As enterprise AI adoption accelerates, AI Model Risk Management is rapidly becoming one of the most important disciplines in modern governance, risk, and compliance programs. Organizations are no longer experimenting with isolated AI models — they are deploying AI across critical business operations, customer interactions, analytics, automation, and decision-making systems. With that scale comes a new category of operational, regulatory, and security risk that cannot be ignored.
The market momentum reflects this shift. The AI Model Risk Management market is projected to grow from USD 5.7 billion in 2024 to USD 10.5 billion by 2029, representing a strong CAGR of 12.9%. This growth highlights a broader reality: organizations now recognize that AI innovation without governance creates significant exposure across compliance, cybersecurity, reputational trust, and business resilience.
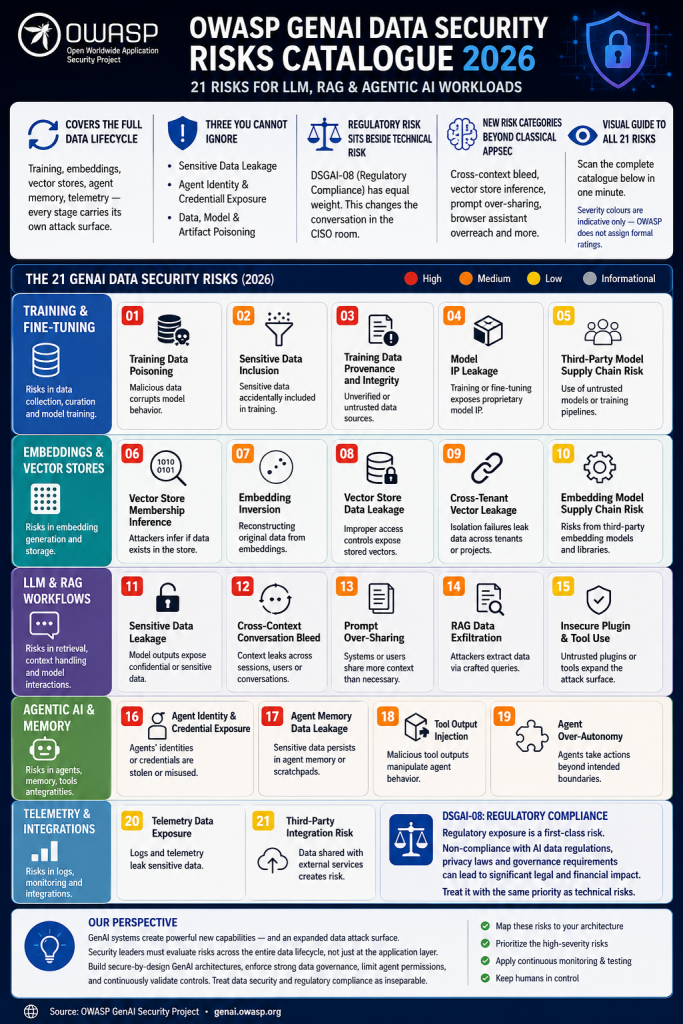
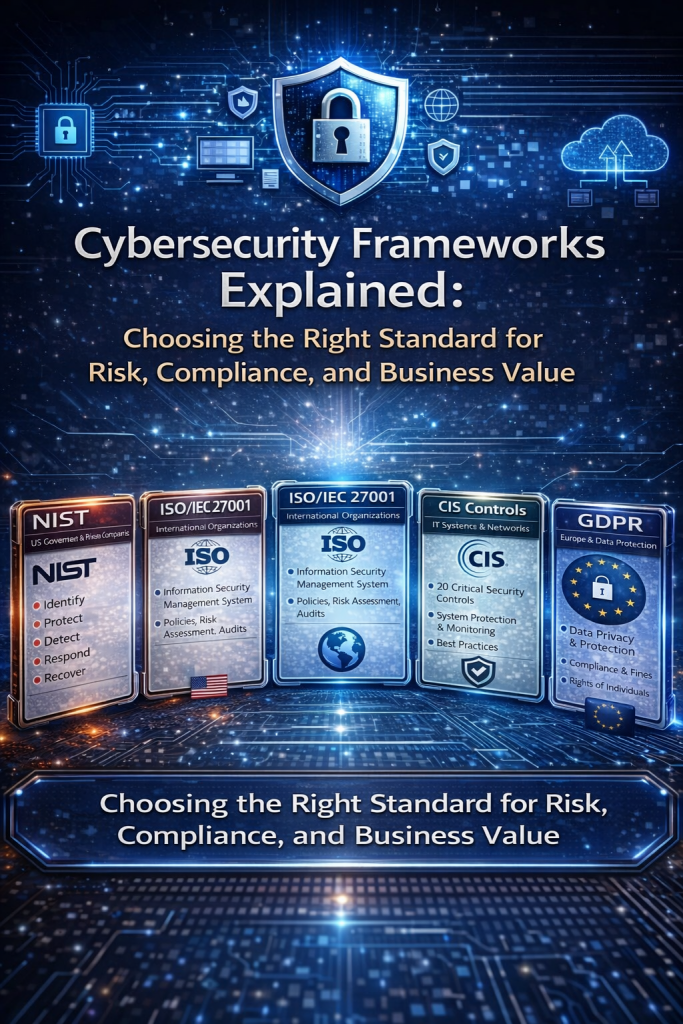
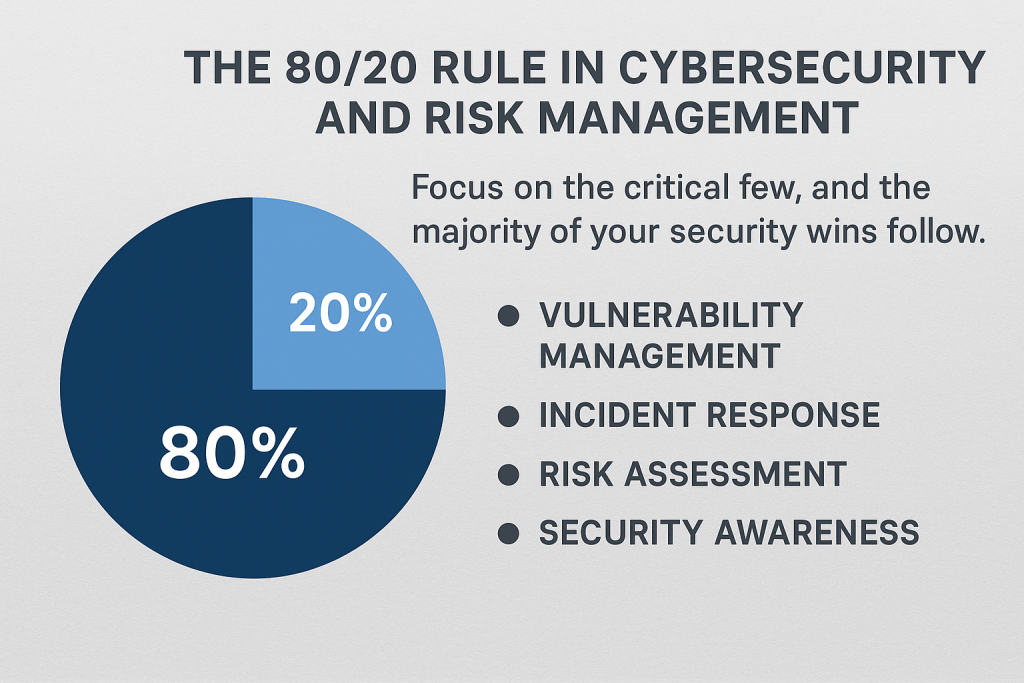
Several major drivers are accelerating investment in AI risk management programs. Security leaders are facing increasing cyber threats targeting AI systems, including model manipulation, prompt injection, data poisoning, and unauthorized model access. At the same time, regulators worldwide are introducing stricter AI governance requirements focused on transparency, accountability, explainability, and ethical AI deployment.
Another major factor is the growing need for automated risk assessment and lifecycle visibility. AI models are dynamic systems that evolve over time, making continuous oversight essential. Without proper controls, organizations risk model drift, inaccurate predictions, biased outcomes, compliance failures, and operational instability that can directly impact business performance and customer trust.
