by Mike Holcomb

Checkout previous OSINT posts here
InfoSec Compliance & AI Governance For over 20 years, DISC InfoSec has been a trusted voice for cybersecurity professionals—sharing practical insights, compliance strategies, and AI governance guidance to help you stay informed, connected, and secure in a rapidly evolving landscape.
Nov 27 2024
Oct 08 2024
American Water, the largest water and wastewater utility company in the U.S., experienced a cyberattack that prompted the shutdown of specific systems. The company took immediate action to secure its infrastructure, and an investigation is ongoing to determine the extent of the breach. The attack has raised concerns about the vulnerability of critical infrastructure to cyber threats.
While the affected systems were isolated to mitigate damage, it is unclear if any customer or operational data was compromised. American Water has stated that service to customers was not disrupted during the incident.
The breach highlights the growing risks faced by essential services and critical infrastructure sectors. This event underscores the importance of robust cybersecurity measures, particularly for utilities that deliver essential public services like water and power.

Homeland Security and Critical Infrastructure Protection
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Feb 23 2024
Ransomware attacks against manufacturers, utilities and other industrial companies were up 50% last year.
The pace and sophistication of cyberattacks against industrial companies are escalating rapidly, as administration officials warn that nation-states are heavily targeting U.S. critical infrastructure sectors.
Ransomware attacks against industrial companies increased by around 50% last year, according to an annual report from cybersecurity company Dragos published Tuesday, which tracked 905 strikes.
The Hanover, Md.-based company, which specializes in protecting systems used by heavy industries such as electric grids and wastewater plants, said it tracked 28% more groups specifically targeting “operational technology” last year than the year before. The term refers to the heavy machinery and industrial control systems used by manufacturing plants, water utilities and similar organizations, as opposed to information technology, which generally comprises software such as accounting and human resources systems. Among industrial companies, manufacturers were targeted most, said Rob Lee, chief executive of Dragos.
“It’s not so much that they’re OT experts, it’s just they know that they’re impacting the revenue-generating portions of those companies,” Lee said, “so the companies are willing to pay, and pay faster.”
Even when ransomware attacks target manufacturers’ corporate technology systems and not their operational technology machinery, there can be collateral damage for production, said Mark Orsi, president of the Manufacturing Information Sharing and Analysis Center, a nonprofit that coordinates the sharing of threat data among manufacturers.
“The vast majority of ransomware variants only target the IT infrastructure of an organization, but all too often the manufacturing plant floor operations are disrupted as a result of compromise to IT systems,” he said.
But ransomware is just the tip of the iceberg, say industry observers. The tools used by hackers to specifically target operations have become more sophisticated in recent years.
The emergence of Pipedream, for instance, a tool believed to have been authored by a nation-state team, has many concerned. Pipedream is able to target industrial systems across industries, and doesn’t rely on common attack methods, such as exploiting vulnerabilities in software.
“When Pipedream or Pipedream-like capabilities leak out into the community, they will be the Cobalt Strikes of OT. That’s the stuff that worries me,” Lee said during a call with reporters on Jan. 30, referring to a suite of cybersecurity tools, Cobalt Strike, developed for network defenders, which gave rise to a slew of malicious hacking tools when it was leaked.
U.S. officials have also ratcheted up warnings of attempts to infiltrate U.S. critical infrastructure. Christopher Wray, director of the Federal Bureau of Investigation, on Sunday said Chinese efforts to secure footholds in critical infrastructure networks are occurring at an unprecedented scale.
While Beijing routinely denies involvement in hacking, Wray’s comments follow a series of similar remarks made by Rob Joyce, cybersecurity director of the National Security Agency. Last month, Joyce told an FBI-sponsored conference that Chinese hackers are positioning themselves within those networks so as to be able to strike at U.S. infrastructure in the event of a conflict. The U.S. government in January said it disrupted one such operation, without specifying the types of infrastructure targeted.
“It’s not just an electric company issue, it’s not just a water issue or a manufacturing issue. I think it’s an issue that affects all of us,” said Jason Nations, director of enterprise security at Oklahoma City-based
OGE Energy, on the same call as Lee.
Critical infrastructure operators also face supply-chain security threats common to companies in many industries. German company
PSI Software, which said last week it had been the victim of a cyberattack, specified on Monday that it had been hit by ransomware, and took its systems offline to prevent further intrusions. PSI Software supplies software specialized for energy providers and other industrial processes. PSI didn’t respond to a request for comment.
One difficulty critical-infrastructure companies struggle with is finding cybersecurity experts to defend their networks. While there is a shortage of around 4 million corporate cyber professionals globally, according to trade association ISC2, some companies say it is especially difficult to hire people with both cyber skills and expertise in heavy machinery and industrial technology.

Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoT
Engineering-Grade OT Security: A manager’s guide
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Dec 04 2023
CISA has recently confirmed that Iran-affiliated attackers took over a Unitronics Vision Series PLC at a water system facility in Pennsylvania, and urged other water authorities to promptly secure their Unitronics PLCs.
The agency has advised them to change the default password and port used by the PLC, disconnect it from the open internet or secure remote access by using firewall, VPN and multi-factor authentication (MFA), create configuration backups, and update the PLC/HMI to the latest available version.
CyberAv3ngers has previously claimed responsibility for numerous attacks against critical infrastructure organizations in Israel working in the water, energy, shipping, and distribution sectors, and only recently targeted Unitronics PLCs deployed by multiple US-based water and wastewater facilities.
In the latest advisory, the agencies shared additional information about the APT group’s activites and indicators of compromise (IoCs) associated with their most recent attacks.
“These PLC and related controllers are often exposed to outside internet connectivity due to the remote nature of their control and monitoring functionalities. The compromise is centered around defacing the controller’s user interface and may render the PLC inoperative. With this type of access, deeper device and network level accesses are available and could render additional, more profound cyber physical effects on processes and equipment,” the advisory explains.
“It is not known if additional cyber activities deeper into these PLCs or related control networks and components were intended or achieved. Organizations should consider and evaluate their systems for these possibilities.”
The UK National Cyber Security Centre (NCSC) says that the compromise of the PLCs is “highly unlikely” to disrupt routine operations of affected organizations. “There is a very low potential risk, if the threat is unmitigated, to some small suppliers,” they noted.
The agencies repeated CISA’s initial risk mitigation advice and urged organizations to apply it to all internet-facing PLCs, not just those manufactured by Unitronics (which, it has been pointed out, may also be rebranded and appear as made by different manufacturers).
Finally, they called on device manufacturers to do their part in securing OT devices by:
Cybersecurity for Industrial Control Systems: SCADA, DCS, PLC, HMI, and SIS
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 17 2023
The skills employed, the hacktivists and other threat actors are not going anywhere. Right now, Russia might be overwhelmingly interested in Ukraine, but their aims and goals remain global.
“These skills will be turned in other directions and other targets in the future, they will be shared in threat actor groups online. This is the world you need to be preparing for right now,” he added.
His warning echoed a similar one by Viktor Zhora, Deputy Chairman and Chief Digital Transformation Officer at the State Service of Special Communication and Information Protection of Ukraine.
Russia’s attack force consists of “hackers in uniform”, cybercriminals and hacktivists congregating in various Telegram channels, but the nation is also working on engaging ever more younger people in their cyber offensive campaigns. They are seeking talented individuals in schools (and not just tech universities), selecting the most talented and training them, he shared.
“The Russians are in it for the long run,” Zhora warned during his IRISSCON talk, and called on countries that are – or expect to be – targeted by cyber aggressive nations to create a cyber coalition so they can prepare, share their experiences, and exchange information.
We can’t talk about the war in Ukraine and not mention cyber attacks aimed at disrupting operational technology (OT) used by companies that are part of the country’s critical infrastructure (CI).
In his talk, Ferguson briefly passed through the known attacks that hit CI entities with OT-specific malware, starting with Stuxnet in 2010 and ending with CosmicEnergy in 2023.
Some of the attacks are believed to be the work of the US and Israel (Stuxnet), cybercriminals (EKANS ransomware, 2020) or are still unattributed (the destructive 2014 attack against a steel plant in Germany). But the rest, he noted, are all believed to have been mounted by Russian state-backed attackers.
And, he says, they are getting better at it. Mirroring the development of attacks against IT systems, they have recently begun exploiting legitimate tools found in OT environments, so they don’t need to develop customized malware.
Many attackers are scanning for OT-specific protocols and probing OT devices, Ferguson noted. While their actual exploitation hinges on the skills of the attackers, some modes of attack (e.g., DDoS and phishing) are available to those who are less skilled, but eager. Hacktivists can target critical infrastructure that’s exposed on the internet as it’s easily discoverable via online tools.
Unfortunately, securing OT systems comes with a host of challenges: a complex infrastructure; an increasing number of endpoints; OT devices insecure by design (and generally not meant to be connected to the internet); rarely integrated OT and IT security teams, a lack of visibility into the OT infrastructure – to name just a few.
Since the start of the war, Russian hackers have been trying to shut down electrical power in the country, have gone after government agencies, IT companies, telecoms, software development firms, media houses, editors, and media personalities, Zhora noted.
While the initial attacks were mostly geared towards destruction, Russian cyber attackers are now also trying to get their hands on information that can help them determine the effectiveness of their kinetic attacks, discover whether their spies have been flagged by the Ukrainian authorities, and see what evidence those authorities have gathered about war crimes.
Clever and subtle psy-ops online campaigns are, as well, a favorite tactic employed by the Russian state to manipulate enemies. And, since the advent of generative AI, it has became easier to mount them, Ferguson added.
All these things should be taken in consideration by governments when preparing for the future. Looking at the cyber component of the unfolding wars in Ukraine and Israel, they can see what future conflicts will look like.
Zhora says that Ukraine is becoming more and more confident of its capacity to counter future attacks, but that each democracy needs to ask themselves: Are we prepared for a global cyber war? “And they need to be honest with the answer,” he noted.
If they are not, they should immediately begin investing in cyber defense and intensifying cooperation, he added.

InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Sep 08 2023
MITRE and the US Cybersecurity and Infrastructure Security Agency (CISA) have collaborated to develop a new open source tool that simulates cyber-attacks on operational technology (OT). The product was published recently.
The MITRE Calder for OT is now accessible to the general public as an addition to the open-source Caldera platform that may be found on GitHub. This would make it possible for cybersecurity specialists who deal with industrial control systems (ICS) to carry out automated adversary simulation exercises. These exercises will have the goal of testing and improving their cyber defenses on a constant basis. In addition to this, this includes security inspections as well as exercises involving red, blue, and purple teams.
This Caldera extension for OT was created via a collaborative effort between CISA and the Homeland Security Systems Engineering and Development Institute (HSSEDI). HSSEDI is a research and development institution that is financed by the federal government and is maintained and run by MITRE on behalf of the Department of Homeland Security (DHS).
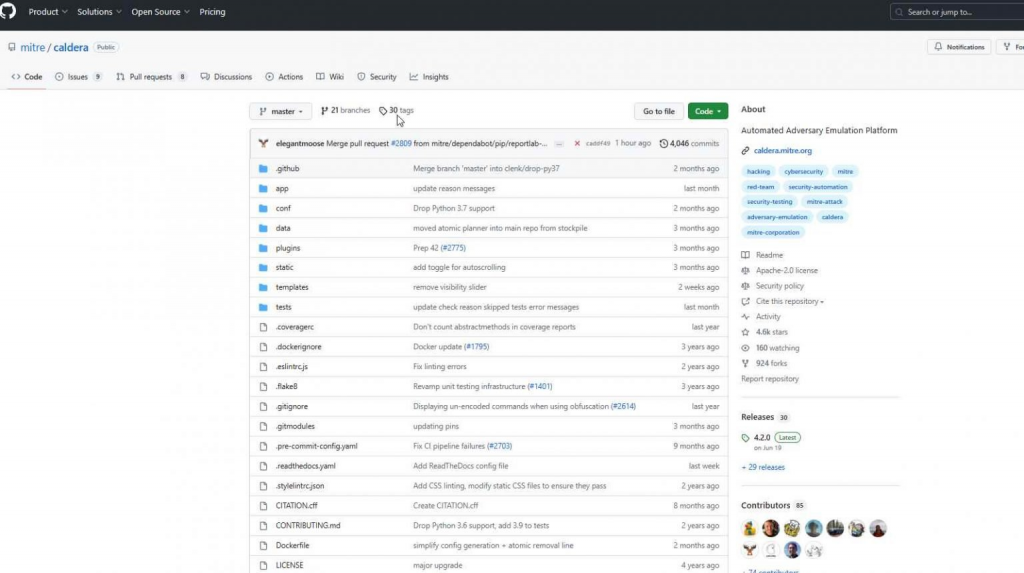
The program contributes to the goal of the federal government to strengthen the security of vital infrastructure that is dependent on OT. Some examples of such infrastructure are water and electricity. This objective was elaborated upon in the United States’ National Cybersecurity Strategy, which was published in March 2023, and in the Executive Order on Improving the Nation’s Cybersecurity, which was issued by President Biden in May 2021.
Work done by CISA and HSSEDI to automate opponent emulation simulations in CISA’s Control Environment Laboratory Resource (CELR) served as the foundation for the OT extension, which was developed upon that work. This made it possible to identify hostile strategies that may be implemented in Caldera.
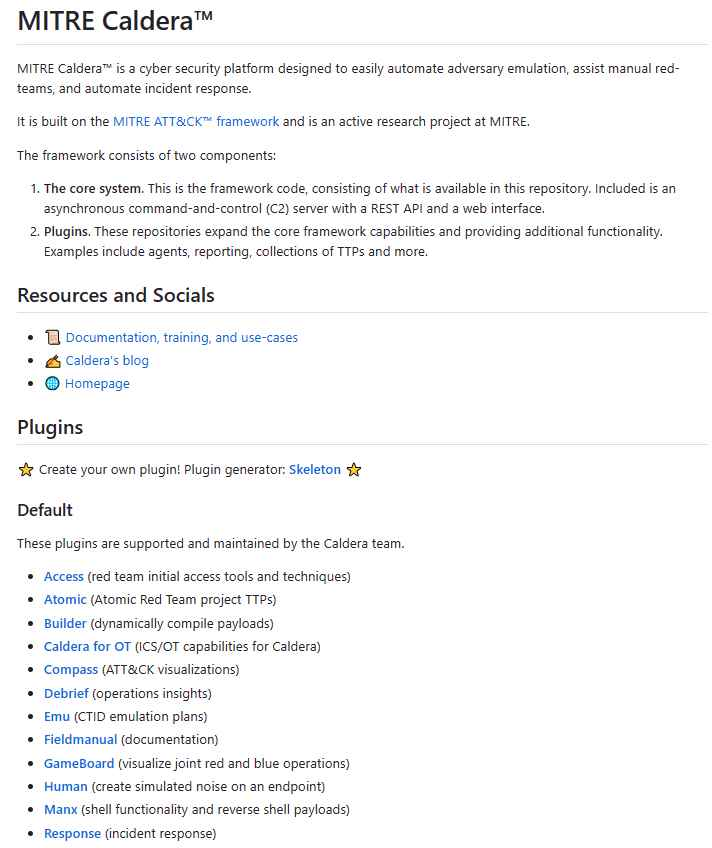
The defensive mechanisms and testing capabilities of critical infrastructure systems are slated to get a boost from the use of these plugins.
These plugins, which are stored in the “caldera-ot” repository, are essential instruments for the protection of operational technology (OT) settings.
They are made available as Git submodules, which enables researchers and experts in the security industry to quickly and readily access them.
The purpose of these plugins is to facilitate enemy simulation inside the OT environment. This was the driving force behind their development.
Because of this, companies are given the ability to strengthen their security defenses and better prepare for possible attacks.
In addition to this, it is compatible with classic use cases for Caldera, such as rigorous testing of security mechanisms and operator training.
The move that has been taken by MITRE marks a major step forward in the continuing endeavor to secure critical infrastructure systems and to strengthen security within the OT sector.
A presentation titled “Emulating Adversary Actions in the Operational Environment with Caldera (TM) for OT” has also been made available by MITRE for individuals who are looking for further information of a more in-depth kind.
Users may apply the following command in order to install the whole collection of Caldera for OT plugins:
git clone https://github.com/mitre/caldera-ot.git –recursive
Individuals also have the option of configuring certain plugins on their own, which allows them to personalize their approach to OT security to meet their unique requirements.
At the moment, the following three important plugins are available:
Open-Source OT Protocol Libraries That Are Unified And Exposed To Users. Caldera for OT plugins is a service provided by MITRE that aims to standardize and expose open-source OT protocol libraries, making them available for use as protocol-specific plugins. Each plugin comes with its own extensive documentation.
Cyber Defence Strategy using NIST and MITRE ATT&CK Frameworks
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Aug 21 2023
Israel and US government agencies announced the BIRD Cyber Program, an investment of roughly $4M in projects to enhance the cyber resilience of critical infrastructure.
The BIRD Cyber Program is a joint initiative from the Israel National Cyber Directorate (INCD), the Israel-US Binational Industrial Research and Development (BIRD) Foundation, and the US Department of Homeland Security (DHS) Science and Technology Directorate (S&T) to promote projects to enhance the cyber resilience of critical infrastructure in both countries.
The program is managed by the BIRD Foundation, a non-profit organization that supports joint research activities between Israeli and American organizations. The initiative plans to invest $3.85 million in projects to develop cutting-edge defense solutions.
The total value of the projects will be increased to approximately $10 million through private-sector funding.
The initiative aims at developing new solutions for detecting and preventing cyberattacks, technologies to protect sensitive data, and improve the security of critical infrastructure systems.
The BIRD foundation provides funding of up to 50% for each approved project, it is important to note that no repayment is required if the project does not reach the sales stage.
The BIRD Cyber Program also provides mentoring for the growth of the projects.
Below are the eligibility requirements for the BIRD Cyber Program:
The BIRD Cyber Program will award four grants for projects related the maritime sectors, airport and air traffic, and industrial control systems (ICS).
Below are the projects approved:
The above projects were submitted in response to the first BIRD Cyber call.
“We are pleased to jointly invest with our Israeli partners in these innovative projects and anticipate that they will deliver new capabilities to enhance the cybersecurity posture and overall resilience of vital critical sectors in both nations,” said Megan Mahle, Director of the DHS S&T Office of Industry Partnerships. Aviram Atzaba, Executive Director for International Cooperation of INCD, added: “We are proud to partner with DHS to develop cutting-edge solutions for small and medium-sized businesses and critical infrastructure cybersecurity… The BIRD mechanism continues to strengthen the strategic alliance between Israel and the United States.”
CRITICAL INFRASTRUCTURE PROTECTION: Agencies Need to Assess Adoption of Cybersecurity Guidance
InfoSec tools | InfoSec services | InfoSec books | Follow our blog
Aug 09 2023
CODESYS, a widely-used integrated environment for controller programming, holds a strong presence in Operational Technology across diverse industries, such as:-
Backed by more than 500 manufacturers (including Schnieder Electric, Beckhoff, Wago, Eaton, ABB, Festo, etc.) and spanning various architectures that we have mentioned below, CODESYS powers millions of global devices:-
Cybersecurity Researcher at Microsoft, Vladimir Eliezer Tokarev, recently identified several high-severity vulnerabilities and 16 zero-day vulnerabilities in CODESYS (CODESYS V3 SDK).
Microsoft’s cyberphysical system researchers identified high-severity vulnerabilities in CODESYS V3 SDK that could lead to security risks for OT infrastructure. If you’re at #BHUSA, you can attend this session on August 10 to learn more: https://msft.it/60199ynQT
Besides this, Vladimir Eliezer Tokarev dubbed the 16 zero-day vulnerabilities that he found in CODESYS as “CoDe16,” a code name for this complete set of CODESYS zero-day vulnerabilities.
While the OT infrastructure could be affected severely by successfully exploiting all these high-severity vulnerabilities discovered in CODESYS V3 SDK.
Moreover, the Microsoft Threat Intelligence team also prompted and recommended that users at the BHUSA event (Black Hat USA 2023) attend their official session related to this vulnerability profile on August 10.
Cybersecurity researchers will detail the following key things during this event session:-
Apart from this, all the challenges, like proprietary network protocols and debugger-free analysis, will also be explored.
Security analysts will also unveil the root-cause for key flaws, and demonstrate the remote code execution chain to implant malicious payload, gaining full PLC control and factory floor manipulation.
Closing remarks will include the mitigation strategies, an open-source validation tool for CODESYS devices, and a live demo of successful RCE on an exposed system.
InfoSec tools | InfoSec services | InfoSec books
Jul 08 2023
For too long the cybersecurity world focused exclusively on information technology (IT), leaving operational technology (OT) to fend for itself. Traditionally, few industrial enterprises had dedicated cybersecurity leaders. Any security decisions that arose fell to the plant and factory managers, who are highly skilled technical experts in other areas but often lack cybersecurity training or knowledge.
In more recent years, an uptick in cyberattacks against industrial facilities and the trend of IT/OT convergence driven by Industry 4.0 have highlighted the vacuum of ownership around OT security. According to a new Fortinet report, most organizations are looking to Chief Information Security Officers (CISOs) to solve the problem.
Fortunately, CISOs are no strangers to change or difficult challenges. The position itself is less than 20 years old, yet in those two decades CISOs have navigated some of the most disruptive cybersecurity events that were truly watershed moments in technology.
Still, most CISOs have made their mark securing IT environments — and IT security strategies and tools rarely translate to an OT context. While the soft skills of collaboration and team-building will certainly help CISOs as they bring the factory floor into their realm of responsibility, they must also make a concentrated effort to understand the OT landscape’s unique topography and distinctive security challenges.
The CIA triad — Confidentiality, Integrity & Availability — is a key concept in cybersecurity. Critically, IT and OT prioritize the elements of the triad differently — although safety is always the common denominator.

