Malware analysis reports – Reports and IoCs from the NCSC malware analysis team
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
InfoSec Compliance & AI Governance For over 20 years, DISC InfoSec has been a trusted voice for cybersecurity professionals—sharing practical insights, compliance strategies, and AI governance guidance to help you stay informed, connected, and secure in a rapidly evolving landscape.
Apr 09 2023
Feb 27 2023
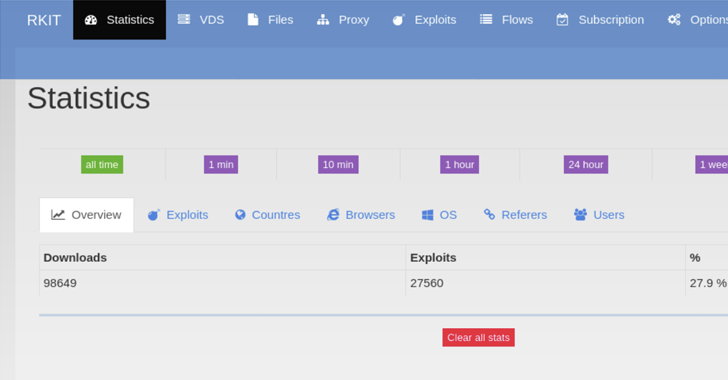
The RIG exploit kit (EK) touched an all-time high successful exploitation rate of nearly 30% in 2022, new findings reveal.
“RIG EK is a financially-motivated program that has been active since 2014,” Swiss cybersecurity company PRODAFT said in an exhaustive report shared with The Hacker News.
“Although it has yet to substantially change its exploits in its more recent activity, the type and version of the malware they distribute constantly change. The frequency of updating samples ranges from weekly to daily updates.”
Exploit kits are programs used to distribute malware to large numbers of victims by taking advantage of known security flaws in commonly-used software such as web browsers.
The fact that RIG EK runs as a service model means threat actors can financially compensate the RIG EK administrator for installing malware of their choice on victim machines. The RIG EK operators primarily employ malvertising to ensure a high infection rate and large-scale coverage.
As a result, visitors using a vulnerable version of a browser to access an actor-controlled web page or a compromised-but-legitimate website are redirected using malicious JavaScript code to a proxy server, which, in turn, communicates with an exploit server to deliver the appropriate browser exploit.
The exploit server, for its part, detects the user’s browser by parsing the User-Agent string and returns the exploit that “matches the pre-defined vulnerable browser versions.”
“The artful design of the Exploit Kit allows it to infect devices with little to no interaction from the end user,” the researchers said. “Meanwhile, its use of proxy servers makes infections harder to detect.”
Since arriving on the scene in 2014, RIG EK has been observed delivering a wide range of financial trojans, stealers, and ransomware such as AZORult, CryptoBit, Dridex, Raccoon Stealer, and WastedLoader. The operation was dealt a huge blow in 2017 following a coordinated action that dismantled its infrastructure.
For more details:
https://thehackernews.com/2023/02/researchers-share-new-insights-into-rig.html
Dec 12 2022
Malware attacks are a growing problem in our increasingly digital world. By infiltrating computers and networks, malicious software can cause serious harm to those affected by it.
One of the most common types of malware is ransomware (encryption-based malware), which prevents users from accessing their files until they pay a hefty fee to the cyber attacker. This type of attack has been used to target everything from individuals to large organizations, including government agencies and healthcare providers.
In addition to financial losses, malware attacks can have devastating effects on businesses and individuals. In some cases, sensitive data can be stolen or destroyed as part of an attack. This can lead to identity theft and other forms of fraud, as well as put organizations at risk for long-term damage if confidential information is exposed or compromised.
A recent study by Atlas VPN shows how malware infection is on the rise and the trends in the new malware samples found in the first three quarters of 2022.
According to researchers, 59.58 million samples of new Windows malware were found in the first three quarters of 2022 and these make up 95.6% of all new malware discovered during that time period.
