The One Security Book That Got Louder With Every Passing Year
Why Click Here to Kill Everybody by Bruce Schneier belongs on every CISO’s, CAIO’s, and board director’s shelf — in that order
There are security books you read once and shelve. And then there is Bruce Schneier’s Click Here to Kill Everybody, which somehow becomes more relevant every quarter you wait to read it.
Schneier wrote it in 2018. Re-read it in 2026 and you will swear he had a working time machine.
If you are a security or AI governance leader and this book is not already dog-eared on your desk, this post is your nudge. Here is why I keep buying copies for clients, board members, and skeptical CFOs.
The thesis, in one sentence
When every “thing” becomes a computer — your car, your insulin pump, your factory floor, your municipal water system, and now your AI agents — every security flaw becomes a safety flaw.
That sounds obvious until you sit with it. Then it becomes terrifying.
Schneier coined the term “Internet+” to describe the merger of the digital and physical worlds. The internet used to steal your data. The Internet+ can steal your data, crash your car, shut off your pacemaker, and disrupt your power grid. Same vulnerabilities. Vastly different consequences.
This is not hypothetical. It is the world we have already built. Schneier just had the courage — and the receipts — to name it first.
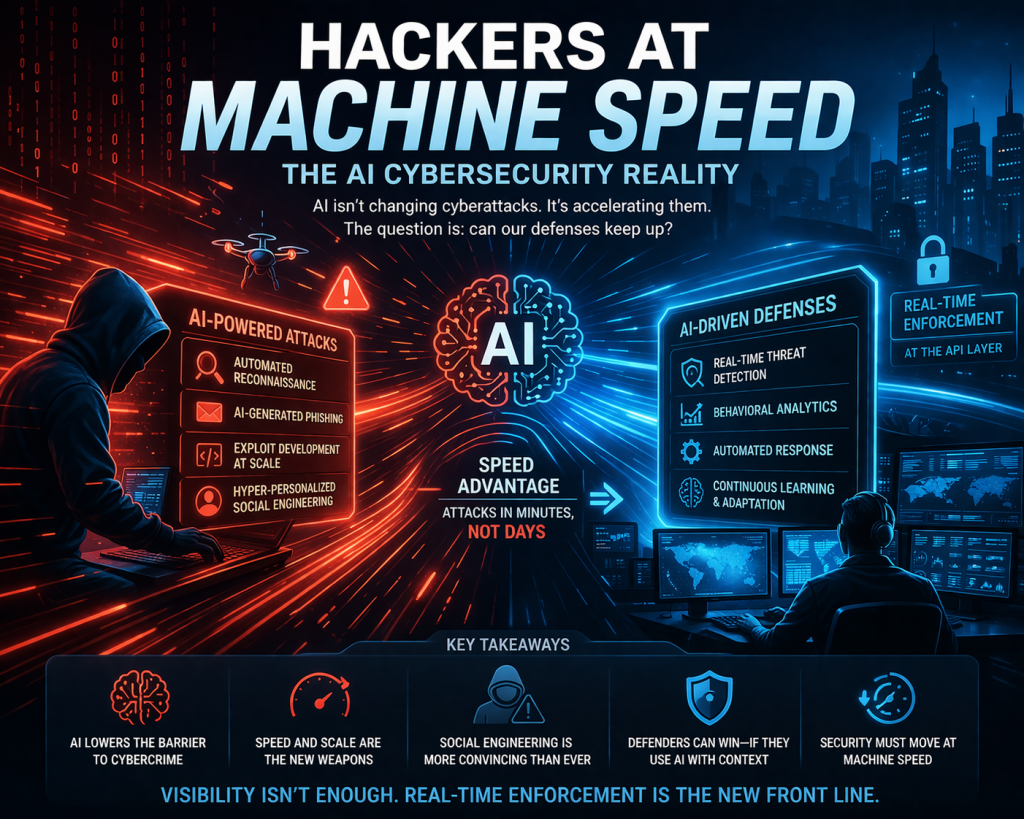
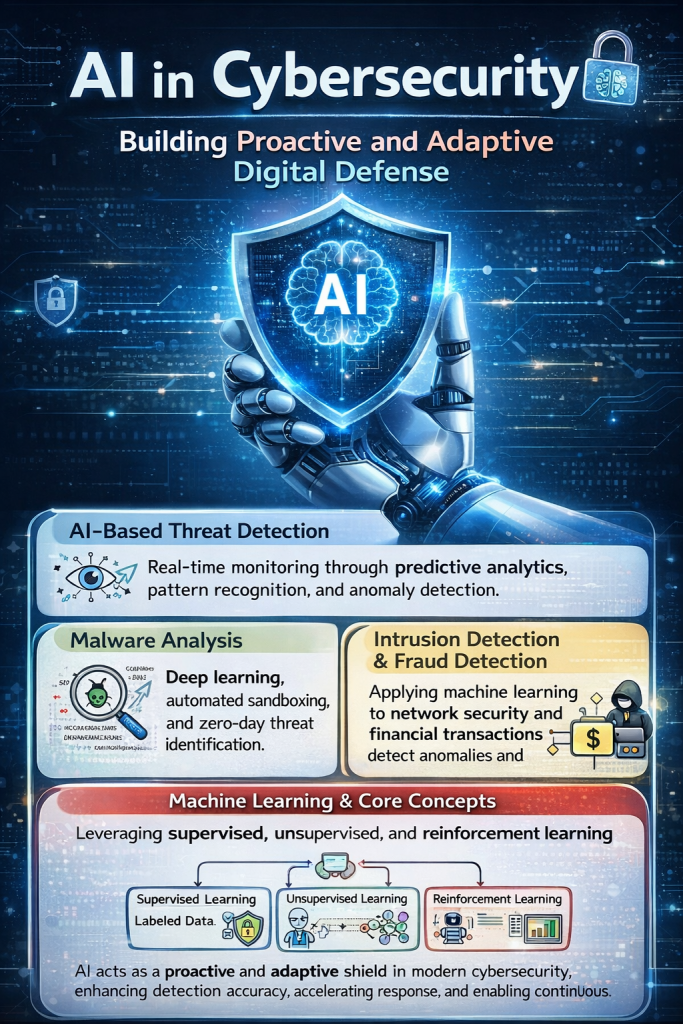
Why this book hits harder in the age of AI
Here is the part that should land for anyone working in AI governance right now.
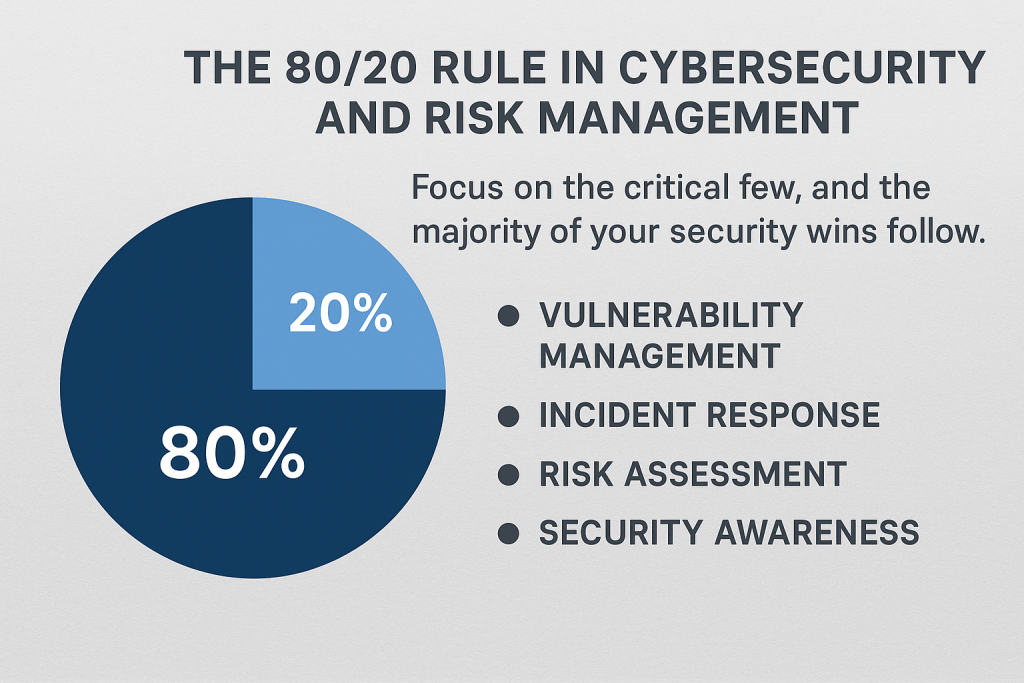
Schneier’s core argument is about the capability-consequence gap: we deployed connectivity faster than we deployed the governance, accountability, and policy machinery needed to manage its consequences.
