Summary: to Address a Security Blind Spot
CrowdStrike recently announced an agreement to acquire Seraphic Security, a browser-centric security company, in a deal valued at roughly $420 million. This move, coming shortly after CrowdStrike’s acquisition of identity authorization firm SGNL, highlights a strategic effort to eliminate one of the most persistent gaps in enterprise cybersecurity: visibility and control inside the browser — where modern work actually happens.
Why Identity and Browser Security Converge
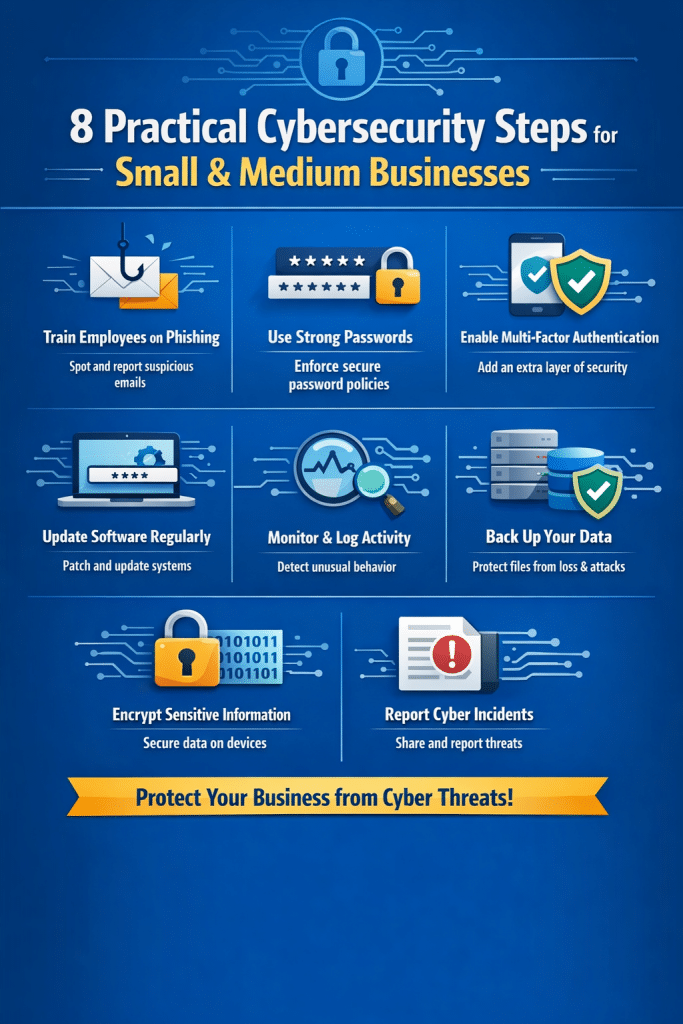
Modern attackers don’t respect traditional boundaries between systems — they exploit weaknesses wherever they find them, often inside authenticated sessions in browsers. Identity security tells you who should have access, while browser security shows what they’re actually doing once authenticated.
CrowdStrike’s CEO, George Kurtz, emphasized that attackers increasingly bypass malware installation entirely by hijacking sessions or exploiting credentials. Once an attacker has valid access, static authentication — like a single login check — quickly becomes ineffective. This means security teams need continuous evaluation of both identity behavior and browser activity to detect anomalies in real time.
In essence, identity and browser security can’t be siloed anymore: to stop modern attacks, security systems must treat access and usage as joined data streams, continuously monitoring both who is logged in and what the session is doing.
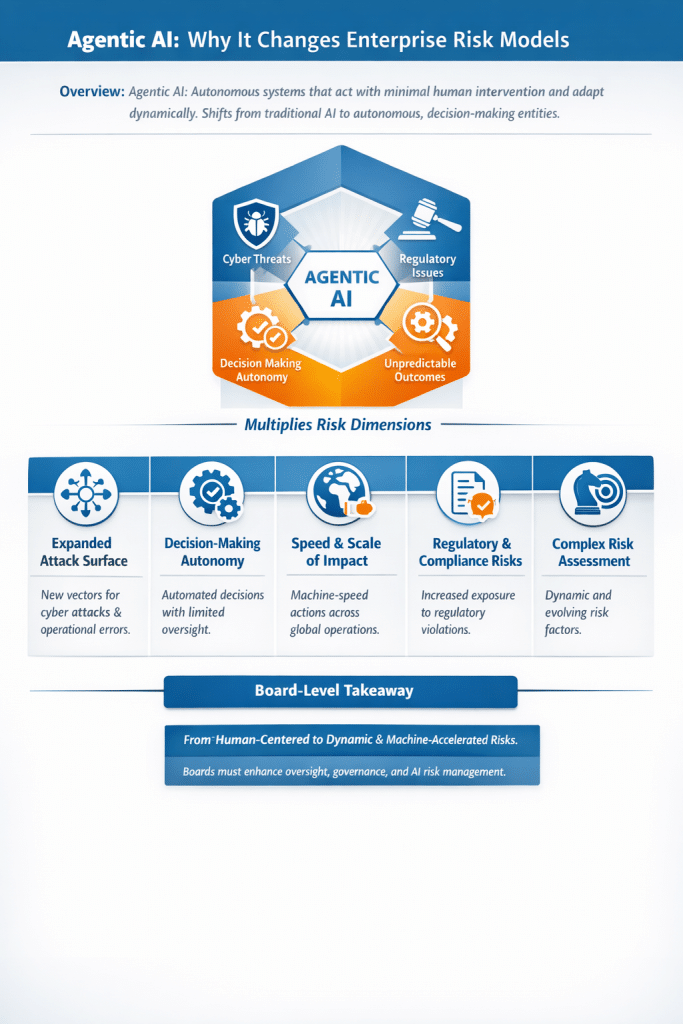
AI Raises the Stakes — and the Signal Value
The rise of AI doesn’t create new vulnerabilities per se, but it amplifies existing blind spots and creates new patterns of activity that traditional tools can easily miss. AI tools — from generative assistants to autonomous agents — are heavily used through browsers or browser-like applications. Without visibility at that layer, AI interactions can bypass controls, leak sensitive data, or facilitate automated attacks without triggering legacy endpoint defenses.
Instead of trying to ban AI tools — a losing battle — CrowdStrike aims to observe and control AI usage within the browser itself. In this context, AI usage becomes a high-value signal that acts as a proxy for risky behavior: what data is being queried, where it’s being sent, and whether it aligns with policy. This greatly enhances threat detection and risk scoring when combined with identity and endpoint telemetry.
The Bigger Pattern
Taken together, the Seraphic and SGNL acquisitions reflect a broader architectural shift at CrowdStrike: expanding telemetry and intelligence not just on endpoints but across identity systems and browser sessions. By aggregating these signals, the Falcon platform can trace entire attack chains — from initial access through credential use, in-session behavior, and data exfiltration — rather than reacting piecemeal to isolated alerts.
This pattern mirrors the reality that attack surfaces are fluid and exist wherever users interact with systems, whether on a laptop endpoint or inside an authenticated browser session. The goal is not just prevention, but continuous understanding and control of risk across a human or machine’s entire digital journey.
Addressing an Enterprise Security Blind Spot
The browser is arguably the new front door of enterprise IT: it’s where SaaS apps live, where data flows, and — increasingly — where AI tools operate. Because traditional security technologies were built around endpoints and network edges, developers often overlooked the runtime behavior of browsers — until now. CrowdStrike’s acquisition of Seraphic directly addresses this blind spot by embedding security inside the browser environment itself.
This approach extends beyond snippet-based URL filtering or restricting corporate browsers: it provides runtime visibility and policy enforcement in any browser across managed and unmanaged devices. By correlating this with identity and endpoint data, security teams gain unprecedented context for detecting session-based threats like hijacks, credential abuse, or misuse of AI tools.
Source: to Address a Security Blind Spot
My Opinion
This strategic push makes a lot of sense. For too long, security architectures treated the browser as a perimeter, rather than as a core execution environment where work and risk converge. As enterprises embrace SaaS, remote work, and AI-driven workflows, attackers have naturally gravitated to these unmonitored entry points. CrowdStrike’s focus on continuous identity evaluation plus in-session browser telemetry is a pragmatic evolution of zero-trust principles — not just guarding entry points, but consistently watching how access is used. Combining identity, endpoint, and browser signals moves defenders closer to true context-aware security, where decisions adapt in real time based on actual behavior, not just static policies.
However, executing this effectively at scale — across diverse browser types, BYOD environments, and AI applications — will be complex. The industry will be watching closely to see whether this translates into tangible reductions in breaches or just a marketing narrative about data correlation. But as attackers continue to blur boundaries between identity abuse and session exploitation, this direction seems not only logical but necessary.
InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
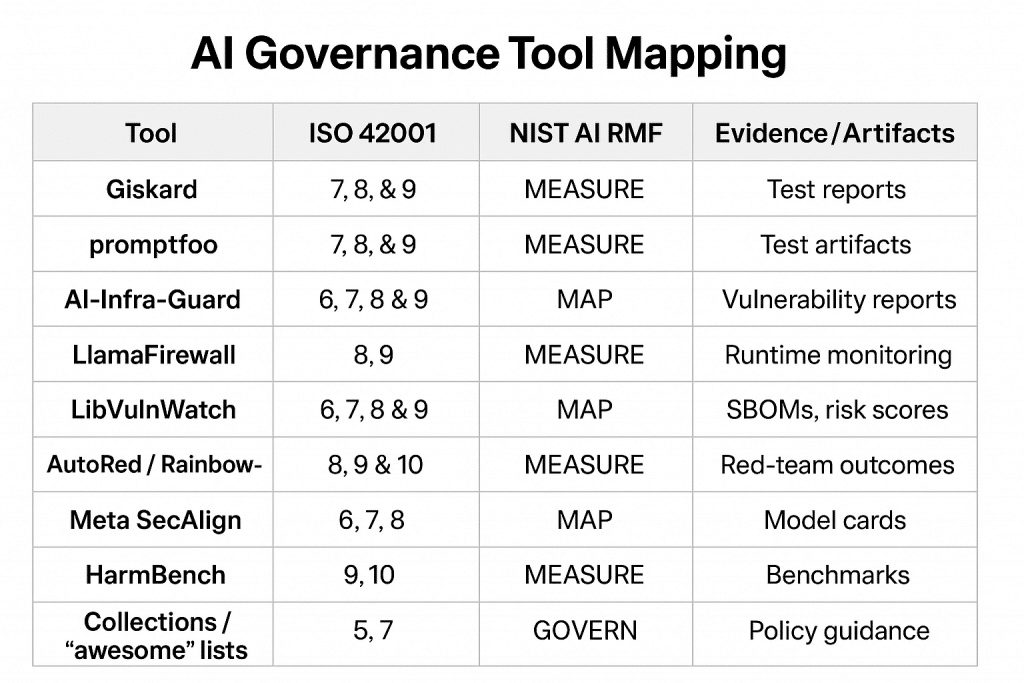
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- AI Governance Enforcement: The Foundation for Scaling AI Governance Effectively
- Securing LLM-Powered Enterprises: From Invisible Threats to Operational Resilience
- Cyber Resilience Maturity Model: From Reactive Security to Operational Resilience
- From Risk to Resilience: A 5-Step Playbook for Securing AI in the Modern Threat Era
- Which AI Governance Framework Should You Adopt First? A Practical Guide for U.S., EU, and Global Organizations