The rise of Generative AI and agentic AI systems is also creating new opportunities and new governance challenges. Organizations are investing heavily in AI-powered decision support, copilots, autonomous workflows, and intelligent automation. These technologies offer enormous business value, but they also introduce complex risks around data privacy, hallucinations, excessive permissions, intellectual property exposure, and accountability gaps.
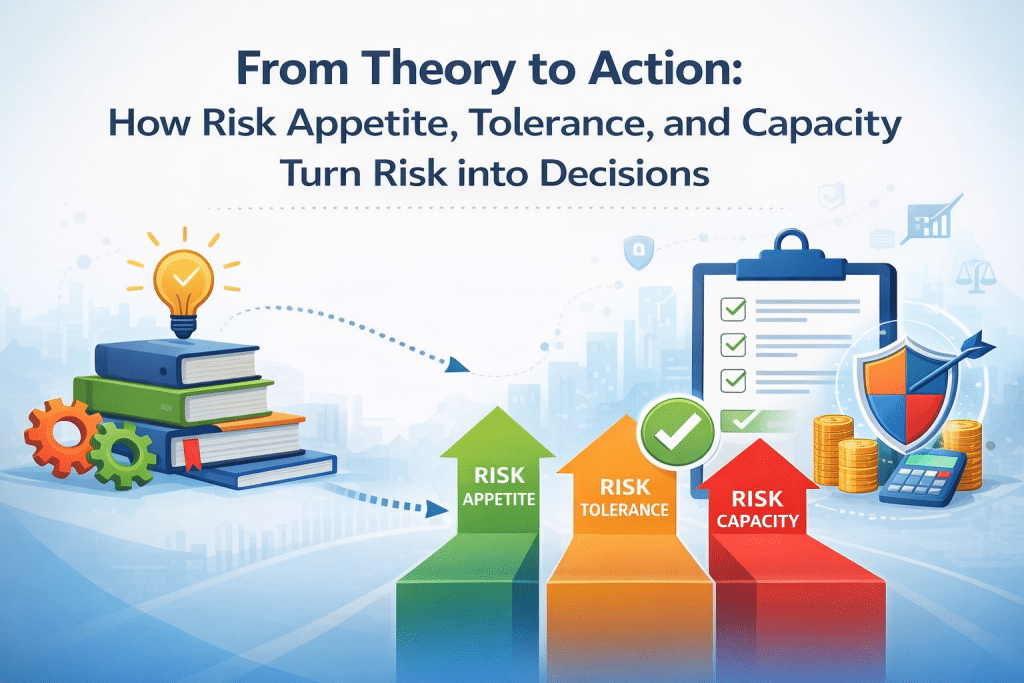
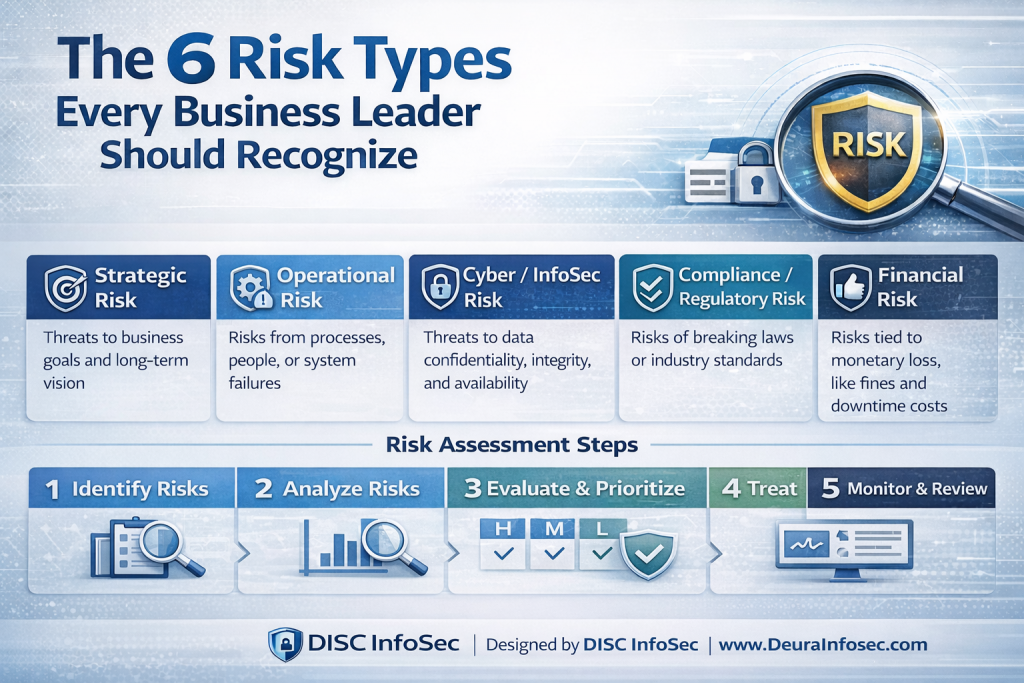
A strong AI Model Risk Management program typically follows a structured five-stage lifecycle approach. The first stage is Identification — understanding what could go wrong. This includes identifying vulnerabilities, ethical concerns, model weaknesses, bias risks, and business impact through assessments, audits, and impact analysis.
