
How Security Is, First and Foremost, a People Issue
At its core, security depends on human behavior—how people design systems, configure controls, respond to threats, and make daily decisions. Technology can enforce rules and automate defenses, but humans create, manage, and sometimes bypass those controls. Most incidents—whether phishing, misconfigurations, or insider actions—originate from human choices. That’s why effective security programs focus not just on tools, but on awareness, accountability, and behavior change across the organization.
“If Someone Can Build It, Someone Can Break It”
This idea reflects a fundamental truth: no system is perfectly secure. Anything created by humans can be understood, tested, and eventually exploited by others. Attackers are often just as creative and persistent as builders. This reinforces the need for continuous improvement, testing, and a mindset that assumes systems can fail—so defenses must evolve constantly.
Most Breaches Start with Human Behavior
A large percentage of security incidents begin with human actions—clicking phishing links, using weak passwords, misconfiguring systems, or mishandling data. These are not purely technical failures but behavioral ones. Addressing this requires training, clear processes, and designing systems that reduce the likelihood of human error.
Technology Enables, but People Decide
Security tools provide capabilities—monitoring, detection, prevention—but they don’t make decisions in isolation. People choose how tools are configured, how alerts are handled, and how risks are prioritized. Poor decisions can weaken even the best technology, while informed decisions can make simple tools highly effective.
Security Culture Matters Most
A strong security culture ensures that everyone—not just the security team—takes responsibility for protecting the organization. When employees understand the importance of security and feel accountable, they make better decisions by default. Culture drives consistent behavior, which ultimately determines how resilient an organization is against threats.
My Perspective (Practical & Strategic)
This post highlights one of the most overlooked truths in cybersecurity: tools don’t fail—people and processes do.
In many organizations, there’s an overinvestment in technology and an underinvestment in people. Companies buy advanced tools (EDR, SIEM, AI security platforms), but still get breached due to:
- Misconfigurations
- Ignored alerts
- Lack of training
- Poor decision-making under pressure
From a vCISO perspective, this is where real value is created.
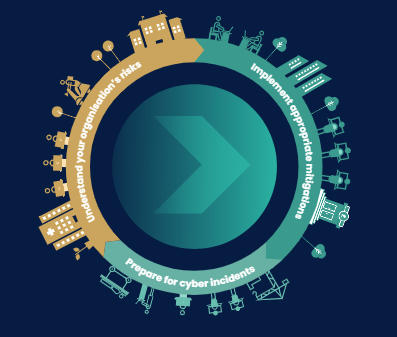
A mature, people-centric security strategy should:
- Treat users as part of the security control system—not the weakest link
- Design “secure-by-default” processes that reduce human error
- Align incentives so teams are rewarded for secure behavior
- Embed security into daily workflows—not just annual training
The biggest shift is moving from blaming users → designing for users.
Because in reality:
- People will click
- People will make mistakes
- People will take shortcuts
The question is: Does your security program expect that—or ignore it?
Organizations that win build a security-first culture, where:
- Employees act as sensors (report threats early)
- Leaders model security behavior
- Security becomes part of how business is done—not an afterthought
That’s when security stops being reactive… and becomes truly resilient.
That’s the level where security leadership becomes strategic—and where vCISOs deliver the most value.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- AI Model Risk Management Is Becoming the Foundation of Enterprise AI Governance
- Sun Tzu for the AI Governance Era: 7 Strategic Rules for InfoSec and Compliance Leaders
- Your Shadow AI Inventory Is Wrong. Here’s a Free Way to Fix It.
- The AI Agent Identity Crisis Has Already Started
- OWASP 2026 GenAI Risk Catalogue Signals a New Era of AI Security Governance












![IT Vendor Risk Management A Complete Guide - 2021 Edition by [Gerardus Blokdyk]](https://m.media-amazon.com/images/I/41jZ5XeJBgL.jpg)





