The perfect introduction to the principles of information security management and ISO27001:2013
Most organizations implementing an information security management regime opt for systems based on the international standard, ISO/IEC 27001. This approach ensures that the systems they put in place are effective, reliable and auditable.
Up to date with the latest version of the Standard (ISO27001:2013), An Introduction to information security and ISO27001:2013 is the perfect solution for anyone wanting an accurate, fast, easy-to-read primer on information security from an acknowledged expert on ISO27001.
This pocket guide will help you to:
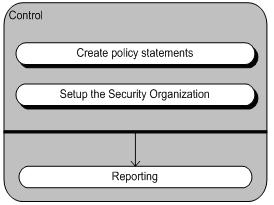
Make informed decisions
- By providing a clear, concise overview of the subject this guide enables the key people in your organization to make better decisions before embarking on an information security project.
Ensure everyone is up to speed
- Once you have decided to implement an information security project, you can use this guide to give the non-specialists on the project board and in the project team a clearer understanding of what the project involves.
Raise awareness among staff
- An Information Security Management System (ISMS) will make demands of the overall corporate culture within your organization. You need to make sure your people know what is at stake with regard to information security, so that they understand what is expected of them.
Enhance your competitiveness
- Your customers need to know that the information you hold about them is managed and protected appropriately. And to retain your competitive edge, you will want the identity of your suppliers and the products you are currently developing to stay under wraps. With an effective knowledge management strategy, you can preserve smooth customer relations and protect your trade secrets.
Download this pocket guide and learn how you can keep your information assets secure.
Related articles














![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=1119f164-7e48-4ad2-b112-d80cd3808a1d)