Somewhat ironically, the AIC triad of the OT world has resulted in systems and tools that prioritize physical safety but often come with few or no cybersecurity features at all. It will be the CISO’s responsibility to identify and implement security solutions that protect OT systems from cyberthreats without disrupting their operations.
In both OT and IT, segmentation limits the network’s attack surface. In OT, the Purdue Model serves as a framework for how and why systems can and should communicate with each other.
In a highly simplified nutshell, the Purdue Model comprises five layers.
The purpose of these layers is to create both logical and physical separation between process levels. The closer you get to the cyber-physical operation of industrial systems like injectors, robotic arms, and industrial presses, the more checks and balances are in place to protect them.
While the concept of segmentation will not be new to CISOs, they will need to understand that the separation of zones is much stricter in OT environments and must be enforced at all times. Industrial enterprises adhere to the Purdue model or other similar frameworks to ensure safety and security and to meet many regulatory compliance mandates.
In IT, downtime for upgrades and patches is no big deal, especially in a Software-as-a-Service (SaaS) world where new updates are released practically in real time.
Whether for safety or profit, OT systems are always up and running. They cannot be stopped or paused to download a new operating system or apply even a critical patch. Any process that requires downtime is simply a non-starter for the vast majority of OT systems. For this reason, CISOs should not be surprised to discover decades-old systems (likely running on software that reached its end-of-life date long ago) that still serve as a crucial piece of the operation.
The challenge facing CISOs will be to identify security controls that will not interrupt or interfere with delicate OT processes. The right solutions will “wrap” the existing OT infrastructure in a layer of security that protects critical processes without changing, complicating, or crowding them.
Traditionally, OT systems have been protected through isolation. Now that organizations are connecting these environments to capitalize on Industry 4.0 or to allow easier access for contractors, all access must be monitored, controlled, and recorded.
In this context, anyone accessing the OT environment is effectively an outsider. Whether it is a vendor connecting remotely, a business user coming in through the IT network, or even an OT operator accessing the environment on-site, every connection comes from the outside. Recognizing this key point will help CISOs to understand that industrial secure remote access (I-SRA) tools should be used for all access scenarios, not only those that IT would consider to be “remote.”

Tools designed for IT hardly ever translate to OT.
Forcing IT-designed tools into OT environments only adds complexity without addressing the fundamental security requirements and priorities of these environments. The sooner a CISO realizes that OT systems deserve security solutions designed for their distinctive needs, the faster they will be on their way to implementing the best tools and policies.
Given that most cybersecurity leaders currently tend to come from IT security roles, it makes sense that many CISOs will have a (perhaps unconscious) bias toward IT philosophies, tools, and practices. To effectively secure OT environments, CISOs will need to become students again and lean on others to learn what they do not yet know.
The good news is that CISOs generally have a propensity to ask the right questions and seek support from the right experts while still pushing the envelope and demanding positive outcomes. At the end of the day, a CISO’s job is to lead people and teams of experts to accomplish the greater goal of securing the enterprise and enabling the business. Those willing to bridge the OT security divide through strong leadership and a willingness to learn should quickly find themselves on the road to success.
https://thehackernews.com/2023/06/5-things-cisos-need-to-know-about.html
InfoSec tools | InfoSec services | InfoSec books
Jun 27 2023
May 30 2023
The widespread adoption of remote and hybrid working practices in recent years has brought numerous benefits to various industries, but has also introduced new cyber threats, particularly in the critical infrastructure sector.
These threats extend not only to IT networks but also to operational technology (OT) and cyber-physical systems, which can directly influence crucial physical processes.
In response to these risks, the US government reinforced critical infrastructure security by introducing Cross-Sector Cybersecurity Performance Goals (CPGs) mandated by the US Cybersecurity Infrastructure & Security Agency (CISA).
Recently, CISA updated the CPGs to align with NIST’s standard cybersecurity framework, establishing each of the five goals as a prioritized subset of IT and OT cybersecurity practices.
In this article, we will look in more detail at CISA’s revamped CPGs and discuss the potential solutions available to help organizations achieve these critical goals.
CISA’s first CPG is “Identify”, which includes identifying the vulnerabilities in the IT and OT assets inventory, establishing supply chain incident reporting and vulnerability disclosure program, validating the effectiveness of third-party security controls across your IT and OT networks, establishing OT security leadership, and mitigating known vulnerabilities. Critical infrastructure organizations must address all these sub-categories exclusively to achieve the first CPG.
Addressing these responsibilities requires a dynamic effort. Firstly, organizations must strengthen their IT and OT relationship by fostering more effective collaboration between the security teams of both departments. But, most importantly, IT and OT teams must come together to understand the potential cyber threats and risks of each environment and how it affects the other. To achieve the first CPG, it is critical that these departments are not kept in isolation but rather collaborate and communicate frequently.
At the same time, organizations must establish OT leadership by clearly identifying a single leader who will be responsible and accountable for OT-specific cybersecurity. From there, organizations must create an asset inventory or glossary that clearly identifies and tracks all OT and IT assets across the entire ecosystem. These assets should be regularly audited based on their vulnerability management program. It’s also highly critical to have an open, public, and easily accessible communication channel where vendors, third parties, or employees can disclose any potential vulnerability in relation to the OT and IT assets.
CISA’s second CPG is “Protect”, which emphasizes the account security aspects of OT assets. To achieve this goal, critical infrastructure organizations are required to strengthen their password policies, change default credentials across OT remote access systems, apply network segmentation to segregate OT and IT networks, and separate general user and privileged accounts.
Addressing all these aspects of account security can be a chore for most organizations, but they can turn to unified secure remote access (SRA) solutions that can extend multiple account-level security controls to OT remote users via enforcement of multi-factor authentication (MFA), least privilege policies, and role-based access. Such solutions can also support advanced credential policies to further reduce the risk of unauthorized access and denial of service attacks.
It’s also important that organizations only leverage SRA solutions that are based on zero trust policies. This will help organizations establish effective network segmentation that eliminates direct, unfettered remote connectivity to OT assets, and to continuously monitor personnel activity during all remote OT connections.
CISA’s third CPG emphasizes the detection of relevant threats and knowledge of potential attack vectors and TTPs (tactics, techniques, and procedures) that can compromise OT security and potentially disrupt critical services.
Detecting relevant threats and TTPs across OT assets and networks requires a proactive approach that combines advanced monitoring and analysis. Real-time monitoring solution should be complemented with comprehensive network visibility, allowing for the swift detection of anomalies and unusual patterns.
A critical aspect of threat detection in OT environments — and meeting the CPG mandate — is the sharing of information and collaboration between various stakeholders. Threat intelligence platforms play an essential role in gathering and disseminating information about current and emerging threats. By leveraging this valuable data, organizations can stay ahead of potential risks, fine-tune their defenses, and ensure the safety and security of their OT assets. Additionally, conducting regular security assessments, penetration testing, and vulnerability scanning will help uncover any weaknesses in the infrastructure, allowing for timely remediation and improved resilience against cyberattacks.
The final two CISA’s CPGs stress the importance of incident reporting and planning. Regardless of how robust your OT security practices are, cyber threats are almost inevitable in today’s interconnected and increasingly remote networking era. So, while proactive security solutions are necessary, attacks still are unavoidable, especially in a highly targeted sector like critical infrastructure.
Therefore, CISA stresses that organizations must have a comprehensive plan and process outlined for reporting security incidents and effectively recovering their affected systems or services upon a breach.
Advanced SRA solutions can help organizations to achieve these goals through automated recording of user activities and asset-related data, as well as creating automated backups of critical data. More specifically, they can log all user sessions, encrypt all user- and asset-related data, and retain logs of OT remote user activity. These measures help to ensure that critical information is stored in accordance with all relevant regulatory requirements and backup and recovery needs.
Overall, the vulnerabilities of ageing OT assets and siloed OT and IT networks have created a significant threat to critical infrastructure entities, which has been further exacerbated by the prevalence of remote access.
CISA’s OT-specific goals and actions within the CPGs provide a much-needed set of guidelines for CNI organizations to strengthen their security posture and increase cyber resilience. By following CISA’s recommendations and employing innovative security technologies, organizations can minimize the risk of cyberattacks affecting the physical world and public safety.


InfoSec tools | InfoSec services | InfoSec books
Feb 17 2023

In this Help Net Security video, Daniel Dos Santos, Head of Security Research at Forescout, talks about recent research, which has revealed how attackers can move laterally between vulnerable networks and devices found at the controller level of critical infrastructure. This would allow them to damage assets such as movable bridges physically.
This lateral movement lets attackers access industrial control systems and cross often-overlooked security perimeters to cause physical damage. From sensors that measure and detect pressure, temperature, flow and levels of liquids, air, and gases, to analyzers that determine chemical compositions and actuators that enable machines to move. Moving through these devices at the lowest levels, attackers can circumvent built-in functional and safety limitations to cause significant damage or disruption to services, or worse, pose a potential threat to life.
To demonstrate the potential implications, Forescout has built an industry-first proof-of-concept (PoC) which shows how attackers can move laterally on the controller level (Purdue level 1) to cause cyber and physical impact, as illustrated through the scenario of damaging a movable bridge during a closing sequence.
As part of the research, two new vulnerabilities are also being disclosed for the first time – CVE-2022-45788 and CVE-2022-45789 – which allows for remote code execution and authentication bypass, respectively, on Schneider Electric Modicon Unity Programmable Logic Controllers (PLCs).
Modicon PLCs are used in a wide range of industrial processes and critical infrastructure, including in industries such as water and wastewater, mining, manufacturing, and energy. Whilst these devices should not be accessible online, Forescout has found that close to a thousand PLCs have been exposed, with France (33%), Spain (17%), Italy (15%), and the United States (6%) revealed as the countries with the most exposed devices.
The number of devices visible is just a small indication of the popularity of these PLCs, but these devices also highlight some of the critical facilities that rely on them. For example, several devices were connected to hydro power plants, solar parks and airports.

Industrial Cybersecurity: Efficiently monitor the cybersecurity posture of your ICS environment
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Dec 29 2022

OT, ICS & SCADA Security
Infosec books | InfoSec tools | InfoSec services
Sep 22 2022

The National Security Agency (NSA) and CISA have issued guidance on how to secure operational technology (OT) and industrial control systems (ICSs) part of U.S. critical infrastructure.
The joint advisory shares info on all the steps used by malicious actors to compromise IT-enabled OT and ICS assets which provide a larger attack surface and highlights measures security professionals can take to defend against them.
“Cyber actors, including advanced persistent threat (APT) groups, have targeted OT/ICS systems in recent years to achieve political gains, economic advantages, and possibly to execute destructive effects. Recently, they’ve developed tools for scanning, compromising, and controlling targeted OT devices,” the NSA said.
The advisory also “notes the increasing threats to OT and ICS assets that operate, control, and monitor day-to-day critical infrastructure and industrial processes. OT/ICS designs are publicly available, as are a wealth of tools to exploit IT and OT systems.”
In today’s advisory [PDF], you can find detailed information on how to block threat actors’ attacks at every step, including attempts to collect intelligence, gain initial access, or deploy and execute malicious tools in compromised critical infrastructure systems.
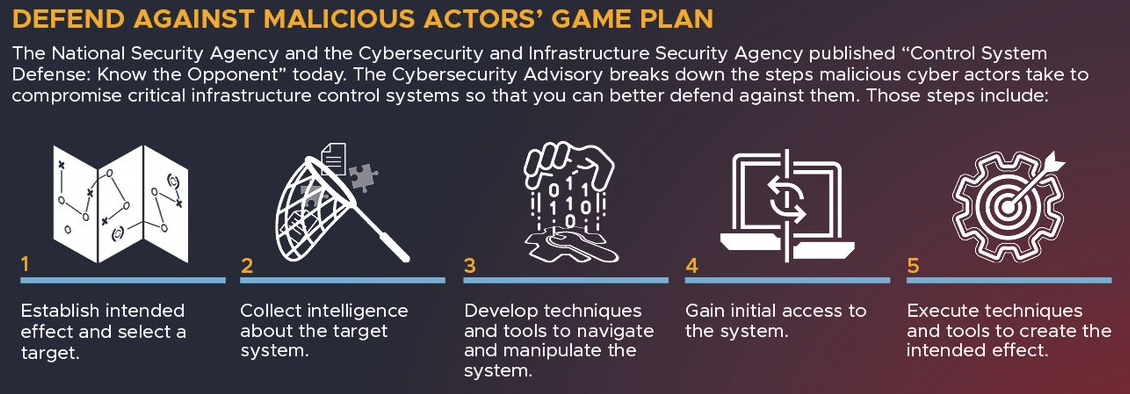
However, some defenders may be unable to implement some of the recommended security strategies that could help mitigate many common tactics used to target critical infrastructure control systems.
For them, NSA and CISA provide some security best practices to counter adversaries’ tactics, techniques and procedures (TTPs):
“It is vital for OT/ICS defenders to anticipate the TTPs of cyber actors combining IT expertise with engineering know-how,” the two federal agencies added.
“Defenders can employ the mitigations listed in this advisory to limit unauthorized access, lock down tools and data flows, and deny malicious actors from achieving their desired effects.”
Powering Through: Building Critical Infrastructure Resilience
Aug 08 2022

Industrial Cybersecurity: Efficiently monitor the cybersecurity posture of your ICS environment
Jul 27 2022
This article discusses OT security and why it is essential for protecting industrial systems from cyberattacks. We will also discuss common control objectives that can help companies improve their overall cybersecurity posture by implementing effective OT security measures.
Table of Contents

IT/OT Security Convergence And Risk Mitigation
#InfoSecTools and #InfoSectraining
Ask DISC an InfoSec & compliance related question
Jun 30 2022
Most third party risk programs are IT-focused – including suppliers that have access to the organization’s intellectual property or network. But some OT suppliers have access – physical and remote – to the OT environment, for troubleshooting, maintenance, etc., and it’s important that the risk posed by those suppliers is included in the enterprise third party risk program, since remote access to OT poses obvious security risks, and on-site access often involves USB drives and other direct electronic access which also can introduce malware into the OT environment. The good news is that these vendors can simply be included in existing third party risk programs.
On the other hand, more and more suppliers are being impacted by ransomware hitting their OT environment. This impacts their ability to provide their products and services to their customers, which can in turn impact their customers’ operations. Therefore, the scope of third party risk programs needs to be broadened once again to include critical suppliers in OT – those whose products or services are critical to the organization’s own OT operations. Now the bad news: existing third party risk programs typically do not assess security risk in OT environments. In fact, although frameworks and best practices are emerging in OT security, organizations usually need to rely on OT security experts to assist in these assessments and remediation recommendations.
Finally, we have seen increasing cyber attacks against the software supply chain, as well as attacks targeting vulnerabilities in critical OT products. When choosing suppliers of critical OT products, it is important to determine whether the vendor is certified to ISA/IEC 62443 – the leading security certification in OT. Those certifications should be an important factor in choosing products for the OT environment.
Industrial Cybersecurity: Efficiently monitor the cybersecurity posture of your ICS environment
Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoT
Apr 14 2022
The Department of Energy (DOE), the Cybersecurity and Infrastructure Security Agency (CISA), the National Security Agency (NSA), and the Federal Bureau of Investigation (FBI) published a joint Cybersecurity Advisory (CSA) to warn of offensive capabilities developed by APT actors that could allow them to compromise multiple industrial control system (ICS)/supervisory control and data acquisition (SCADA) devices, including:
According to the advisory that was issued with the help of leading cybersecurity firms (Dragos, Mandiant, Microsoft, Palo Alto Networks, and Schneider Electric), nation-state hacking groups were able to hack multiple industrial systems using a new ICS-focused malware toolkit dubbed PIPEDREAM that was discovered in early 2022.
“APT actors have developed custom-made tools that, once they have established initial access in an OT network, enables them to scan for, compromise, and control certain ICS/SCADA devices” reads the advisory.
“The APT actors’ tools have a modular architecture and enable cyber actors to conduct highly automated exploits against targeted devices. The tools have a virtual console with a command interface that mirrors the interface of the targeted ICS/SCADA device. Modules interact with targeted devices, enabling operations by lower-skilled cyber actors to emulate higher-skilled actor capabilities.”
The toolkit could allow to scan for targeted devices, conduct reconnaissance on device details, upload malicious configuration/code to the targeted device, back up or restore device contents, and modify device parameters.
Threat actors can also leverage a tool to install and exploit a known-vulnerable ASRock-signed motherboard driver (“AsrDrv103.sys“) by triggering the CVE-2020-15368 flaw to execute malicious code in the Windows kernel. The tool could be used to perform lateral movements within an IT or OT environment and interfere with devices’ operation.
Researchers from Dragos shared a detailed analysis of the new PIPEDREAM toolkit confirming that it has yet to be employed in attacks in the wild.
“PIPEDREAM is the seventh known ICS-specific malware. The CHERNOVITE Activity Group (AG) developed PIPEDREAM. PIPEDREAM is a modular ICS attack framework that an adversary could leverage to cause disruption, degradation, and possibly even destruction depending on targets and the environment.” reads the report published by Dragos. “Dragos assesses with high confidence that PIPEDREAM has not yet been employed in the wild for destructive effects. This is a rare case of accessing and analyzing malicious capabilities developed by adversaries before their deployment and gives defenders a unique opportunity to prepare in advance.”
Mandiant, which tack the toolkit as INCONTROLLER, also published a detailed analysis warning of its dangerous cyber attack capability.
“The tools can interact with specific industrial equipment embedded in different types of machinery leveraged across multiple industries. While the targeting of any operational environments using this toolset is unclear, the malware poses a critical risk to organizations leveraging the targeted equipment. INCONTROLLER is very likely state sponsored and contains capabilities related to disruption, sabotage, and potentially physical destruction.” reads the analysis published by Mandiant. “INCONTROLLER represents an exceptionally rare and dangerous cyber attack capability. It is comparable to TRITON, which attempted to disable an industrial safety system in 2017;”
The joint report also included the following recommendations for all organizations with ICS/SCADA devices:

Industrial Cybersecurity: Efficiently monitor the cybersecurity posture of your ICS environment
👇 Please Follow our LI page…
#InfoSecTools and #InfoSectraining
Mar 23 2022
“Most of America’s critical infrastructure is owned and operated by the private sector and critical infrastructure owners and operators must accelerate efforts to lock their digital doors,” he noted, and advised those that have not yet done it to harden their cyber defenses by implementing security best practices delineated earlier this year.
“[This warning is] based on evolving intelligence that the Russian Government is exploring options for potential cyberattacks,” he added.
US Deputy National Security Advisor Anne Neuberger has followed up the warning with a press briefing, during which she stated that “there is no certainty there will be a cyber incident on critical infrastructure,” but that owners and operators of critical infrastructre have the ability and the responsibility to harden the systems and networks the country relies on.
She shared that last week, federal agencies hosted classified briefings with several hundred companies in sectors they felt would be most affected, and “provided very practical, focused advice.”
Previously, the Cybersecurity and Infrastructure Security Agency (CISA) released guidance to help critical infrastructure owners and operators identify and mitigate the risks of influence operations that use mis-, dis-, and malinformation (MDM) narratives.
Neuberger also said that US agencies have not yet attributed the recent attack on satellite communications company Viasat. Nevertheless, the attack has been followed by a CISA alert advising SATCOM network providers or customers on how to upgrade their defenses.

Feb 07 2022
The attacks on critical industrial systems such as Colonial Pipeline last year pushed industrial cybersecurity to center stage. And with the threat of war between Russia and Ukraine, experts warned nations that a global flare-up of cybersecurity attacks on critical infrastructure could be looming. In late January, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) put critical infrastructure organizations on notice: Take “urgent, near-term steps” to mitigate the risk of digital attacks. The alert cited tension in eastern Europe as the catalyst for possible attacks against U.S. digital assets.
Unfortunately, critical systems have long been under significant attack. In fact, an overwhelming 80% of critical infrastructure organizations experienced ransomware attacks last year, according to a survey released today by PollFish on behalf of cyber-physical systems security provider Claroty. The survey, completed in September 2021, gathered responses from full-time information technology and operational technology (OT) security professionals in the United States (500 professionals), Europe (300) and Asia-Pacific (300). The industries surveyed include IT hardware, oil and gas (including pipelines), consumer products, electric energy, pharmaceutical/life sciences/medical devices, transportation, agriculture/food and beverage, heavy industry, water and waste and automotive.
Globally, 80% of respondents reported experiencing an attack and 47% of respondents said the attack impacted their operational technology and industrial control systems environment. A full 90% of respondents that reported their attacks to authorities or shareholders said the impact of those attacks was substantial in 49% of cases.
Cybersecurity Investments
Effectiveness of National Cyber Policy to Strengthen the Security and Resilience of Critical Infrastructure Against Cyber Attacks