CyberAv3ngers targeting Unitronics PLCs
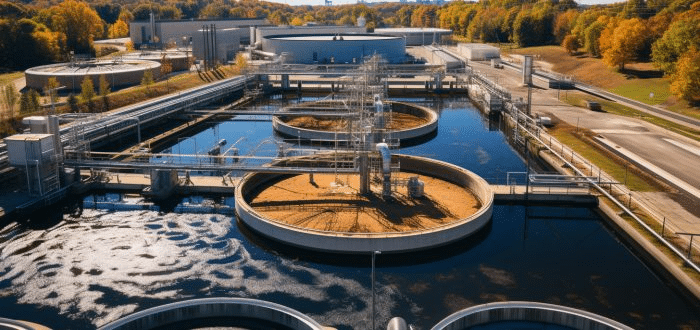
CISA has recently confirmed that Iran-affiliated attackers took over a Unitronics Vision Series PLC at a water system facility in Pennsylvania, and urged other water authorities to promptly secure their Unitronics PLCs.
The agency has advised them to change the default password and port used by the PLC, disconnect it from the open internet or secure remote access by using firewall, VPN and multi-factor authentication (MFA), create configuration backups, and update the PLC/HMI to the latest available version.
CyberAv3ngers has previously claimed responsibility for numerous attacks against critical infrastructure organizations in Israel working in the water, energy, shipping, and distribution sectors, and only recently targeted Unitronics PLCs deployed by multiple US-based water and wastewater facilities.
In the latest advisory, the agencies shared additional information about the APT group’s activites and indicators of compromise (IoCs) associated with their most recent attacks.
“These PLC and related controllers are often exposed to outside internet connectivity due to the remote nature of their control and monitoring functionalities. The compromise is centered around defacing the controller’s user interface and may render the PLC inoperative. With this type of access, deeper device and network level accesses are available and could render additional, more profound cyber physical effects on processes and equipment,” the advisory explains.
“It is not known if additional cyber activities deeper into these PLCs or related control networks and components were intended or achieved. Organizations should consider and evaluate their systems for these possibilities.”
The UK National Cyber Security Centre (NCSC) says that the compromise of the PLCs is “highly unlikely” to disrupt routine operations of affected organizations. “There is a very low potential risk, if the threat is unmitigated, to some small suppliers,” they noted.
The agencies repeated CISA’s initial risk mitigation advice and urged organizations to apply it to all internet-facing PLCs, not just those manufactured by Unitronics (which, it has been pointed out, may also be rebranded and appear as made by different manufacturers).
Finally, they called on device manufacturers to do their part in securing OT devices by:
- Not shipping products with default passwords
- Avoiding the exposure of administrative interfaces to the internet
- Not imposing additional fees for security features
- Making sure the devices support MFA
Cybersecurity for Industrial Control Systems: SCADA, DCS, PLC, HMI, and SIS
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory




