A UAE-based startup named Advanced Security Solutions has entered the cybersecurity scene with a bold proposition: offering up to $20 million for zero-day exploits that can compromise any smartphone via a single text message. This figure places it among the highest publicly known bounties in the exploit market, signaling aggressive intent and deep pockets.
💰 Bounty Breakdown
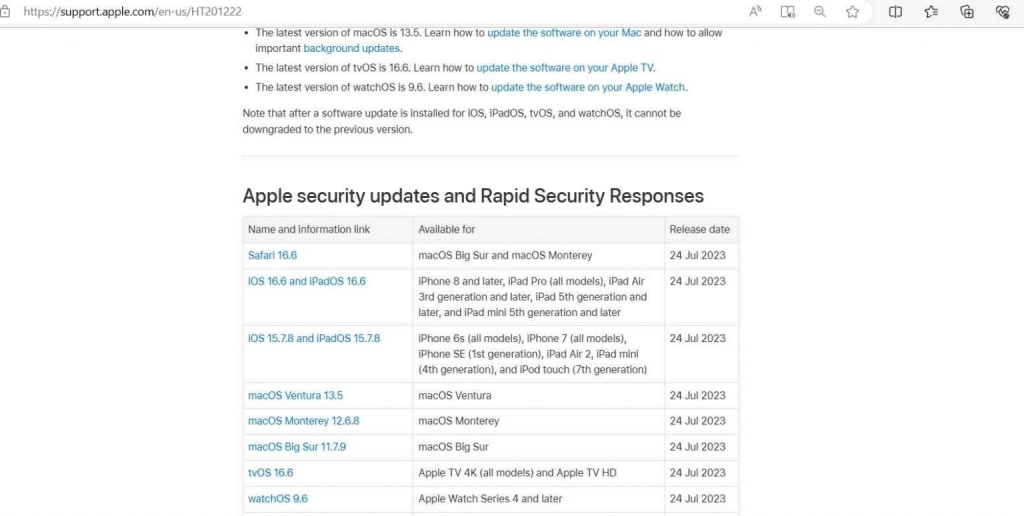
The company’s bounty structure includes $15 million for Android and iPhone exploits, $10 million for Windows vulnerabilities, and smaller amounts for browser-based flaws—$5 million for Chrome and $1 million for Safari and Edge. Messaging apps like WhatsApp, Telegram, and Signal are also targeted, with $2 million offered for each. These figures reflect a growing demand and rising prices in the zero-day ecosystem.
🧩 Mystery Behind the Curtain
Despite its high-profile launch, Advanced Security Solutions remains opaque. The company has not disclosed its ownership, funding sources, or client list. Its website claims partnerships with over 25 government and intelligence agencies and boasts a team of veterans from elite intelligence units and private military contractors. However, it avoids any mention of ethical or legal boundaries.
🧠 Expert Opinions and Market Context
Security researchers familiar with the zero-day market suggest the offered prices are realistic, though one expert noted that $20 million might be considered “low” depending on the buyer’s ethics. The same expert cautioned against selling exploits to entities that conceal their identity, emphasizing the risks of dealing with anonymous buyers.
📈 Evolution of the Exploit Economy
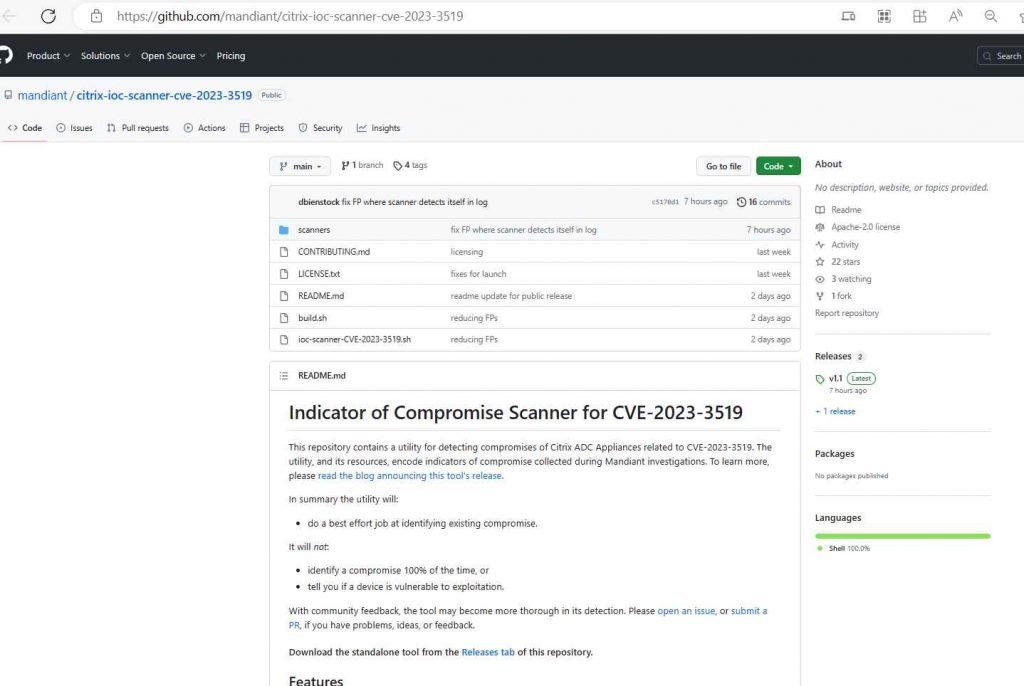
The zero-day market has evolved rapidly over the past decade. In 2015, Zerodium offered $1 million for iPhone exploits. By 2018, Crowdfense raised the bar to $3 million. Today, prices have surged due to improved device security and increased demand from governments. Crowdfense’s latest list includes $7 million for iPhone and $8 million for WhatsApp exploits, showing how competitive the landscape has become.
