Introducing to Cybersecurity | Cyber Writes ✍
Introduction to Cyber Security: Basic to Advance Techniques
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
InfoSec and Compliance – With 20 years of blogging experience, DISC InfoSec blog is dedicated to providing trusted insights and practical solutions for professionals and organizations navigating the evolving cybersecurity landscape. From cutting-edge threats to compliance strategies, this blog is your reliable resource for staying informed and secure. Dive into the content, connect with the community, and elevate your InfoSec expertise!
Dec 03 2023
Introducing to Cybersecurity | Cyber Writes ✍
Introduction to Cyber Security: Basic to Advance Techniques
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Dec 02 2023
I still love software as much today as I did when Paul Allen and I started Microsoft. But—even though it has improved a lot in the decades since then—in many ways, software is still pretty dumb.
To do any task on a computer, you have to tell your device which app to use. You can use Microsoft Word and Google Docs to draft a business proposal, but they can’t help you send an email, share a selfie, analyze data, schedule a party, or buy movie tickets. And even the best sites have an incomplete understanding of your work, personal life, interests, and relationships and a limited ability to use this information to do things for you. That’s the kind of thing that is only possible today with another human being, like a close friend or personal assistant.
In the next five years, this will change completely. You won’t have to use different apps for different tasks. You’ll simply tell your device, in everyday language, what you want to do. And depending on how much information you choose to share with it, the software will be able to respond personally because it will have a rich understanding of your life. In the near future, anyone who’s online will be able to have a personal assistant powered by artificial intelligence that’s far beyond today’s technology.
This type of software—something that responds to natural language and can accomplish many different tasks based on its knowledge of the user—is called an agent. I’ve been thinking about agents for nearly 30 years and wrote about them in my 1995 book The Road Ahead, but they’ve only recently become practical because of advances in AI.
Agents are not only going to change how everyone interacts with computers. They’re also going to upend the software industry, bringing about the biggest revolution in computing since we went from typing commands to tapping on icons.
Some critics have pointed out that software companies have offered this kind of thing before, and users didn’t exactly embrace them. (People still joke about Clippy, the digital assistant that we included in Microsoft Office and later dropped.) Why will people use agents?
The answer is that they’ll be dramatically better. You’ll be able to have nuanced conversations with them. They will be much more personalized, and they won’t be limited to relatively simple tasks like writing a letter. Clippy has as much in common with agents as a rotary phone has with a mobile device.
An agent will be able to help you with all your activities if you want it to. With permission to follow your online interactions and real-world locations, it will develop a powerful understanding of the people, places, and activities you engage in. It will get your personal and work relationships, hobbies, preferences, and schedule. You’ll choose how and when it steps in to help with something or ask you to make a decision.
“Clippy was a bot, not an agent.”
To see the dramatic change that agents will bring, let’s compare them to the AI tools available today. Most of these are bots. They’re limited to one app and generally only step in when you write a particular word or ask for help. Because they don’t remember how you use them from one time to the next, they don’t get better or learn any of your preferences. Clippy was a bot, not an agent.
Agents are smarter. They’re proactive—capable of making suggestions before you ask for them. They accomplish tasks across applications. They improve over time because they remember your activities and recognize intent and patterns in your behavior. Based on this information, they offer to provide what they think you need, although you will always make the final decisions.
Imagine that you want to plan a trip. A travel bot will identify hotels that fit your budget. An agent will know what time of year you’ll be traveling and, based on its knowledge about whether you always try a new destination or like to return to the same place repeatedly, it will be able to suggest locations. When asked, it will recommend things to do based on your interests and propensity for adventure, and it will book reservations at the types of restaurants you would enjoy. If you want this kind of deeply personalized planning today, you need to pay a travel agent and spend time telling them what you want.
The most exciting impact of AI agents is the way they will democratize services that today are too expensive for most people. They’ll have an especially big influence in four areas: health care, education, productivity, and entertainment and shopping.
Today, AI’s main role in healthcare is to help with administrative tasks. Abridge, Nuance DAX, and Nabla Copilot, for example, can capture audio during an appointment and then write up notes for the doctor to review.
The real shift will come when agents can help patients do basic triage, get advice about how to deal with health problems, and decide whether they need to seek treatment. These agents will also help healthcare workers make decisions and be more productive. (Already, apps like Glass Health can analyze a patient summary and suggest diagnoses for the doctor to consider.) Helping patients and healthcare workers will be especially beneficial for people in poor countries, where many never get to see a doctor at all.
These clinician-agents will be slower than others to roll out because getting things right is a matter of life and death. People will need to see evidence that health agents are beneficial overall, even though they won’t be perfect and will make mistakes. Of course, humans make mistakes too, and having no access to medical care is also a problem.
“Half of all U.S. military veterans who need mental health care don’t get it.”
Mental health care is another example of a service that agents will make available to virtually everyone. Today, weekly therapy sessions seem like a luxury. But there is a lot of unmet need, and many people who could benefit from therapy don’t have access to it. For example, RAND found that half of all U.S. military veterans who need mental health care don’t get it.
AI agents that are well trained in mental health will make therapy much more affordable and easier to get. Wysa and Youper are two of the early chatbots here. But agents will go much deeper. If you choose to share enough information with a mental health agent, it will understand your life history and your relationships. It’ll be available when you need it, and it will never get impatient. It could even, with your permission, monitor your physical responses to therapy through your smart watch—like if your heart starts to race when you’re talking about a problem with your boss—and suggest when you should see a human therapist.
AI is about to completely change how you use computers
AI Made Simple: A Beginner’s Guide to Generative Intelligence
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Dec 01 2023
The widespread adoption of SaaS applications, remote work, and shadow IT compels organizations to adopt cloud-based cybersecurity. This is essential as corporate resources, traffic, and threats are no longer restricted to the office premises.
Cloud-based security initiatives, such as Secure Access Service Edge (SASE) and Security Service Edge (SSE), comprising Secure Web Gateway (SWG), Cloud Access Security Brokers (CASB), Data Loss Prevention (DLP), and Zero Trust Network Access (ZTNA), effectively push security to wherever the corporate users, devices, and resources are – all via the cloud. With all security functions now delivered over the cloud and managed through a single pane of glass, the incoming and outgoing traffic (aka, the north-south traffic) is all but secure.
However, the east-west traffic — i.e., traffic that traverses the internal network and data centers and does not cross the network perimeter — is never exposed to these cloud-based security checks.
One way around it is to maintain a legacy data center firewall that monitors and controls the east-west traffic specifically. For starters, this hybrid security architecture adds up the cost and complexity of managing disparate security solutions, something organizations desperately attempt to overcome with cloud-based converged security stacks.
Secondly, the absence of unified visibility across cloud and on-premise security components can result in a loss of shared context, which renders security loopholes inevitable. Even Security Information and Event Management (SIEM) or Extended Detection and Response (XDR) solutions can’t address the complexity and operational overhead of maintaining a hybrid security stack for different kinds of traffic. As such, organizations still need that single, integrated security stack that offers ubiquitous protection for incoming, outgoing, and internal traffic, managed via a unified dashboard.
Organizations need a security solution that offers both north-south and east-west protection, but it must all be orchestrated from a unified, cloud-based console. There are two ways to achieve this:
Cloud-native security architectures like SASE and SSE can offer the east-west protection typically delivered by a data center firewall by rerouting all internal traffic through the closest point of presence (PoP). Unlike a local firewall that comes with its own configuration and management constraints, firewall policies configured in the SSE PoP can be managed via the platform’s centralized management console. Within the unified console, admins can create access policies based on ZTNA principles. For instance, they can allow only authorized users connected to the corporate VLAN and running an authorized, Active Directory-registered device to access sensitive resources hosted within the on-premise data center.
In some cases, however, organizations may need to implement east-west traffic protection locally without redirecting the traffic to the PoP.
Consider a situation where a CCTV camera connected to an IoT VLAN needs to access an internal CCTV server.
Given the susceptibility of the IoT camera to be compromised by a malicious threat actor and controlled over the internet via a remote C2 server, the camera’s internet or WAN access should be disabled by default. If the data center firewall policy is implemented in the PoP, the traffic from internet-disabled IoT devices will naturally be exempt from such policies. To bridge this gap, SASE and SSE platforms can allow admins to configure firewall policies at the local SD-WAN device.
Typically, organizations connect to the SASE or SSE PoPs through an SD-WAN device, also known as a socket, installed at the site. The centralized dashboard can allow admins to configure rules for allowing or blocking internal or LAN traffic directly at the SD-WAN device, without ever sending it to the PoP over WAN.
In this scenario, if the traffic matches the pre-configured LAN firewall policies, the rules can be enforced locally. For instance, admins can allow corporate VLAN users to access printers connected to the printer VLAN while denying such access to guest Wi-Fi users. If the traffic does not match pre-defined policies, the traffic can be forwarded to the PoP for further classification.
As security functions move increasingly to the cloud, it’s crucial not to lose sight of the controls and security measures needed on-site.
Cloud-native protections aim to increase coverage while reducing complexities and boosting convergence. As critical as it is to enable east-west traffic protection within SASE and SSE architectures, it’s equally important to maintain the unified visibility, control, and management offered by such platforms. To achieve this, organizations must avoid getting carried away by emerging threats and adding back disparate security solutions.
As such, any on-premise security measures added within cloud-based security paradigms should maintain a unified dashboard for granular policy configuration and end-to-end visibility across LAN and WAN traffic. This is the only way organizations can reliably bridge the gap between cloud and on-premise security and enable a sustainable, adaptable, and future-proof security stack.
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 29 2023
Google has fixed the sixth Chrome zero-day bug that was exploited in the wild this year. The flaw, identified as CVE-2023-6345, is classified as an integer overflow in Skia, an open-source 2D graphics library written in C++.
“Google is aware that an exploit for CVE-2023-6345 exists in the wild,” Google said.
There are several potential risks associated with this high-severity zero-day vulnerability, including the execution of arbitrary code and crashes.
On November 24, 2023, Benoît Sevens and Clément Lecigne from Google’s Threat Analysis Group reported the issue.
Google has upgraded the Stable channel version 119.0.6045.199 for Mac and Linux and 119.0.6045.199/.200 for Windows, addressing the year’s sixth actively exploited zero-day vulnerability. This upgrade will be rolled out over the next few days/weeks.
Additionally, Google has fixed six high-severity security vulnerabilities with this update.
Type Confusion in Spellcheck is a high-severity bug that is being tracked as CVE-2023-6348. Mark Brand from Google Project Zero reported the issue.
Use after free in Mojo is the next high-severity bug, tagged as CVE-2023-6347. 360 Vulnerability Research Institute’s Leecraso and Guang Gong reported the issue, and they were rewarded with a bounty of $31,000.
Use after free in WebAudio is a high-severity issue identified as CVE-2023-6346. Following Huang Xilin of Ant Group Light-Year Security Lab’s disclosure, a $10,000 prize was given out.
A High severity bug in libavif, Out-of-bounds memory access, is tagged as CVE-2023-6350. Fudan University reported it, and $7000 was given out.
Use after free in libavif is a high-severity bug identified as CVE-2023-6351. Fudan University reported it, and $7000 was given out.
To stop exploitation, Google highly advises users to update their Chrome web browser right away. The following are the easy procedures that you must follow to update the Chrome web browser:-
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 28 2023
In the realm of cybersecurity, where a constant influx of new “essential” products occurs, it’s tempting to be influenced into investing in unnecessary tools that not only expand your vulnerability but also provide minimal, if any, value. Let’s delve into the intricacies of security expenditure and the advantages of optimization, especially in times of economic uncertainty as we plan for the 2024 budget.
This is an industry that uses fear, uncertainty, and doubt (FUD) as a selling tactic, making security leaders feel like every product is make-or-break for the wellbeing of their organization. The promise of a fix-it-all solution (the mythical silver bullet) is particularly tempting in this environment, especially for smaller organizations that most likely don’t have the budgets to implement a multitude of security tools or hire cyber specialists in-house. Vendors play on that desperation to make profits, and a lot of them are very good at it.
The fear mongering may also lead to impulsive decisions to invest in products that won’t configure correctly with the buyer’s current technology stack, thus introducing even more risk. The name of the game in a lean operation is a solution that is customizable and adaptable, and that will grow with the changing needs of an organization’s security team.
According to IBM’s 2023 Cost of a Data Breach Report, organizations are now paying $4.5 million to deal with breaches – a 15% increase over the last three years. Aside from spending cash to purchase the product, panic buying can result in a wider attack surface, costly auto-renews and misconfigurations.
There is no doubt that taking advantage of new technological solutions (with AI and machine learning being fan favorites right now), can be extremely beneficial from both a technological and reputational perspective. But without looking at the big picture and calculating the actual value of the product in question, it’s nearly impossible to make a well-informed investment decision.
To assess the value of a product, security leaders should examine whether it adds or minimizes organizational risk and whether their current cybersecurity personnel and tools will be able to interact with it effectively.
Calculating the value of a product doesn’t have to be a guessing game. Risk = likelihood x impact is a great equation to use to solve for the value of a product or service.
To calculate likelihood of an attack, examine the degree of difficulty to execute an attack and the exposure of your assets. Determine your organization’s acceptable risk and use that equation to work backwards to identify the monetary impact of an attack. If that impact is significantly higher than the price of the product or service, it may be worth looking elsewhere.
It’s easy to fall into the trap of impulse buying cybersecurity products that don’t improve security but instead leave you vulnerable to costly attacks. Organizations should aim to protect their most valuable assets and prioritize addressing threats to those critical puzzle pieces of their business.
Look inward and optimize. Companies need to understand what inside their networks and data is most attractive and most vulnerable to attackers. Get visibility into what you have, calculate the value of your tools, and use the information to move forward.
Understanding risk by gaining full visibility into what you already have can allow companies to communicate better with investors and the public in the case of an attack or breach. For example, they will be able to give clear information about the impact (or lack of impact) on the business when an attack occurs and lay out clear steps for remediation, not having to guess the next best course of action.
It is important to remember that the goal is not to buy more tools to chase the growing number of vulnerabilities that experts find every day, but to protect the assets that are most relevant to overall vital business operations and limit the fallout of inevitable cyber incidents.
By attaching a dollar value to the cyber risks the organization is up against, you will be in a much better position to discuss your security plan and budgetary needs.
When budgets are tight, every purchase must be accounted for with a clear indication of its value to the business operation. This is especially true for security purchases, which tend to be costly line items.
In today’s economic climate, proving ROI for security spend is a big part of security leaders’ jobs. It is crucial that before purchasing a new cybersecurity tool, investing in a service, or hiring specialists, you understand their functionality and purpose.

InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 25 2023
Nov 25 2023
CISSP Study Guide | Cyber Press
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 21 2023
https://www.scmagazine.com/brief/increasingly-prevalent-netsupport-rat-infections-reported
Attacks involving the NetSupport RAT have become increasingly common, The Hacker News reports. More than 15 infections have been observed mostly in organizations in the education, government, and business sectors, in recent weeks, according to a report from VMware Carbon Black researchers. Fraudulent browser updates have been leveraged by threat actors to facilitate the distribution of the SocGholish downloader malware, also known as FakeUpdates, which then uses PowerShell to establish a remote server connection and facilitate the retrieval of a NetSupport RAT-containing ZIP archive file. Researchers also noted that the installation of NetSupport would then enable behavior tracking, file transfers, computer setting alterations, and lateral network movement. “The delivery mechanisms for the NetSupport RAT encompass fraudulent updates, drive-by downloads, utilization of malware loaders (such as GHOSTPULSE), and various forms of phishing campaigns,” said researchers. NetSupport RAT, which was once a remote access tool, was previously reported by Sucuri to have been spread through fake Cloudflare distributed denial-of-service protection pages.
Rat : Remote Access Trojan – Launching Virus Remotely
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 20 2023
https://time.com/6333716/china-icbc-bank-hack-usb-stick-trading/
On Thursday, trades handled by the world’s largest bank in the globe’s biggest market traversed Manhattan on a USB stick.
Industrial & Commercial Bank of China Ltd.’s U.S. unit had been hit by a cyberattack, rendering it unable to clear swathes of U.S. Treasury trades after entities responsible for settling the transactions swiftly disconnected from the stricken systems. That forced ICBC to send the required settlement details to those parties by a messenger carrying a thumb drive as the state-owned lender raced to limit the damage.
The workaround — described by market participants — followed the attack by suspected perpetrator Lockbit, a prolific criminal gang with ties to Russia that has also been linked to hits on Boeing Co., ION Trading U.K. and the U.K.’s Royal Mail. The strike caused immediate disruption as market-makers, brokerages and banks were forced to reroute trades, with many uncertain when access would resume.
The incident spotlights a danger that bank leaders concede keeps them up at night — the prospect of a cyber attack that could someday cripple a key piece of the financial system’s wiring, setting off a cascade of disruptions. Even brief episodes prompt bank leaders and their government overseers to call for more vigilance.
“This is a true shock to large banks around the world,” said Marcus Murray, the founder of Swedish cybersecurity firm Truesec. “The ICBC hack will make large banks around the globe race to improve their defenses, starting today.”
As details of the attack emerged, employees at the bank’s Beijing headquarters held urgent meetings with the lender’s U.S. division and notified regulators as they discussed next steps and assessed the impact, according to a person familiar with the matter. ICBC is considering seeking help from China’s Ministry of State Security in light of the risks of potential attack on other units, the person said.
Late Thursday, the bank confirmed it had experienced a ransomware attack a day earlier that disrupted some systems at its ICBC Financial Services unit. The company said it isolated the affected systems and that those at the bank’s head office and other overseas units weren’t impacted, nor was ICBC’s New York branch.
The extent of the disruption wasn’t immediately clear, though Treasury market participants reported liquidity was affected. The Securities Industry and Financial Markets Association, or Sifma, held calls with members about the matter Thursday.
ICBC FS offers fixed-income clearing, Treasuries repo lending and some equities securities lending. The unit had $23.5 billion of assets at the end of 2022, according to its most recent annual filing with U.S. regulators.
The attack is only the latest to snarl parts of the global financial system. Eight months ago, ION Trading U.K. — a little-known company that serves derivatives traders worldwide — was hit by a ransomware attack that paralyzed markets and forced trading shops that clear hundreds of billions of dollars of transactions a day to process deals manually. That has put financial institutions on high alert.
ICBC, the world’s largest lender by assets, has been improving its cybersecurity in recent months, highlighting increased challenges from potential attacks amid the expansion of online transactions, adoption of new technologies and open banking.
“The bank actively responded to new challenges of financial cybersecurity, adhered to the bottom line for production safety and deepened the intelligent transformation of operation and maintenance,” ICBC said in its interim report in September.
Ransomware attacks against Chinese firms appear rare in part because China has banned crypto-related transactions, according to Mattias Wåhlén, a threat intelligence specialist at Truesec. That makes it harder for victims to pay ransom, which is often demanded in cryptocurrency because that form of payment provides more anonymity.
But the latest attack likely exposes weaknesses in ICBC’s defenses, Wåhlén said.
“It appears ICBC has had a less effective security,” he said, “possibly because Chinese banks have not been tested as much as their Western counterparts in the past.”
Ransomware hackers have become so prolific that attacks may hit record levels this year.
Blockchain analytics firm Chainalysis had recorded roughly $500 million of ransomware payments through the end of September, an increase of almost 50% from the same period a year earlier. Ransomware attacks surged 95% in the first three quarters of this year, compared with the same period in 2022, according to Corvus Insurance.
In 2020, the website of the New Zealand Stock Exchange was hit by a cyberattack that throttled traffic so severely that it couldn’t post critical market announcements, forcing the entire operation to shut down. It was later revealed that more than 100 banks, exchanges, insurers and other financial firms worldwide were targets of the same type of so-called DDoS attacks simultaneously.
Caesars Entertainment Inc., MGM Resorts International and Clorox Co. are among companies that have been hit by ransomware hackers in recent months.
ICBC was struck as the Securities and Exchange Commission works to reduce risks in the financial system with a raft of proposals that include mandating central clearing of all U.S. Treasuries. Central clearing platforms are intermediaries between buyers and sellers that assume responsibility for completing transactions and therefore prevent a default of one counterparty from causing widespread problems in the marketplace.
The incident underscores the benefits of central clearing in the $26 trillion market, said Stanford University finance professor Darrell Duffie.
“I view it as one example of why central clearing in the U.S. Treasuries market is a very good idea,” he said, “because had a similar problem occurred in a not-clearing firm, it’s not clear how the default risk that might result would propagate through the market.”

The Hacker and the State: Cyber Attacks and the New Normal of Geopolitics
In the Lair of the Cozy Bear: Cyberwarfare with APT 29 Up Close and Personal
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 20 2023
The Ukrainian National Security and Defense Council (NDSC) reported that APT29 (aka SVR group, Cozy Bear, Nobelium, Midnight Blizzard, and The Dukes) has been exploiting the CVE-2023-38831 vulnerability in WinRAR in recent attacks.
APT29 along with APT28 cyber espionage group was involved in the Democratic National Committee hack and the wave of attacks aimed at the 2016 US Presidential Elections.
The Russia-linked APT group was observed using a specially crafted ZIP archive that runs a script in the background to show a PDF lure while downloading PowerShell code to fetch and execute a payload.
The APT group targeted multiple European nations, including Azerbaijan, Greece, Romania, and Italy, with the primary goal of infiltrating embassy entities.
The threat actors used a lure document (“DIPLOMATIC-CAR-FOR-SALE-BMW.pdf”) containing images of a BMW car available for sale to diplomatic entities. The weaponized documents embedded malicious content that exploited the WinRAR vulnerability.

“In the context of this particular attack, a script is executed, generating a PDF file featuring the lure theme of a BMW car for sale. Simultaneously, in the background, a PowerShell script is downloaded and executed from the next-stage payload server.” reads the report published by NDSC. “Notably, the attackers introduced a novel technique for communicating with the malicious server, employing a Ngrok free static domain to access their server hosted on their Ngrok instance.”
In this attack scheme, Ngrok has been used to host their next-stage PowerShell payloads and establish covert communication channels.
Threat actors use the tool to obfuscate their communications with compromised systems and evade detection.
“What makes this campaign particularly noteworthy is the synthesis of old and new techniques. APT29 continues to employ the BMW car for sale lure theme, a tactic that’s been seen in the past. However, the deployment of the CVE-2023-38831 WinRAR vulnerability, a novel approach, reveals their adaptability to the evolving threat landscape. Additionally, their use of Ngrok services to establish covert communications emphasizes their determination to remain concealed.” concludes the NDSC that also published indicators of compromise (IoCs) for these attacks.
In April, Google observed Russia-linked FROZENBARENTS APT (aka SANDWORM) impersonates Ukrainian drone training school to deliver the Rhadamanthys infostealer.
The threat actors used a lure themed as an invitation to join the school, the email included a link to an anonymous file-sharing service, fex[.]net. The file-sharing service was used to deliver a benign decoy PDF document with a drone operator training curriculum and specially crafted ZIP archive (“Навчальна-програма-Оператори.zip” (Training program operators)) that exploits the flaw CVE-2023-38831.
In September, CERT-UA observed the FROZENLAKE group exploitingthe WinRAR flaw to deploy malware in attacks aimed at energy infrastructure.
Google TAG experts also observed the Russia-linked ATP28 group exploiting the flaw in attacks against Ukraine users. The state-sponsored hackers employed a malicious PowerShell script (IRONJAW) to steal browser login data and local state directories.
The China-linked APT40 group was observed exploiting the CVE-2023-38831 vulnerability in attacks against targets in Papua New Guinea.
Last week, researchers at cybersecurity firm NSFOCUS analyzed DarkCasino attack pattern exploiting the WinRAR zero-day vulnerability tracked as CVE-2023-38831. The economically motivated APT group used specially crafted archives in phishing attacks against forum users through online trading forum posts.
In the Lair of the Cozy Bear: Cyberwarfare with APT 29 Up Close and Personal
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 18 2023
Written and directed by Kilian Lieb and Max Rainer, Cyberbunker is a Netflix documentary about a group of hackers that enabled the proliferation of dark web forums where illegal materials were bought and sold.
The documentary begins with a special police unit performing a raid in what looks like a military bunker. We are then shown a thin individual with glasses and long, gray hair: Herman Johan Xennt.
The (now) 64-year-old Dutchman, who is currently serving a prison sentence in Germany, is a bunker aficionado, having been fascinated with them since he visited a WWII bunker in Arnhem when he was a kid.
Understanding the possibilities of computer technology and the internet, he first opened a profitable computer store in the early 90s. In 1995, with the money earned from this business, he was able to buy a former NATO bunker in the southern part of the Netherlands, which ended up being the location of the first Cyberbunker – a company that provides internet and web hosting services to questionable operations.
In 2002, a fire broke in the bunker and revealed the existence of an MDMA lab. Xennt claimes that he knew nothing about the lab and that he was simply subletting part of the bunker to another group. For many years after, the company’s servers were located above ground, in Amsterdam. In 2013, Xennt found and purchased a 5-level underground Cold War-era bunker in Traben-Trarbach, a small town in the South of Germany.
But the town’s mayor soon grew suspicious of the activities going on in the bunker and decided to contact the authorities, which started telephone surveillance in 2015. The group communicated in codes, though, which made crime identification impossible. In 2017, the authories began monitoring the network node to identify illegal data traffic.
This led to the discovery of evidence of criminal activity: Cyberbunker provided hosting for dark web marketplaces, a forum for exchanging illegal drugs, counterfeit money and fake identification, and more.
The undercover operation provided crucial information to the police, helping them to plan and execute a successful raid. Xennt and his criminal colleagues were arrested, and over 280 servers hosting websites for up to 200 customers were shut down.
Cyberbunker was know among cybercriminals as a “bulletproof hoster”, which meant that the servers hosting the content stayed online no matter what (i.e., even if the authorities requested sites’ removal). It also guaranteed privacy, which was very convenient for anyone who wanted to host questionable or illegal content.
Cyberbunker advertised that it would host everything except child pornography and terrorism-related content, but the group later claimed that they didn’t really know what the clients were using their servers for.
The group was driven by the idea of “freedom of the internet” and, during the interviews with all the members of the group (including Xennt), we can see that they have a twisted idea of what it should be.
They went so far as to declare the Republic of Cyberbunker, with its “administration” and hierarchy, and perpetuated the delusion that what they were doing was good.
The documentary is suitable for a wide audience and does not burden the spectator with technical details. Instead, it has a movie-like format that’s captivating and easy to follow.
The timeline of the events is well presented and clear, complemented with historical data about the main “character” – Xennt – and original private and police footage.
The authors tried to create a tense and scary atmosphere, though the characters at times act bizarrely and seem out of touch with reality that, on occasion, you might almost feel sorry for them. It’s hard to believe these individuals thought they were untouchable and that, even after getting arrested, they were still convinced they were making the world a better place.

Codes of the Underworld: How Criminals Communicate
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 17 2023
The skills employed, the hacktivists and other threat actors are not going anywhere. Right now, Russia might be overwhelmingly interested in Ukraine, but their aims and goals remain global.
“These skills will be turned in other directions and other targets in the future, they will be shared in threat actor groups online. This is the world you need to be preparing for right now,” he added.
His warning echoed a similar one by Viktor Zhora, Deputy Chairman and Chief Digital Transformation Officer at the State Service of Special Communication and Information Protection of Ukraine.
Russia’s attack force consists of “hackers in uniform”, cybercriminals and hacktivists congregating in various Telegram channels, but the nation is also working on engaging ever more younger people in their cyber offensive campaigns. They are seeking talented individuals in schools (and not just tech universities), selecting the most talented and training them, he shared.
“The Russians are in it for the long run,” Zhora warned during his IRISSCON talk, and called on countries that are – or expect to be – targeted by cyber aggressive nations to create a cyber coalition so they can prepare, share their experiences, and exchange information.
We can’t talk about the war in Ukraine and not mention cyber attacks aimed at disrupting operational technology (OT) used by companies that are part of the country’s critical infrastructure (CI).
In his talk, Ferguson briefly passed through the known attacks that hit CI entities with OT-specific malware, starting with Stuxnet in 2010 and ending with CosmicEnergy in 2023.
Some of the attacks are believed to be the work of the US and Israel (Stuxnet), cybercriminals (EKANS ransomware, 2020) or are still unattributed (the destructive 2014 attack against a steel plant in Germany). But the rest, he noted, are all believed to have been mounted by Russian state-backed attackers.
And, he says, they are getting better at it. Mirroring the development of attacks against IT systems, they have recently begun exploiting legitimate tools found in OT environments, so they don’t need to develop customized malware.
Many attackers are scanning for OT-specific protocols and probing OT devices, Ferguson noted. While their actual exploitation hinges on the skills of the attackers, some modes of attack (e.g., DDoS and phishing) are available to those who are less skilled, but eager. Hacktivists can target critical infrastructure that’s exposed on the internet as it’s easily discoverable via online tools.
Unfortunately, securing OT systems comes with a host of challenges: a complex infrastructure; an increasing number of endpoints; OT devices insecure by design (and generally not meant to be connected to the internet); rarely integrated OT and IT security teams, a lack of visibility into the OT infrastructure – to name just a few.
Since the start of the war, Russian hackers have been trying to shut down electrical power in the country, have gone after government agencies, IT companies, telecoms, software development firms, media houses, editors, and media personalities, Zhora noted.
While the initial attacks were mostly geared towards destruction, Russian cyber attackers are now also trying to get their hands on information that can help them determine the effectiveness of their kinetic attacks, discover whether their spies have been flagged by the Ukrainian authorities, and see what evidence those authorities have gathered about war crimes.
Clever and subtle psy-ops online campaigns are, as well, a favorite tactic employed by the Russian state to manipulate enemies. And, since the advent of generative AI, it has became easier to mount them, Ferguson added.
All these things should be taken in consideration by governments when preparing for the future. Looking at the cyber component of the unfolding wars in Ukraine and Israel, they can see what future conflicts will look like.
Zhora says that Ukraine is becoming more and more confident of its capacity to counter future attacks, but that each democracy needs to ask themselves: Are we prepared for a global cyber war? “And they need to be honest with the answer,” he noted.
If they are not, they should immediately begin investing in cyber defense and intensifying cooperation, he added.

InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 16 2023
In a startling revelation, Bitdefender, a leading cybersecurity firm, has disclosed a series of sophisticated attack methods that could significantly impact users of Google Workspace and Google Credential Provider for Windows (GCPW). This discovery highlights potential weaknesses in widely used cloud and authentication services, prompting a reevaluation of current security measures.
Bitdefender’s research team, working in conjunction with their in-house research institute Bitdefender Labs, has identified previously unknown methods that cybercriminals could use to escalate a breach from a single endpoint to a network-wide level. These techniques, if exploited, could lead to severe consequences such as ransomware attacks or massive data exfiltration.
The attack progression involves several key stages, starting from a single compromised machine. Once inside the system, attackers could potentially:
These findings were responsibly disclosed to Google. However, Google has stated that these issues will not be addressed directly, as they fall outside their designated threat model. This decision reflects Google’s risk assessment and security priorities.
At the heart of these vulnerabilities is the Google Credential Provider for Windows (GCPW), a tool designed to streamline access and management within Google’s ecosystem. GCPW serves two primary functions:
Understanding GCPW’s functioning is crucial in comprehending the vulnerabilities. Here’s a breakdown of its operational process:
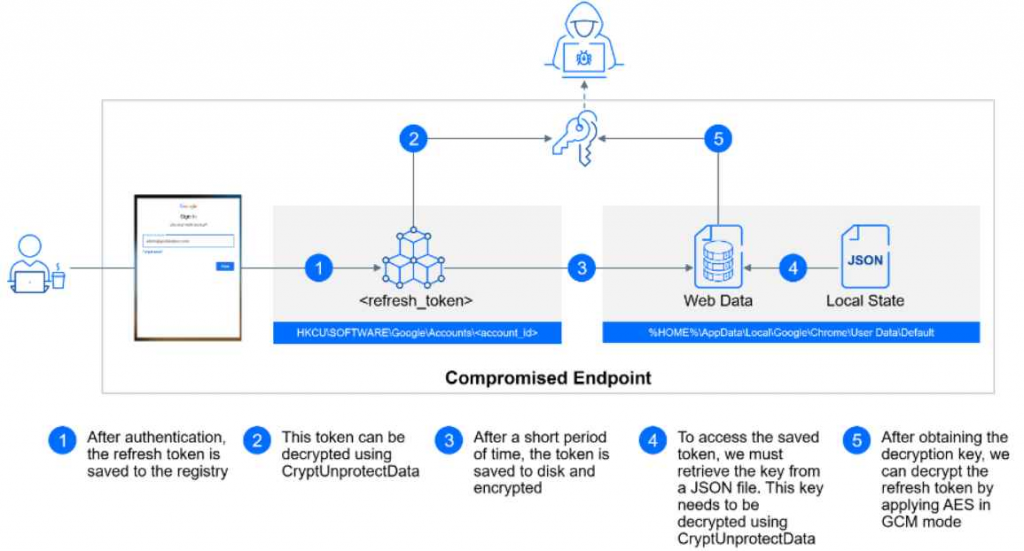
Attack Example:
Scenario: A small business, “Gamma Inc.,” uses GCPW for managing their Windows devices and Google Workspace accounts.
Attack Example:
Google’s decision not to address these findings, citing their exclusion from the company’s specific threat model, has stirred a debate in the cybersecurity community. While Google’s risk.
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 15 2023
SystemBC (aka Coroxy or DroxiDat) is a multifunctional malware known as Proxy, Bot, Backdoor, and RAT, adapting to attackers’ needs.
Since 2018, this multifunctional malware has been active, and it remains popular in underground markets, with consistent annual incidents.
Cybersecurity researcher, REXor (aka Aaron) recently discovered that several ransomware groups are employing SystemBC, a Swiss Knife proxy malware, for their illicit purposes.
Here below, we have mentioned all the ransomware groups that are involved in using this malware:-
Coroxy infiltrates systems using diverse methods tailored to the user group, employing:-
It’s also utilized in Spear Phishing campaigns, delivered via loaders or other malware for installation on victim systems.
SystemBC malware adapts its methods but maintains core tasks:-
Gather system info –> Establish persistence –> Create a Socks5 connection to the C&C server –> Transmit data –> Await attacker commands or malware launches
This backdoor enables attackers to operate from their infrastructure, and over time, numerous groups have used SystemBC.
SystemBC usage varies with each attacker’s access to the infrastructure. Studied samples show diverse executions yet share consistent core functions.
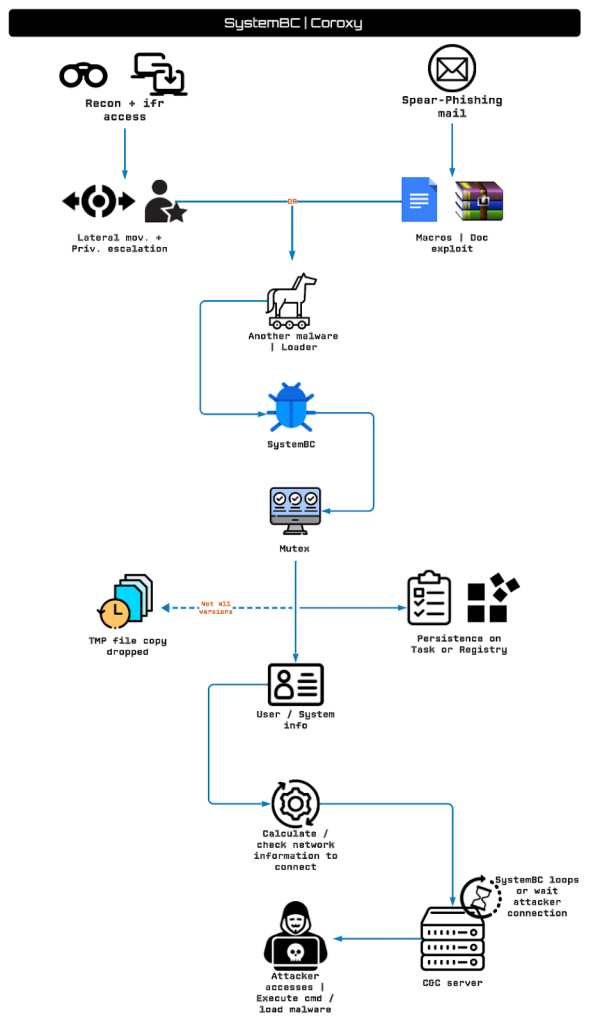
Usually, when an executable is run, a duplicate copy of SystemBC is made and persistence is established via tasks or registry entries.
Some samples may use a packer or need deobfuscation/extraction without a loader or malware.
Extracting from memory may be required, revealing identical copies in a temporary folder indicating malware duplication with dynamic filenames.
Coroxy employs a Mutex control in all examined samples that prevents multiple runs. It may generate a random string or deobfuscate a domain as a Mutex, adding complexity.
Samples establish persistence differently, as some create jobs or registry entries, often using PowerShell to execute SystemBC.
In certain versions, SystemBC launches a duplicate in the following paths:-
SystemBC detects a2guard, a handy anti-analysis move to spot antivirus or disruptive software. It captures process snapshots, using ProcessFirst and ProcessNext to hunt for the binary.
This grants persistence, process control, and info gathering, with deobfuscation and decryption for future network connections.
After pinpointing the connection location, SystemBC establishes it through a loop, usually targeting a known server and port, reads the report.
Though versions may differ slightly, the core behavior remains the same. However, the analyst found a focus on Coroxy’s relevance, with active discussions and inquiries in forums.
Besides this, the identified infrastructure allows OS access for around $350 to $300, payable through active cryptocurrency wallets.
Hash:
Domain:
IP (High confidence):
IP (Mid-Low confidence):
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 14 2023

https://therecord.media/cyber-espionage-campaign-embassies-apt29-cozy-bear
Russian state-sponsored hackers have targeted embassies and international organizations in a recent cyber-espionage campaign, Ukrainian government cybersecurity researchers have found.
The attacks were attributed to the infamous hacker group labeled APT29, also known as Cozy Bear or Blue Bravo. Analysts previously have linked it to Russia’s Foreign Intelligence Service (SVR), which gathers political and economic information from other countries.
The campaign, analyzed by Ukraine’s National Cyber Security Coordination Center (NCSCC), occurred in September of this year. The group used similar tools and tactics in its previous campaigns, particularly during an operation against embassies in Kyiv in April.
The most recent operation had “the primary goal of infiltrating embassy entities,” the NCSCC said, including targets in Azerbaijan, Greece, Romania and Italy. Another victim was the major Greek internet provider Otenet, the NCSCC said.
Diplomatic accounts, especially those associated with the foreign affairs ministries in Azerbaijan and Italy, suffered the most, according to researchers. One possible reason is that Russian intelligence was attempting to gather information regarding Azerbaijan’s strategic activities, especially leading up to the Azerbaijani invasion of the Nagorno-Karabakh region.
In total, APT29’s campaign targeted over 200 email addresses, but it’s not clear how many attacks were successful.
APT29 exploited a recently discovered vulnerability in the Windows file archiver tool WinRAR. Identified as CVE-2023-3883, the bug was utilized by state-controlled hackers connected to Russia and China in early 2023 before being patched. Unpatched versions of the tool remain vulnerable.
According to NCSCC, this vulnerability still “poses a significant threat” as it allows attackers to execute arbitrary code through the exploitation of a specially crafted ZIP archive.
In the recent campaign, Cozy Bear sent victims phishing emails containing a link to a PDF document and a malicious ZIP file that exploits the vulnerability, potentially granting attackers access to the compromised systems.
To convince their targets to open malicious files, the hackers created emails claiming to have information about the sale of diplomatic BMW cars. The same lure was used during the group’s attack on the embassies in Kyiv this spring.
In this campaign, the attackers introduced a novel technique for communicating with the malicious server, researchers said. In particular, they used a legitimate tool called Ngrok that allows users to expose their local servers to the internet.
Ngrok is commonly used during web development and testing to provide temporary public URLs for local web servers but cybercriminals deployed it to obfuscate their activities and communicate with compromised systems while evading detection.
By exploiting Ngrok’s capabilities in this way, threat actors can further complicate cybersecurity analysis and remain under the radar, making defense and attribution more challenging, NCSCC said.
During the war in Ukraine, APT29 has carried out cyberattacks against the Ukrainian military and its political parties, as well as diplomatic agencies, think tanks and nonprofit organizations.
In April, for example, the group launched a spying campaign targeting foreign ministries and diplomatic entities in NATO countries, the European Union and, “to a lesser extent,” Africa.
The hackers’ tactics were similar to those used in the September campaign. In particular, they sent phishing emails impersonating the embassies of European countries to specific personnel, usually including a malicious link either in the body of the message or an attached PDF inviting the target diplomat to access the ambassador’s calendar.
APT29 has been blamed for several high-profile incidents prior to the war, including the SolarWinds supply chain attack in 2020 that affected thousands of organizations globally and led to a series of data breaches.

InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 14 2023

Dark forums and Telegram channels have become great places for threat actors to sell critical vulnerabilities and exploits.
These vulnerabilities and exploits were associated with the Elevation of Privilege, Authentication Bypass, SQL Injection, and Remote Code Execution in products like Windows, JetBrains software, Microsoft Streaming Service Proxy, and Ubuntu kernels.
Recent discoveries state that these vulnerabilities were sold in underground forums even before the Vendor officially assigned them.
One such example was the Microsoft Streaming Server vulnerability (CVE-2023-36802) that was on sale in February, though the CVE was officially assigned in September 2023.
According to the reports shared with Cyber Security News, several critical and high-severity vulnerabilities were sold in the underground forums, which certain ransomware groups used to gain initial access and lateral movement inside the victim network.
This vulnerability was published in NVD on June 02, 2023. However, it was observed to be exploited by threat actors since May 2023. This vulnerability had a severity of 9.8 (Critical) and was patched by Progress.
This vulnerability arises due to insufficient sanitization of user-provided data, which enables unauthenticated remote attackers to access the MOVEit application. With this vulnerability, the Cl0p ransomware group targeted more than 3000 organizations in the US and 8000 organizations worldwide.

NVD published this vulnerability on June 19, 2023, and Citrix patched it in July 2023. However, threat actors were seen to be exploiting this vulnerability in June 2023, which affected Netscaler ADC and Gateway versions.
A threat actor can use this vulnerability to execute remote code on affected Citrix ADC and Gateway systems to steal sensitive information without any authentication. The severity of this vulnerability was given as 9.8 (Critical).
This vulnerability could allow an unauthenticated threat actor to access the TeamCity server and execute remote code,, which could compromise the source code and add to a supply chain attack.
This vulnerability was published in NVD in September 2023 and was found to be sold in the underground forums in October 2023. This authentication bypass leading to RCE vulnerability was given a severity of 9.8 (Critical).
According to Microsoft, this vulnerability was potentially used by North Korean nation-state threat actors like Diamond Sleet and Onyx Sleet to install malware and backdoors on their targets.
A complete report about the vulnerabilities sold on the underground market, their associated threat groups, and other information has been published.
Users of these products are recommended to patch the affected versions accordingly and take precautionary measures to prevent them from getting exploited by threat actors.
The Darkest Web: Drugs, Death and Destroyed Lives . . . the Inside Story of the Internet’s Evil Twin
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 13 2023
Living-off-the-land (LotL) techniques in cyber attacks refer to the use of legitimate, native tools already present in the target system to carry out malicious activities. This approach is particularly stealthy because it leverages tools and processes that are typically trusted and thus less likely to raise alarms. In the context of Operational Technology (OT) or Industrial Control Systems (ICS), such attacks can be especially dangerous due to the critical nature of the systems involved. Here’s how such an attack might work, with examples:
In late 2022, a significant cyber-physical incident occurred in Ukraine, attributed to the Russia-linked threat actor Sandworm. This event targeted Ukrainian critical infrastructure and utilized a multi-event cyber attack strategy, incorporating innovative techniques to impact industrial control systems (ICS) and operational technology (OT). The Sandworm actor employed OT-level living-off-the-land (LotL) techniques, likely causing a substation’s circuit breakers to trip and resulting in an unplanned power outage. This outage coincided with mass missile strikes across Ukraine’s critical infrastructure. Additionally, Sandworm executed a second disruptive event by deploying a new variant of CADDYWIPER malware in the victim’s IT environment.
This attack exemplifies the latest advancements in Russia’s cyber-physical attack capabilities, particularly visible since Russia’s invasion of Ukraine. The techniques used indicate a maturing offensive OT arsenal, capable of identifying novel OT threat vectors, developing new capabilities, and leveraging various types of OT infrastructure for attacks. Utilizing LotL techniques likely reduced the time and resources required for the cyber-physical attack. Although the initial intrusion point remains undetermined, the rapid development of the OT component of this attack suggests the actor’s ability to swiftly create similar capabilities against other OT systems globally.
Sandworm, active since at least 2009, is a versatile threat actor conducting espionage, influence, and attack operations, primarily supporting Russia’s Main Intelligence Directorate (GRU). The group’s primary focus has been Ukraine, where it has orchestrated disruptive and destructive attacks using wiper malware, especially during Russia’s re-invasion in 2022. However, Sandworm’s activities extend globally, underlining the Russian military’s extensive ambitions and interests in various regions. The group’s global threat activity and novel OT capabilities necessitate proactive measures from OT asset owners to mitigate potential risks.
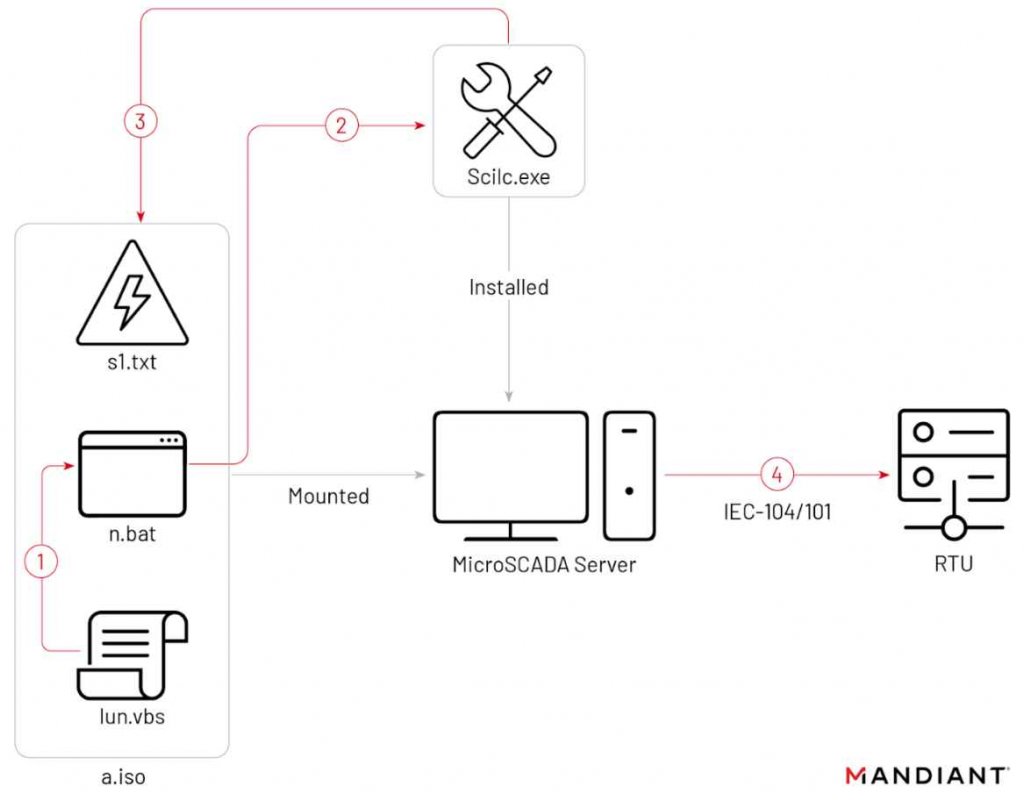
As per mandiant research, the 2022 intrusion began or prior to June 2022, culminating in two disruptive events on October 10 and 12. Sandworm accessed the OT environment via a hypervisor hosting a SCADA management instance for a substation, potentially having SCADA system access for up to three months. On October 10, Sandworm used an optical disc (ISO) image, “a.iso,” to execute a native MicroSCADA binary, likely for malicious control commands to switch off substations. The attackers, got into the operational technology (OT) system through a key piece of software (a hypervisor) that managed the control system (SCADA) of a power substation. This means they had access to the system that controls how the power substation works. For up to three months, they could have been inside this system without being detected. On October 10, they used a special file (an ISO image named “a.iso”) to run a command in the control system that was likely intended to turn off power substations.
This case underscores the evolving nature of cyber threats, particularly in critical infrastructure sectors. The increasing sophistication and rapid development of such attacks highlight the need for enhanced cybersecurity measures, continuous monitoring, and preparedness against novel and complex cyber threats in OT and ICS environments.
In OT/ICS environments, such LotL attacks are particularly concerning because they:
Defending against such attacks requires a combination of robust cybersecurity practices, including employee training, network segmentation, constant monitoring for anomalous behaviors, and regular updating and patching of all systems.
Business internet safety guide
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 10 2023

In a recent and alarming development, the notorious Russia-linked threat actor Sandworm executed a sophisticated cyber-physical attack targeting a critical infrastructure organization in Ukraine.
The incident, responded to by cybersecurity firm Mandiant, unfolded as a multi-event assault, showcasing a novel technique to impact Industrial control systems (ICS) and operational technology (OT).
The attack, spanning from June to October 2022, demonstrated a significant evolution in Russia’s cyber-physical attack capabilities, notably visible since the invasion of Ukraine.
Sandworm, known for its allegiance to Russia’s Main Intelligence Directorate (GRU), has historically focused on disruptive and destructive campaigns, particularly in Ukraine.
The unique aspect of this attack involved Sandworm’s utilization of living-off-the-land (LotL) techniques at the OT level, initially causing an unplanned power outage in conjunction with missile strikes across Ukraine.
The threat actor further demonstrated its adaptability by deploying a new variant of the CADDYWIPER malware in the victim’s IT environment.
Mandiant’s analysis revealed the complexity of the attack, highlighting Sandworm’s ability to recognize novel OT threat vectors, develop new capabilities, and exploit various OT infrastructures.
The threat actor’s deployment of LotL techniques indicated a streamlined approach, reducing the time and resources required for the cyber-physical assault.
Despite being unable to pinpoint the initial intrusion point, Mandiant suggested that the OT component of the attack may have been developed in as little as two months.
This raises concerns about Sandworm’s capability to rapidly adapt and deploy similar attacks against diverse OT systems worldwide.
Sandworm’s global threat activity, coupled with its novel OT capabilities, prompted a call to action for OT asset owners worldwide.
Mandiant provided detailed guidance, including detection methods, hunting strategies, and recommendations for hardening systems against such threats.
The attack’s timing, coinciding with Russian kinetic operations, suggested a strategic synchronization, indicating that the threat actor may have been waiting for a specific moment to deploy its capabilities.
As observed in this incident, the evolution of Sandworm’s tactics offers insights into Russia’s ongoing investment in OT-oriented offensive cyber capabilities.
In conclusion, this Sandworm attack serves as a stark reminder of the escalating cyber threats faced by critical infrastructure globally.
The continuous evolution of cyber adversaries necessitates a proactive approach from governments, organizations, and asset owners to secure and safeguard vital systems against such sophisticated attacks.
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 09 2023
If you are not using a reliable VPN, your private information can be easily accessed by third parties. Get NordVPN to protect yourself from prying eyes.
Next-generation encryption
Connect to a VPN server and be sure that NordVPN’s cutting-edge A-256 encryption keeps your online data safe, even on public Wi-Fi.
Malware protection
Enjoy a higher level of security with NordVPN’s Threat Protection feature. Scan downloads for malware, block trackers, and hide ads.
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory
Nov 09 2023
CVE-2023-4911 is a serious security vulnerability within the GNU C Library (glibc), specifically in the dynamic loader ld.so, associated with the processing of the GLIBC_TUNABLES environment variable. This vulnerability has been exploited in cloud attacks, particularly by a group using the Kinsing malware for cryptojacking operations.
The flaw is a buffer overflow that can be exploited by a local attacker using specially crafted GLIBC_TUNABLES environment variables when launching binaries with Set-UID (SUID) permissions, which could potentially allow the execution of code with elevated privileges. The Qualys Threat Research Unit has been credited with discovering this vulnerability.
This vulnerability has been given a severity score of 7.8, which classifies it as high severity. Exploitation of this flaw could enable an attacker to gain root permission on a Linux system that is running a vulnerable version of GLIBC, specifically version 2.34 or similar.
The issue has been noted to impact major Linux distributions, and organizations that use Linux systems, especially in cloud environments, are advised to patch this vulnerability promptly to mitigate the risks associated with it.
Exploit
To exploit CVE-2023-4911, threat actors would typically follow a sequence of steps that hinge on local access to a vulnerable system. The exploitation process can generally be broken down into the following stages:
ld.so is affected by the buffer overflow. This access could be obtained through various means, such as compromising a low-privileged user account.GLIBC_TUNABLES environment variable. This variable is meant to be used for tuning performance and behavior aspects of the GNU C Library, but when crafted maliciously, it can trigger a buffer overflow.ld.so) is handling the environment variable.Here’s a hypothetical example:
GLIBC_TUNABLES variable and uses it in conjunction with a vulnerable application that has SUID set to run as root.ld.so, which Bob exploits to redirect the application’s execution flow to his shellcode.It’s important to note that exploitation of CVE-2023-4911, like many vulnerabilities, requires specific conditions to be met and often sophisticated knowledge of software internals, memory layout, and exploitation techniques. The exact details of the exploit can vary based on the system’s configuration, the attacker’s goals, and the environment variables involved.
The Aqua Nautilus team documented an attack by the Kinsing malware that exploited CVE-2023-4911 to elevate permissions on a compromised machine. Here’s how they described the exploitation process:
/tmp.gnu-acme.py, which was an exploit for the Looney Tunables vulnerability (CVE-2023-4911), allowing for local privilege escalation by exploiting a buffer overflow in the handling of the GLIBC_TUNABLES environment variable by ld.so.This attack demonstrates the attackers’ sophisticated capabilities in chaining vulnerabilities to penetrate cloud environments, gain unauthorized access, and elevate privileges within the system.
Kinsing aims to gather CSP credentials, potentially exposing sensitive data, like AWS instance identity, which poses risks in cloud environments.
Here below, we have mentioned all the types of credentials and data that could be exposed:-
Mitigation
To mitigate an attack exploiting CVE-2023-4911, you should take the following steps:
By following these steps, you can significantly reduce the risk of exploitation and mitigate potential damage from attacks like those involving CVE-2023-4911.
InfoSec tools | InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory