1
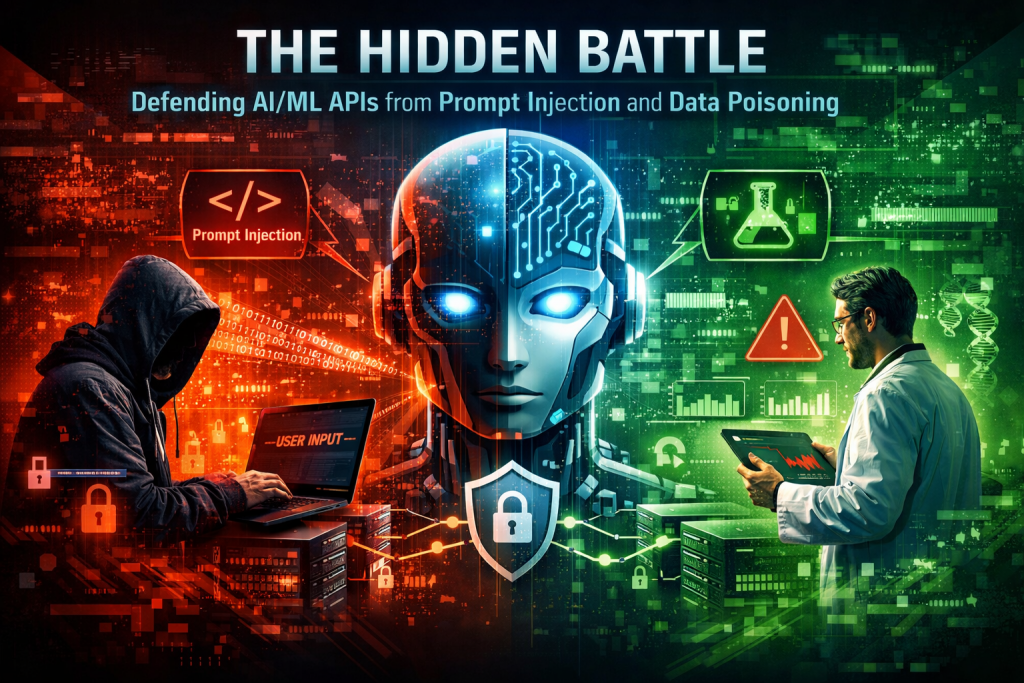
Protecting AI and ML model–serving APIs has become a new and critical security frontier. As organizations increasingly expose Generative AI and machine learning capabilities through APIs, attackers are shifting their focus from traditional infrastructure to the models themselves.
2
AI red teams are now observing entirely new categories of attacks that did not exist in conventional application security. These threats specifically target how GenAI and ML models interpret input and learn from data—areas where legacy security tools such as Web Application Firewalls (WAFs) offer little to no protection.
3
Two dominant threats stand out in this emerging landscape: prompt injection and data poisoning. Both attacks exploit fundamental properties of AI systems rather than software vulnerabilities, making them harder to detect with traditional rule-based defenses.
4
Prompt injection attacks manipulate a Large Language Model by crafting inputs that override or bypass its intended instructions. By embedding hidden or misleading commands in user prompts, attackers can coerce the model into revealing sensitive information or performing unauthorized actions.
5
This type of attack is comparable to slipping a secret instruction past a guard. Even a well-designed AI can be tricked into ignoring safeguards if user input is not strictly controlled and separated from system-level instructions.
6
Effective mitigation starts with treating all user input as untrusted code. Clear delimiters must be used to isolate trusted system prompts from user-provided text, ensuring the model can clearly distinguish between authoritative instructions and external input.
7
In parallel, the principle of least privilege is essential. AI-serving APIs should operate with minimal access rights so that even if a model is manipulated, the potential damage—often referred to as the blast radius—remains limited and manageable.
8
Data poisoning attacks, in contrast, undermine the integrity of the model itself. By injecting corrupted, biased, or mislabeled data into training datasets, attackers can subtly alter model behavior or implant hidden backdoors that trigger under specific conditions.
9
Defending against data poisoning requires rigorous data governance. This includes tracking the provenance of all training data, continuously monitoring for anomalies, and applying robust training techniques that reduce the model’s sensitivity to small, malicious data manipulations.
10
Together, these controls shift AI security from a perimeter-based mindset to one focused on model behavior, data integrity, and controlled execution—areas that demand new tools, skills, and security architectures.
My Opinion
AI/ML API security should be treated as a first-class risk domain, not an extension of traditional application security. Organizations deploying GenAI without specialized defenses for prompt injection and data poisoning are effectively operating blind. In my view, AI security controls must be embedded into governance, risk management, and system design from day one—ideally aligned with standards like ISO 27001, ISO 42001 and emerging AI risk frameworks—rather than bolted on after an incident forces the issue.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- AI Model Risk Management Is Becoming the Foundation of Enterprise AI Governance
- Sun Tzu for the AI Governance Era: 7 Strategic Rules for InfoSec and Compliance Leaders
- Your Shadow AI Inventory Is Wrong. Here’s a Free Way to Fix It.
- The AI Agent Identity Crisis Has Already Started
- OWASP 2026 GenAI Risk Catalogue Signals a New Era of AI Security Governance