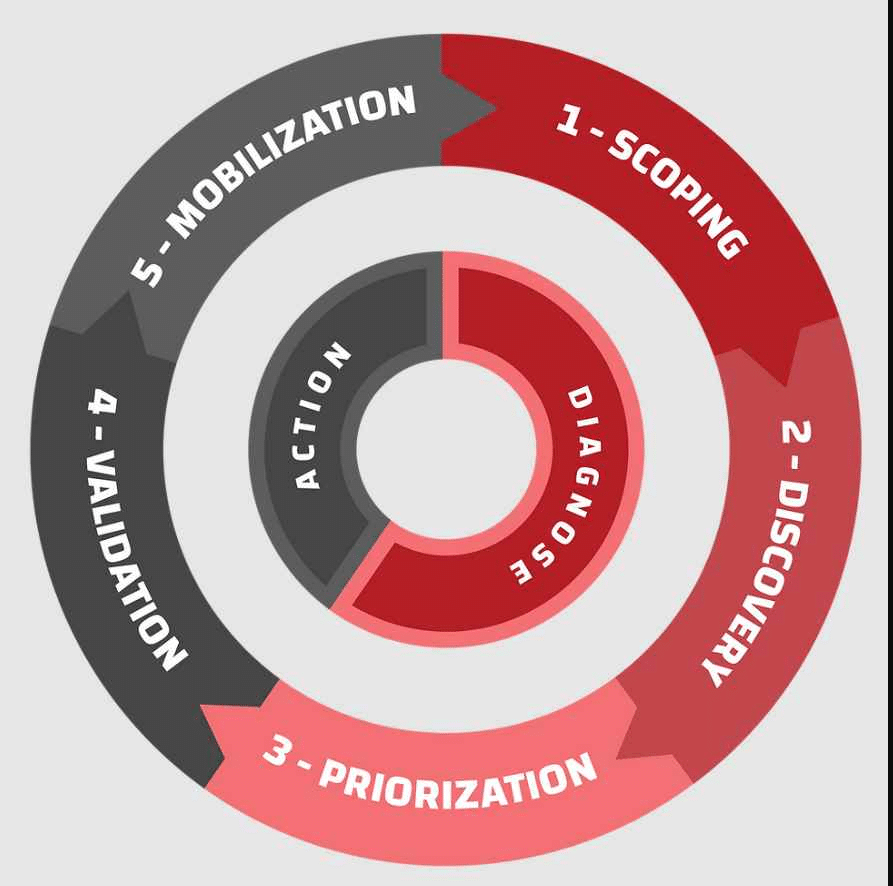
Continuous Threat Exposure Management (CTEM) is an evolving cybersecurity practice focused on identifying, assessing, prioritizing, and addressing security weaknesses and vulnerabilities in an organization’s digital assets and networks continuously. Unlike traditional approaches that might assess threats periodically, CTEM emphasizes a proactive, ongoing process of evaluation and mitigation to adapt to the rapidly changing threat landscape. Here’s a closer look at its key components:
The goal of CTEM is to reduce the “attack surface” of an organization—minimizing the number of vulnerabilities that could be exploited by attackers and thereby reducing the organization’s overall risk. By continuously managing and reducing exposure to threats, organizations can better protect against breaches and cyber attacks.
Continuous Threat Exposure Management (CTEM) represents a proactive and ongoing approach to managing cybersecurity risks, distinguishing itself from traditional, more reactive security practices. Understanding the differences between CTEM and alternative approaches can help organizations choose the best strategy for their specific needs and threat landscapes. Let’s compare CTEM with some of these alternative approaches:
CTEM offers a comprehensive and continuous approach to cybersecurity, focusing on reducing exposure to threats in a dynamic and ever-evolving threat landscape. While alternative approaches each have their place within an organization’s overall security strategy, integrating them with CTEM principles can provide a more resilient and responsive defense mechanism against cyber threats.
Implementing Continuous Threat Exposure Management (CTEM) within an AWS Cloud environment involves leveraging AWS services and tools, alongside third-party solutions and best practices, to continuously identify, assess, prioritize, and remediate vulnerabilities and threats. Here’s a detailed example of how CTEM can be applied in AWS:
Imagine you’re managing a web application hosted on AWS. Here’s how CTEM comes to life:
This cycle of identifying, assessing, prioritizing, mitigating, and continuously improving forms the core of CTEM in AWS, helping to ensure that your cloud environment remains secure against evolving threats.
Implementing Continuous Threat Exposure Management (CTEM) in Azure involves utilizing a range of Azure services and features designed to continuously identify, assess, prioritize, and mitigate security risks. Below is a step-by-step example illustrating how an organization can apply CTEM principles within the Azure cloud environment:
Let’s say you’re managing a web application hosted in Azure, utilizing Azure App Service for the web front end, Azure SQL Database for data storage, and Azure Blob Storage for unstructured data.
By following these steps and utilizing Azure’s comprehensive suite of security tools, organizations can implement an effective CTEM strategy that continuously protects against evolving cyber threats.
Implementing Continuous Threat Exposure Management (CTEM) in cloud environments like AWS and Azure involves a series of strategic steps, leveraging each platform’s unique tools and services. The approach combines best practices for security and compliance management, automation, and continuous monitoring. Here’s a guide to get started with CTEM in both AWS and Azure:
Implementing CTEM in AWS and Azure requires a deep understanding of each cloud environment’s unique features and capabilities. By leveraging the right mix of tools and services, organizations can create a robust security posture that continuously identifies, assesses, and mitigates threats.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 20 2024
Kyna Kosling March 14, 2024
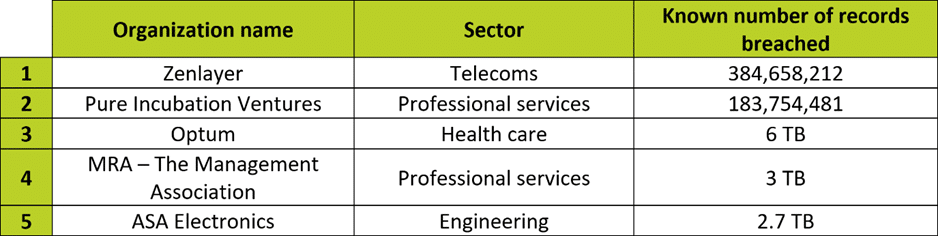
IT Governance USA’s research found the following for February 2024:
This month, globally, 719,366,482 records were known to be breached – 86% of them were in the USA.
This is unusual. Typically, the USA suffers more incidents than any other country, but these tend to lead to a disproportionately low number of records breached.
This month is different due to two outlier breaches:
*The threat actor provided 100,000 records as a sample.
For a quick, one-page overview of this month’s findings, please use our Data Breach Dashboard:
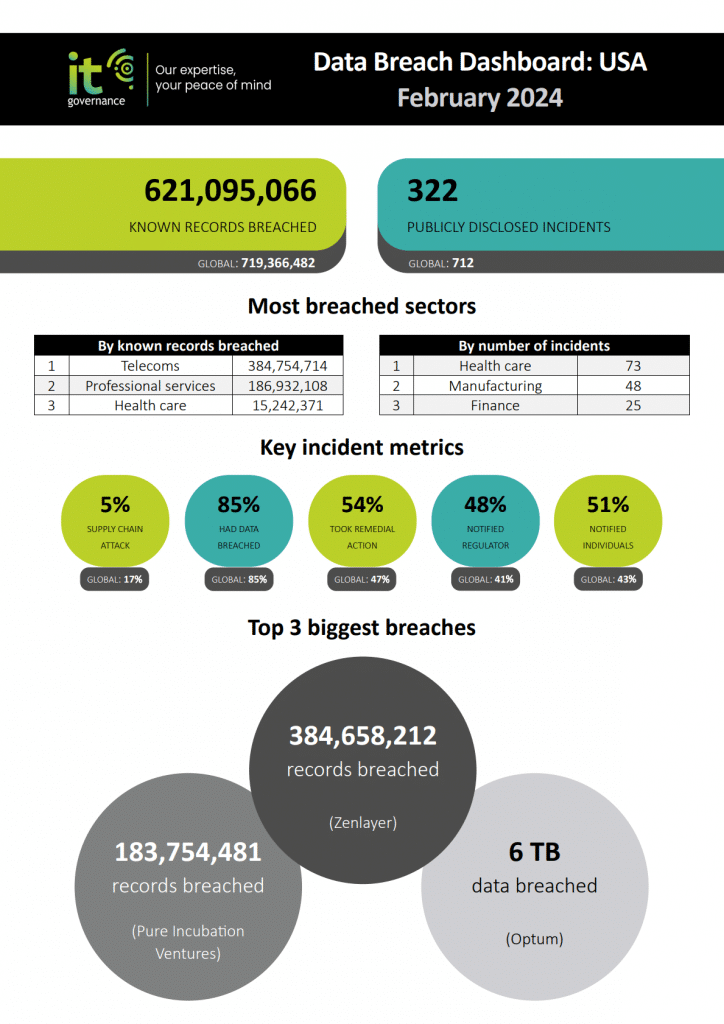
Kyna Kosling March 14, 2024
IT Governance USA’s research found the following for February 2024:
This month, globally, 719,366,482 records were known to be breached – 86% of them were in the USA.
This is unusual. Typically, the USA suffers more incidents than any other country, but these tend to lead to a disproportionately low number of records breached.
This month is different due to two outlier breaches:
*The threat actor provided 100,000 records as a sample.
For a quick, one-page overview of this month’s findings, please use our Data Breach Dashboard:

You can also download this and previous months’ Dashboards as free PDFs here.
This blog provides further analysis of the data we’ve collected. We also provide an annual overview and analyze the longer-term trends in our 2024 overview of publicly disclosed data breaches and cyber attacks in the USA.
You can learn more about our research methodology here.
Note 1: Where ‘around,’ ‘about,’ etc. is reported, we record the rounded number. Where ‘more than,’ ‘at least,’ etc. is reported, we record the rounded number plus one. Where ‘up to,’ etc. is reported, we record the rounded number minus one.
Note 2: For incidents where we only know the file size of the data breached, we use the formula 1 MB = 1 record. Given that we can’t know the exact numbers, as it depends on the types of records included (e.g. pictures and medical histories are considerably larger files than just names and addresses), we err on the side of caution by using this formula. We believe that this underestimates the records breached in most cases, but it is more accurate than not providing a number at all.
Big Breaches: Cybersecurity Lessons for Everyone
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Mar 19 2024
Proof-of-concept (PoC) exploit code for a critical RCE vulnerability (CVE-2024-25153) in Fortra FileCatalyst MFT solution has been published.
Fortra FileCatalyst is an enterprise managed file transfer (MFT) software solution that includes several components: FileCatalyst Direct, Workflow, and Central.
CVE-2024-25153 is a directory traversal vulnerability in FileCatalyst Workflow’s web portal that could allow a remote authenticated threat actor to execute arbitrary code on vulnerable servers.
“A directory traversal within the ‘ftpservlet’ of the FileCatalyst Workflow Web Portal allows files to be uploaded outside of the intended ‘uploadtemp’ directory with a specially crafted POST request. In situations where a file is successfully uploaded to web portal’s DocumentRoot, specially crafted JSP files could be used to execute code, including web shells,” the company noted in the advisory.
The vulnerability was first discovered in August 2023 and patched a few days later in the FileCatalyst version 5.1.6 Build 114, but had no CVE identifier at the time.
The identifier was assigned after Fortra became a CVE Numbering Authority (CNA) in December 2023.
The company and Tom Wedgbury, the security researcher that discovered and reported the flaw, planned its coordinated disclosure in March 2024.
Fortra’s security advisory and Wedgbury’s blog post with technical details and the PoC have been published on Wednesday.
There are currently no indications of the vulnerability being exploited in the wild, but organizations are nevertheless advised to apply the available patch (if they haven’t already).
When a PoC for a critical authentication bypass vulnerability (CVE-2024-0204) in Fortra’s GoAnywhere MFT solution was recently made public, exploit attempts began soon after.
In late January 2023, the Cl0p ransomware group leveraged a zero-day vulnerability (CVE-2023-0669) in the same solution, and stole data of over 130 victim organizations.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory