
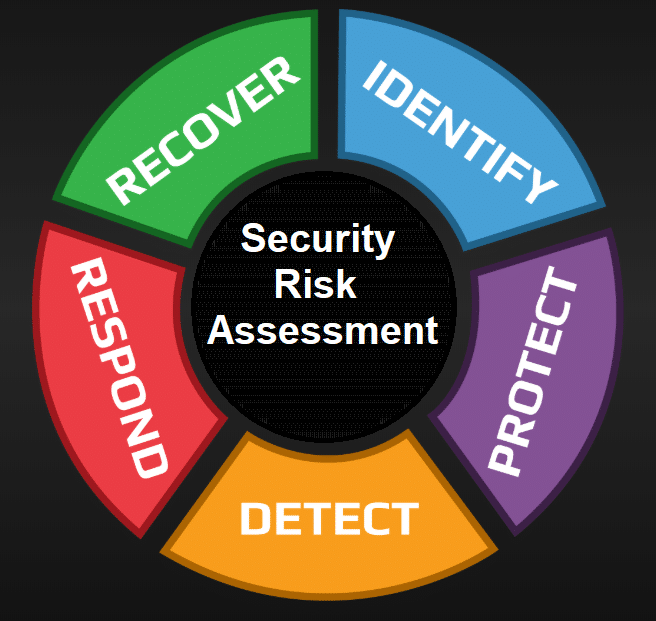
Security Risk Assessments: Choosing the Right Test at the Right Time
Cybersecurity isn’t about running every assessment available—it’s about selecting the right assessment based on your organization’s risk, maturity, and business context. Each security assessment answers a different question across people, process, and technology. When used correctly, they improve resilience, reduce waste, and deliver measurable ROI.
Below is a practical breakdown of the 10 key types of security assessments, their purpose, and when to use them.
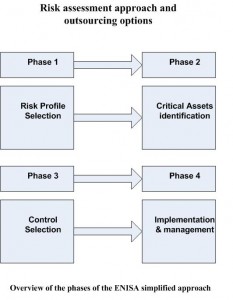
Enterprise Risk Assessment
An enterprise risk assessment provides an organization-wide view of critical assets, threats, and potential business impact.
Purpose: To help executives and boards understand cyber risk in business terms.
When to use: When establishing a security baseline, prioritizing investments, or aligning security strategy with business objectives.
Gap Assessment
A gap assessment compares current controls against frameworks like ISO 27001, SOC 2, PCI DSS, HIPAA, or GDPR.
Purpose: To identify compliance and control gaps.
When to use: When preparing for audits, certifications, customer due diligence, or regulatory reviews.
Vulnerability Assessment
This assessment uses automated scanning and validation to identify known technical weaknesses.
Purpose: To uncover exploitable vulnerabilities and hygiene issues.
When to use: On a recurring basis (monthly or quarterly) to guide patching and configuration management.
Network Penetration Test
A human-led attack simulation focused on networks and hosts.
Purpose: To test how real attackers could compromise systems and move laterally.
When to use: For new environments, after major infrastructure changes, or annually for deep testing.
Application Security Test
This assessment targets applications and APIs for authentication, input validation, business logic, and data handling flaws.
Purpose: To reduce application-layer risk and prevent data breaches.
When to use: Before major releases or for applications handling sensitive data or payments.
Red Team Exercise
A stealthy, goal-driven adversary simulation spanning people, process, and technology.
Purpose: To test detection, response, and organizational readiness—not just prevention.
When to use: When baseline security hygiene is strong and you want to validate end-to-end defenses.
Cloud Security Assessment
A review of cloud configurations, IAM, logging, network design, and security posture.
Purpose: To reduce misconfigurations and cloud-native risks.
When to use: If you’re cloud-first, multi-cloud, or scaling rapidly.
Architecture Review
A forward-looking assessment focused on threat modeling and secure design.
Purpose: To prevent risk before systems are built.
When to use: When designing, replatforming, or integrating major applications or APIs.
Phishing Assessment
Controlled phishing and social engineering simulations targeting users.
Purpose: To measure human risk and security awareness effectiveness.
When to use: When improving security culture or validating training programs with real data.
Incident Response Readiness
Scenario-based exercises that test incident response plans and coordination.
Purpose: To ensure teams can respond effectively under pressure.
When to use: Annually, after major changes, or following a real incident.
Key Takeaway
Security risk assessments are not interchangeable—and they are not checkboxes. Organizations that align assessments to risk maturity, business growth, and regulatory pressure consistently outperform those that test blindly.
- Maturity-driven security beats checkbox security
- Smart assessment selection improves resilience and ROI
- The right test, at the right time, makes security defensible and scalable
A well-designed assessment strategy turns security from a cost center into a risk management advantage.
💡 The real question: Which assessment has delivered the most value in your organization—and why?

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- The AI Governance Quick-Start: Defensible in 10 Days, Not 4 Quarters
- AI Security Tool Evaluation: A Reality Check for CISOs
- How to Answer AI Questions on Your Vendor Assessment (Without Stalling the Deal)
- Most AI Security Tools Won’t Pass an Audit. Here’s a 15-Minute Way to Find Out.
- Most AI Security Tools Won’t Pass an Audit. Here’s a 15-Minute Way to Find Out.








![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=28dcae72-914e-4823-9632-cd34145194b7)

![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=f4c7607a-8a48-4ed1-bba2-9bb41450aa23)



