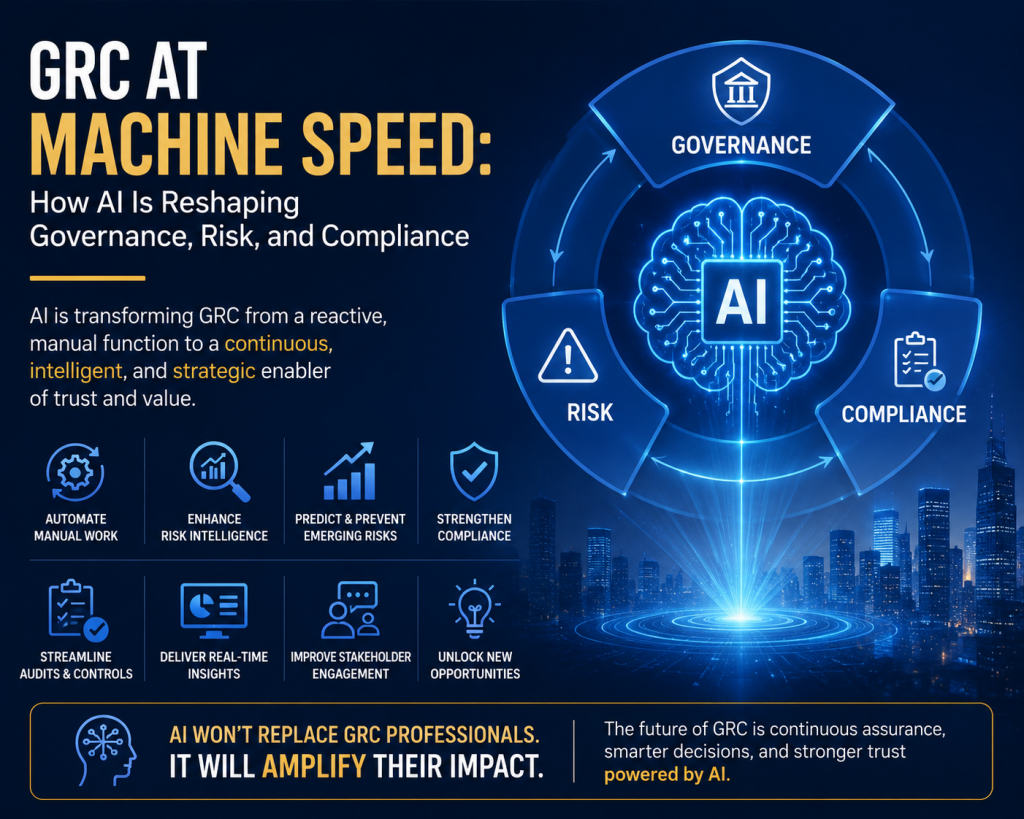
AI is not simply another technology that GRC teams will govern — it will fundamentally reshape how GRC is practiced, measured, and delivered.
From an AI governance perspective, the biggest shift over the next few years is that GRC will move from periodic, documentation-heavy activities toward continuous assurance. Traditional models built around annual assessments, point-in-time audits, and manually maintained control libraries are increasingly misaligned with AI systems that learn, adapt, and change rapidly. Governance programs will need near real-time monitoring, automated evidence collection, and dynamic risk scoring to keep pace with AI-enabled businesses.
AI will also force GRC teams to rethink what risk means. Historically, cybersecurity, privacy, operational, and regulatory risks were often managed in separate silos. AI collapses these boundaries. A single AI system can simultaneously create security risks, bias risks, privacy concerns, intellectual property exposure, regulatory obligations, and reputational damage. Future GRC programs will need integrated risk models that account for technical, legal, ethical, and business impacts together rather than independently.
The role of GRC professionals is also likely to evolve significantly. Much of today’s work — control mapping, evidence collection, questionnaire reviews, policy maintenance, risk reporting, and audit preparation — is highly automatable. The value of future practitioners will shift away from administration and toward interpretation, governance design, and decision support. Organizations will increasingly expect GRC teams to explain not only whether AI systems comply with requirements, but whether they are trustworthy, resilient, and aligned with business objectives.
