$167 Million Ruling Against NSO Group: What It Means for Spyware and Global Security
1. Landmark Ruling Against NSO Group After six years of courtroom battles, a jury has delivered a powerful message: no one is above the law—not even a state-affiliated spyware vendor. NSO Group, the Israeli company behind the notorious Pegasus spyware, has been ordered to pay $167 million for illegally hacking over 1,000 individuals via WhatsApp. This penalty is the largest ever imposed in the commercial spyware sector.
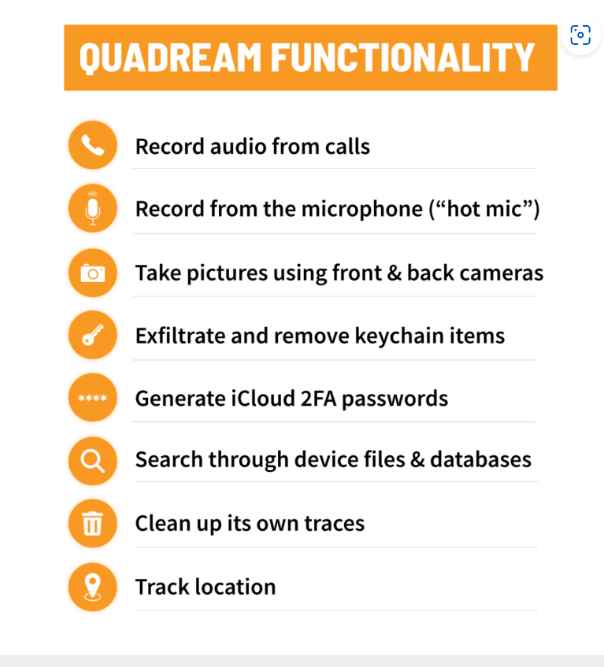
2. The Pegasus Exploit NSO’s flagship product, Pegasus, exploited a vulnerability in WhatsApp to inject malicious code into users’ phones. Approximately 1,400 devices were targeted, with victims ranging from journalists and activists to dissidents and government critics across multiple countries. This massive breach sparked international outrage and legal action.
3. Violation of U.S. Law While a judge had previously ruled that NSO violated U.S. anti-hacking laws, this trial was focused on determining financial damages. In addition to the $167 million fine, the company was ordered to pay $440,000 in legal costs, signaling a strong stand against cyber intrusion under the guise of state security.
4. Courtroom Accountability This case marked the first time NSO executives were compelled to testify in court. Their defense—that selling only to governments shielded them from liability—was rejected. The court’s decision emphasized that state affiliation doesn’t grant immunity when human rights are at stake.
5. Inside NSO’s Operations Court documents revealed the scale of NSO’s operations: 140 engineers working to breach mobile devices and apps. Pegasus can extract messages, emails, images, and more—even those protected by encryption. Some attacks require no user interaction and leave virtually no trace.
6. Broader Implications for Global Security Though NSO claims its spyware isn’t deployed within the U.S., other similar tools aren’t bound by such restrictions. This underscores the urgent need for secure communication practices, especially within government institutions. Even encrypted apps like Signal are vulnerable if a device itself is compromised.
7. Opinion: The Future of Spyware and How to Contain It This ruling sets a precedent, but the fight against spyware is far from over. As demand persists, especially among authoritarian regimes, containment will require:
- Binding international regulations on surveillance tech.
- Increased transparency from both public and private sectors.
- Sanctions on malicious spyware actors.
- Wider adoption of secure, open-source platforms.
Spyware like Pegasus represents a direct threat to privacy and democratic freedoms. The NSO case proves that legal accountability is possible—and necessary. The global community must now act to ensure this isn’t a one-off, but the beginning of a new era in digital rights protection.
How a Spy in Our Pocket Threatens the End of Privacy

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services