by Mike Holcomb

Checkout previous OSINT posts here
InfoSec and Compliance – With 20 years of blogging experience, DISC InfoSec blog is dedicated to providing trusted insights and practical solutions for professionals and organizations navigating the evolving cybersecurity landscape. From cutting-edge threats to compliance strategies, this blog is your reliable resource for staying informed and secure. Dive into the content, connect with the community, and elevate your InfoSec expertise!
Nov 27 2024
Nov 27 2024
The article emphasizes the importance of the MITRE Engenuity ATT&CK Evaluations for security leaders in navigating the complex cybersecurity landscape. These evaluations simulate real-world threats to test how vendors’ solutions detect, respond to, and report adversary tactics, techniques, and procedures (TTPs). The evaluations leverage the globally recognized MITRE ATT&CK framework, which categorizes TTPs into a structured model, helping organizations assess and address security gaps effectively.
Key factors that set MITRE ATT&CK Evaluations apart include their focus on real-world conditions, transparent results, and alignment with the ATT&CK framework. Unlike traditional assessments, these evaluations emulate attack scenarios, enabling vendors to demonstrate their capabilities under realistic conditions. The transparency of the results allows organizations to evaluate performance metrics directly, helping security leaders choose solutions tailored to their unique threat environments.
The 2023 MITRE ATT&CK Evaluation highlighted notable advancements, with Cynet achieving 100% visibility and analytic coverage without configuration changes—a first in the evaluation’s history. For 2024, MITRE plans to introduce more targeted evaluations, testing vendor solutions against adaptable ransomware-as-a-service variants and North Korean state-sponsored tactics, expanding coverage to Linux, Windows, and macOS platforms.
Cybersecurity leaders are encouraged to closely monitor the upcoming results, which will offer valuable insights into the strengths and weaknesses of vendor solutions. By leveraging these findings, organizations can refine their defenses, mitigate risks, and strengthen resilience against evolving threats. The Cynet-hosted webinar provides an opportunity to understand and act on these evaluations, making them a critical resource for informed decision-making.
For further details, access the full article here

Previous articles on Mitre Att&ck Framework
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services
Nov 22 2024

The redesigned Atomic Red Team website features a new browser interface, improved search capabilities, and easier test execution
Red Canary’s Atomic Red Team is an open-source framework designed to help security teams test their detection capabilities against adversary tactics defined in the MITRE ATT&CK framework. It provides small, portable tests, enabling organizations to simulate specific attacker techniques in a controlled environment. This framework empowers defenders to validate their security controls, identify gaps in detection, and better understand malicious behaviors. Atomic Red Team offers a highly flexible approach, supporting manual execution via command-line scripts or automated tools like Invoke-Atomic, a PowerShell module that simplifies running tests
The platform focuses on making security testing accessible to teams of all sizes by offering easy-to-follow documentation and a community-driven approach. Tests are mapped to MITRE ATT&CK tactics, allowing users to tailor simulations to their environment while ensuring compliance with security protocols. By leveraging these tests, organizations can proactively enhance their detection capabilities, address visibility gaps, and prepare for real-world threats effectively
The new site provides several long-requested feature additions such as an easier method to execute the sometimes complex command lines in your environment, more detailed searching and filtering capabilities, and a generally more streamlined interface. This convenient interface ensures that even a casual user can learn about and launch tests in their own environment to help improve their security posture.

Previous posts on Att&ck Matrix
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services
Nov 22 2024
A group of Chinese researchers has successfully cracked RSA and AES encryption using D-Wave quantum computers. This breakthrough marks the first time such widely used encryption methods have been defeated. RSA, used in digital security protocols like HTTPS, relies on the difficulty of factoring large prime numbers. AES, on the other hand, protects sensitive data by converting it into unintelligible code. Both encryption methods are foundational to modern cybersecurity and global data protection systems.
The researchers employed a combination of advanced quantum computing and innovative algorithms to break the encryption. Quantum computers, unlike classical systems, process information using quantum bits (qubits), enabling parallel computations at an unprecedented scale. This capability makes them uniquely suited to solving problems like factoring large numbers or solving complex mathematical challenges—processes essential for breaking RSA and AES.
This achievement signals an urgent need for post-quantum cryptography, which can withstand quantum attacks. Governments and technology organizations worldwide are now accelerating the development of cryptographic systems designed for this new era. This breakthrough emphasizes the importance of adopting quantum-resistant encryption to ensure long-term security for sensitive information in areas like banking, healthcare, and national defense.
The implications of this research extend beyond encryption. Quantum computing’s power could revolutionize fields such as medicine, artificial intelligence, and materials science. However, it also presents significant challenges to current cybersecurity practices. Researchers and policymakers must urgently address these dualities to harness quantum computing’s potential while mitigating its risks.
You can access the details here
The value of quantum-resistant cryptography, post-quantum cryptography, and decentralized technologies just skyrocketed.

Inside Cyber: How AI, 5G, IoT, and Quantum Computing Will Transform Privacy and Our Security
Advancing Cyber Security Through Quantum Cryptography
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | Security Risk Assessment Services
Nov 20 2024

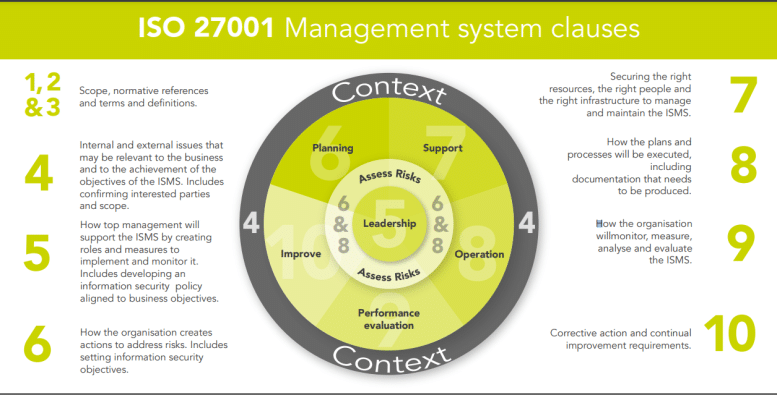
The article highlights three critical controls from ISO 27001:2022 to enhance cloud security, providing organizations with guidance on how to protect sensitive data stored in the cloud effectively:
These controls underscore the importance of robust policies, contractual due diligence, and clear delineation of responsibilities to secure cloud environments effectively. More details can be found here.
The Risk Assessment Process and the tool that supports it
What is the significance of ISO 27001 certification for your business?
Pragmatic ISO 27001 Risk Assessments
ISO/IEC 27001:2022 – Mastering Risk Assessment and the Statement of Applicability
ISO 27001 implementation ISO 27002 ISO 27701 ISO 27017 ISO27k
How to Address AI Security Risks With ISO 27001
How to Conduct an ISO 27001 Internal Audit
4 Benefits of ISO 27001 Certification
How to Check If a Company Is ISO 27001 Certified
How to Implement ISO 27001: A 9-Step Guide
ISO 27001 Standard, Risk Assessment and Gap Assessment
ISO 27001 standards and training
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Nov 13 2024

Amid the rush to adopt AI, leaders face significant risks if they lack an understanding of the technology’s potential cyber threats. A PwC survey revealed that 40% of global leaders are unaware of generative AI’s risks, posing potential vulnerabilities. CISOs should take a leading role in assessing, implementing, and overseeing AI, as their expertise in risk management can ensure safer integration and focus on AI’s benefits. While some advocate for a chief AI officer, security remains integral, emphasizing the CISO’s/ vCISO’S strategic role in guiding responsible AI adoption.
CISOs are crucial in managing the security and compliance of AI adoption within organizations, especially with evolving regulations. Their role involves implementing a security-first approach and risk management strategies, which includes aligning AI goals through an AI consortium, collaborating with cybersecurity teams, and creating protective guardrails.
They guide acceptable risk tolerance, manage governance, and set controls for AI use. Whether securing AI consumption or developing solutions, CISOs must stay updated on AI risks and deploy relevant resources.
A strong security foundation is essential, involving comprehensive encryption, data protection, and adherence to regulations like the EU AI Act. CISOs enable informed cross-functional collaboration, ensuring robust monitoring and swift responses to potential threats.
As AI becomes mainstream, organizations must integrate security throughout the AI lifecycle to guard against GenAI-driven cyber threats, such as social engineering and exploitation of vulnerabilities. This requires proactive measures and ongoing workforce awareness to counter these challenges effectively.
“AI will touch every business function, even in ways that have yet to be predicted. As the bridge between security efforts and business goals, CISOs serve as gatekeepers for quality control and responsible AI use across the business. They can articulate the necessary ground for security integrations that avoid missteps in AI adoption and enable businesses to unlock AI’s full potential to drive better, more informed business outcomes. “
You can read the full article here
CISOs play a pivotal role in guiding responsible AI adoption to balance innovation with security and compliance. They need to implement security-first strategies and align AI goals with organizational risk tolerance through stakeholder collaboration and robust risk management frameworks. By integrating security throughout the AI lifecycle, CISOs/vCISOs help protect critical assets, adhere to regulations, and mitigate threats posed by GenAI. Vigilance against AI-driven attacks and fostering cross-functional cooperation ensures that organizations are prepared to address emerging risks and foster safe, strategic AI use.
Need expert guidance? Book a free 30-minute consultation with a vCISO.
The CISO’s Guide to Securing Artificial Intelligence
Hackers will use machine learning to launch attacks
To fight AI-generated malware, focus on cybersecurity fundamentals
4 ways AI is transforming audit, risk and compliance
AI security bubble already springing leaks
Could APIs be the undoing of AI?
The Rise of AI Bots: Understanding Their Impact on Internet Security
How to Address AI Security Risks With ISO 27001
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Nov 06 2024
Cybersecurity involves technologies, processes, and measures aimed at safeguarding systems, networks, and data from cyber threats. A strong cybersecurity strategy minimizes the risk of attacks and prevents unauthorized access to systems, networks, and technologies.
Cybersecurity focuses on protecting computer systems from unauthorized access, damage, or events that would make them inaccessible.
It is important that all staff are informed about how to identify and avoid common cyber threats, and for those responsible for the technical aspects of cybersecurity to keep up to date with the latest skills and qualifications.
Processes are crucial in defining how the organization’s activities, roles, and documentation are used to mitigate the risks to the organization’s information. Cyber threats change quickly, so processes need to be continually reviewed to ensure you stay ahead.
To mitigate cyber risks, you must first identify what risks your organization faces. From there, you can implement technological controls. Technology can be used to prevent or reduce the impact of cyber risks, depending on your risk assessment and the level of risk you consider acceptable.
Types of cybersecurity threats
Phishing is a method of social engineering used to trick people into divulging sensitive or confidential information, often via email. These scams are not always easy to distinguish from genuine messages, and can inflict enormous damage on organizations.
Train your staff how to spot and avoid phishing attacks
Social engineering is used to deceive and manipulate victims into providing information or access to their computer. This is achieved by tricking users into clicking malicious links or opening malicious files, or by the attacker physically gaining access to a computer through deception.
Malware is short for “malicious software.” It can take the form of viruses, worms, Trojans, and other types of malicious code. Malware can be used to steal personal information, destroy data, and take control of computers.
Ransomware is a form of malware that encrypts victims’ information and demands payment in return for the decryption key. Paying a ransom does not necessarily guarantee that you will be able to recover the encrypted data.
cyber secure today!



What is Cybersecurity ? : FAST/FOR BEGINNERS
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Nov 05 2024
ISO 27001 certification is essential for SaaS companies to ensure data protection and strengthen customer trust by securing their cloud environments. As SaaS providers often handle sensitive customer data, ISO 27001 offers a structured approach to manage security risks, covering areas such as access control, encryption, and operational security. This certification not only boosts credibility but also aligns with regulatory standards, enhancing competitive advantage.
The implementation process involves defining an Information Security Management System (ISMS) tailored to the company’s operations, identifying risks, and applying suitable security controls. Although achieving certification can be challenging, particularly for smaller businesses, ISO 27001’s framework helps SaaS companies standardize security practices and demonstrate compliance.
To maintain certification, SaaS providers must continuously monitor, audit, and update their ISMS to address emerging threats. Regular internal and external audits assess compliance and ensure the ISMS’s effectiveness in a constantly evolving security landscape. By following ISO 27001’s guidance, SaaS companies gain a proactive approach to security and data privacy, making them more resilient against breaches and other cybersecurity risks.
Moreover, ISO 27001 certification can be a decisive factor for clients evaluating SaaS providers, as it shows commitment to security and regulatory compliance. For many SaaS businesses, certification can streamline client acquisition and retention by addressing data privacy concerns proactively.
Ultimately, ISO 27001 provides SaaS companies with a competitive edge, instilling confidence in clients and partners. This certification reflects a company’s dedication to safeguarding customer data, thereby contributing to long-term growth and stability in the competitive SaaS market. For more information, you can visit the full article here.
Need expert guidance? Book a free 30-minute consultation with a ISO27k expert.

The Risk Assessment Process and the tool that supports it
What is the significance of ISO 27001 certification for your business?
Pragmatic ISO 27001 Risk Assessments
ISO/IEC 27001:2022 – Mastering Risk Assessment and the Statement of Applicability
ISO 27001 implementation ISO 27002 ISO 27701 ISO 27017 ISO27k
How to Address AI Security Risks With ISO 27001
How to Conduct an ISO 27001 Internal Audit
4 Benefits of ISO 27001 Certification
How to Check If a Company Is ISO 27001 Certified
How to Implement ISO 27001: A 9-Step Guide
ISO 27001 Standard, Risk Assessment and Gap Assessment
ISO 27001 standards and training
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Oct 16 2024

There is a misconception among security professionals: the belief that all information security risks will result in significant business risks. This perspective is misleading because not every information security incident has a severe impact on an organization’s bottom line. Business decision-makers can become desensitized to security alerts if they are inundated with generalized statements, leading them to ignore real risks. Thus, it is essential for security experts to present nuanced, precise analyses that distinguish between minor and significant threats to maintain credibility and ensure their assessments are taken seriously.
There are two types of risks:
Not all information security risks translate directly to business risks. For example, ISO27001 emphasizes calculating the Annual Loss Expectation (ALE) and suggests that risks should only be addressed if their ALE exceeds the organization’s acceptable threshold.
Example:
Small Business Data Breach: A small Apple repair company faced internal sabotage when a disgruntled employee reformatted all administrative systems, erasing customer records. The company managed to recover by restoring data from backups and keeping customer communication open. Despite the breach’s severity, the company retained its customers, and the incident was contained. This case underscores the importance of adequate data management and disaster recovery planning.
Several factors to consider when assessing the relationship between information security and business risk:
Ultimately, information security risks must be evaluated within the broader business context. A comprehensive understanding of the company’s environment, stakeholders, and industry will help in prioritizing actions and reducing overall breach costs.
Information Risk Management: A practitioner’s guide

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Sep 09 2024

The article emphasizes that AI cybersecurity must be multi-layered, like the systems it protects. Cybercriminals increasingly exploit large language models (LLMs) with attacks such as data poisoning, jailbreaks, and model extraction. To counter these threats, organizations must implement security strategies during the design, development, deployment, and operational phases of AI systems. Effective measures include data sanitization, cryptographic checks, adversarial input detection, and continuous testing. A holistic approach is needed to protect against growing AI-related cyber risks.
For more details, visit the full article here
Benefits and Concerns of AI in Data Security and Privacy
Predictive analytics provides substantial benefits in cybersecurity by helping organizations forecast and mitigate threats before they arise. Using statistical analysis, machine learning, and behavioral insights, it highlights potential risks and vulnerabilities. Despite hurdles such as data quality, model complexity, and the dynamic nature of threats, adopting best practices and tools enhances its efficacy in threat detection and response. As cyber risks evolve, predictive analytics will be essential for proactive risk management and the protection of organizational data assets.
AI raises concerns about data privacy and security. Ensuring that AI tools comply with privacy regulations and protect sensitive information.
AI systems must adhere to privacy laws and regulations, such as GDPR, CPRA to protect individuals’ information. Compliance ensures ethical data handling practices.
Implementing robust security measures to protect data (data governance) from unauthorized access and breaches is critical. Data protection practices safeguard sensitive information and maintain trust.
Predictive analytics offers substantial benefits by helping organizations anticipate and prevent cyber threats before they occur. It leverages statistical models, machine learning, and behavioral analysis to identify potential risks. These insights enable proactive measures, such as threat mitigation and vulnerability management, ensuring an organization’s defenses are always one step ahead.
AI systems raise concerns regarding data privacy and security, especially as they process sensitive information. Ensuring compliance with privacy regulations like GDPR and CPRA is crucial. Organizations must prioritize safeguarding personal data while using AI tools to maintain trust and avoid legal ramifications.
Robust security measures are essential to protect data from breaches and unauthorized access. Implementing effective data governance ensures that sensitive information is managed, stored, and processed securely, thus maintaining organizational integrity and preventing potential data-related crises.
Adversarial AI Attacks, Mitigations, and Defense Strategies: A cybersecurity professional’s guide to AI attacks, threat modeling, and securing AI with MLSecOps
Data Governance: The Definitive Guide: People, Processes, and Tools to Operationalize Data Trustworthiness
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Sep 02 2024

DISC LLC, situated at Sonoma county, CA, is dedicated to offering premier information security services. As a consultant specializing in information security, we pride ourselves in helping businesses across the United States build resilient security programs.
When are vCISO services most appropriate? Our expert virtual Chief Information Security Officer (vCISO) services are designed to build a robust security program that effectively detects and mitigates risks. Reach out to us today to develop a security program tailored to today’s challenges.
We specialize in implementing ISO 27001 standards and establishing Information Security Management Systems (ISMS) that ensure your organization’s compliance with the highest industry standards. Achieve certification and maintain a strong competitive edge in security compliance.
DISC InfoSec offers insights on ISO 27k through its posts
Our detailed security risk assessment services identify potential threats and vulnerabilities in your systems. By understanding these risks, we develop strategic measures to counteract them, safeguarding your business from data breaches and other security incidents.
In the Information Security and Compliance industry, organizations are increasingly seeking services that help them manage the growing complexity of cyber threats and regulatory requirements.
Maintaining security compliance is crucial in today’s digital landscape. DISC LLC helps organizations navigate complex regulatory requirements, ensuring they meet all necessary standards to protect their data and operations.
Overview: As regulations and standards like GDPR, HIPAA, CCPA, and ISO 27001 become stricter, organizations seek expert advice to ensure compliance and reduce risk.
Key DISC GRC Services:
With the rapid adoption of cloud services, securing cloud environments (e.g., AWS, Azure, Google Cloud) is critical. Cloud security solutions focus on protecting data, identities, and workloads in cloud infrastructure.
DISC provide Cloud security assessments and architecture reviews.
How to manage information in the cloud: Best practice frameworks
With regulations like GDPR and CCPA, and with advent of an AI organizations need to implement measures that protect sensitive data, data governance and ensure that personal information is handled according to legal standards.
Protecting sensitive data and complying with privacy regulations is essential. AI systems must be designed to handle data securely and adhere to relevant legal and ethical standards
Understanding the risks associated with AI systems: AI Risk Management
Contact DISC LLC today at info@deurainfosec.com or call us at +17079985164 to learn more about how our services can fortify your organization’s security posture.
Build a secure future with DISC LLC.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Aug 27 2024

WordPress admins using the Litespeed Cache plugin must update their sites with the latest plugin release to address a critical vulnerability. Exploiting the flaw allows an unauthenticated attacker to take control of target websites.
The security researcher John Blackbourn from PatchStack discovered a critical privilege escalation vulnerability in the LiteSpeed Cache plugin. LiteSpeed Cache for WordPress offers an exclusive server-level cache and numerous site optimization features. The plugin boasts over 5 million active installations, indicating its popularity among WordPress users. Nonetheless, it also shows how any vulnerability in the plugin potentially threatens millions of websites. Specifically, the vulnerability existed in the plugin’s crawler feature that exhibits a user simulation functionality to perform crawler requests as authenticated users. However, due to a weak security hash in this feature, the plugin allowed an unauthenticated adversary to spoof an authenticated user and gain elevated site privileges. The worst exploitation scenarios even allowed the installation of malicious plugins and a complete site takeover. This vulnerability, identified as CVE-2024-28000, received a critical severity rating and a CVSS score of 9.8. It affected all plugin releases until 6.3.0.1. Detailed technical analysis of the vulnerability is available in the recent post from PatchStack.
Upon noticing the vulnerability, Blackbourn responsibly disclosed the flaw via Patchstack to the plugin developers. In response, the developers patched the vulnerability with the LiteSpeed Cache plugin version 6.4. The researcher also received a $14,400 bounty under the Patchstack Zero Day program for this bug report. Since the patch has arrived, all WordPress admins must update their sites with the latest plugin release to avoid potential threats. Ideally, users should update to the LiteSpeed Cache plugin version 6.4.1, which appears as the latest release on the plugin’s official page.
Attribution link: https://latesthackingnews.com/2024/08/26/litespeed-cache-plugin-vulnerability-risked-5-million-wordpress-websites/
Essential WordPress Security Plugins
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Aug 24 2024
Deura Information Security Consulting offers comprehensive vCISO services designed to build robust security programs that effectively detect and mitigate risks. Our seasoned consultants will work with you to develop a security strategy tailored to meet today’s challenges.
Securing your information assets and achieving compliance is crucial. Our experts specialize in assisting businesses with ISO 27001 implementation. Benefit from our extensive experience in information security management systems (ISMS) to ensure your organization meets the stringent requirements of ISO 27001.
At Deura Information Security Consulting, our focus is on creating and implementing security programs that address your specific needs. Contact us at info@deurainfosec.com or call +1 707-998-5164 to schedule a consultation.
Our extensive industry knowledge ensures that your security infrastructure is built to detect and mitigate risks effectively. Choose Deura Information Security Consulting for expert vCISO services and ISO 27001 compliance support.

In what situations would a vCISO or CISOaaS service be appropriate?
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Jul 31 2024
Injecting spoofed headers with email relaying involves manipulating the email headers to disguise the true origin of an email, making it appear as if it was sent from a legitimate source. Here’s a detailed explanation of how this process works:
Email headers contain vital information about the sender, recipient, and the path an email takes from the source to the destination. Key headers include:
Email relaying is the process of sending an email from one server to another. This is typically done by SMTP (Simple Mail Transfer Protocol) servers. Normally, email servers are configured to relay emails only from authenticated users to prevent abuse by spammers.
Spoofing email headers involves altering the email headers to misrepresent the email’s source. This can be done for various malicious purposes, such as phishing, spreading malware, or bypassing spam filters. Here’s how it can be done:
An attacker can use various tools and scripts to create an email with forged headers. They might use a command-line tool like sendmail, mailx, or a programming language with email-sending capabilities (e.g., Python’s smtplib).
An open relay is an SMTP server configured to accept and forward email from any sender to any recipient. Attackers look for misconfigured servers on the internet to use as open relays.
The attacker crafts an email with forged headers, such as a fake “From” address, and sends it through an open relay. The open relay server processes the email and forwards it to the recipient’s server without verifying the authenticity of the headers.
The recipient’s email server receives the email and, based on the spoofed headers, believes it to be from a legitimate source. This can trick the recipient into trusting the email’s content.
Here’s an example using Python’s smtplib to send an email with spoofed headers:
import smtplib
from email.mime.text import MIMEText
# Crafting the email
msg = MIMEText("This is the body of the email")
msg['Subject'] = 'Spoofed Email'
msg['From'] = 'spoofed.sender@example.com'
msg['To'] = 'recipient@example.com'
# Sending the email via an open relay
smtp_server = 'open.relay.server.com'
smtp_port = 25
with smtplib.SMTP(smtp_server, smtp_port) as server:
server.sendmail(msg['From'], [msg['To']], msg.as_string())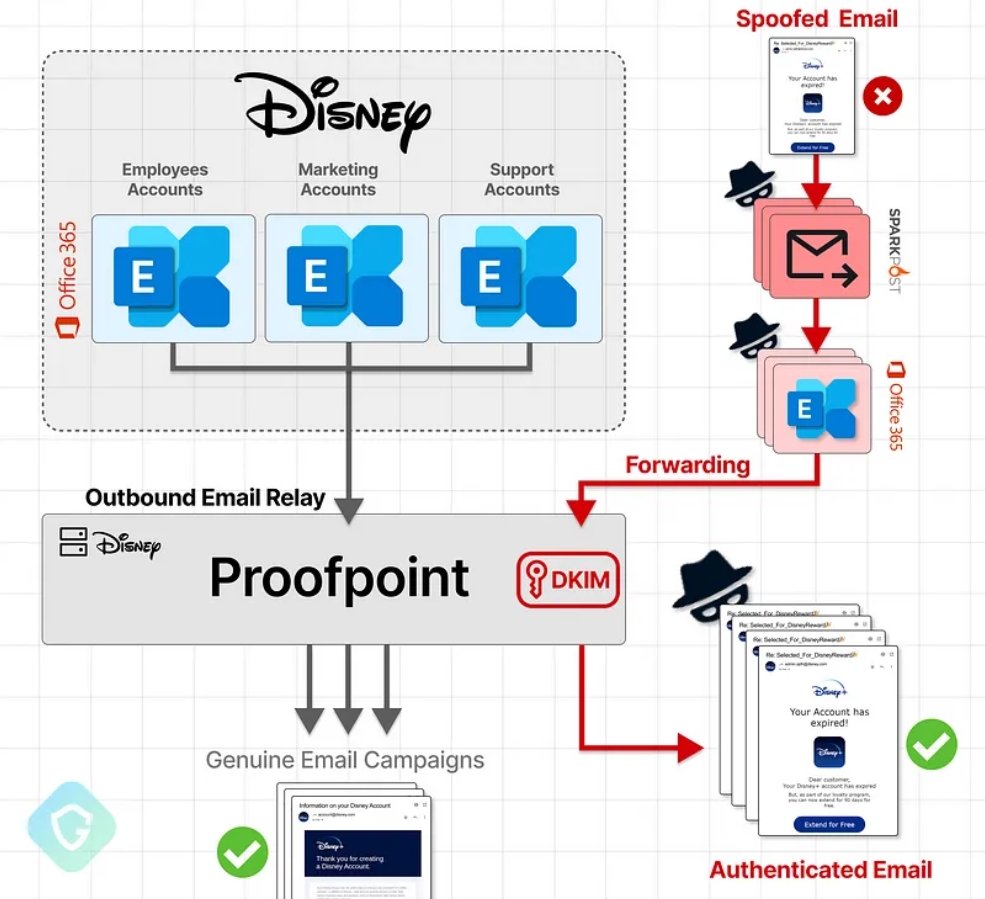
The statement about the term “via Frontend Transport” in header values refers to a specific configuration in Microsoft Exchange Server that could suggest a misconfiguration allowing email relaying without proper verification. Let’s break down the key elements of this explanation:
In Microsoft Exchange Server, the Frontend Transport service is responsible for handling client connections and email traffic from the internet. It acts as a gateway, receiving emails from external sources and forwarding them to the internal network.
Email relaying is the process of forwarding an email from one server to another, eventually delivering it to the final recipient. While this is a standard part of the SMTP protocol, it becomes problematic if a server is configured to relay emails without proper authentication or validation.
When email headers include the term “via Frontend Transport”, it indicates that the email passed through the Frontend Transport service of an Exchange server. This can be seen in the Received headers of the email, showing the path it took through various servers.
The concern arises when these headers suggest that Exchange is configured to relay emails without altering them or without proper checks. This could imply that:
Open relays are notorious for being exploited by spammers and malicious actors because they can be used to send large volumes of unsolicited emails while obscuring the true origin of the message. This makes it difficult to trace back to the actual sender and can cause the relay server’s IP address to be blacklisted.
Here’s a detailed breakdown of the key points:
protection.outlook.com.Disney’s SPF record includes spf.protection.outlook.com, which means emails sent through this relay server are authorized by Disney’s domain.protection.outlook.com), it will pass the SPF check, making it seem legitimate to the recipient’s email server.DKIM is another email authentication method that allows the receiver to check if an email claiming to come from a specific domain was indeed authorized by the owner of that domain. This is done by verifying a digital signature added to the email.
protection.outlook.com) included in Disney’s SPF record.To fully understand if the email can pass DKIM checks, we would need to know if the attackers can sign the email with a valid DKIM key. If they manage to:
Proofpoint and similar services are email security solutions that offer various features to protect organizations from email-based threats, such as phishing, malware, and spam. They act as intermediaries between the sender and recipient, filtering and relaying emails. However, misconfigurations or overly permissive settings in these services can be exploited by attackers. Here’s an explanation of how these services work, their roles, and how they can be exploited:
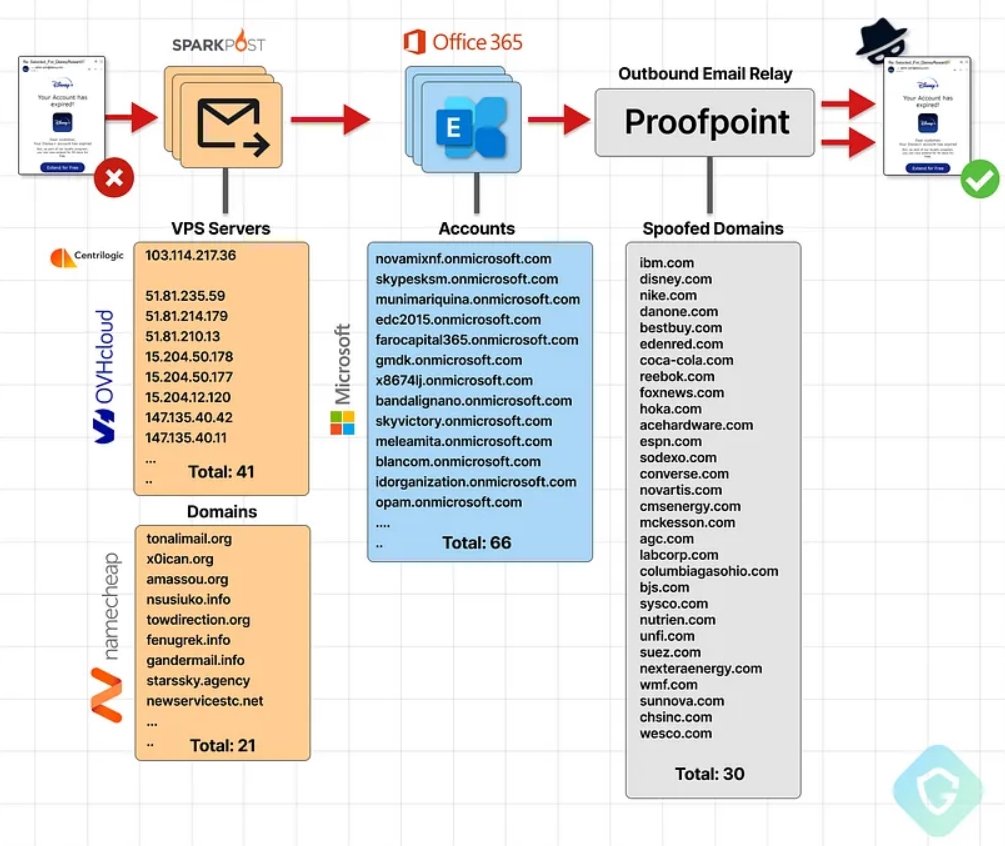
A recent attack exploited a misconfiguration in Proofpoint’s email routing, allowing millions of spoofed phishing emails to be sent from legitimate domains like Disney and IBM. The attackers used Microsoft 365 tenants to relay emails through Proofpoint, bypassing SPF and DKIM checks, which authenticate emails. This “EchoSpoofing” method capitalized on Proofpoint’s broad IP-based acceptance of Office365 emails. Proofpoint has since implemented stricter configurations to prevent such abuses, emphasizing the need for vigilant security practices.
For more details, visit https://labs.guard.io/echospoofing-a-massive-phishing-campaign-exploiting-proofpoints-email-protection-to-dispatch-3dd6b5417db6
The Domain Name System: Understand Why Domain Name Is Still Relevant
How to Catch a Phish: A Practical Guide to Detecting Phishing Emails
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Jul 24 2024
Cybersecurity jobs available right now…
Quantstamp | EMEA | Remote – View job details
As an Applied Cryptographer, you will research about various cryptographic protocols and have knowledge of cryptographic primitives or concepts, like elliptic curve cryptography, hash functions, and PCPs. You should have experience with at least one major language, like Rust, Python, Java, or C; the exact language is not too important. You should be familiar with versioning software (specifically, GitHub), testing, and a familiarity with algorithms and data structures.

KMS Lighthouse | Israel | On-site – View job details
As a Cloud Security Specialist, you will design, implement, and manage Azure and Microsoft 365 security solutions. Monitor security alerts, lead incident response, and conduct regular assessments. Ensure compliance with ISO 27001, SOC2 Type II and NIST standards.

CYBERcom | Israel | Hybrid – View job details
As a CISO, you will develop and implement comprehensive cybersecurity policies and procedures. Ensure compliance with relevant regulations and standards (e.g., GDPR, ISO 27001). Conduct risk assessments and develop mitigation strategies. Advise on security best practices and emerging threats. Collaborate with clients to enhance their security posture.
Booz Allen Hamilton | Japan | On-site – No longer accepting applications
As a Cyber Range Lead, you will lead a team of professionals as they use cyberspace capabilities to evaluate potential weaknesses as well as the effectiveness of mitigations for cyber security solutions. You will leverage cyberspace operations systems to aggregate threat feeds that inform briefings for senior leadership aligned to our client’s mission area.

Thales | Mexico | Hybrid – View job details
As a Cybersecurity Technical Consultant, you will provide onsite or remote consulting services and support to Thales customer with a focus on high quality, accuracy and customer satisfaction. Develop and deliver technical hands-on product deep knowledge transfer to customers. Track and ensure successful completion of high impact projects by creating project scoping plans, design guides and relevant documentation.

H&M | Sweden | On-site – View job details
As a Cyber Security Advisor, you will conduct security assessment of in-house developed and/or by third-party provided solutions in order to ensure that they are in compliance with H&M’s security standards. Conduct security maturity and risk assessment for internal and external partners.

PetroApp | Egypt | Remote – View job details
As a Cyber Security Engineer, you will develop and implement cyber security policies, procedures, and controls to protect the company’s digital assets. Conduct Pen-tests, monitor network traffic and security alerts to detect and respond to potential security breaches. Perform vulnerability assessments and penetration testing to identify and remediate security vulnerabilities. Conduct regular audits of security systems and processes to ensure compliance with industry standards and regulations.

Munster Technological University | Ireland | On-site – View job details
As a Cyber Security Governance Risk & Compliance Manager, you will develop, implement, and maintain a robust IT governance, risk, and compliance framework in line with industry best practices and regulatory requirements. Drive risk maturity through project lifecycle and provide independent assessments, challenge inherent risks in material changes e.g., business decisions, projects, process changes, implementation of new systems, applications, and infrastructure.

ABM College | Canada | On-site – View job details
As a Cyber Security Instructor, you will create dynamic classroom learning experiences using various teaching strategies to facilitate adult learners in achieving learning objectives in accordance with the program objectives as set out in the curriculum. Ensure students are motivated to learn and to maximize their potential. Develop different classroom strategies to ensure knowledge and skills acquisition and retention.

Accenture | Philippines | On-site – View job details
As a Digital Forensics and Incident Response Analyst, you will perform incident response to cybersecurity incidents, including but not limited to APT & Nation State attacks, Ransomware infections and Malware outbreaks, Insider Threats, BEC, DDOS, Security and Data breach, etc. Conduct in-depth investigations of cybersecurity incidents, identifying the root cause, the extent of the impact, and recommended actions for containment, eradication, and recovery, and providing a final report that contains recommendations on how to prevent the same attack in the future by strengthening security posture.

S&P Global | Italy | On-site – No longer accepting applications
As a Director of Information Security, Cyber Risk and Compliance, you will become familiar with the Cyber Risk and Compliance team activities and Market Intelligence regarding SOC reporting, relevant regulatory requirements, control frameworks, internal and external audit processes, customer interactions including security questions and audits, and overall company and divisional cyber security processes and controls. Make recommendations related to balancing requirements and deadlines made by corporate departments with human resource and technical capabilities that exist in Market Intelligence. Negotiate differences to find and implement solutions acceptable to both corporate groups and Market Intelligence.

Nexi Croatia | Croatia | Hybrid – View job details
As Head of Identity Management Platform, you will leverage your strong background in Identity and Privileged Access Management, expertise in IT technologies, and in-depth knowledge of IT security to organize and lead complex projects, manage third-party teams, and oversee platform lifecycle activities such as upgrades and integrations.

Orange Cyberdefense | Norway | Hybrid – View job details
As a Head of Consulting, you will lead, mentor, and develop a team of cybersecurity consultants, fostering a culture of excellence and continuous improvement. Define and implement the consultancy department’s strategy in alignment with the company’s goals, ensuring the delivery of innovative and effective cybersecurity solutions. Ensure that all consultancy activities adhere to industry standards, regulatory requirements, and best practices, mitigating risks to both clients and the company.

Ericsson | Thailand | On-site – View job details
As a Head of Security CU TH, you will facilitate execution of and follow up on security strategy, policies & instructions, governance model and frameworks. Support the business in implementation and maintenance of ISO 27001 controls across the CU as per the MA scope and Ericsson Global ISO 27001 control framework. Manage local security incidents and support investigations.

Bose Corporation | USA | On-site – View job details
As an IT Program Manager, you will develop, implement, and manage cybersecurity programs in alignment with the organization’s strategic objectives. Oversee the security projects related to enterprise applications, with a focus on safeguarding sensitive data and ensuring compliance with regulatory standards. Facilitate regular security assessments and audits to identify vulnerabilities and implement corrective actions.

Navy Federal Credit Union | USA | On-site – View job details
As a Penetration Tester, you will manage penetration tests from inception through delivery. Identify and prescribe remediation for vulnerabilities in NFCU applications, systems, and networks. Leverage complex tactics including, but not limited to, lateral movement, network tunneling/pivoting, credential compromise, and hash cracking.

Oracle | Spain | On-site – View job details
As a Principal Data Security Specialist, you will focus on delivering technical and procedural guidance to assist customers in defining the platform requirement though to realisation of the subscription value. Research and evaluate emerging solutions and services to drive continuous improvement.

Presight | UAE | On-site – View job details
As a Senior Architect – Cyber Security, you will develop and implement security architecture solutions to secure the organization’s IT infrastructure. Design and review security policies, standards, and procedures. Conduct security assessments and risk analysis to identify vulnerabilities and recommend mitigation strategies. Lead security projects and collaborate with cross-functional teams to integrate security measures.

Hexagon Geosystems | European Economic Area | Remote – View job details
As a Senior CyberSecurity Architect, you will plan, organize, test, and document the implementation of new security systems and tools; define the success criteria and security requirements, and develop reference architecture, functional and non-functional requirements for proof-of-concept efforts and projects. Lead in performing threat modeling, security architecture review, and risk assessments of new and existing technical solutions.

Oetker Digital | Germany | Hybrid – View job details
As a (Senior) Information Security Officer, you will develop, implement, and monitor a strategic, comprehensive company information security and IT risk management program, based on the Oetker Group-wide security directive. Manage and assist in the development in implementation of the information security policies, procedures, and guidelines. Provide guidance and counsel to the C-Level, the senior management team, and staff about information security and its alignment with business objectives and risk management.

Citi | Poland | On-site – View job details
As a Technology & Cyber Risk: Senior Officer – Cybersecurity Risk, you will review and evaluate compliance and cyber policies and procedures, technology and tools, and governance processes to provide credible challenge for minimizing losses from cyber risks. Assess cyber risks and evaluates actions to address the root causes that persistently lead to operational risk losses by challenging both historical and proposed practices. Support independent assurance activities to assess areas of concern including substantive and controls testing.

TTM Technologies | USA | Remote – View job details
As a Vulnerability Manager, you will be responsible for identifying, assessing, prioritizing, and managing vulnerabilities across our systems and networks. Conduct regular vulnerability assessments and penetration tests across our systems, applications, and networks.

Starting Your Cyber Security Career: Building a Successful Career in Cyber Security
Cybersecurity Career Master Plan
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Jun 06 2024
The hardest part of many projects is knowing where to start.
ISO 27001 is no exception. This standard describes best practice for an ISMS (information security management system).
In other words, it lays out the requirements you must meet, but doesn’t show you the how. How you can adopt or implement them.
With ISO 27001:2013 certification no longer available, many organisations are preparing to adopt the 2022 version of the standard – which means tackling a new Annex A control set, among other new requirements.
The implementation project should begin by appointing a project leader.
They’ll work with other members of staff to create a project mandate, which is essentially a set of answers to these questions:
The next step is to use your project mandate to create a more detailed outline of:
Your information security objectives should be more granular and specific than your answer to ‘What do we hope to achieve?’ from step 1.
They’ll inform and be included in your top-level information security policy. They’ll also shape how the ISMS is applied.
Your project risk register should account for risks to the project itself, which might be:
Each risk in the register should have an assigned owner and a mitigation plan. You should also regularly review the risks throughout the project.
The project plan should detail the actions you must take to implement the ISMS.
This should include the following information:
The project team should represent the interests of every part of the organisation and include various levels of seniority.
Drawing up a RACI matrix can help with this. This identifies, for the project’s key decisions, who’s:
One critical person to appoint and include in the project team is the information security manager. They’ll have a central role in the implementation project and eventually be responsible for the day-to-day functioning of the ISMS.
You’re now ready to initiate your ISMS!
A big part of this is establishing your documentation structure – any management system is very policy- and procedure-driven.
We recommend a four-tier approach:
A. Policies
These are at the top of the ‘pyramid’, defining your organisation’s position and requirements.
B. Procedures
These enact the requirements of your policies at a high level.
C. Work instructions
These set out how employees implement individual elements of the procedures.
D. Records
These track the procedures and work instructions, providing evidence that you’re following them consistently and correctly.
This structure is simple enough for anyone to grasp quickly. At the same time, it provides an effective way of ensuring you implement policies at each level of your organisation. Plus, that you develop well-functioning, cohesive processes.
Your policies and procedures must also be effective. Here are four tips:
Make sure you systematically communicate your documentation – particularly new or updated policies – throughout your organisation. Be sure to also communicate them to other stakeholders.
As part of your ISMS initiation, you’ll need to select a continual improvement methodology.
First, understand that continual improvement might sound expensive, but is cost-effective if done well. As ISO 27001 pioneer Alan Calder explains:
Continual improvement means getting better results for your investment. That typically means one of two things:
1. Getting the same results while spending less money.
2. Getting better results while spending the same amount of money.Yes, you need to be looking at your objectives, and asking yourself how well your ISMS is currently meeting them. And where your management system falls short, money may have to be spent.
But many improvements have little financial cost. You can make a process more efficient – perhaps by cutting out a step, or automating some manual work.
While continual improvement is a critical element of an ISO 27001 ISMS, the Standard doesn’t specify any particular continual improvement methodology.
Instead, you can use whatever method you wish, so long as it continually improves the ISMS’s “suitability, adequacy and effectiveness” (Clause 10.1). That can include a continual improvement model you’re already using for another activity.
ISO 27001 Standard, Risk Assessment and Gap Assessment
ISO 27001 standards and training
Key strategies for ISO 27001:2022 compliance adoption
Implementation Guide ISO/IEC 27001:2022
Please send an email related to ISO27001:2022 implementation to info@DeuraInfoSec.com and we are happy to help!
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
May 14 2024
Ensuring the security of your organization’s information systems is crucial in today’s digital landscape.
Access Control is a fundamental aspect of cybersecurity that safeguards sensitive data and protects against unauthorized access. To assist you in establishing robust access control measures, we are pleased to offer a comprehensive Access Control Policy Template, available for download.
Our Access Control Policy template is designed to provide a clear, structured framework for managing access to your organization’s information systems.
Here are some of the key components included in the template:
Implementing an effective access control policy offers several key benefits:
To take advantage of our comprehensive Access Control Policy Template, simply click on the links at the top of the article to download them. The download will start automatically.
You can then customize the template to fit the specific needs and context of your organization.
By doing so, you’ll be taking a significant step towards securing your information systems and safeguarding your valuable data.
Feel free to check out our other cybersecurity templates, such as patch management templates, incident response plan templates, email security policy templates, threat and vulnerability management templates, and more.
Gabriella is the Social Media Manager and Cybersecurity Communications Officer at Heimdal®, where she orchestrates the strategy and content creation for the company’s social media channels. Her contributions amplify the brand’s voice and foster a strong, engaging online community. Outside work, you can find her exploring the outdoors with her dog.

RELATED ARTICLES
Free and Downloadable Account Management Policy Template [2024]
Free and Downloadable Email Security Policy Template [2024]
[Free & Downloadable] Cybersecurity Incident Response Plan Templates – 2024
[Free & Downloadable] Cybersecurity Risk Assessment Templates – 2024[Free & Downloadable] Threat & Vulnerability Management Templates – 2024
[Free & Downloadable] Patch Management Templates – 2024
Employee policy handbook template
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
May 07 2024
The Damselfly Advanced Persistent Threat (APT) group, also known as APT42, has been actively utilizing custom backdoor variants, NiceCurl and TameCat, to infiltrate Windows machines.
These backdoors are primarily delivered through spear-phishing campaigns, marking a significant escalation in the capabilities and focus of this Iranian state-sponsored hacking group.
The NiceCurl and TameCat backdoors represent a sophisticated toolkit in Damselfly’s arsenal, enabling threat actors to gain initial access to targeted environments discreetly.
NiceCurl, a VBScript-based malware, is designed to download and execute additional malicious modules, enhancing the attackers’ control over compromised systems.
On the other hand, the TameCat backdoor facilitates the execution of PowerShell and C# scripts, allowing for further exploitation by downloading additional arbitrary content.
These tools are part of a broader strategy employed by Damselfly to conduct espionage and potentially disrupt operations at targeted facilities.
According to Broadcom report, the group’s activities have been primarily directed at energy companies and other critical infrastructure sectors across the U.S., Europe, and the Middle East.
The sophistication of their methods and the critical nature of their targets underscore the high level of threat they pose.
These include adaptive, behavior, file, and network-based detection mechanisms, ensuring robust defense against Damselfly’s tactics.
The security firm’s efforts are crucial in mitigating the risks posed by such state-sponsored cyber activities, characterized by their complexity and stealth.
The operations of the Damselfly group highlight the ongoing challenges in cybersecurity, where state-sponsored actors employ advanced techniques and malware to achieve their objectives.
Using custom backdoors like NiceCurl and TameCat, coupled with spear-phishing campaigns, enables these actors to maintain persistence in their target networks and carry out their missions with a high degree of secrecy and efficiency.

Ethical Hacking Module 6 – Trojans and Backdoors
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
May 03 2024
Smishing is a type of social engineering attack. Social engineering is when a cyber attacker tricks their victim into doing something they should not do, such as giving money, their password, or access to their computer. Cyber attackers have learned the easiest way to get something is just ask for it. This concept is not new, con artists and scammers have existed for thousands of years, it’s just that the Internet makes it very simple for any cyber attacker to pretend to be anyone they want and target anyone they want.
Phishing is one of the most common forms of social engineering as it’s one of the simplest and most effective and an attack method we are all familiar with. However, both organizations and individuals are becoming not only far more aware of how phishing attacks work, but much better at spotting and stopping them. Phishing is still an effective attack method, but it is getting harder and harder for cyber criminals to be effective with phishing. This is where smishing comes in.
Smishing is very similar to phishing, but instead of sending emails trying to trick people, cyber attackers send text messages. The term smishing is a combination of the words SMS messaging and phishing. You may have noticed a rise in random text messages that are trying to get you to click on links or respond to text messages. That’s smishing.
So, what type of text messaging attacks are there? While these attacks are always evolving, some of the most common are detailed below.
The text message entices you to click on a link, often through a sense of urgency, something too good to be true, or simple curiosity. Once you click on the link, the goal is usually to harvest your personal information (by getting you to fill out a survey) or your login and password (to your bank or email account, for example). Notice how, in the link in the message below, the cyber attacker uses HTTPS, an encrypted connection to make the link look more legitimate.
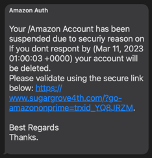
In these attacks, the cyber attacker will attempt to start a conversation with you, build trust, and ultimately scam you. Romance scams are one common example where cyber criminals randomly text millions of people to find those who are lonely or emotionally vulnerable, build a pretend romance, and then take advantage of them.
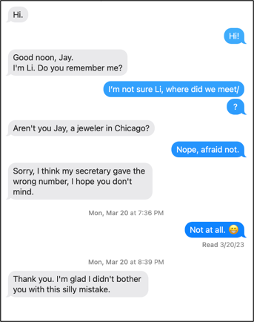
Like some phishing emails, the text message has a phone number in it and is urging the victim to call. Once the victim calls the phone number they are then scammed.
While many security training programs focus on phishing, we far too often neglect text based smishing attacks. In fact, this can create a situation where your workforce is highly aware of phishing attacks but may mistakenly think that cyber attackers only use email for attacks. From a training perspective, we recommend you teach people that cyber attackers can use a variety of different methods to trick people, to include both email phishing and text based smishing. For smishing, we do not recommend that you try to teach people about every different type of attack possible. Not only will this likely overwhelm your workforce, but cyber attackers are constantly changing their lures and techniques. Instead, like in phishing training, focus on the most commonly shared indicators and clues of an attack. This way, your workforce will be trained and enabled regardless of the method or lures cyber attackers use. Of note, the indicators below are the same indicators of an email phishing attack.
Smishing Minefield: Defusing Text Message Threats
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot
Apr 08 2024