Another major change is that AI itself becomes both the subject and operator of governance. Organizations will use AI agents to perform risk analysis, review controls, monitor compliance, generate policies, and identify anomalies. This creates a recursive challenge: organizations must govern the AI systems that are helping govern the organization. Oversight mechanisms, human review checkpoints, and assurance controls around AI-generated outputs will become critical.
Regulatory pressure will accelerate this transformation. New AI-focused requirements are emerging globally, but organizations cannot rely solely on regulations to define good governance. Compliance-based thinking alone will struggle because AI technology evolves faster than legislation. Forward-looking organizations will need governance models based on principles such as accountability, transparency, explainability, resilience, and human oversight.
One overlooked area is evidence and auditability. AI systems often operate as probabilistic systems rather than deterministic ones. Traditional audit approaches designed for fixed software systems may not adequately assess AI outcomes, model drift, or decision quality. Future audits may increasingly examine datasets, model lifecycle controls, prompt management, human oversight processes, and monitoring mechanisms rather than only reviewing policies and procedures.
The organizations that adapt fastest will likely treat GRC less as a control function and more as an engineering discipline. Governance controls will increasingly be embedded into development pipelines, procurement workflows, cloud infrastructure, and AI deployment processes rather than documented after implementation.
My perspective: AI is unlikely to eliminate GRC functions — but it will compress manual work, increase the speed of decision-making, and raise expectations for business alignment. The biggest risk for GRC teams is not automation itself; it is remaining dependent on slow, reactive governance models while businesses adopt AI at machine speed. Future GRC leaders will need to become part governance expert, part technologist, and part business strategist.
The GRC Function Is Changing: Are You Ready for AI-Native Governance?
GRC Engineering Is the Future of Cloud Compliance
The AI Governance Quick-Start: Defensible in 10 Days, Not 4 Quarters
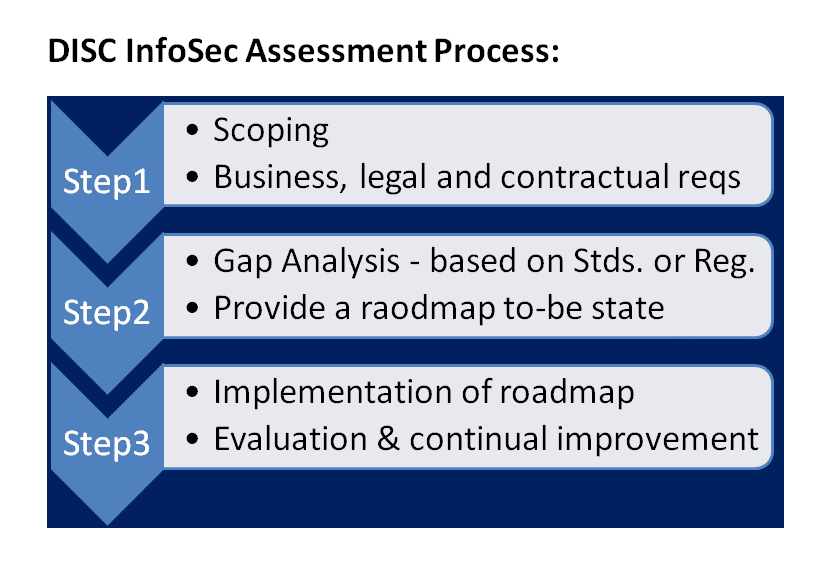
DISC InfoSec is an active ISO 42001 implementer and PECB Authorized Training Partner specializing in AI governance for B2B SaaS and financial services organizations.
AI Vulnerability Scorecard: Discover Your AI Attack Surface Before Attackers Do
Your Shadow AI Problem Has a Name-And Now It Has a Score
Most AI Security Tools Won’t Pass an Audit. Here’s a 15-Minute Way to Find Out.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
- AI Can Pentest Your Network Now. That’s Not the Risk You Should Worry About
- GRC at Machine Speed: How AI Is Reshaping Governance, Risk, and Compliance
- Building AI Governance That Actually Works: From Ethics to the Exam Room
- Corporate Visibility as an Attack Surface: Managing Risk in the AI Era
- GRC Engineering Is the Future of Cloud Compliance