Attackers in South Korea are distributing malware disguised as cracked software, including RATs and crypto miners, and registering themselves with the Task Scheduler to ensure persistence.
Even after removing the initial malware, the Task Scheduler triggers PowerShell commands to download and install new variants, which persists because the PowerShell commands keep changing, leaving unpatched systems vulnerable to information theft, proxy abuse, and cryptocurrency mining.
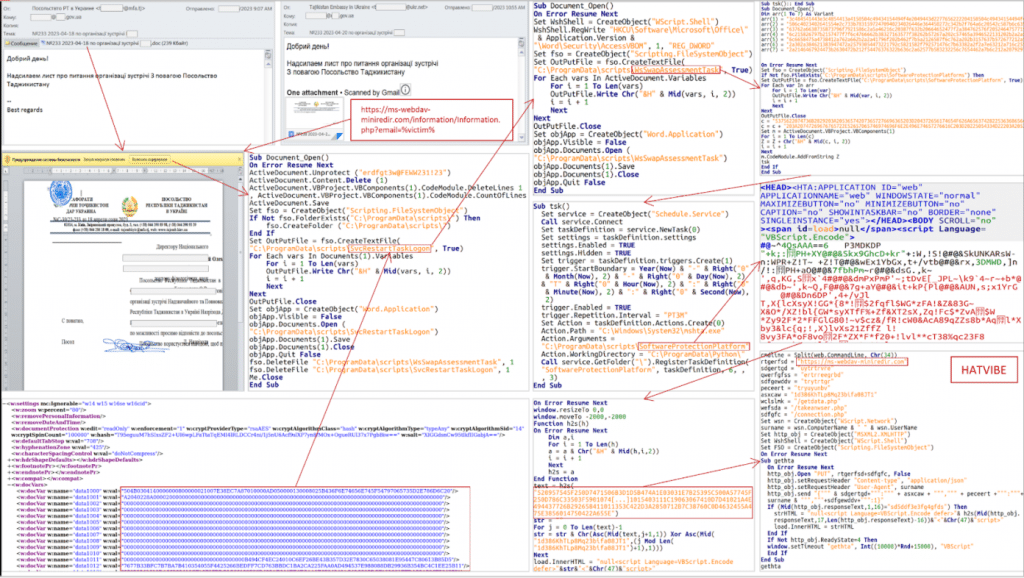
Malicious actors are leveraging file-sharing platforms to distribute malware disguised as cracked MS Office, which retrieves the download URL and target platform during infection, potentially enabling them to tailor attacks and evade detection.
Cybercriminals are distributing malware disguised as cracked software. The malware, developed in.NET, uses obfuscation to hide its malicious code, and initially, it accessed Telegram to retrieve a download URL.
Newer versions contain two Telegram URLs and a Mastodon URL, each with a string linked to a Google Drive or GitHub URL.
The threat actor hides malicious PowerShell commands within these cloud storage locations, using Base64 encoding for further obfuscation, and once executed, these commands install additional malware strains.
The updater malware, “software_reporter_tool.exe,” leverages a PowerShell script to download and maintain persistence, which creates a malicious executable at “C:\ProgramData\KB5026372.exe” and uses a compromised 7zip installation (“C:\ProgramData\Google\7z.exe”) to decompress a password-protected archive from GitHub or Google Drive (password: “x”) by mirroring tactics from a previous campaign.
Additionally, the updater registers itself with the Task Scheduler to ensure continuous operation after a reboot, and the scheduled task triggers the PowerShell script for further updates and potential malware installation.
The attackers deployed Orcus RAT and XMRig on the compromised system.
Orcus RAT can steal information through keylogging, webcam, and screenshot capture, while XMRig mines cryptocurrency.
XMRig is configured to stop mining when resource-intensive programs are running and to terminate processes competing for resources, such as security software installers, while 3Proxy is used to turn the infected machine into a proxy server by adding a firewall rule and injecting itself into a legitimate process.
According to ASEC, PureCrypter downloads and executes further payloads, and AntiAV malware disrupts security products by modifying their configuration files.
Attackers are distributing malware disguised as popular Korean software (Windows, MS Office, Hangul) through file-sharing sites, and the malware bypasses file detection with frequent updates and utilizes the Task Scheduler for persistence, leading to repeated infections upon removal.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot