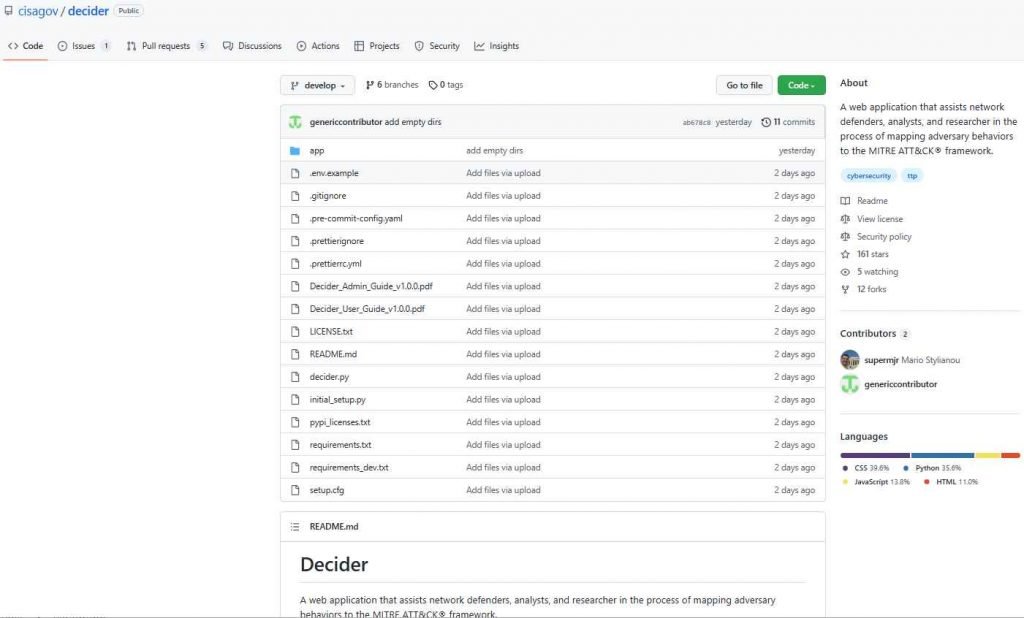
Decider is a new, free tool that was launched today by CISA. It is designed to assist the cybersecurity community in mapping the behavior of threat actors to the MITRE ATT&CK framework. Through the use of guided questions, a powerful search and filter function, and a cart functionality that allows users to export results to commonly used formats, Decider helps make mapping both quick and accurate. It was developed in collaboration with the Homeland Security Systems Engineering and Development Institute (HSSEDI) and MITRE.
To get started with Decider, network defenders, analysts, and researchers may get started by viewing the video, information sheet, and blog posted by CISA. CISA strongly recommends that users of the community make use of the tool in tandem with the newly revised Best Practices for MITRE ATT&CK Mapping guidance. The MITRE ATT&CK framework is a lens that network defenders can use to analyze the behavior of adversaries, and it directly supports “robust, contextual bi-directional sharing of information to help strengthen the security of our systems, networks, and data,” as CISA Executive Assistant Director Eric Goldstein noted in his June 2021 blog post on the framework. Since it offers a standardized vocabulary for the evaluation of threat actors, the CISA strongly recommends that the cybersecurity community make use of the framework.
This revision of the best practices was made in collaboration with the Homeland Security Systems Engineering and Development InstituteTM (HSSEDI), which is a research and development facility owned by the Department of Homeland Security and run by MITRE. Since CISA first released the best practices in June 2021, the update addresses the modifications that the MITRE ATT&CK team has made to the framework as a result of those improvements. Moreover, frequent analytical biases, mapping problems, and particular ATT&CK mapping guidelines for industrial control systems are included in this version (ICS).
This tool leads users through a mapping process by asking them a series of guided questions concerning enemy behavior. The purpose of these questions is to assist users in determining the appropriate strategy, technique, or sub-technique. In addition to the application itself, users are given access to a data sheet and a short film that will acquaint them with the most important capabilities and features that Decider offers.
Previous posts on Security Tools
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services





March 30th, 2026 10:31 am
[…] ‘DECIDER’ AN OPEN-SOURCE TOOL THAT HELPS TO GENERATE MITRE ATT&CK MAPPING REPORTS […]