InfoSec tools | InfoSec services | InfoSec books
InfoSec and Compliance – With 20 years of blogging experience, DISC InfoSec blog is dedicated to providing trusted insights and practical solutions for professionals and organizations navigating the evolving cybersecurity landscape. From cutting-edge threats to compliance strategies, this blog is your reliable resource for staying informed and secure. Dive into the content, connect with the community, and elevate your InfoSec expertise!
Jul 07 2023
Jul 04 2023
Chief Information Security Officers (CISOs) hold a critical and challenging role in today’s rapidly evolving cybersecurity landscape. Here are the common security challenges CISOs face.
As organizations increasingly rely on technology to drive their operations, CISOs face complex security challenges that demand their expertise and strategic decision-making.
These challenges arise from the constant emergence of sophisticated cyber threats, the need to protect sensitive data, and the ever-evolving regulatory landscape.
The role of a CISO requires balancing proactive risk mitigation with the ability to respond swiftly to incidents and breaches.
This article will delve into the top challenges CISOs face, including protecting digital assets, managing security incidents, ensuring compliance, dealing with insider threats, and the relentless pursuit of cyber resilience.
By understanding these challenges, CISOs can develop robust cybersecurity strategies and lead their organizations toward a secure and resilient future.
Chief Information Security Officer (CISO) is a senior executive responsible for overseeing and administering an organization’s information security plan.
A CISO’s primary responsibility is safeguarding the confidentiality, availability, and integrity of an organization’s information assets and systems.
They are accountable for creating and enforcing strategies, policies, and procedures to defend against cyber threats, protect sensitive data, and mitigate security risks.
CISOs play a crucial role in maintaining an organization’s security posture by establishing and enforcing security standards, conducting risk assessments, and implementing appropriate security controls.
They collaborate with other executives, IT teams, and stakeholders to align security initiatives with business objectives and ensure that security measures are integrated into the organization’s operations.
In addition to their technical expertise, CISOs often engage in risk management, incident response planning, security awareness training, and compliance with regulatory requirements.
They stay updated on the latest cybersecurity trends, threats, and technologies to address emerging risks and implement appropriate security measures effectively.
The role of a CISO has become increasingly important as cyber threats evolve in complexity and frequency.
CISOs are responsible for safeguarding the organization’s sensitive information, maintaining the trust of customers and stakeholders, and ensuring business continuity in the face of cybersecurity challenges.
CISO Guide to Balancing Network Security Risks Offered by Perimeter 81 for free, helps to prevent your network from being at Risk.
CISOs face various common security challenges as they strive to protect their organizations’ digital assets and information. Perimeter 81 Guide helps CISOs to prevent their network from being at Risk. Some of the key challenges they encounter include:
As a Chief Information Security Officer (CISO), there are several security compliance frameworks and regulations that you should consider following, depending on the nature of your organization and its operations. Here are some of the key security compliance frameworks and regulations:
Managing a security team as a Chief Information Security Officer (CISO) requires effective leadership, communication, and coordination. Here are some key aspects to consider when managing a security team:
CISOs face many common security challenges as protectors of their organization’s digital assets and information.
From sophisticated cyberattacks and insider threats to compliance requirements and resource constraints, these challenges highlight the complex and evolving nature of the cybersecurity landscape.
CISOs must navigate these challenges by adopting a proactive and strategic approach to security, leveraging advanced technologies, fostering a strong security culture, and collaborating with stakeholders.
To overcome these challenges, CISOs must stay abreast of emerging threats, continuously evaluate and improve their security measures, and prioritize investments in critical security capabilities.
They must also foster strong partnerships with internal teams, third-party vendors, and industry peers to collectively address security challenges and share best practices.
While the security challenges CISOs face may seem daunting, they also present opportunities for innovation and growth.
By effectively addressing these challenges, CISOs can enhance their organizations’ security posture, safeguard critical assets, and instill confidence in customers and stakeholders.
Ultimately, the role of a CISO requires a comprehensive and adaptable approach to cybersecurity, where staying one step ahead of threats and continuously improving security measures are paramount.
By embracing these challenges, CISOs can help shape a secure and resilient future for their organizations in an increasingly interconnected and threat-filled digital landscape.
InfoSec tools | InfoSec services | InfoSec books
Jul 01 2023
CISSP books – Official (ISC)2® Guides
CISSP training

InfoSec tools | InfoSec services | InfoSec books
Jun 30 2023
This attack method can help attackers surpass all barriers to exploit side channels, which so far were not possible.