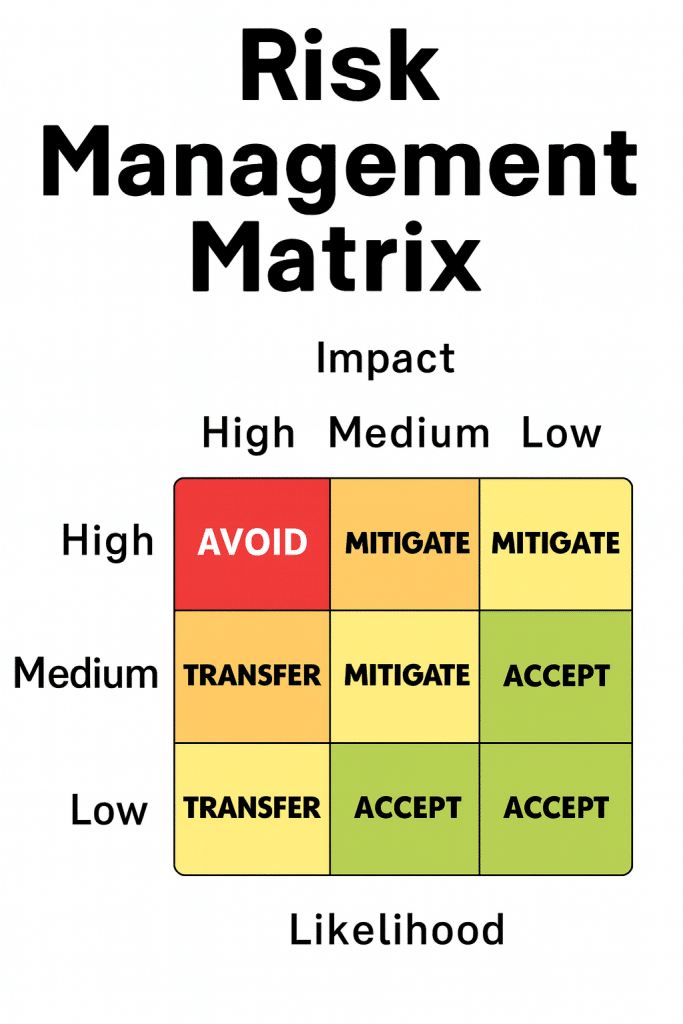
The second stage is Assessment, where organizations evaluate the severity, likelihood, and operational impact of identified risks. This step helps prioritize remediation efforts while measuring model reliability, explainability, resilience, and alignment with business objectives and regulatory expectations.
The third stage is Mitigation, which focuses on reducing risk through safeguards and controls. Organizations may retrain models, improve data quality, implement human oversight, strengthen explainability, apply access controls, and establish governance guardrails to minimize exposure and improve trustworthiness.
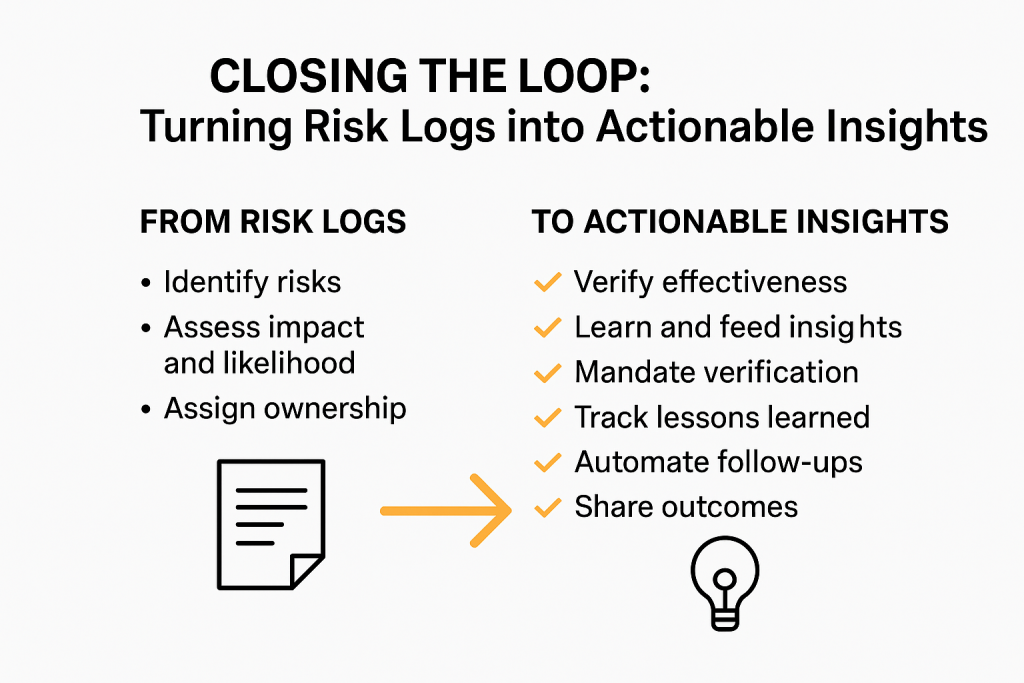
The fourth and fifth stages — Monitoring and Governance — are where mature AI programs separate themselves from basic AI deployments. Continuous monitoring helps detect model drift, abnormal behavior, and emerging threats in real time, while governance ensures policies, accountability, compliance obligations, and executive oversight remain active throughout the AI lifecycle.
Effective AI Model Risk Management ultimately delivers measurable business value. It reduces bias, strengthens trust in AI-driven decisions, improves compliance readiness, minimizes financial and reputational exposure, and enables organizations to scale AI responsibly with confidence. In today’s environment, AI governance is no longer a theoretical discussion — it is becoming a board-level business requirement.
My perspective: Many organizations are still approaching AI governance as a documentation exercise instead of an operational discipline. The companies that will succeed with AI over the next five years will be the ones that treat AI governance like cybersecurity — continuous, measurable, risk-based, and integrated directly into business operations. AI risk management is no longer optional; it is becoming the foundation for trustworthy and sustainable AI adoption.