This analysis was based on data by AV-TEST GmbH, an independent organization that evaluates and rates antivirus and supplies services in IT Security and Antivirus Research. The study also includes new malware samples detected in the four quarters of 2021 and the first three quarters of 2022.
Overall, there is a downward trend in the data with the malware samples this year has decreased by 34% as compared to the same period last year. However, the numbers are still exceptionally high.
Following Windows on the list is Linux malware with 1.76 million new malware samples – 2.8% of the total malware threats in 2022.
Android malware takes third place with the first three quarters of 2022 seeing 938,379 new Android malware threats, constituting 1.5% of the total new malware.
Lastly, 8,329 samples of never before seen malware threats aimed at macOS were observed in the same period.
The study also shows that the total number of malware threats found in the first three quarters of 2022 across all operating systems amount to 62.29 million. This is about 228,164 malware threats daily.
If we make a quarter-by-quarter comparison, the first quarter of 2022 saw the most significant number of malware samples – 22.35 million. However, this number dropped by 4% to 21.49 million in the second quarter of this year. Again, it decreased by another 14% to 18.45 million.
The numbers continue to plummet into the fourth quarter of the year with 7.62 million new threats found in October and November – nearly 60% less than at the same time last year.
Malware is a pervasive threat to internet users on both personal and professional networks. It can cause serious damage to computers, networks, and data that can be expensive to fix. Fortunately, there are steps you can take to protect yourself from malware.
The most important step in protecting your network from malware is keeping your anti-malware software up to date. Regularly updating anti-malware programs ensures that they’re able to detect the latest threats and keep them away from your computer or network.
Additionally, be sure not to click on suspicious links or download files from unknown sources as these could contain malicious code that could harm your system.
Another way to stay safe online is by using a secure web browser with built-in security features like pop-up blockers, phishing protection, and ad blockers ((don’t use it on Hackread.com though :0)) for enhanced protection against malicious activities.

Dec 24 2021
Elastic Security researchers uncovered a malware campaign that leverages a new malware and a stealthy loader tracked as BLISTER, that uses a valid code signing certificate issued by Sectigo to evade detection.
BLISTER loads second-stage payloads that are executed directly in the memory of the Windows system and maintain persistence. The malicious code has a low detection rate and implements multiple tricks to avoid detection.
“A valid code signing certificate is used to sign malware to help the attackers remain under the radar of the security community. We also discovered a novel malware loader used in the campaign, which we’ve named BLISTER. The majority of the malware samples observed have very low, or no, detections in VirusTotal.” “The infection vector and goals of the attackers remain unknown at this time.”

The certificate used to sign the loader code was issued by Sectigo for a company called Blist LLC, which has an email address from a Russian provider Mail.Ru.
The loader is embedded into legitimate libraries, such as colorui.dll, to avoid raising suspicion, it can be initially written to disk from simple dropper executables.
Upon execution, BLISTER decodes bootstrapping code stored in the resource section with a simple 4-byte XOR routine. The malware authors heavily obfuscated the bootstrapping code that initially sleeps for 10 minutes before executing in an attempt to evade sandbox analysis.
Then the loader decrypts the embedded malware payload, experts reported the use of CobaltStrike and BitRat as embedded payloads. The payload is loaded into the current process or injected into a newly pawned WerFault.exe process.
In order to achieve persistence, BLISTER copy itself to the C:\ProgramData folder and re-names a local copy of rundll32.exe. Then it creates a link to the current user’s Startup folder to launch the malware at logon as a child of explorer.exe.
Elastic’s researchers shared Yara rules for this campaign along with indicators of compromise.
Malware Analysis and Detection Engineering: A Comprehensive Approach to Detect and Analyze Modern Malware
InfoSec is the page where the InfoSec community interacts, and share InfoSec & compliance related information.
“You Become What You Think About Ask; and it shall be given to you Seek; and you shall find Knock; and it shall be opened unto you.”