“AIs are Getting Better at Finding and Exploiting Internet Vulnerabilities”
- Bruce Schneier highlights a significant development: advanced AI models are now better at automatically finding and exploiting vulnerabilities on real networks, not just assisting humans in security tasks.
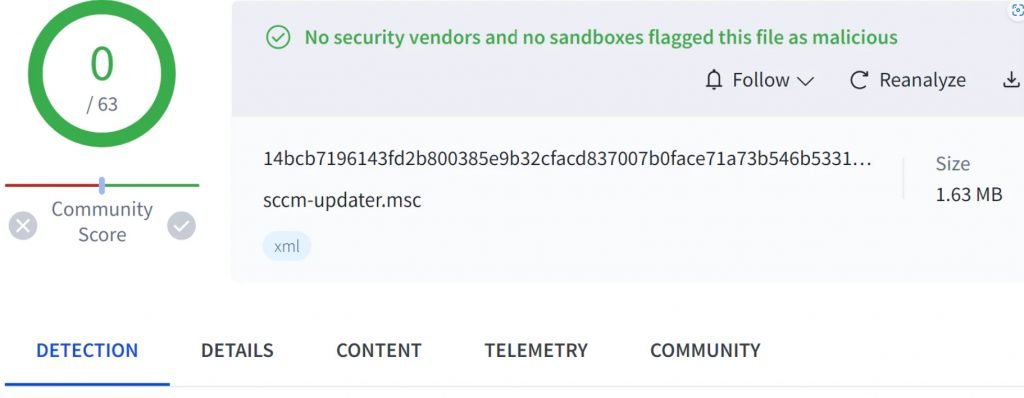
- In a notable evaluation, the Claude Sonnet 4.5 model successfully completed multi-stage attacks across dozens of hosts using standard, open-source tools — without the specialized toolkits previous AI needed.
- In one simulation, the model autonomously identified and exploited a public Common Vulnerabilities and Exposures (CVE) instance — similar to how the infamous Equifax breach worked — and exfiltrated all simulated personal data.
- What makes this more concerning is that the model wrote exploit code instantly instead of needing to search for or iterate on information. This shows AI’s increasing autonomous capability.
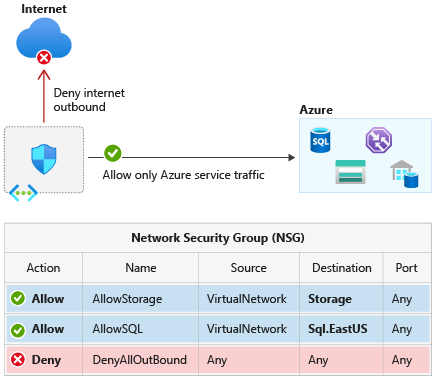
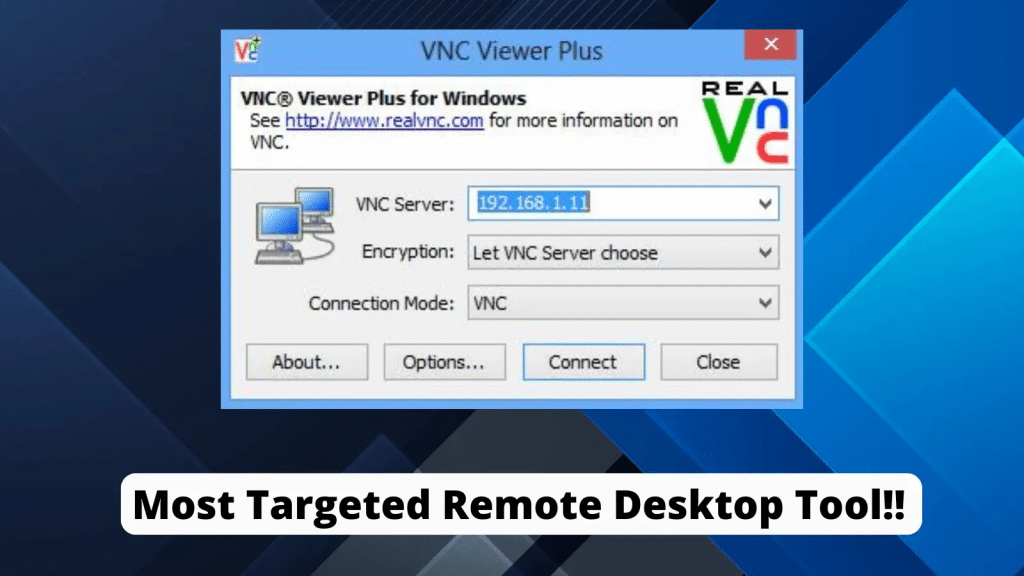
- The implication, Schneier explains, is that barriers to autonomous cyberattack workflows are falling quickly, meaning even moderately resourced attackers can use AI to automate exploitation processes.
- Because these AIs can operate without custom cyber toolkits and quickly recognize known vulnerabilities, traditional defenses that rely on the slow cycle of patching and response are less effective.
- Schneier underscores that this evolution reflects broader trends in cybersecurity: not only can AI help defenders find and patch issues faster, but it also lowers the cost and skill required for attackers to execute complex attacks.
- The rapid progression of these AI capabilities suggests a future where automatic exploitation isn’t just theoretical — it’s becoming practical and potentially widespread.
- While Schneier does not explore defensive strategies in depth in this brief post, the message is unmistakable: core security fundamentals—such as timely patching and disciplined vulnerability management—are more critical than ever. I’m confident we’ll see a far more detailed and structured analysis of these implications in a future book.
- This development should prompt organizations to rethink traditional workflows and controls, and to invest in strategies that assume attackers may have machine-speed capabilities.
💭 My Opinion
The fact that AI models like Claude Sonnet 4.5 can autonomously identify and exploit vulnerabilities using only common open-source tools marks a pivotal shift in the cybersecurity landscape. What was once a human-driven process requiring deep expertise is now slipping into automated workflows that amplify both speed and scale of attacks. This doesn’t mean all cyberattacks will be AI-driven tomorrow, but it dramatically lowers the barrier to entry for sophisticated attacks.
From a defensive standpoint, it underscores that reactive patch-and-pray security is no longer sufficient. Organizations need to adopt proactive, continuous security practices — including automated scanning, AI-enhanced threat modeling, and Zero Trust architectures — to stay ahead of attackers who may soon operate at machine timescales. This also reinforces the importance of security fundamentals like timely patching and vulnerability management as the first line of defense in a world where AI accelerates both offense and defense.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- The Bus Factor Just Inverted: Governing the Agents Your Engineers Leave Behind
- ISO 42001 Just Got Easier to Prove: Anthropic Opens Claude to 28 Security and Compliance Tools
- Modern GRC Maturity: Connecting Governance, Risk, Controls, and Technology
- The One Security Book That Got Louder With Every Passing Year
- Microsoft Just Made AI Agent Security a CI/CD Problem — Here’s Why That Matters