🇷🇺 A Russian Outlier
Operation Zero, a Russian firm, also offers up to $20 million for similar exploits but claims to work exclusively with the Russian government. This exclusivity limits its reach, especially since U.S. and European researchers are legally barred from selling to Russia. In contrast, Advanced Security Solutions appears to be casting a wider net, albeit under a veil of secrecy.
🔍 Ethical and Strategic Implications
The emergence of such companies raises serious ethical and geopolitical questions. While they claim to support counterterrorism and narcotics control, the lack of transparency and accountability makes it difficult to assess their true impact. The commodification of zero-days risks empowering regimes with poor human rights records or enabling surveillance beyond legal bounds.
Source: New zero-day startup offers $20 million for tools that can hack any smartphone
Zero Days
Given my expertise in AI governance and ethical deployment, this development is a flashing red light. The lack of transparency, combined with astronomical bounties, suggests a market that prioritizes power over accountability. I recommend using this case as a teaching tool in my training materials—perhaps a mind map contrasting ethical vs. unethical exploit markets, or a stakeholder matrix showing who benefits and who risks harm. It’s also a prime scenario for simulating AICP-style questions around lawful use, vendor vetting, and international compliance.
Here’s a structured mind map to help you visualize the ethical, strategic, and regulatory dimensions of the TechCrunch article on Advanced Security Solutions and its $20M zero-day bounty offer:
🧠 Mind Map: Ethical & Strategic Implications of High-Stakes Zero-Day Markets
1. Actors & Stakeholders
- Advanced Security Solutions: UAE-based startup offering record bounties
- Exploit Developers: Researchers, hackers, private contractors
- Government & Intelligence Agencies: Claimed clients, potential end-users
- Regulators & Compliance Bodies: GDPR, EU AI Act, ISO 42001
- Civil Society & Journalists: Transparency advocates, watchdogs
- Tech Companies: Apple, Google, Meta—targets of exploits
2. Motivations & Incentives
- Startup: Market dominance, intelligence leverage, financial gain
- Researchers: Monetary reward, prestige, ethical dilemma
- Governments: Surveillance, counterterrorism, geopolitical advantage
- Regulators: Risk mitigation, legal enforcement, public trust
3. Risks & Ethical Concerns
- Lack of Transparency: Unknown buyers, undisclosed use cases
- Human Rights Violations: Potential misuse by authoritarian regimes
- Surveillance Overreach: Exploits used beyond legal boundaries
- Market Commodification: Treating vulnerabilities as tradable assets
4. Legal & Compliance Tensions
- GDPR: Data protection vs. surveillance tools
- EU AI Act: High-risk AI systems and cybersecurity implications
- ISO 42001: Governance of AI lifecycle and exploit handling
- Export Controls: Restrictions on selling to sanctioned entities
5. Strategic Comparisons
- Crowdfense: Transparent pricing, selective clientele
- Zerodium: Longstanding player, known bounty structure
- Operation Zero (Russia): Exclusive to Russian government
- Advanced Security Solutions: High bounty, opaque operations
6. Sectoral Impact
- Finance & Insurance: Data breaches, regulatory exposure
- Healthcare: Patient data vulnerability, ethical fallout
- Education: Surveillance of students, academic integrity risks
- Autonomous Driving: Exploit-induced safety failures
- Advertising & Tourism: Behavioral tracking, privacy erosion
7. Governance & Response Strategies
- Vendor Vetting Protocols: Due diligence on exploit buyers
- Ethical Disclosure Frameworks: Incentivizing responsible reporting
- Stakeholder Matrices: Mapping impact across sectors
- Training & Certification: AICP-style scenarios, compliance drills
🧭 Advice for You,
This case is a goldmine for scenario-based learning. I suggest turning this mind map into:
- A stakeholder matrix for training sessions
- A compliance quiz with ethical dilemmas
- A visual aid contrasting exploit markets (ethical vs. opaque)
- A briefing slide for sector-specific risk analysis
- Reach out to us with any questions. info@DeuraInfoSec.com
OWASP LLM01:2025 Prompt Injection
DISC InfoSec previous posts on AI category
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services | Mergers and Acquisition Security