The cybersecurity researchers from the Ben-Gurion University of the Negev and Cornell University have revealed how a side-channel attack targeting a smart card reader’s power LED can recover encryption keys.
This ground-breaking method can help adversaries extract encryption keys from a device simply by analyzing the video footage of its power LED. This happened because the CPU’s cryptographic computations can change the power consumption of a device and impact the brightness of its power LED.
This ingenious attack method leverages the connection between a device’s power consumption and the brightness of its power LED. Adversaries can obtain secret keys from the RGB values as the LED’s brightness changes when the CPU performs cryptographic operations.
They exploited the flickering of the power LED during this operation and used their understanding of the card reader’s inner workings to decode the keys and gain access.
The team conducted two side-channel cryptanalytic timing attacks using this video-based cryptanalysis method. After examining the video footage of the power LED, they recovered a 256-bit ECDSA key from the smart card using a compromised internet-connected security camera. They placed the camera at a distance of 16 meters from the smart card reader.
Next, they recovered a 378-bit SIKE key from a Samsung Galaxy S8 by analyzing the video footage of the power LED of Logitech Z120 USB speakers connected to the USB hub they used to charge the Galaxy S8.
“This is caused by the fact that the power LED is connected directly to the power line of the electrical circuit, which lacks effective means (e.g., filters, voltage stabilizers) of decoupling the correlation with the power consumption,” researchers explained in their report.
But, this technique is not as simple as it seems because merely observing the LED with a camera cannot help recover security keys, even if the frame rate is considerably high. To record the rapid changes in an LED’s brightness using a standard webcam or smartphone camera, turning on the rolling shutter effect is essential, as this is when camera sensors start recording images line by line.
In a regular setting, the camera will record the entire image sensor. Using the same technique, attackers can exploit the video camera of an internet-connected security camera or even an iPhone 13 camera to obtain cryptographic keys. Cybersecurity researchers have shown concerns as this attack method will help attackers surpass all barriers to exploit side channels, which so far were not possible. The method’s non-intrusiveness makes it even more sinister.
However, as with every attack, there are some limitations to this one. For example, apart from being placed at a 16m distance, the camera should be in the direct line of sight view of the LED, and signatures should be recorded for 65 minutes.
Countering such attacks is possible if LED manufacturers add capacitors to reduce power consumption fluctuations. An alternate solution is covering the power LED with black tape to prevent information exposure.
Researchers have shared their explosive findings in a paper titled “Video-Based Cryptanalysis: Extracting Cryptographic Keys from Video Footage of a Device’s Power LED,” available here (PDF).
InfoSec tools | InfoSec services | InfoSec books
Jun 29 2023
Defending Continuous Integration/Continuous
Delivery (CI/CD) Environments
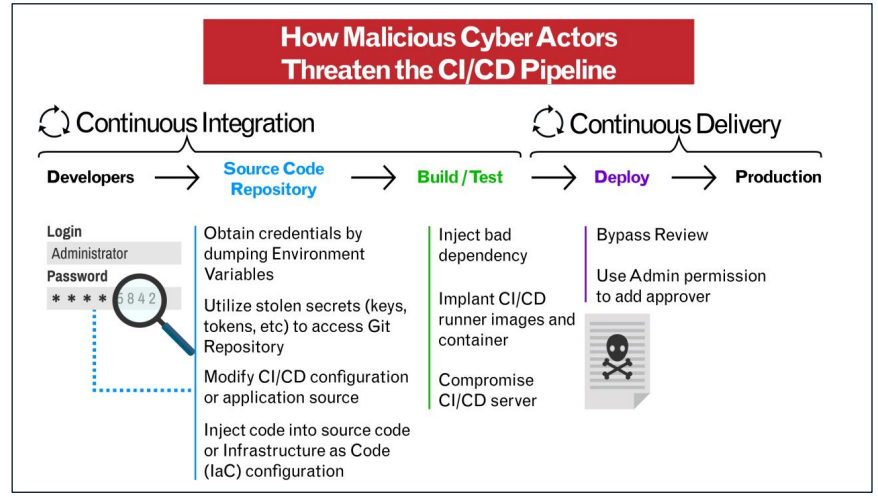
NSA Tips: Defending Continuous Integration/Continuous Delivery (CI/CD) Environments
InfoSec tools | InfoSec services | InfoSec books
Jun 29 2023

https://therecord.media/nso-group-robert-simonds-white-house-national-security-council
The White House National Security Council cautioned on Wednesday that it will review any attempted takeover of foreign commercial surveillance software by an American company to determine whether the acquisition poses a “counterintelligence threat” to the U.S. government.
The statement came in response to reporting from the Guardian revealing that a chewing gum heir and producer of several Adam Sandler movies is considering a bid for the NSO Group, including its powerful Pegasus spyware.
The Biden administration is concerned about the spread of foreign commercial surveillance tools like Pegasus and believes they “pose a serious counterintelligence and security risk to U.S. personnel and systems,” the statement said.
The Hollywood producer, Robert Simonds, was responsible for more than 30 movies that made in excess of $6 billion earlier in his career and more recently had worked as the chairman of STX Entertainment, which Variety calls a “fully integrated entertainment outlet” focused on expanding into emerging global markets on a variety of platforms. Simonds’ credits with Sandler include “Happy Gilmore,” “The Wedding Singer” and “Billy Madison.”
According to the Guardian, Simonds was recently picked to run the Luxembourg-based holding company controlling NSO. Sources told the Guardian that Simonds is considering ways to take over some of the spyware firm’s assets in an effort to give the Five Eyes intelligence partnership of the US, the UK, Canada, Australia and New Zealand exclusive access to the potent technology.
Pegasus and similar tools are being “misused around the world to enable human rights abuses and target journalists, human rights activists, political opposition members, or others perceived as dissidents and critics,” the White House statement said, noting that the Biden administration has launched a government-wide effort to stop Pegasus and other foreign commercial surveillance software from spreading. In March, the administration issued an executive order barring all U.S. government agencies from using the spyware, among other measures.
In its statement the White House also warned that U.S. companies should “be aware that a transaction with a foreign entity on the Entity List will not automatically remove the designated entity from the Entity List.” The list, published by the United States Department of Commerce’s Bureau of Industry and Security (BIS), restricts trade with specified foreigners, foreign entities, or governments. Companies included on the Entity List must meet strict licensing requirements for exports.
NSO has been on the Entity List since 2021. Despite the controversy swirling around the firm, its unprecedented technology has long attracted the attention of investors. Pegasus can hack into users’ phones remotely, activating the camera and microphone without a user knowing, as well as intercept all communications, including over encrypted apps like Signal.
Last July, the American defense firm L3Harris decided not to pursue a bid for NSO after initial explorations led to a backlash from the Biden administration

InfoSec tools | InfoSec services | InfoSec books
Jun 29 2023
In this course, you’ll learn how to protect information to ensure its integrity, confidentiality, authenticity, and non-repudiation.
You will develop a basic understanding of cryptographic concepts and how to apply them, implement secure protocols, key management concepts, critical administration and validation, and Public Key Infrastructure.

In this course, you will learn about the network structure, data transmission methods, transport formats, and the security measures used to maintain integrity, availability, authentication, and confidentiality of the information being transmitted. Concepts for both public and private communication networks will be discussed.
Course objectives:
1. Describe network-related security issues
2. Identify protective measures for telecommunication technologies
3. Define processes for controlling network access
4. Identify processes for managing LAN-based security
5. Describe procedures for operating and configuring networked-based security devices
6. Define procedures to implement and operate wireless technologies

This course is a complete foundational security awareness training program that covers a wide array of topics for nearly every type of end-user and learner level. The content is designed to allow organizations to be able to provide a comprehensive training program to help them protect their information assets against threats.
This training lasts approximately 2 hours, was designed to be engaging, and is based on real scenarios staff may face. The training is modular and must not be completed in one sitting.

This course addresses basic security concepts and the application of those concepts in the day to day operation and administration of enterprise computer systems and the information that they host. Ethical considerations in general, and the (ISC)² Code of Ethics in particular, provide the backdrop for any discussion of information security and SSCP candidates will be tested on both. Information security professionals often find themselves in positions of trust and must be beyond reproach in every way.
Several core information security principles stand above all others and this domain covers these principles in some depth. The CIA triad of confidentiality, integrity and availability forms the basis for almost everything that we do in information security and the SSCP candidate must not only fully understand these principles but be able to apply them in all situations. additional security concepts covered in this domain include privacy, least privilege, non-repudiation and the separation of duties.

In this course, you will gain an understanding of computer code that can be described as harmful or malicious. Both technical and non-technical attacks will be discussed. You will learn how an organization can protect itself from these attacks. You will learn concepts in endpoint device security, cloud infrastructure security, securing big data systems, and securing virtual environments.
Course objectives:
1. Identify malicious code activity
2. Describe malicious code and the various countermeasures
3. Describe the processes for operating endpoint device security
4. Define mobile device management processes
5. Describe the process for configuring cloud security
6. Explain the process for securing big data systems
7. Summarize the process for securing virtual environments

Cyber security courses (mostly free)

InfoSec tools | InfoSec services | InfoSec books | Follow our blog
Jun 29 2023
An specialist in Russian cybersecurity who was sought by the United States has been arrested by officials in Kazakhstan, according to his employer, who made the announcement on Wednesday. At the same time, authorities in Moscow said that they will also pursue his extradition.
According to a statement released by the business, Nikita Kislitsin, an employee of the Russian cybersecurity firm F.A.C.C.T., was arrested on June 22. The Kazakh authorities are now reviewing an extradition request from the United States of America. Nikita Kislitsin was arrested in 2012 and accused of selling the usernames and passwords of American clients of the social networking firm Formspring. The facts of the arrest and the motivation for it are not clear; nonetheless, the case against Kislitsin was filed. After Group-IB left Russia earlier this year, the spinoff business that was established there and was branded as F.A.C.C.T. had Kislitsin working as the head of network security for both companies.
According to a statement released by Group-IB on Telegram, the arrest of Kislitsin is not connected to his employment there in any way. The F.A.C.C.T. said that the allegations brought against Kislitsin originated from his time “as a journalist and independent researcher,” but they could not disclose any other information. Kislitsin served as the editor-in-chief of the Russian publication “Hacker,” which is primarily concerned with information security and hacking at one point in his career.
In a separate proceeding that took place on Wednesday, a Moscow court issued a warrant for Kislitsin’s arrest on allegations that are associated with the unlawful access of confidential computer information. Russia has indicated that it would demand his extradition from Kazakhstan as well.

InfoSec tools | InfoSec services | InfoSec books
Jun 28 2023
Researchers at Censys have analyzed the attack surfaces of more than 50 Federal Civilian Executive Branch (FCEB) organizations and sub-organizations and discovered more than 13,000 distinct hosts across 100 autonomous systems.
The experts focused on roughly 1,300 of these hosts that were accessible online and discovered hundreds of devices with management interfaces exposed to the public internet.
These devices clearly are not compliant with the BOD 23-02 directive released in June by the US CISA with the objective of mitigating the risks associated with remotely accessible management interfaces.
“The Directive requires federal civilian executive branch (FCEB) agencies to take steps to reduce their attack surface created by insecure or misconfigured management interfaces across certain classes of devices.” states CISA.
Censys specifically looked for publicly accessible remote management interfaces associated with networked devices, including routers, access points, firewalls, VPNs, and other remote server management technologies.
“In the course of our research, we discovered nearly 250 instances of web interfaces for hosts exposing network appliances, many of which were running remote protocols such as SSH and TELNET.” reads the analysis published by Censys. “Among these were various Cisco network devices with exposed Adaptive Security Device Manager interfaces, enterprise Cradlepoint router interfaces exposing wireless network details, and many popular firewall solutions such as Fortinet Fortiguard and SonicWall appliances.”
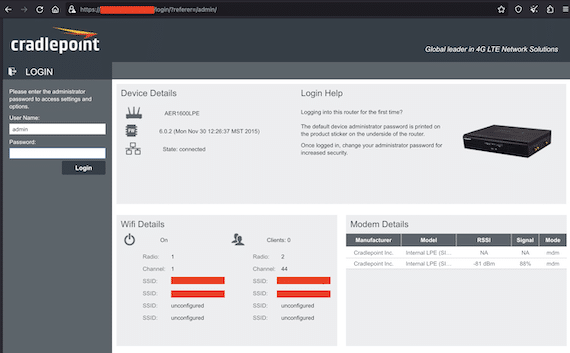
The researchers discovered 15 instances of exposed remote access protocols such as FTP, SMB, NetBIOS, and SNMP that were running on hosts exposed by Federal Civilian Executive Branches (FCEB). These protocols are known to be plagued by multiple security vulnerabilities that can be exploited by threat actors to compromise them and gain remote unauthorized access to government infrastructure.
The report also states that multiple out-of-band remote server management devices such as Lantronix SLC console servers were exposed only despite CISA’s directive stating that “these out-of-band interfaces should never be directly accessible via the public internet.”
The study also revealed that multiple federal civilian executive branch were exposing managed file transfer tools, such as MOVEit transfer, GoAnywhere MFT, VanDyke VShell file transfer, and SolarWinds Serv-U file transfer. These devices are often the targets of attacks from different threat actors.
“Exposed physical Barracuda Email Security Gateway appliances, which recently made headlines after a critical zero day was discovered being actively exploited to steal data” concludes the report. “Over 150 instances of end-of-life software, including Microsoft IIS, OpenSSL, and Exim. End-of-life software is more susceptible to new vulnerabilities and exploits because it no longer receives security updates, making it an easy target.”
According to BOD 23-02, FCEB agencies have to secure the devices within 14 days of identifying one of these devices.
InfoSec tools | InfoSec services | InfoSec books
Jun 28 2023
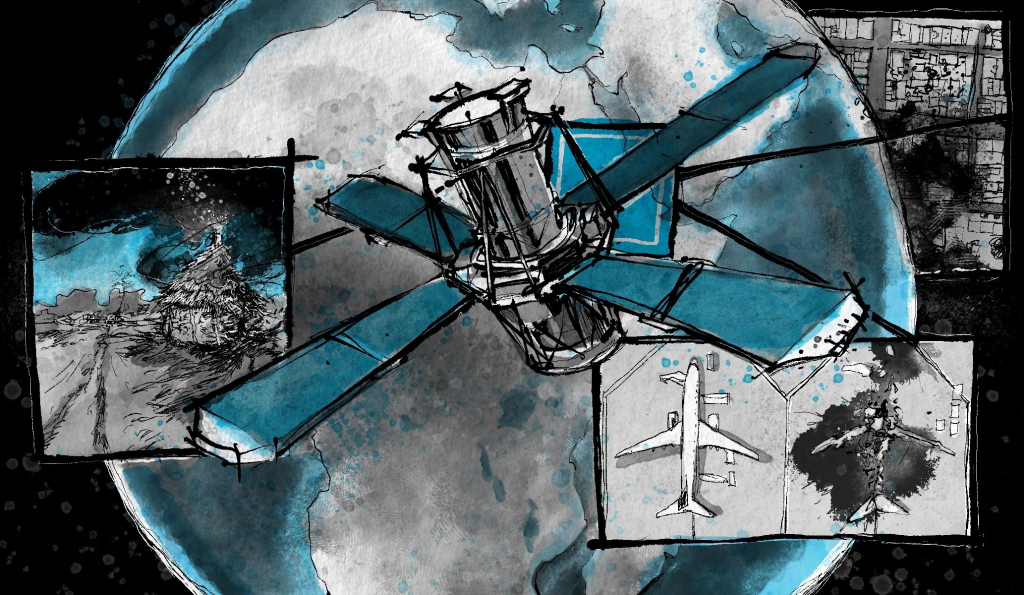
Since April, Sudan has been rocked by fighting between two factions of its army. At first, the violence was contained in the capital city, Khartoum, but in recent days fighting has flared up in western Darfur, ground zero for a genocide that started back in 2003 and left hundreds of thousands dead.
Arab militiamen, known as janjaweed, or “devils on horseback,” were able to kill so many in Darfur in such a short time because the area is so remote — there was no one to witness the atrocities or hold the perpetrators to account, so they continued apace.
That’s what makes this latest conflict so different: Technology is allowing third-party observers to document human rights abuses in near real time thanks to, among other things, low-orbit satellites.
Researchers like Nathaniel Raymond, the executive director of Yale’s Humanitarian Research Lab, have been using satellites not just to document the violence, but with the right on-the-ground intelligence, to predict attacks before they happen.
The team recently documented evidence of war crimes in Ukraine with a report that provided both photographic and other proof that Russia was behind the systematic relocation of thousands of children from Ukraine into Russia and Russian-controlled regions of Ukraine.
Now Raymond and the team are working with the U.S. State Department to document human rights abuses in Sudan. It is a bit of a homecoming for them — they pioneered the use of satellite analysis and open-source intelligence in Darfur more than a decade ago and now they are back with better tools and a focus on ending a crisis that is decades in the making.
This conversation has been edited for length and clarity.
Click Here: Let’s start at the beginning. Can you explain how you got into this work?
https://therecord.media/tracking-atrocities-satellites-sudan-darfur-nathaniel-raymond-click-here
InfoSec tools | InfoSec services | InfoSec books
Jun 27 2023
Jun 27 2023
Jun 27 2023
Jun 27 2023
By Chris Hall
This article gives some guidance on how to transition to ISO27001:2022 from the 2013 version.

This approach is tried and tested in that I have used it to successfully transition an organization to the new version. In the transition audit there were no nonconformities.
#iso27001 #iso27001transition
How to transition to the 2022 version of ISO27001

Jun 26 2023
Jun 24 2023
Web Application Security: A 2023 Guide | Cyber Press
Written by: Cyber Writes

Web App Security
InfoSec tools | InfoSec services | InfoSec books
Jun 24 2023
Exploitation, Detection, and Mitigation Strategies
The Complete Active Directory Security Handbook – by Picus Security
Download pdf
InfoSec tools | InfoSec services | InfoSec books
Jun 23 2023

Salt Security has released key findings from its ‘State of the CISO’ report. Conducted by Global Surveyz for Salt, the global CISO survey gathered feedback from 300 CISOs/CSOs around the world on issues resulting from digital transformation and enterprise digitalization.
The results highlight significant CISO challenges including the biggest security control gaps they must manage, the most significant personal struggles they face, and the impact that broader global issues are having on their ability to deliver effective cyber security strategies.
Today’s digital-first economy has transformed the role of the modern CISO, increasing threats and changing security priorities.
Key findings include:
The 2023 report shows that the digital-first economy has brought new security challenges for CISOs. Interestingly, most of the challenges cited by CISOs represent nearly equal levels of concern, forcing CISOs to address multiple challenges at the same time.
CISOs cite the following top security challenges:
Also notable, while most CISOs (44 percent) report security budgets are about 25 percent higher than two years ago, nearly 30 percent identify lack of budget to address new security challenges from digital transformation as a key challenge, and 34 percent of CISOs cite difficulty justifying the cost of security investments as a challenge.
Two thirds of CISOs state that they have more new digital services to secure compared to 2021. In addition, 89 percent of CISOs state that the rapid introduction of digital services creates unforeseen security risks in protecting their companies’ vital data. API adoption and supply chain/third party vendors presented the two highest security control gaps in organizations’ digital initiatives.
CISOs rank security control gaps resulting from digital initiatives as follows:
The vast majority of CISOs admit to feeling the impact of a number of global trends. More CISOs cited the speed of AI adoption as having significant impact, followed by macro-economic uncertainty, the geo/political climate, and layoffs. Specific CISO responses regarding the impact of global trends were:
The digital-first economy has also impacted CISOs on a personal level. Among the personal challenges reported were:
Nearly 50 percent of CISOs cite litigation concerns. With several high-profile CISO lawsuits making waves recently, CISOs are fearful of being found personally liable in the event of a breach, putting their livelihood at risk.
On a positive note, 96 percent of CISOs worldwide report that their boards of directors are knowledgeable or very knowledgeable about cyber security issues. In addition, the survey showed that 26 percent of CISOs present to the board on cyber risks mitigation and business exposure once a quarter or more, and 57 percent present to the board at least once every six months.
InfoSec tools | InfoSec services | InfoSec books
Jun 23 2023
Altdns is a DNS recon tool that allows for the discovery of subdomains that conform to patterns. Altdns takes in words that could be present in subdomains under a domain (such as test, dev, staging) and takes in a list of subdomains you know of.
From these two lists provided as input to Altdns, the tool then generates a massive output of “altered” or “mutated” potential subdomains that could be present. It saves this output so that it can then be used by your favorite DNS brute-forcing tool.

The OWASP Amass project performs network mapping of attack surfaces and external asset discovery using open-source information gathering and active reconnaissance techniques.
The high adoption rate of Amass potentially means better data consistency and integration with other tools. As such, it can constitute a trustworthy tool to use in proof of concepts and engagements, and it may be easier to convince your clients or manager to use it for periodic mapping of the organization’s attack surface.

Aquatone is a tool for the visual inspection of websites across a large number of hosts and is convenient for quickly gaining an overview of HTTP-based attack surface. Aquatone is started by piping the output of a command into the tool. It doesn’t really care how the piped data looks, as URLs, domains, and IP addresses will be extracted with regular expression pattern matching. This means you can give it the output of any tool you use for host discovery.

Assetfinder lets you find domains and subdomains potentially related to a given domain. Implemented:

Gobuster is a tool used to brute-force:

Gotator is a tool to generate DNS wordlists through permutations.

HTTPX is a fully featured HTTP client library for Python 3. It includes an integrated command line client, has support for both HTTP/1.1 and HTTP/2, and provides both sync and async APIs.

Naabu is a port scanning tool written in Go that allows you to enumerate valid ports for hosts in a fast and reliable manner. It is a really simple tool that does fast SYN/CONNECT/UDP scans on the host/list of hosts and lists all ports that return a reply.

MASSCAN is an Internet-scale port scanner. It can scan the entire Internet in under 5 minutes, transmitting 10 million packets per second, from a single machine. Its usage (parameters, output) is similar to Nmap, the most famous port scanner.

WhatWeb identifies websites. Its goal is to answer the question, “What is that Website?”. WhatWeb recognises web technologies including content management systems (CMS), blogging platforms, statistic/analytics packages, JavaScript libraries, web servers, and embedded devices. WhatWeb has over 1800 plugins, each to recognise something different. WhatWeb also identifies version numbers, email addresses, account IDs, web framework modules, SQL errors, and more.
Open Source Intelligence Methods and Tools: A Practical Guide to Online Intelligence
InfoSec tools | InfoSec services | InfoSec books