Sound familiar?
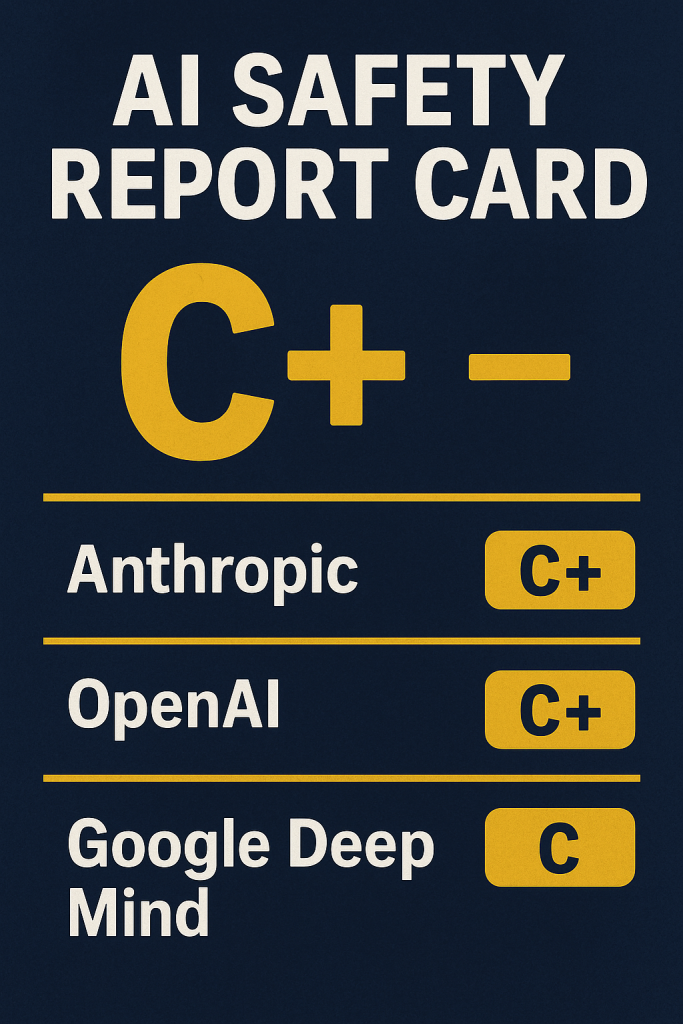
Replace “IoT” with “generative AI” and “Internet+” with “agentic AI workflows,” and you are reading the playbook for the next five years of enterprise risk. The same market failures Schneier diagnosed — externalized costs, opaque supply chains, asymmetry between attackers and defenders, vendors who treat security as somebody else’s problem — are all reappearing in AI procurement decks today.
