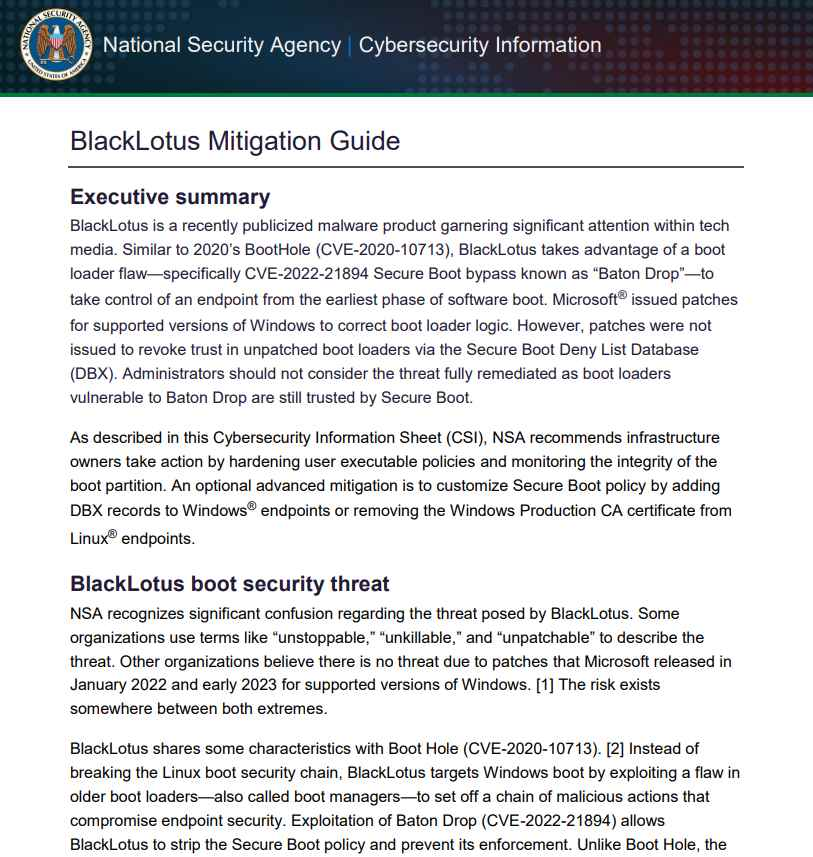
Cybercriminals have launched a campaign known as FLUX#CONSOLE, exploiting Microsoft Common Console Document (.MSC) files to infiltrate systems with backdoor malware. This method allows attackers to bypass traditional antivirus defenses by leveraging lesser-known Windows features. The campaign represents a shift from the previously common use of LNK files in phishing attacks.
The attack begins with phishing emails that use tax-related themes to deceive users into opening seemingly legitimate documents. These emails contain attachments disguised as PDFs, such as “Income-Tax-Deduction-and-Rebates202441712.pdf,” which are actually .MSC files. The default setting in Windows hides file extensions, making it easier for these malicious files to masquerade as harmless documents.
When a user opens the .MSC file, it executes embedded malicious scripts under the legitimate mmc.exe process. The attackers employ advanced obfuscation techniques to conceal the malicious code, which is often written in JavaScript or VBScript. This method allows the malware to run unnoticed, as it appears to be part of a standard administrative tool.
The .MSC file serves as both a loader and dropper for the malware payload. It delivers a malicious DLL file named DismCore.dll, which is sideloaded through the legitimate Dism.exe process. To maintain persistence on the infected system, the malware creates scheduled tasks, such as “CoreEdgeUpdateServicesTelemetryFallBack,” ensuring it executes every five minutes, even after system reboots.
This campaign highlights the increasing sophistication of phishing techniques and the exploitation of trusted Windows features. By abusing .MSC files and legitimate system processes, attackers can evade detection and establish persistent access to compromised systems. Users and organizations should be cautious of unexpected emails with attachments and consider adjusting settings to display file extensions to better identify potentially malicious files.

For further details, access the article here
vCISO Guide for Small & Mid Sized Businesses
DISC LLC is listed on Cynomi vCISO Directory
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services



.webp)
.webp)