#AI #AIGovernance #AIRiskManagement #CyberSecurity #GenAI #ResponsibleAI #AICompliance #ModelRiskManagement #AISecurity #Governance #RiskManagement #AgenticAI #DataGovernance #TrustworthyAI #DISCInfoSec
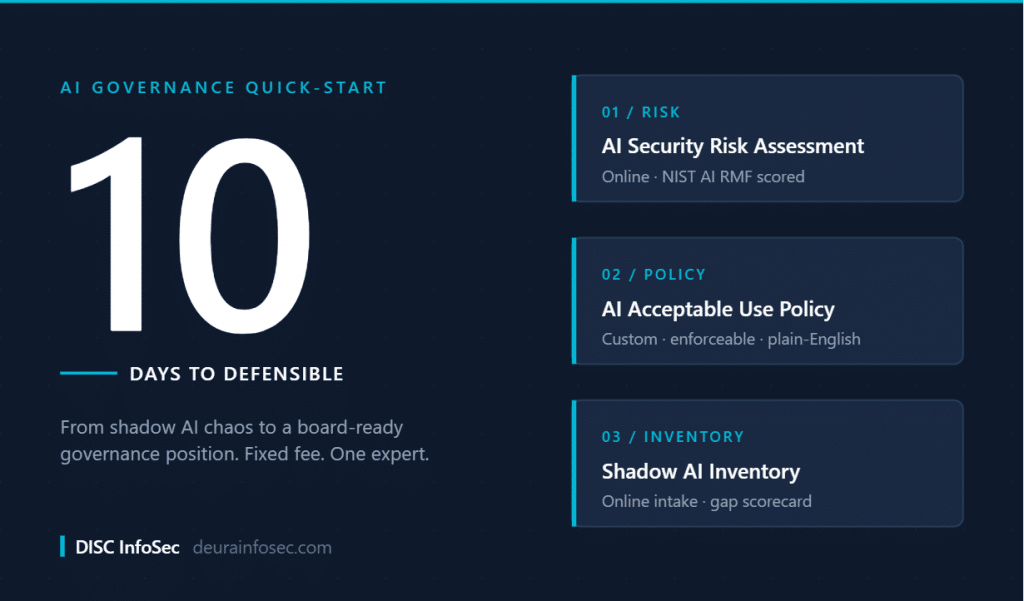
The AI Governance Quick-Start: Defensible in 10 Days, Not 4 Quarters
DISC InfoSec is an active ISO 42001 implementer and PECB Authorized Training Partner specializing in AI governance for B2B SaaS and financial services organizations.
AI Vulnerability Scorecard: Discover Your AI Attack Surface Before Attackers Do
Your Shadow AI Problem Has a Name-And Now It Has a Score
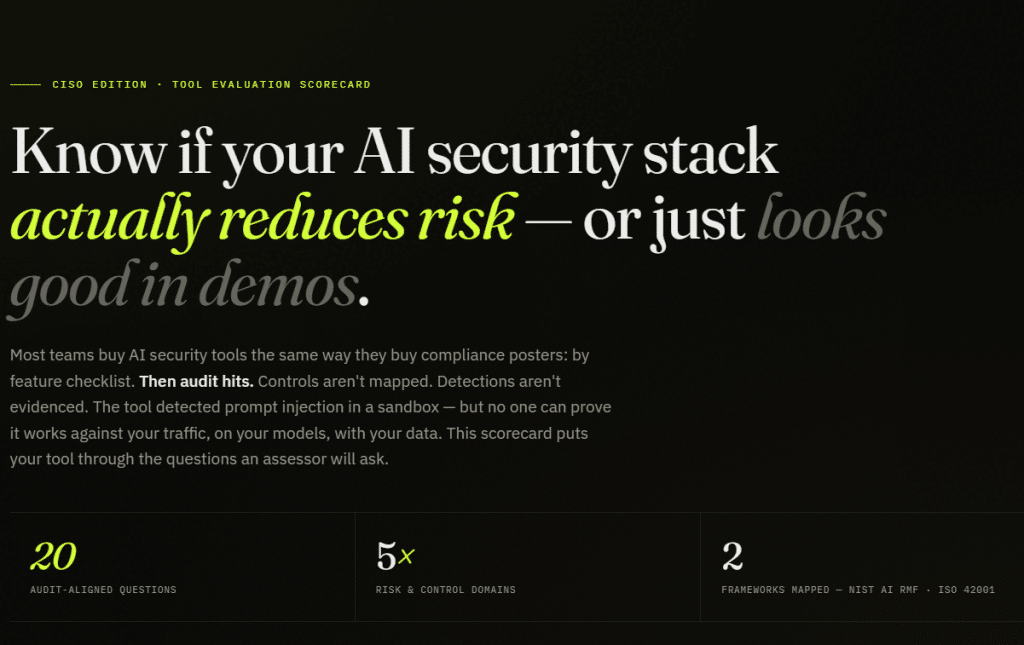
Most AI Security Tools Won’t Pass an Audit. Here’s a 15-Minute Way to Find Out.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
- AI Model Risk Management Is Becoming the Foundation of Enterprise AI Governance
- Sun Tzu for the AI Governance Era: 7 Strategic Rules for InfoSec and Compliance Leaders
- Your Shadow AI Inventory Is Wrong. Here’s a Free Way to Fix It.
- The AI Agent Identity Crisis Has Already Started
- OWASP 2026 GenAI Risk Catalogue Signals a New Era of AI Security Governance