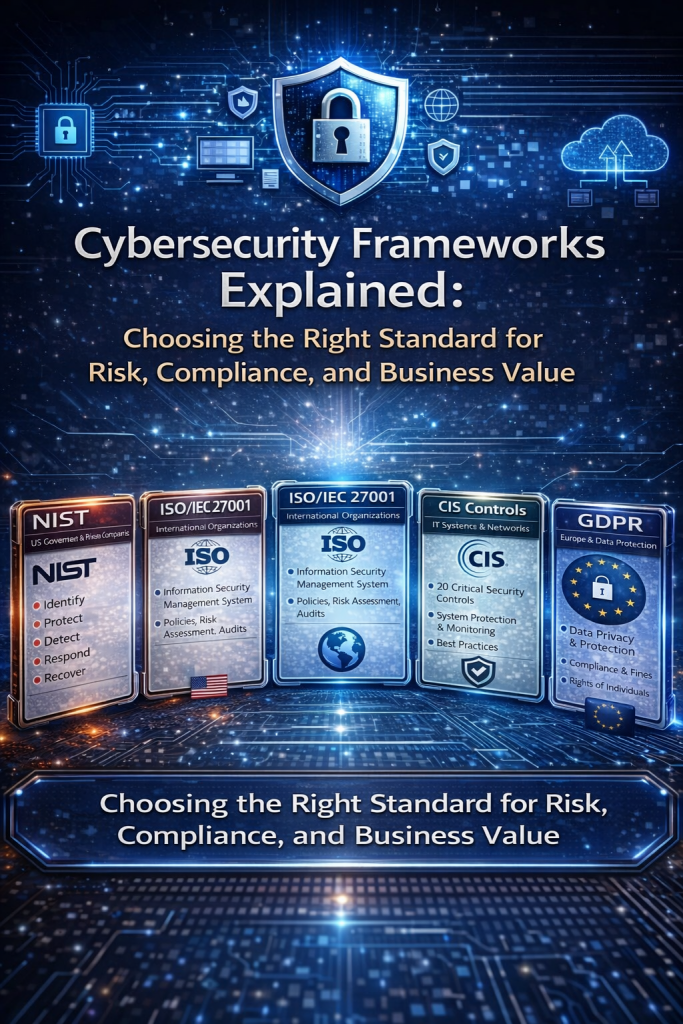
If you are implementing ISO 42001, building an AI risk program, or sitting in a room arguing about model approval workflows, this book gives you the moral and economic vocabulary you have been missing.
What you actually get when you read it
This is not a 400-page lecture. Schneier writes like an engineer who learned to talk to lawyers and then learned to talk to everyone else. The book is structured to be useful to three very different readers:
For the technical reader, it is a clear-eyed inventory of why secure-by-default is so hard at scale, why patching is broken, and why software liability has been ducked for thirty years.
For the policy reader, it is one of the most coherent arguments ever published for why cybersecurity is a public-policy problem, not a private one — and what regulation that actually works might look like.
For the executive reader, it is the most useful translation layer you will find between “our threat model” and “our fiduciary duty.” Hand it to a board member who keeps asking why the company can’t just buy a tool to fix this.
The five ideas you will quote for the rest of your career
Without spoiling the book, here are the frames I borrow from Schneier almost weekly with clients:
- Security is a property of systems, not products. You cannot bolt it on at the end. (Try telling that to a vendor selling “AI safety” as a feature flag.)
- Cheap, networked, and insecure beats expensive and safe — every time — until policy changes the math.
- The attacker only has to be right once. The defender has to be right always. Asymmetry is the entire game.
- Markets do not fix safety problems. They never have. Aviation, pharmaceuticals, automobiles, food — every safety regime was paid for in bodies before it was paid for in regulation.
- Resilience beats prevention. Build systems that fail well, because they will fail.
If any of those land hard, you are ready for the book.
Who this book is for (and who it really is not)
Read it if you are:
- A CISO trying to articulate cyber-physical risk to a board that still thinks “cyber” means email phishing.
- A Chief AI Officer or vCAIO building governance for systems whose blast radius extends into the physical and economic world.
- An auditor, consultant, or implementer working on ISO 27001, ISO 42001, NIST CSF, or the EU AI Act — and looking for the why behind the controls.
- A founder shipping connected hardware or AI agents who would rather understand the coming regulation than be surprised by it.
- A policymaker, journalist, or director who wants one book that explains the whole landscape without dumbing it down.
