Aug 21 2008
InfoSec Threats

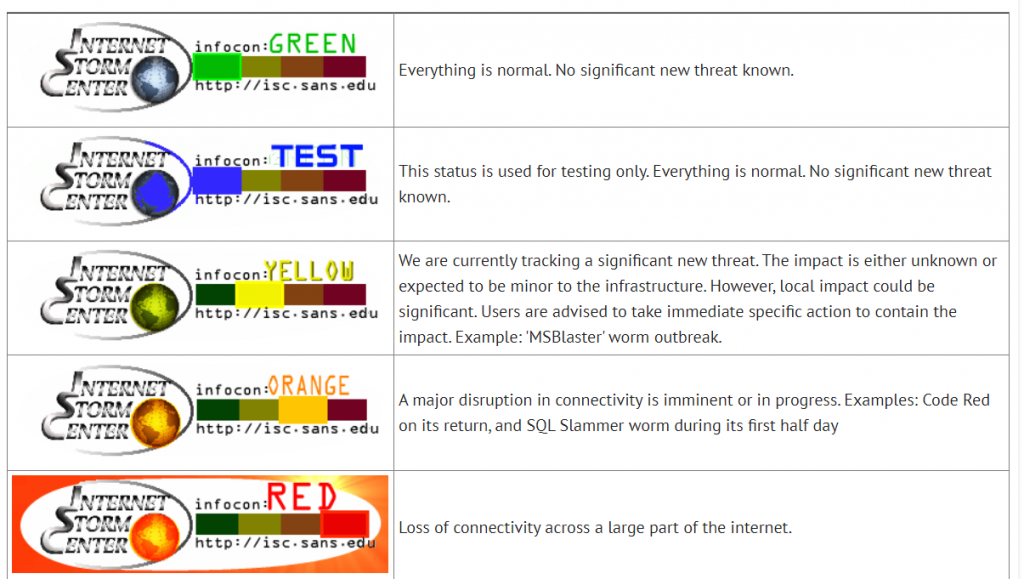
The daily Infocon alert
The daily Infocon alert Live Cyber Attack Threat Map | World’s Biggest Data Breaches & Hacks | CVE Trends | Check if you have an account that has been compromised in a data breach
Security Threats & Safeguard Solutions
DISC online store for recommended InfoSec products
Online Threat Analysis
Trend Micro Virus Scan | Analyze suspicious files | Virus Removal Guides | Email Spoof Test | AbuseIPDB | AlienVault Open Threat Exchange | Shodan records historical open ports and services on the host | Google’s DNS over HTTPS service to do a PTR lookup on the IP | Malware traffic analysis | Open-source Threat Intelligence Feeds | Use a Free IP locator tool | Interactive malware analysis – Any>Run | Find your IP Geolocation | urlscan.io – a sandbox for the web | Have I been pwned | ThreatMiner | DNS Twist Phishing domain scanner | DNSdumpster | Shodan | OSINT Framework | Known Exploited Vulnerabilities Catalog(KEV) – CISA | Threat Actors | ATT&CK® Navigator | World Monitor – Real-Time Global Intelligence Dashboard
The Mozilla Observatory has helped over 240,000 websites by teaching developers, system administrators, and security professionals how to configure their sites safely and securely.
Scan your Site
#SecureCode Journey starts with #CodeSec
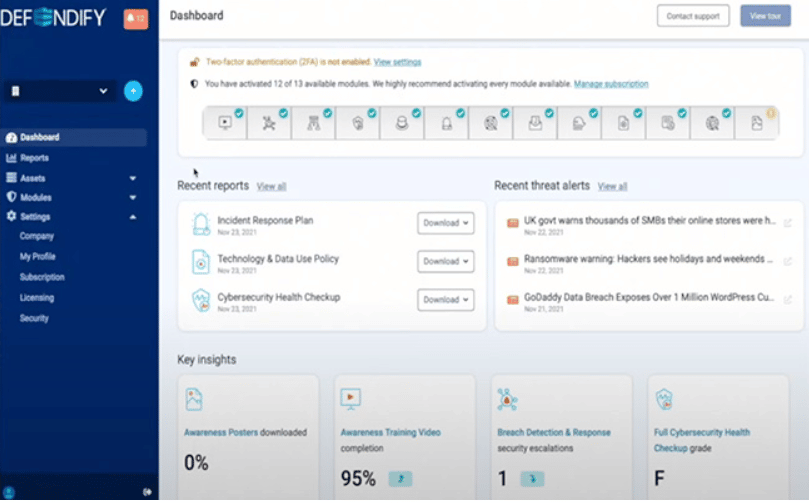
Improve awareness with essential tools from Defendify
PhishTank provides information about phishing on the Internet

Shodan is the world’s first search engine for Internet-connected devices

LookingGlass Threat Map

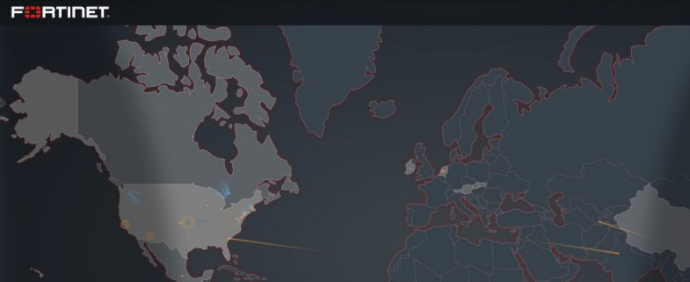
Fortinet Threat Map
More on latest InfoSec Threat titles
Click the InfoSec, Compliance and Risk Management Awareness Quiz, it will open in your browser for a full-screen mode.




