Ben Rothke’s review of Inside Cyber Warfare: Mapping the Cyber Underworld by Jeffrey Carr offers a sobering examination of the modern landscape of cyber conflict. The book delves into the evolving nature of cyber threats, highlighting how state-sponsored actors and criminal organizations exploit digital vulnerabilities to achieve their objectives. Carr’s analysis underscores the complexity and pervasiveness of cyber warfare in today’s interconnected world.
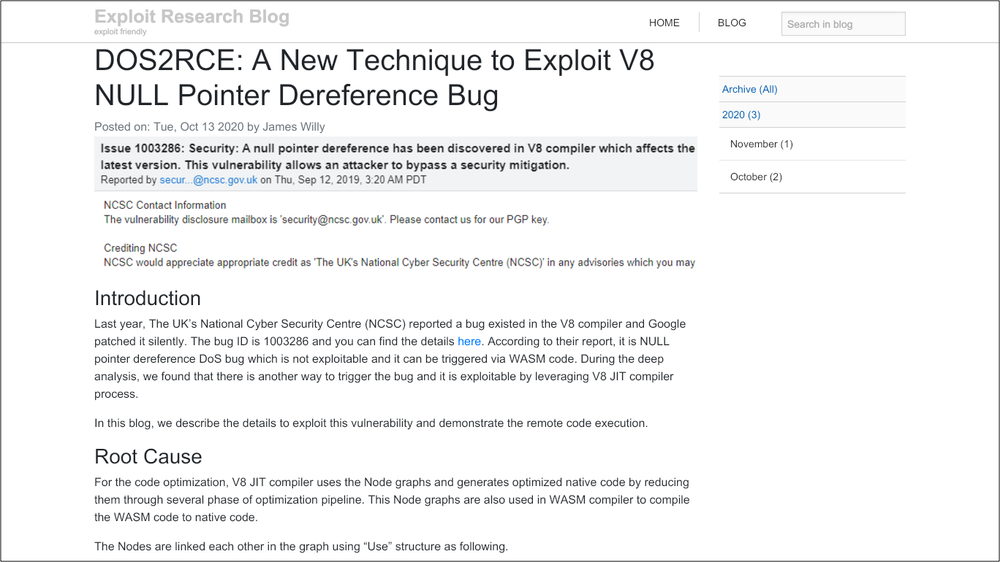
Carr emphasizes that cyber warfare is not confined to isolated incidents but is a continuous and multifaceted threat. He illustrates how nations leverage cyber capabilities for espionage, sabotage, and influence operations. The book provides detailed accounts of various cyber attacks, shedding light on the tactics and motivations behind them. Carr’s insights reveal the strategic importance of cyber operations in modern geopolitical conflicts.
One of the critical themes in Carr’s work is the attribution challenge in cyber attacks. Determining the origin of an attack is often fraught with uncertainty, complicating responses and accountability. Carr discusses the implications of this ambiguity, particularly in the context of international law and norms. The difficulty in attributing attacks hampers efforts to deter malicious actors and enforce consequences.
Carr also explores the role of non-state actors in cyber warfare. He examines how terrorist groups, hacktivists, and criminal syndicates exploit cyberspace for their agendas. The book delves into the methods these groups use, from defacing websites to orchestrating complex cyber heists. Carr’s analysis highlights the democratization of cyber capabilities and the resulting proliferation of threats.
The book doesn’t shy away from discussing the vulnerabilities within critical infrastructure. Carr outlines how essential services like power grids, water supplies, and transportation systems are susceptible to cyber attacks. He stresses the potential for catastrophic consequences if these systems are compromised, urging for robust security measures and contingency planning.
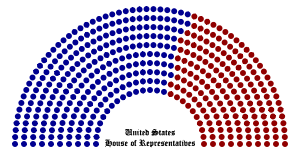
Carr’s narrative also touches on the psychological and societal impacts of cyber warfare. He examines how disinformation campaigns and cyber propaganda can erode public trust and destabilize societies. The book provides examples of how such tactics have been employed to influence elections and sow discord, emphasizing the need for resilience against information warfare.
In conclusion, Inside Cyber Warfare serves as a comprehensive guide to understanding the complexities of cyber conflict. Carr’s work is a call to action for policymakers, security professionals, and the public to recognize the gravity of cyber threats. The book advocates for international cooperation, robust cybersecurity frameworks, and public awareness to mitigate the risks posed by cyber warfare.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services














![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=1119f164-7e48-4ad2-b112-d80cd3808a1d)

![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=02d47642-2651-4395-b8dd-28e3a18dc505)

![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=2b18960c-caaa-4f56-a227-a5ede7b55594)