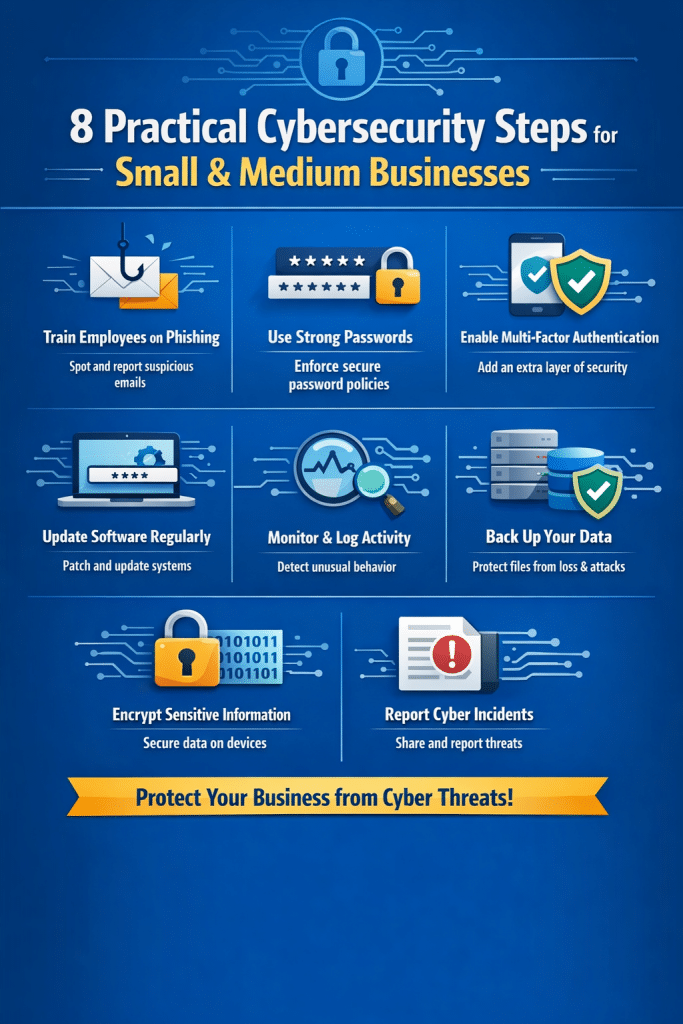
Skip it if you are: looking for tactical hardening checklists or a CISSP study guide. This is a strategy book, not a runbook.
My honest take after twenty years in the trenches
I have spent two decades implementing security and governance programs across KPMG, IBM, Intel/McAfee, and now in my own practice — most recently as lead implementer for one of the first ISO 42001 certifications in the financial-data-room space. I have read every framework worth reading and most of the ones that are not.
Click Here to Kill Everybody is one of a very small number of books I re-read every year. Not because the technology stays the same — it absolutely does not — but because the frame Schneier built has aged better than almost any framework I have audited against.
The risks have gotten bigger. The systems have gotten more connected. The governance still lags. Schneier saw it. Read what he wrote.
Get the book
You can find Click Here to Kill Everybody: Security and Survival in a Hyper-connected World by Bruce Schneier wherever you buy books. Hardcover, paperback, audiobook — all worth it. The audiobook is particularly good for a commute or a long flight if you spend your day reading PDFs already.
If you want to discuss how the ideas in this book translate into a working AI governance and ISO 42001 program for your organization — including the parts Schneier could only gesture at in 2018 — that is exactly the work we do at DISC InfoSec.
info@deurainfosec.com
Financial data rooms are the “hard mode” of compliance — if it works there, it works anywhere.
Disc is the Principal Consultant at DISC InfoSec, a boutique AI governance and cybersecurity firm and PECB Authorized Training Partner for ISO 27001 and ISO 42001. He served as lead implementer and internal auditor for ShareVault’s recent ISO 42001 certification.
The AI Governance Quick-Start: Defensible in 10 Days, Not 4 Quarters
DISC InfoSec is an active ISO 42001 implementer and PECB Authorized Training Partner specializing in AI governance for B2B SaaS and financial services organizations.
AI Vulnerability Scorecard: Discover Your AI Attack Surface Before Attackers Do
Your Shadow AI Problem Has a Name-And Now It Has a Score
Most AI Security Tools Won’t Pass an Audit. Here’s a 15-Minute Way to Find Out.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
- AI Can Pentest Your Network Now. That’s Not the Risk You Should Worry About
- GRC at Machine Speed: How AI Is Reshaping Governance, Risk, and Compliance
- Building AI Governance That Actually Works: From Ethics to the Exam Room
- Corporate Visibility as an Attack Surface: Managing Risk in the AI Era
- GRC Engineering Is the Future of Cloud Compliance