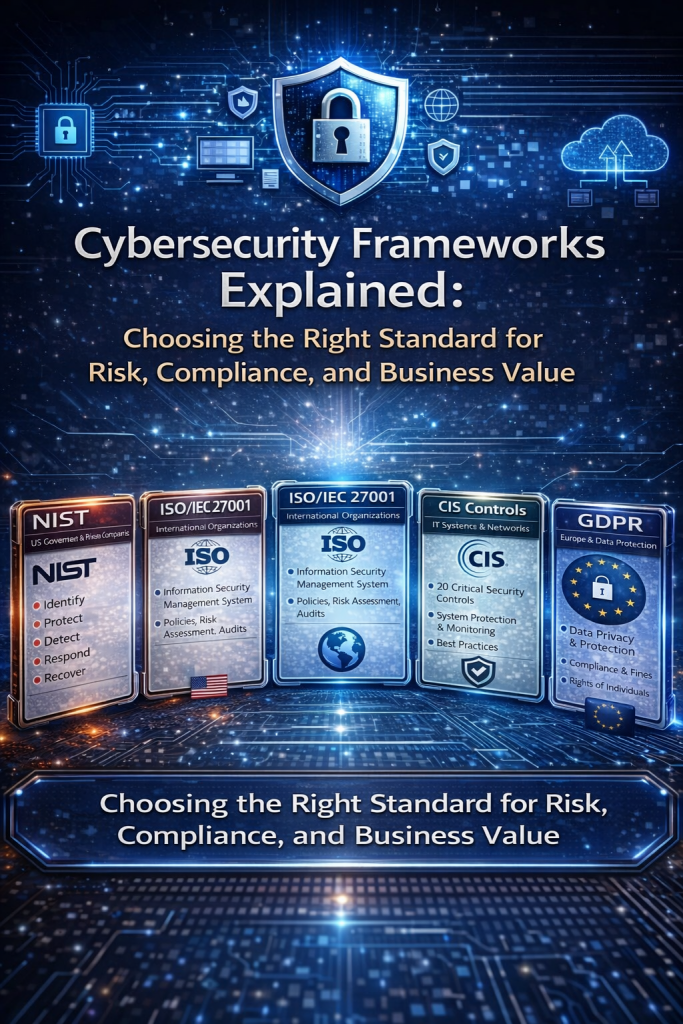
NIST Cybersecurity Framework (CSF)
The NIST Cybersecurity Framework provides a flexible, risk-based approach to managing cybersecurity using five core functions: Identify, Protect, Detect, Respond, and Recover. It is widely adopted by both government and private organizations to understand current security posture, prioritize risks, and improve resilience over time. NIST CSF is particularly strong as a communication tool between technical teams and business leadership because it focuses on outcomes rather than prescriptive controls.
ISO/IEC 27001
ISO/IEC 27001 is an international standard for establishing, implementing, and maintaining an Information Security Management System (ISMS). It emphasizes governance, risk assessment, policies, audits, and continuous improvement. Unlike NIST, ISO 27001 is certifiable, making it valuable for organizations that need formal assurance, regulatory credibility, or customer trust across global markets.
CIS Critical Security Controls
The CIS Controls are a prioritized set of practical, technical security best practices designed to reduce the most common cyber risks. They focus on actionable safeguards such as system hardening, access control, monitoring, and incident detection. CIS is highly effective for organizations that want fast, measurable security improvements without the overhead of full governance frameworks.
PCI DSS
PCI DSS is a mandatory compliance standard for organizations that store, process, or transmit payment card data. It focuses on securing cardholder data through access control, monitoring, encryption, and vulnerability management. PCI DSS is narrowly scoped but very detailed, making it essential for payment security but insufficient as a standalone enterprise security framework.
COBIT
COBIT is an IT governance and management framework that aligns IT processes with business objectives, risk management, and compliance requirements. It is less about technical security controls and more about decision-making, accountability, performance measurement, and process maturity. COBIT is commonly used by large enterprises, auditors, and boards to ensure IT delivers business value while managing risk.
GDPR
GDPR is a data protection regulation focused on privacy rights, lawful data processing, and accountability for personal data handling within the EU (and beyond). It requires organizations to implement strong data protection controls, transparency mechanisms, and breach response processes. GDPR is regulatory in nature, with significant penalties for non-compliance, and places individuals’ rights at the center of security and governance efforts.
Opinion: When and How to Apply These Frameworks
In practice, no single framework is sufficient on its own. The most effective security programs intentionally combine frameworks based on business context, risk exposure, and regulatory pressure.
- Use NIST CSF when you need a strategic, flexible starting point to assess risk, communicate with leadership, or build a roadmap without jumping straight into certification.
- Adopt ISO/IEC 27001 when you need formal governance, customer assurance, or regulatory credibility, especially for SaaS, global operations, or enterprise clients.
- Implement CIS Controls when your priority is rapid risk reduction, technical hardening, and improving day-to-day security operations.
- Apply PCI DSS only when payment data is involved—treat it as a mandatory baseline, not a full security program.
- Use COBIT when security must be tightly integrated with enterprise governance, audit expectations, and board oversight.
- Comply with GDPR whenever personal data of EU residents is processed, and use it to strengthen privacy-by-design practices globally.
How Do You Know Which Framework Is Relevant?
You know a framework is relevant when it clearly answers one or more of these questions for your organization:
- What regulatory or contractual obligations do we have?
- What risks matter most to our business model?
- Who needs assurance—customers, regulators, auditors, or the board?
- Do we need outcomes, controls, certification, or governance?
The right framework is the one that reduces real risk, supports business goals, and can actually be operationalized by your organization—not the one that simply looks good on paper. Mature security programs evolve by layering frameworks, not replacing them.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- AI Can Pentest Your Network Now. That’s Not the Risk You Should Worry About
- GRC at Machine Speed: How AI Is Reshaping Governance, Risk, and Compliance
- Building AI Governance That Actually Works: From Ethics to the Exam Room
- Corporate Visibility as an Attack Surface: Managing Risk in the AI Era
- GRC Engineering Is the Future of Cloud Compliance