Malware analysis reports – Reports and IoCs from the NCSC malware analysis team
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
InfoSec and Compliance – With 20 years of blogging experience, DISC InfoSec blog is dedicated to providing trusted insights and practical solutions for professionals and organizations navigating the evolving cybersecurity landscape. From cutting-edge threats to compliance strategies, this blog is your reliable resource for staying informed and secure. Dive into the content, connect with the community, and elevate your InfoSec expertise!
Apr 09 2023
Apr 08 2023

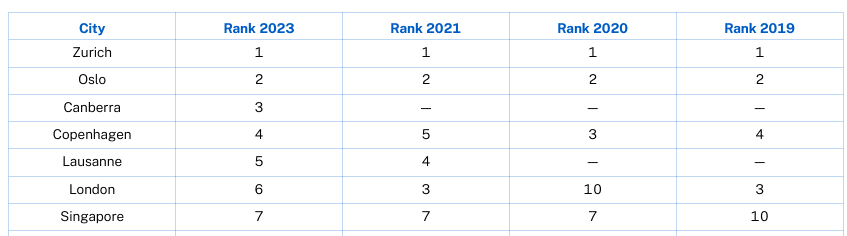
Abu Dhabi and Dubai have have been ranked as the smartest cities in the Middle East and North Africa region.in the ‘Smart City Index 2021’. The index, by the Institute for Management Development (IMD), in collaboration with Singapore University for Technology and Design (SUTD) surveys residents in ranked cities to assess smart infrastructure and services covering health and safety, mobility, activities, opportunities, and governance.
According to ITU, a smart sustainable city is an innovative city that uses information and communication technologies (ICTs) and other means to improve quality of life, efficiency of urban operation and services, and competitiveness, while ensuring that it meets the needs of present and future generations with respect to economic, social and environmental aspects.
In 2016, the ITU, the United Nations Economic Commission for Europe (UNECE) and the UN Habitat launched the initiative ‘United for Smart Sustainable Cities’ (U4SSC). The U4SSC developed a set of key performance indicators (KPIs) for Smart Sustainable Cities (SSC) to establish the criteria to evaluate the contribution of ICT in making cities smarter and more sustainable, and to provide cities with the means for self-assessments in order to achieve the sustainable development goals (SDGs).
The State of Play of Sustainable Cities and Buildings in the Arab Region-2017
The State of Play of Sustainable Cities and Buildings in the Arab Region Report (PDF 26.19 MB) is a compilation of the main public policies, programmes, case studies, organisations and initiatives associated with sustainable city and building practices in twelve countries in the Arab region. Read about the UAE’s current situation with respect to sustainable cities from pages 79 to 86.
Read more on:
The UAE Government aims to ensure sustainable development while preserving the environment and to achieve a perfect balance between economic and social development. Abu Dhabi and Dubai are planning and developing several smart sustainable cities.
For the second year in a row, Abu Dhabi and Dubai have been ranked as the smartest cities in the Middle East and North Africa region, as per the Smart City Index 2021.
While Abu Dhabi is ranked 28, Dubai is closely behind at 29, out of 118 cities. Compared to 2020, both the emirates climbed up 14 places globally.
The top three smart cities are:
Explore how New Zealand is using technology and data to design sustainable smart cities.
Smart Cities: MIT Press Essential Knowledge Series – audio book $0.00
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Apr 06 2023

The malware is designed to monitor browser activity, take screenshots, and steal cryptocurrency through scripts injected in web pages.
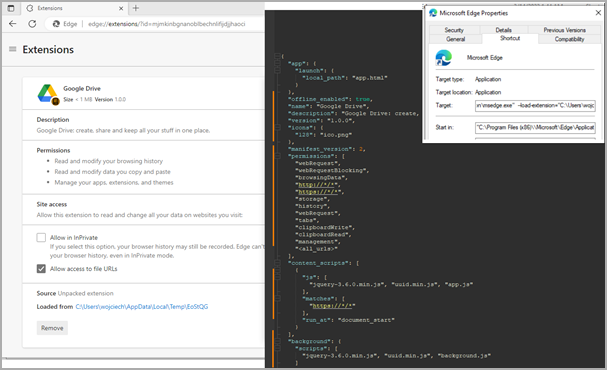
Researchers at Trustwave SpiderLabs found that Rilide mimicked benign Google Drive extensions to hide in plain sight while abusing built-in Chrome functionalities.
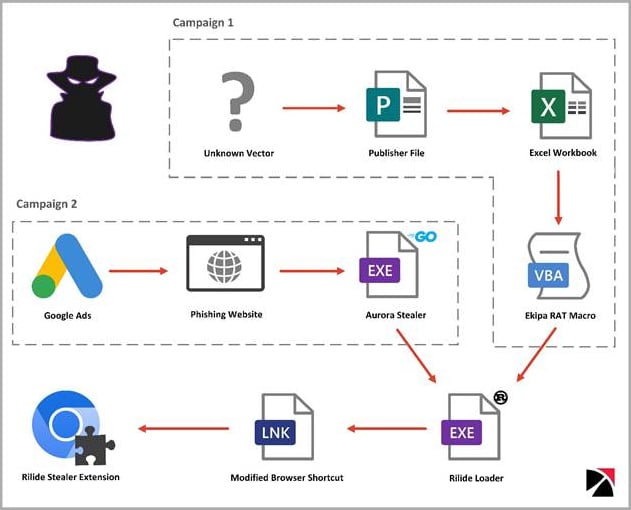
The cybersecurity company detected two separate campaigns that distributed Rilide. One was using Google Ads and Aurora Stealer to load the extension using a Rust loader. The other one distributed the malicious extension using the Ekipa remote access trojan (RAT).
While the origin of the malware is unknown, Trustwave reports that it has overlaps with similar extensions sold to cybercriminals. At the same time, portions of its code were recently leaked on an underground forum due to a dispute between cybercriminals over unresolved payment.
Rilide’s loader modifies the web browser shortcut files to automate the execution of the malicious extension that is dropped on the compromised system.
If there’s a match, the extension loads additional scripts injected into the webpage to steal from the victim information related to cryptocurrencies, email account credentials, etc.
The extension also disables ‘Content Security Policy,’ a security feature designed to protect against cross-site scripting (XSS) attacks, to freely load external resources that the browser would normally block.
In addition to the above, the extension regularly exfiltrates browsing history and can also capture screenshots and send them to the C2.
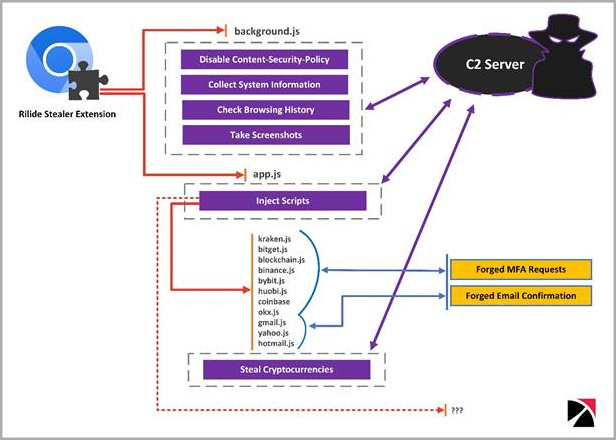
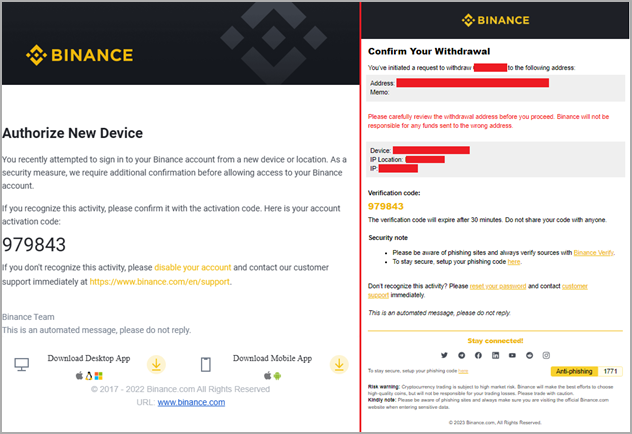
An interesting feature in Rilide is its 2FA-bypassing system, which uses forged dialogs to deceive victims into entering their temporary codes.
The system is activated when the victim initiates a cryptocurrency withdrawal request to an exchange service that Rilide targets. The malware jumps in at the right moment to inject the script in the background and process the request automatically.
Once the user enters their code on the fake dialog, Rilide uses it to complete the withdrawal process to the threat actor’s wallet address.
“Email confirmations are also replaced on the fly if the user enters the mailbox using the same web browser,” explains Turstwave in the report.
“The withdrawal request email is replaced with a device authorization request tricking the user into providing the authorization code.”
Rilide showcases the growing sophistication of malicious browser extensions that now come with live monitoring and automated money-stealing systems.
While the roll-out of Manifest v3 on all Chromium-based browsers will improve resistance against malicious extensions, Trustwave comments that it won’t eliminate the problem.
source:
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Mar 30 2023
Mar 30 2023
Mar 27 2023
In response to a recent vulnerability identified in Outlook, Microsoft recently published a proper guide for its customers to help them discover the associated IoCs.
That Outlook vulnerability in question has been tracked as “CVE-2023-23397” with a CVSS score of 9.8 and marked as Critical.
As a result of this flaw, NTLM hashes can be stolen, and without any user interaction, they can be reused to execute a relay attack.
The threat actors use specially crafted malicious emails to exploit the vulnerability and manipulate the victim’s connection. As a result, this allows them to get control of an untrusted location.

The attacker can authenticate as the victim with the Net-NTLMv2 hash leaked to the untrusted network.
In the Patch Tuesday updates for March 2023, Microsoft fixed the vulnerability in order to prevent the possibility of any further attacks.
The problem is that this approach was taken after it was weaponized by Russian threat actors and used as a weapon against the following sectors in Europe:
It was reported in April 2022 that Microsoft’s incident response team had found evidence that the shortcoming could be exploited.
It has been identified that a Net-NTLMv2 Relay attack allowed a threat actor to gain unauthorized entry to an Exchange Server in one attack chain.

By exploiting this vulnerability, the attacker could modify mailbox folder permissions and maintain persistent access, posing a significant security risk.
The adversary used the compromised email account in the compromised environment to extend their access. It has been discovered that this is done by sending additional malicious messages through the same organization to other members.
CVE-2023-23397 can lead to credential compromise in organizations if they do not implement a comprehensive threat-hunting strategy.
As a first step, running the Exchange scanning script provided by Microsoft is important to detect any malicious activity. However, it’s imperative to note that for all scenarios, this script is not capable of providing any visibility into messages that are malicious in nature.
Multiple mailboxes can be opened at the same time by Outlook users. Messages received through one of the other services will still trigger the vulnerability if a user configured Outlook to open mailboxes from multiple services. The scanned mailboxes do not contain that message.
If a user wishes to move a message to a local file, they can do so. Finding evidence of a prior compromise in Archived messages may be possible in some cases.
You can no longer access your Exchange messages if they have been deleted from Exchange. It is recommended that incident responders review the security telemetry collected from all available channels in order to confirm the presence of IP addresses and URIs obtained from the PidLidReminderFileParameter values.
There are a number of data sources that can be used to gather data, including:-
Here below we have mentioned all the recommendations:-
Source:
Mar 24 2023
It is the third day of the PWN2OWN VANCOUVER 2023 hacking contest. So far, security researchers managed to crack the operating systems Ubuntu, macOS and Windows 11, and other products, including Tesla cars and Adobe Reader.
Security researchers who managed to hack their targets win price money and the hacked devices, even if it is a Tesla.
Six of the eight hacks on day one were successful, a seventh was also successful, but it used an exploit that was known previously. Only one attempt failed to hack the target in time.

Here is the day one overview:
A total price money of $375,000 was awarded to the successful researchers and teams. The Tesla Model 3 changed owner as well.
On day two, security researchers managed to hack Oracle VirtualBox, Microsoft Teams, another Tesla, and Ubuntu Desktop.
Here is the day two overview:
The researchers received $475,000 in price money on the second day.
Attacks against Ubuntu Desktop, Microsoft Teams, Microsoft Windows 11, and VMWare Workstation are planned for the third and final day of the hacking competition.
Additional information about the successful hacks and exploits have not been released to the public. Companies whose products have been exploited will create security patches to protect their devices and applications from potential attacks targeting the bugs.
Expect security updates for all hacked products in the coming days and weeks.
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Mar 13 2023
Vendor Security Checklist – by Ministry of Security

Third Party Risk Management
Previous posts on Vendor Assessment
DISC performs Vendor assessment, we’d love to hear from you! If you have any questions, comments, or feedback, please don’t hesitate to contact us. Our team is here to help and we’re always looking for ways to improve our services. You can reach us by email (info@deurainfosec.com), or through our website’s contact form
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Mar 10 2023
The threat actor who posted the data for sale has claimed credit for multiple other breaches, including one at grocery platform Weee! that exposed data on more than 1.1 million customers.
Jai VijayanContributing Writer, Dark Reading

Hundreds of US lawmakers and their families are at risk of identity theft, financial scams, and potentially even physical threats after a known info-theft threat actor called IntelBroker made House of Representatives members’ personally identifiable information (PII) available for sale on the “Breached” criminal forum.
The information, confirmed as being obtained via a breach at health insurance marketplace DC Health Link, includes names, Social Security numbers, birth dates, addresses, and other sensitive identifying information. The data on the House members was part of a larger data set of PII belonging to more than 170,000 individuals enrolled with DC Health Link that the threat actor put up for sale this week.
In a March 8 email to members of the House and their staff, US House Chief Administrative Officer Catherine Szpindor said the attack on DC Health Link does not appear to have specifically targeted US lawmakers. But the breach was significant and potentially exposed PII on thousands of people enrolled with DC Health Link.
“The FBI also informed us that they were able to purchase this PII, along with other enrollee information, on the Dark Web,” Speaker of the House Kevin McCarthy (R-Calif.) and House Minority Leader Hakeem Jeffries (D-N.Y.) said in a joint letter to the executive director at DC Health Link on March 8. The letter sought specifics from the health exchange on the breach, including details on the full scope of the attack and DC Health Link’s plans to notify affected individuals and offer credit monitoring services for them.
Despite the letter, details of the intrusion at DC Health Link are not yet available. The organization, governed by an executive board appointed by the DC mayor, did not immediately respond to a request for comment on the incident.
A report in BleepingComputer this week first identified the threat actor as the appropriately named IntelBroker, after the cybercriminals put the stolen data up for sale on March 6. According to the underground forum ad, the data set is available for “an undisclosed amount in Monero cryptocurrency.” Interested parties are asked to contact the sellers via a middleman for details.
This is not the first big heist for the group: A threat actor, using the same moniker in February, had claimed credit for a breach at Weee!, an Asian and Hispanic food delivery service. IntelBroker later leaked some 1.1 million unique email addresses and detailed information on over 11.3 million orders placed via the service.
Security vendor BitDefender, which covered the incident in its blog at the time, published an ad that IntelBroker placed on BreachedForums that showed the attacker boasting about obtaining full names, email addresses, phone number, and even order notes which included apartment and building access codes.
Meanwhile, Chris Strand, chief risk and compliance officer at Cybersixgill says his company has been tracking IntelBroker since 2022 and is about to release a report on the actor. “IntelBroker is a highly active Breached member with an 9/10 reputation score, who claimed in the past to be the developer of Endurance ransomware,” Strand says.
IntelBroker’s use of Breached to sell the health exchange PII, instead of a dedicated leak site or a Telegram channel, is consistent with the threat actor’s previous tactics. It suggests either a lack of resources or inexperience on the individual’s part, Strand says.
“In addition to IntelBroker’s presence on Breached, the threat actor has maintained a public GitHub repository titled Endurance-Wiper,” he tells Dark Reading.
In November, IntelBroker claimed that it used Endurance to steal data from high level US government agencies, Strand notes. The threat actor has in total made some 13 claims about breaching top US government agencies, likely to attract customers to a ransomware-as-a-service (RaaS) program. Other organizations that IntelBroker claims to have broken into include Volvo, cult footwear maker Dr. Martens, and an Indonesian subsidiary of The Body Shop.
“Our intelligence analysts have been tracking IntelBroker since 2022, and we have been collecting intel attributed to that threat actor since then, as well as associated threats that have been related or attributed to IntelBroker,” Strand says.
Justin Fier, senior vice president of red team operations at Darktrace, says the threat actor’s reason for putting the data up for sale appears to be purely financially motivated rather than political. And given the high profile of the victims, IntelBroker may find that the attention the breach is garnering will increase the value of the stolen data (or bring more heat than it would like).
The buyers might be another story. Given the availability of physical addresses and electronic contact information, the kinds of potential follow-on attacks are myriad, ranging from social engineering for identity theft or espionage, to physical targeting, meaning that interested parties could run the gamut in terms of motivation.
“The amount tells you a great deal about who they may be thinking of in terms of buyers,” he says. If all that the threat actor ends up asking is a couple of thousand dollars, they are likely to be a smaller criminal enterprise. But “you start talking millions, they are clearly then catering to nation-state buyers,” he says.
Fier assesses that the data that the threat actor stole on US House members as potentially posing a national security issue. “We shouldn’t only think external nation-states that might want to purchase this,” Fier says. “Who is to say that other political parties and/or activists couldn’t weaponize it?”
Previous posts on Cyber Attacks
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Mar 06 2023
LayerX has published its annual browser security report in which the company highlights the most prominent browser security risks of 2022. The report includes predictions and recommendations for 2023 as well.
The report focuses on Enterprise environments, but several of its key takeaways apply to small business and home environments as well. The browser security threats of 2022 make up the largest part of the document, but users find predictions, recommendations and an interesting monthly overview of major security events in the report as well.
The nine major threats that LayerX identified in 2022 were the following ones:
Some of these are quite clear, others may require explanation. For phishing attacks, the researchers discovered that threat actors are hosting phishing URLs on legitimate SaaS platforms at an alarming rate. The rate of phishing attacks that use these legitimate platforms has increased by 1100% when compared to 2021, according to a Palo Alto Networks study.
LayerX conducted tests on how well browsers and network security tools protected against 1-day phishing sites. According to the test, the best performing browser had a catch rate of just 36%. Network security software blocked 48% of threats.
Similarly, malware is distributed via sanctioned services such as Google Drive and Microsoft OneDrive, to overcome blocks that may be in place for lesser known services and sites.
An analysis of data leakage in browsers concluded that 29% of users connected work browsers to personal profiles, and that 5.8% of identities were exposed in data breaches.
Outdated browsers are another threat to security, according to LayerX’s report. Ana analysis of 500 Chrome browsers revealed that a good number was either critically outdated or vulnerable to 1-day attacks.
Weak passwords and the reuse of passwords continue to be major issues. According to LayerX’s report, 29% of users use weak or medium strength passwords, and 11% of users reuse passwords regularly. The company noticed that 29% browser profiles were personal and set to sync.
Web browser extensions are another attack vector, as they “can grant excessive permissions once installed”. A recent Incogni study found that almost half of the analysed browser extensions posted either a high security or privacy risk.
The report includes an overview of browser security highlights of the year 2022. It is an interesting account that lists major security events in 2022. Some of these involved attacks, like the January 2022 video player attack that stole credit card information from over a hundred sites. Others highlight security advances, like the passwordless logins announcement by major tech companies in May, or the end of Internet Explorer in June.
The report ends with four predictions and recommendations. Predictions include that browsers will become “the main attack surface”, that attacks will “be increasingly SaaS-based and less file-based”, and that malicious web pages “will become more sophisticated”.
Closing Words
The report offers insights on the browser threat landscape of 2022, and how threats will evolve in 2023 and beyond. While most of it is aimed at Enterprise and large business environments, it may still be of interest to home users and small businesses alike.
The recommendations focus on SaaS and Enterprise-grade protections, but all users may use the listed threats to improve security. For example, outdated browsers may be updated more frequently, and weak or reused passwords may be replaced with unique strong passwords.
The report is available for download here, but a short form needs to be filled out before the download link is made available.
Source:
Previous posts on Web Security
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Web App Security
Feb 25 2023
Ethical Hacking Essentials (EHE)
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Feb 24 2023

Here are the top 10 infoSec blogs: by ChatGPT
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Feb 16 2023
A large number of e-commerce payment platforms use effective payment gateway tools and effectively integrate them with an acceptable payment strategy. Today’s e-commerce websites need to integrate anti-fraud tools, renew bank cards, integrate multiple gateways, and manage alternative payment methods.
It is important to get these complex integrations right and bring them together into one functioning system; choosing the right tokenization partner is the key to success in these processes.
Tokenization is an important process of replacing sensitive data, such as credit card numbers, with unique identifying information while preserving all important data information; a tokenization solution is a form of using a unique security key to provide an appropriate level of security to important confidential data.
Think of tokenization as a secret code that uses a key to retrieve an encrypted message. Some versions of the credit card number store the last four digits; however, the remaining digits of the credit number are random.
In this case, you can safely store the token in the database. Anyone with access to this token cannot use it to compromise your credit card account. For these tokens to be used to process credit card transactions, they must be re-linked to the original credit card numbers. Typically, this mapping is performed by a secure third party. All this is done to ensure full security.
Blockchain technology is a technology that most people associate only with cryptocurrencies. This attribution is not entirely incorrect, as the blockchain was created for the Bitcoin cryptocurrency. However, much has changed since 2009 (the year Bitcoin appeared), and the scope of blockchain technology continues to actively expand.
One of the key applications of this technology today is tokenization, a secure form of digitization based on the blockchain technology mentioned above. The process of tokenization consists of assigning a specific value to a symbol, which can exist materially or immaterially, and is a digital “token” that stores data. With this efficient solution, you can securely buy and sell your assets online.
Examples of this use of tokens include the value of the stock market. Most of us associate stocks and bonds with paper-based notices of ownership of those assets, but tokenization allows us to replace those paper notices with digital versions. The implementation of traditional solutions in the digital world simplifies and optimizes a large number of important processes, making them significantly more efficient.
The terms “token” and “cryptocurrency” are often confused and used interchangeably; not surprisingly, both concepts are closely related to blockchain technology. The key difference between cryptocurrencies and tokens is that cryptocurrencies are a means of payment, whereas tokens cannot; they can be compared to a kind of chip.
A token is created using smart contracts on a specific blockchain network and can perform various key functions. Each blockchain network can contain an unlimited number of tokens.
On the other hand, a smart contract is a kind of computer program embedded in a certain blockchain network that automatically enforces the terms contained in it. Both tokens and cryptocurrencies can be transferred on the blockchain network; however, token transaction fees depend on the cryptocurrency.
Tokenization is commonly used to protect credit card numbers, a process mandated by the Payment Card Industry Council (PCI). However, there are many different use cases, tokenization terminology allows you to learn a variety of effective tools that provide active growth in the field of security for business organizations for which it is important to reliably protect confidential data.
Consider personal or personally identifiable information. HIPPA, General Data Protection Regulation (GDPR) requires confidential processing, anonymization, and secure storage of personal data. Organizations and various business environments should use tokenization capabilities when the business needs to securely store confidential information, such as:
Due to the universality of tokens, they are divided into several types that perform different functions. One of the key differences is between mutual tokens and non-splitting tokens. For example, payment tokens are used to make payments. Their function is mainly to ensure the safety of investors. Issued security tokens are protected by law and represent specific stocks, bonds, or other assets of genuine interest.
Undoubtedly, there are many advantages to using tokens, but is it safe to store data? Security is considered one of the most important benefits of tokenization. Stability, irreversibility of transactions, and elimination of intermediaries are just some of the characteristics that affect security when using blockchain technology.
In addition, the security of tokenization is provided by smart contracts that allow parties to trade directly. For example, selling real estate in the form of tokens does not require a notary or a real estate agent. Everything is done quickly and directly.
Note that each contracting party must ensure that personal tokens are properly stored and protected from loss to properly act as guarantors of successful transactions. Tokenization is a form of business digitization based on blockchain technology.
The potential of tokenization is huge and has yet to be fully explored. Tokens are divided into different types. The most common use of tokens is to digitize different types of assets, such as physical assets, digital assets, projects, company shares, shares, or loans.
When it comes to PCI tokens, there are three key types of tokenization: gateway tokenization, end-to-end tokenization, and payment service tokenization. Gateway tokenization. When you do e-commerce, you most likely get paid through a payment gateway.
Most gateways have technology that allows you to securely store your credit card in the system, then issue a refund and delete your card data. The downside is that each gateway provides its token scheme. This means that you cannot use this gateway. Changing gateways is often a time-consuming and expensive process of moving customer data to a new gateway for secure processing.
In some cases, the gateway may not allow these actions. End-to-end tokenization. Some independent tokenization providers have their technology that sits between your e-commerce site and the gateway. These end-to-end token providers allow you to use your existing gateway integration code.
One of the key advantages of this type of tokenization is that it uses existing technology and can be adapted at a very fast pace. It also has the advantage of modularity. Unlike gateway tokenization, modularity can be actively used for more than just credit card payments. You can use the tokenization model to connect to most APIs and tokenize data other than credit card data.
End-to-end tokenization is an evolution of gateway tokenization. This gives payment solutions the freedom to route transactions to different gateways in real-time, avoiding costly and time-consuming transfers of card data between different payment platforms.
A key tokenization strategy is the payment service model. This model offers a single API that, when integrated, can route payments to multiple gateways. The payment service model is best suited for companies with more complex payment needs.
This model works well when a company needs to pay in several regions or several different currencies or through several gateways. A disadvantage of the payment service model is that existing gateway embed code cannot be reused.
In addition to reduced PCI coverage and increased security, the tokenized payment service model has unique key benefits from its active use. The payment services model not only simplifies your embed code but also takes control of your tokens away from the payment gateway. Unlike gateway tokenization, tokens provided by third parties can be actively used with supported gateways.
Tokens issued by payment gateways cannot be used against competing alternative gateways. Security and compliance alone are reasons enough to implement a popular solution like the tokenization of various assets that are important to you, your company, and your customers.
The truth is that key security requirements for online payments are difficult to implement on your own. In particular, startups often choose to sacrifice security for time to market. Accepting online payments makes your business a target for cybercriminals. Hiring security experts and implementing effective tokenization processes can save your business environment valuable time and money in the long run.
Keep these practical tips in mind. Choose a reliable tokenization partner, test the tokenization, what level of protection you can achieve by working on the integration, and find a vendor that can integrate multiple gateways, methods, and services into a single integration. One of the key technologies needed to connect all payment solutions is tokenization.
A trusted provider fully controls tokens, provides redundancy, reduces PCI coverage, and improves the security standards in place in your business environment.
The use cases for tokenization can grow endlessly. Since anything can be digitized, tokenization is often used in professional life. These are various business projects that can demonstrate the most practical examples of using tokenization.
Digitization of the company involves the creation of tokens that are closely related to a specific project. Tokenization techniques that add value to tokens can be used as an indispensable tool for automating processes in companies and as a means of financing them. Real estate tokenization is becoming more and more popular worldwide due to the following features: transaction speed, lack of intermediaries, and security.
The process of property tokenization involves issuing tokens on the blockchain network and linking them to certain properties. Thus, the investor becomes a co-owner or owner of a certain asset, the shares of which can be represented in tokens.
Using blockchain technology and a specially designed platform, it is also possible to assign unique numbers to gems and certain forms of ore to determine their authenticity.
Raw materials registered with digital numbers can then be identified by verifying their origin, properties, and associated processes. NFT tokens have the unique potential to revolutionize both the physical and digital art markets. Each NFT token has a unique, non-tradable value that allows you to express your interest in the rights to a work of art, making investing in art an easy and fast process.

Digital Finance: Security Tokens and Unlocking the Real Potential of Blockchain
Blockchain and the Future of Finance
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Feb 12 2023
Feb 10 2023
Welcome to our February 2023 review of phishing attacks, in which we explore the latest email scams and the tactics that cyber criminals use to trick people into handing over personal data.
This month, we look at a UK government warning about a resurgence in Russian cyber attacks and concerns that the much-discussed AI programme ChatGPT could be used for fraud.
The UK government has issued a warning amid an increase in phishing attacks stemming from Russia and Iran.
In an advisory statement, the NCSC (National Cyber Security Centre) shared details about the campaign, which appears to have been sponsored by the fraudsters’ national governments.
The researchers are most concerned about spear phishing, which is a sophisticated form of fraud. Scammers target specific individuals by researching them online – often using Facebook, LinkedIn or the website of the target’s employer.
Although spear phishing emails often contain the same clues as regular phishing scams, they have a much higher success rate. This suggests that people are more likely to assume that a message is genuine if it contains a few specific details about them, such as their name or their place of work.
The NCSC’s advisory highlights ongoing scams that were conducted throughout last year by the Russia-based group SEABORGIUM and the Iran-based group TA453, also known at APT42.
Their attacks target specific sectors within the UK, including academia, defence, governmental organisations, NGOs and thinktanks, as well as politicians, journalists and activists.
Commenting on the findings, NCSC Director of Operations Paul Chichester said: “The UK is committed to exposing malicious cyber activity alongside our industry partners and this advisory raises awareness of the persistent threat posed by spear-phishing attacks.
“These campaigns by threat actors based in Russia and Iran continue to ruthlessly pursue their targets in an attempt to steal online credentials and compromise potentially sensitive systems.
“We strongly encourage organisations and individuals to remain vigilant to potential approaches and follow the mitigation advice in the advisory to protect themselves online.”

ChatGPT has taken the Internet by storm, with the AI-backed tool helping writers and hobbyists create content almost instantly.
The program’s advanced language model has been championed by people looking to quickly produce quotes, articles and think pieces. However, cyber security experts are warning that another group – scammers – could also embrace the technology.
As Chester Wisniewski, the principal research scientist as Sophos, explained, ChatGPT can instantly produce grammatically correct and natural-looking writing, which would resolve one the biggest challenges that scammers face when creating their baits.
“The first thing I do whenever you give me something is figuring out how to break it. As soon as I saw the latest ChatGPT release, I was like, ‘OK, how can I use this for bad things?’ I’m going to play to see what bad things I can do with it,” Wisnieski told TechTarget.
One of those ‘bad things’ that he considered was the ability for ChatGPT to create phishing scams.
“If you start looking at ChatGPT and start asking it to write these kinds of emails, it’s significantly better at writing phishing lures than real humans are, or at least the humans who are writing them,” he said.
“Most humans who are writing phishing attacks don’t have a high level of English skills, and so because of that, they’re not as successful at compromising people.
“My concerns are really how the social aspect of ChatGPT could be leveraged by people who are attacking us. The one way we’re detecting them right now is we can tell that they’re not a professional business.
“ChatGPT makes it very easy for them to impersonate a legitimate business without even having any of the language skills or other things necessary to write a well-crafted attack.”
All organisations are vulnerable to phishing, no matter their size or sector, so it’s essential to understand how you might be targeted and what you can do to prevent a breach.

You can help educate your staff with IT Governance’s Phishing Staff Awareness Training Programme.
This 45-minute course uses real-world examples like the ones we’ve discussed here to explain how phishing attacks work, the tactics that cyber criminals use and how you can detect malicious emails.
More resources on Phishing training
InfoSec Threats | InfoSec books | InfoSec tools | InfoSec services
Feb 08 2023
Jan 31 2023
Jan 30 2023
Today, the specialists of the Cyber Security 360 course of the International Institute of Cyber Security (IICS) will show us in detail the use of Fuzz Faster U Fool (ffuf), a free and easy-to-use fuzzing tool, using the command line method for configuration on web servers.
Created by Twitter user @joohoi, cybersecurity professionals around the world have praised ffuf for its advanced capabilities, versatility, and ease of use, making it one of the top choices in fuzzing.
Before keep going, as usual, we remind you that this article was prepared for informational purposes only and does not represent a call to action; IICS is not responsible for the misuse that may occur to the information contained herein.
According to the experts of the Cyber Security 360 course, ffuf runs on a Linux terminal or Windows command prompt. Upgrading from the source code is no more difficult than compiling, except for the inclusion of “-u”.
| 1 | go get -u github.com/ffuf/ffuf |
For this example Kali Linux was used, so you will find ffuf in the apt repositories, which will allow you to install it by running a simple command.
| 1 | apt install ffuf |
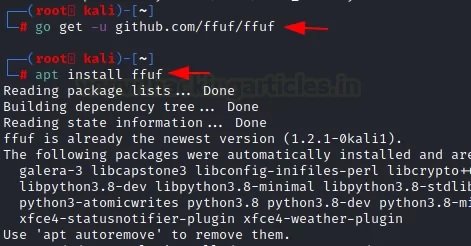
After installing this program, you can use the “-h” option to invoke the help menu.
| 1 | ffuf –h |
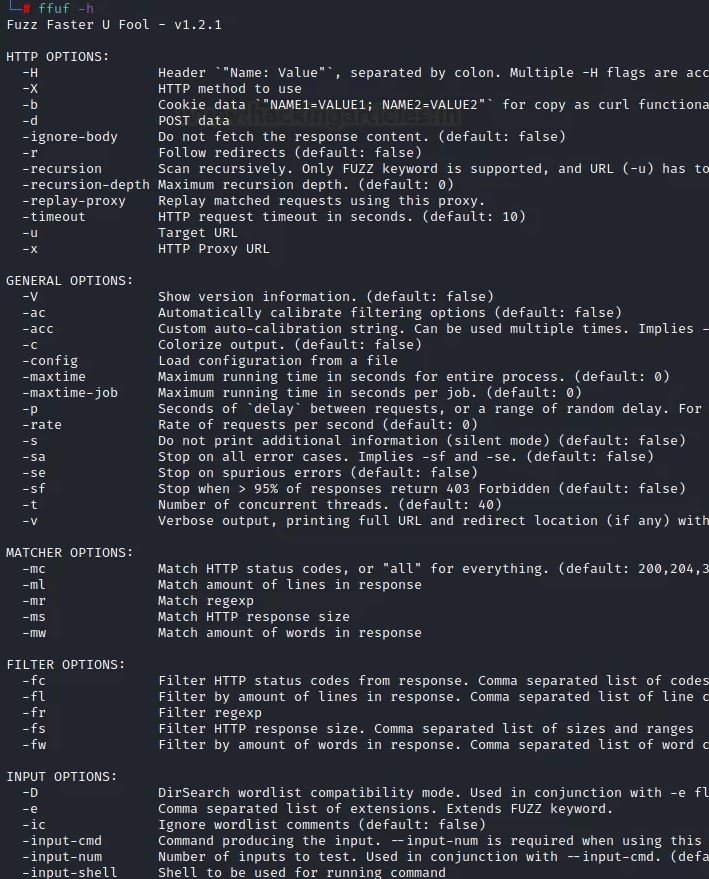
These are parameters that help us provide the data needed for a web search of a URL using word lists.
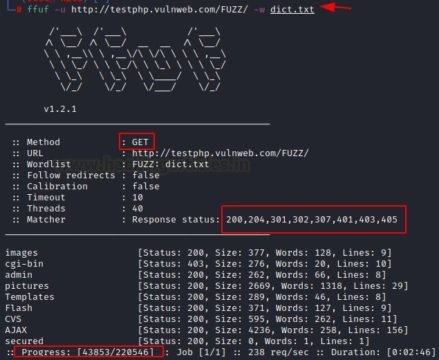
For a normal attack, use the parameters “-u” for the target URL and “-w” to load the word list.
| 1 | ffuf -u http://testphp.vulnweb.com/FUZZ/ -w dict.txt |
After you run the command, you will need to focus on the results.
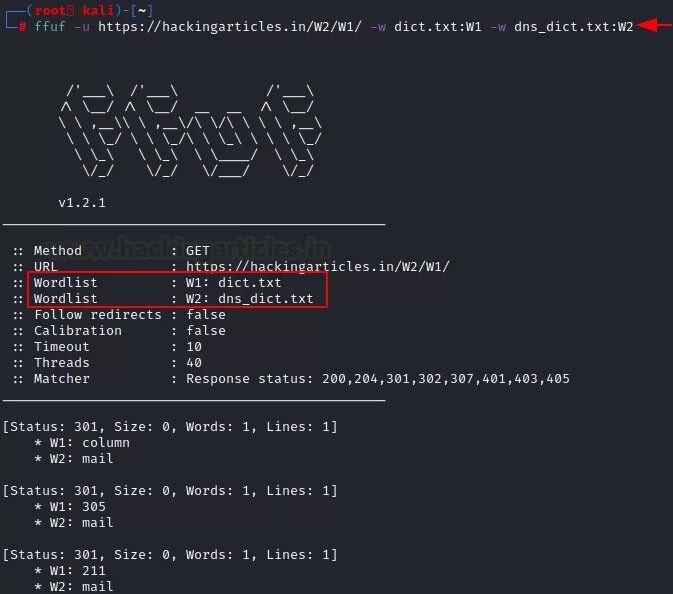
The experts of the Cyber Security 360 course mention that a single list of words is not always enough to get the desired results. In these cases, you can apply multiple word lists at the same time, one of the most attractive functions of ffuf. In this example, we have granted the program access to two dictionaries (txt:W1 and txt:W2), which the tool will run at the same time:
| 1 | ffuf -u https://ignitetechnologies.in/W2/W1/ -w dict.txt:W1 -w dns_dict.txt:W2 |
Usually, the default word list has some comments that can affect the accuracy of the results. In this case, we can use the “-ic” parameter to delete the comments. Also, to remove any banners in the tools used, use the “-s” parameter:
| 1 | ffuf -u http://testphp.vulnweb.com/FUZZ/ -w dict.txt |
Here we can notice that some comments are shown in the results if the above command is executed. After using the “-s” and “-ic” parameters, all comments and banners will be removed.
| 1 | ffuf -u http://testphp.vulnweb.com/FUZZ/ -w dict.txt -ic –s |

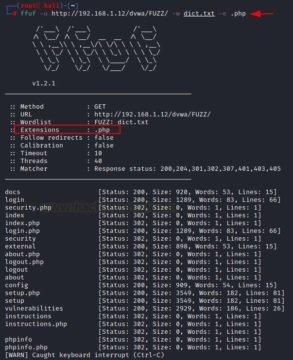
It is also possible to search for a file with a specific extension on a web server using the “-e” option. All you need to do is specify the extension and name of the file along with the parameter in the appropriate command format:
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -e .php |
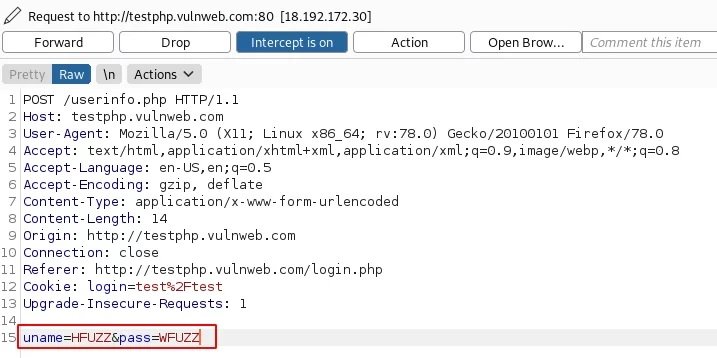
Burp Suite is a professional platform for monitoring the security of web applications. The “cluster bomb” function allows using multiple payloads, mention the experts of the Cyber Security 360 course. There is a separate payload package for each given location; the attack goes through each payload packet one by one, checking all possible options.
There are several parameters of this tool that make it easy to use the script. For example, the “-request” parameter allows you to use the request in an attack, while “-request-proto” allows you to define the parameter itself, and “-mode” helps you choose the attack mode.
First, random credentials are used on the target URL page and the proxy server is configured to capture the request in interception mode in Burp Suite.

Now, on the Intercept tab, you need to change the credentials provided by adding HFUZZ and WFUZZ. HFUZZ is added before “uname” and WFUZZ before “pass”. Then, you need to copy and paste this query into the text and name according to the purposes of the project. In this case, the file was named as brute.txt.
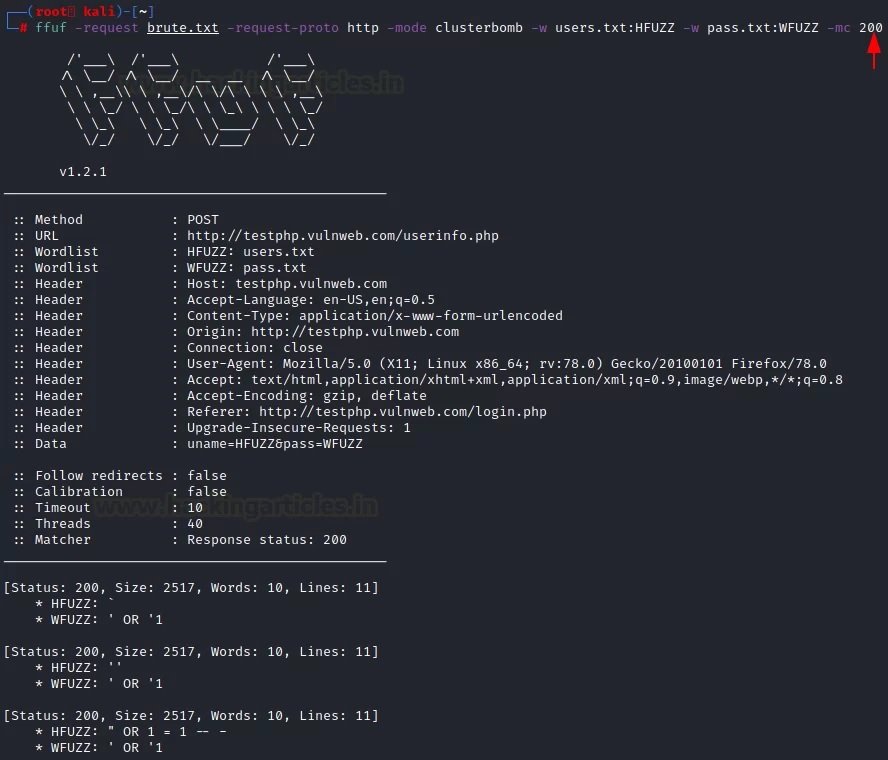
Later we will move to the main attack mode, where the “-request” parameter contains a “-request-proto” text file that will help you create a prototype of http, and “-mode” will be responsible for the “cluster bomb” attack. The lists of words in question (users.txt and pass.txt) consist of SQL injections. By entering the following command, an attack will be launched:
| 1 | ffuf -request brute.txt -request-proto http -mode clusterbomb -w users.txt:HFUZZ -w pass.txt:WFUZZ -mc 200 |
As you can see from the results of the attack, SQL injections have been successfully found to be effective for this specific purpose.
If we want the ffuf to show only the data that is important for web fuzzing, we must pay attention to these parameters. For example, it can be HTTP code, strings, words, size and regular expressions, mention the experts of the Cyber Security 360 course.
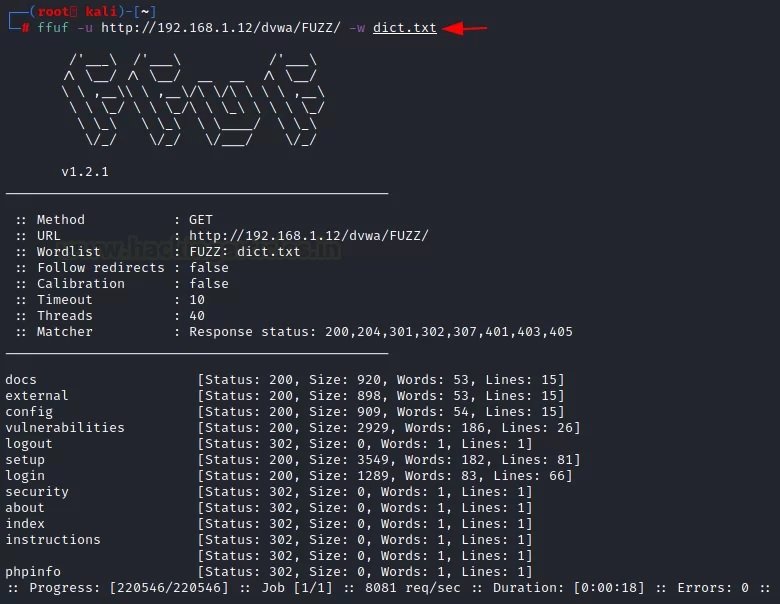
To understand this configuration, you should consider a simple attack on which you will be able to see which HTTP codes appear in the results.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt |
It is clear that the codes 302 HTTP and 200 HTTP were received.
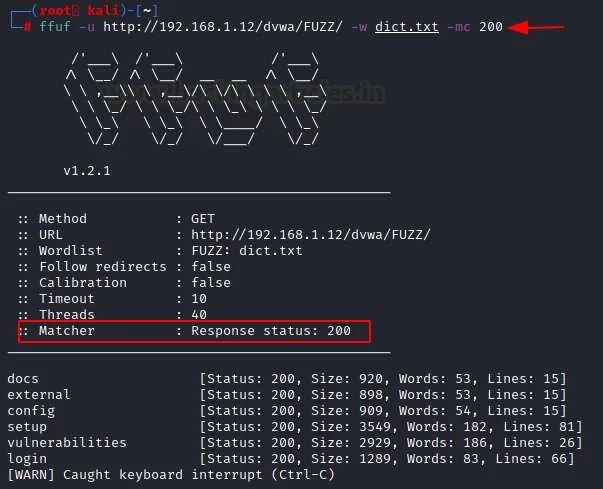
If you want to see specific attacks, such as HTTP code 200, you must use the “-mc” parameter along with a specific number. To verify that this parameter works, you just need to run the following command:
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -mc 200 |
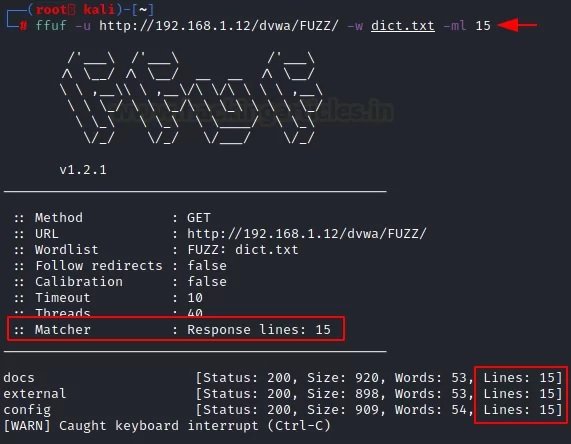
The tool returns results for specific lines in the file using the “-ml” parameter. We can use it by specifying the strings we need.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -ml 15 |
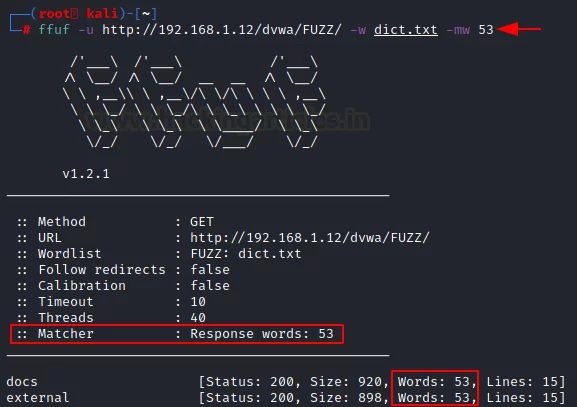
Similarly, since the above options correspond to a function, you can provide a result with a certain number of words. For this, use the “-mw” parameter along with the number of words you want to see in the results.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -mw 53 |
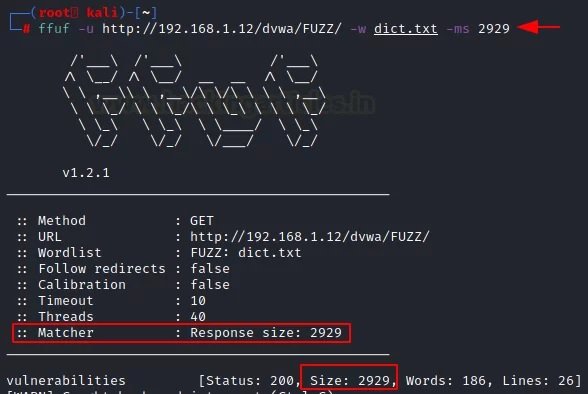
It is also possible to use the “-ms” parameter along with the specific size you want to see in the results.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -ms 2929 |
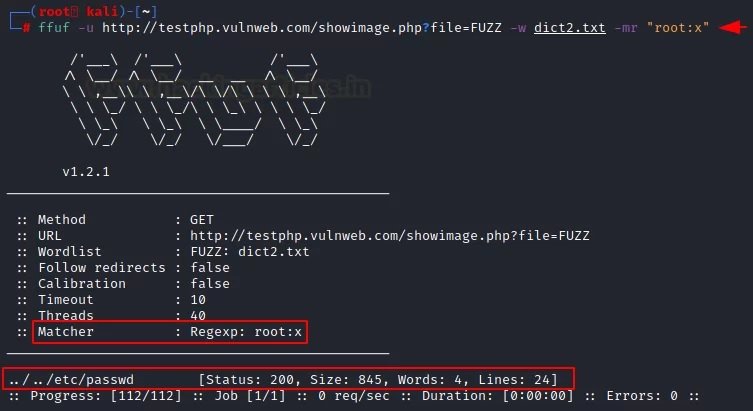
This is the last of all the mapping options available in ffuf. LFI fuzzing will be applied by matching the string to the subsequent “root:x” pattern for this dictionary.
A URL is used that can provide this functionality, and with the “-mr” parameter, the corresponding string “root:x” is defined. This is what a special list of words looks like.
Using this list of words, we enter the following command to add the “-mr” parameter to the attack script:
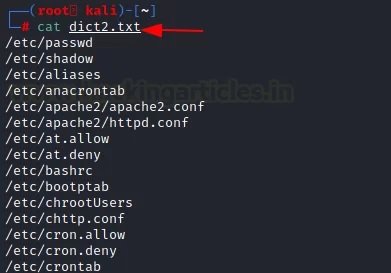
| 1 | ffuf -u http://testphp.vulnweb.com/showimage.php?file=FUZZ -w dict2.txt -mr "root:x" |
We received the http 200 response for /etc/passwd for this list of words.
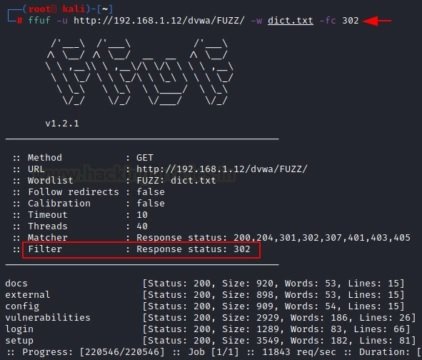
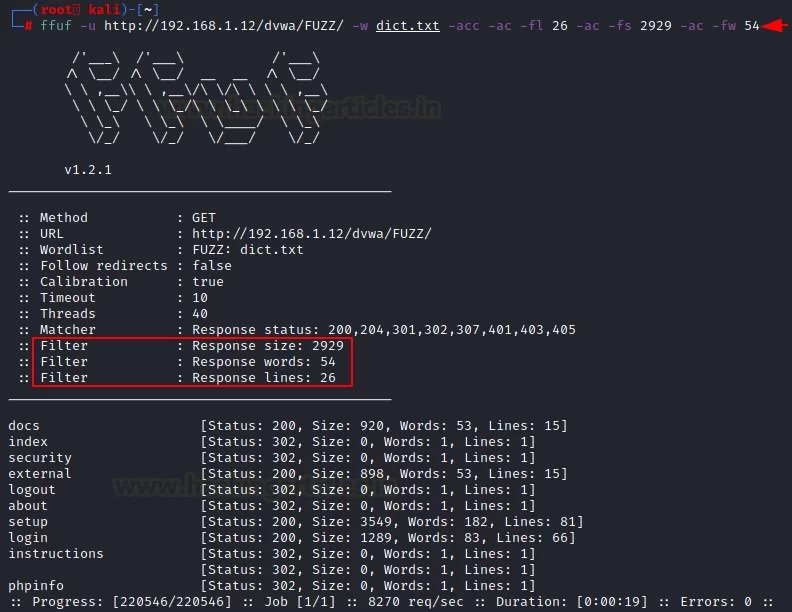
Filtering options are the exact opposite of matching parameters. The experts of the Cyber Security 360 course recommend using these options to remove unnecessary elements during web fuzzing. It also applies to HTTP code, strings, words, size, and regular expressions.
The “-fc” parameter requires a specific HTTP status code that the user wants to remove from the results.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -fc 302 |
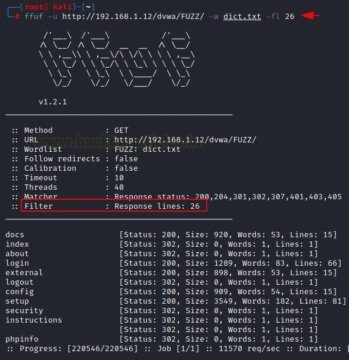
With the help of the “-fl” parameter, it is possible to remove a certain row from the result or filter it from the attack.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -fl 26 |
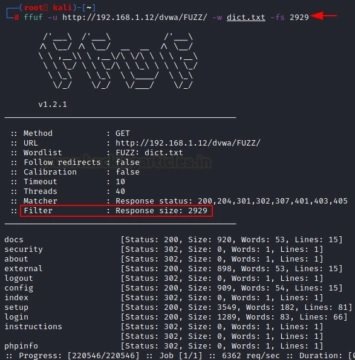
The “-fs” option allows you to filter the specified size described by the user during the attack.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -fs 2929 |
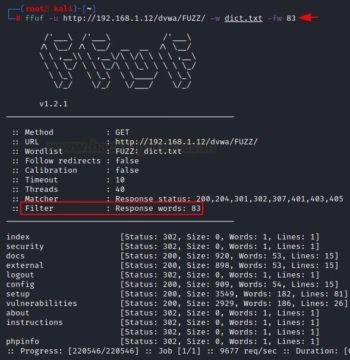
The “-fw” option allows you to filter the number of words of the results that the user wants to receive.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -fw 83 |
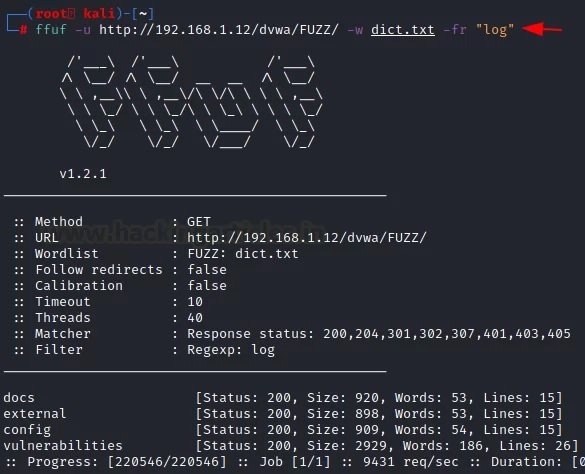
The “-fr” option allows you to delete a specific regular expression. In this case, we will try to exclude the log files from the results.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -fr "log" |
Below are the general parameters of this tool, which are completely related to the web fuzzing process.
Calibration is the process of providing a measuring instrument with the information it needs to understand the context in which it will be used. When collecting data, calibrating your computer ensures that the process works accurately, mention the experts of the Cyber Security 360 course.
We can adjust this function according to the needs in each case using the “-acc” parameter, which cannot be used without the “-ac” parameter.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -acc -ac -fl 26 -ac -fs 2929 -ac -fw 54 |
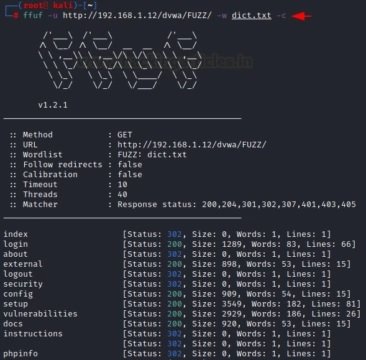
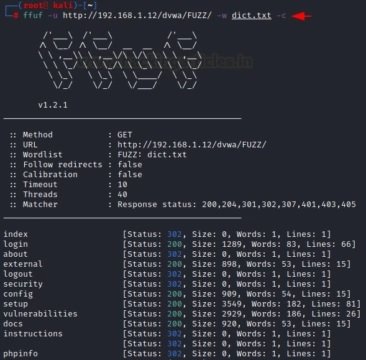
Sometimes color separation helps identify relevant details in the results. The “-c” parameter helps to divide the data into categories.ç
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt –c |
If you want to apply fuzzing for a limited period of time, you can use the “-maxtime” parameter. You must enter a command to specify the selected time interval.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -maxtime 5 |
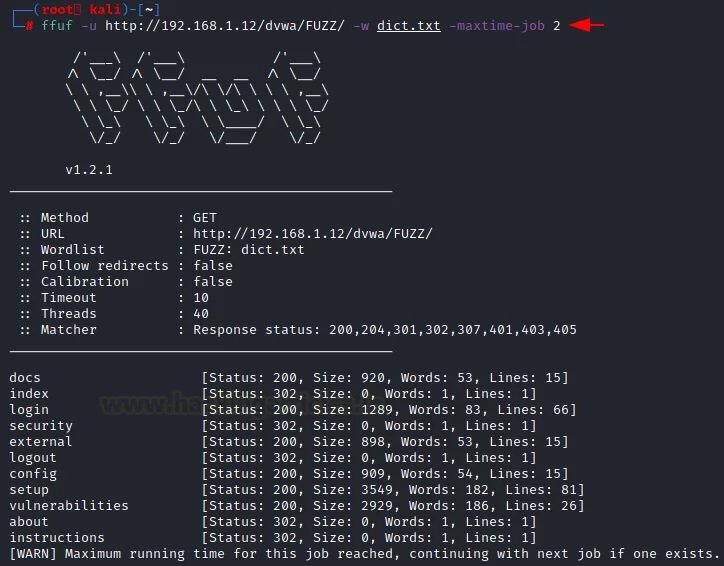
Using the “-max time-job” parameter, the user can set a time limit for a specific job. With this command, you can limit the time it takes to complete a task or query.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -maxtime-job 2 |
Using the “-p” parameter, the user will add a slight delay for each request offered by the attack. According to the experts of the Cyber Security 360 course, with this feature the consultation becomes more efficient and provides clearer results.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -p 1 |
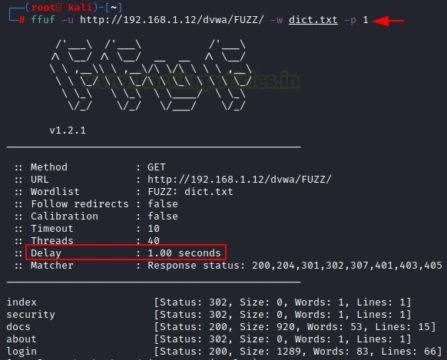
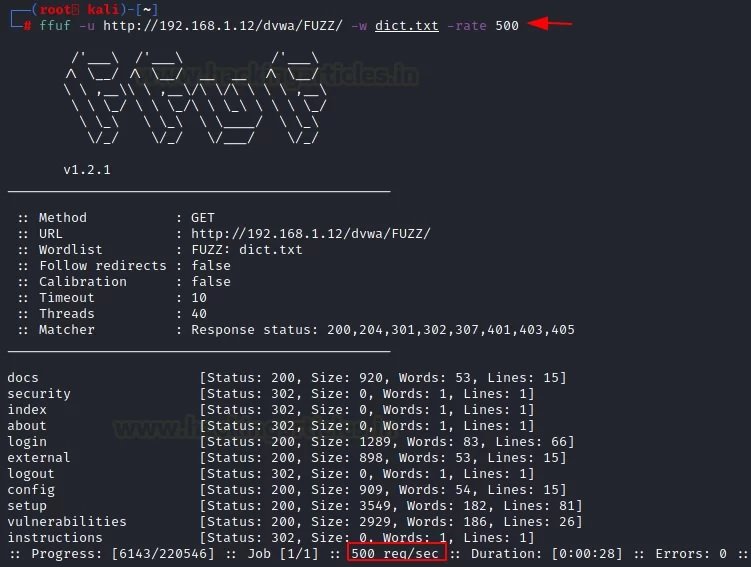
We can select the request speed you need for each of the attacks using the “-rate” parameter. For example, we can create one request per second according to the desired attack.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -rate 500 |
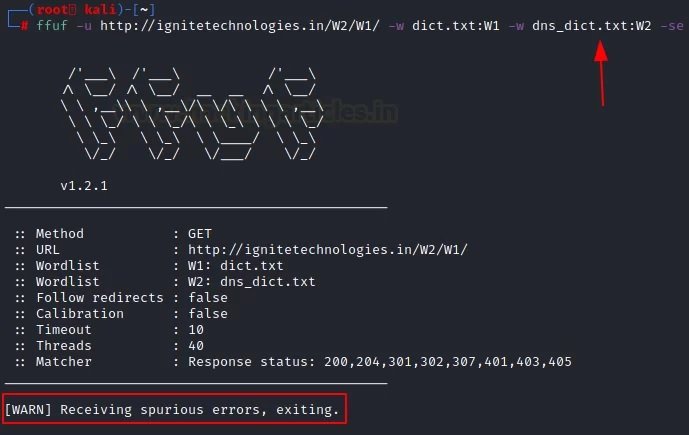
There are three parameters that support the error function. The first parameter is “-se”, a “false error” that says whether the next request is genuine or not. The second “-sf” parameter will stop the attack when more than 95% of the requests are counted as an error. The third parameter is “-sa”, a combination of the above parameters.
In the example shown below, we will use the “-se” parameter:
| 1 | Ffuf -u http://ignitetechnologies.in/W2/W1/ -w dict.txt:W1 -w dns_dict.txt:W2 –se |
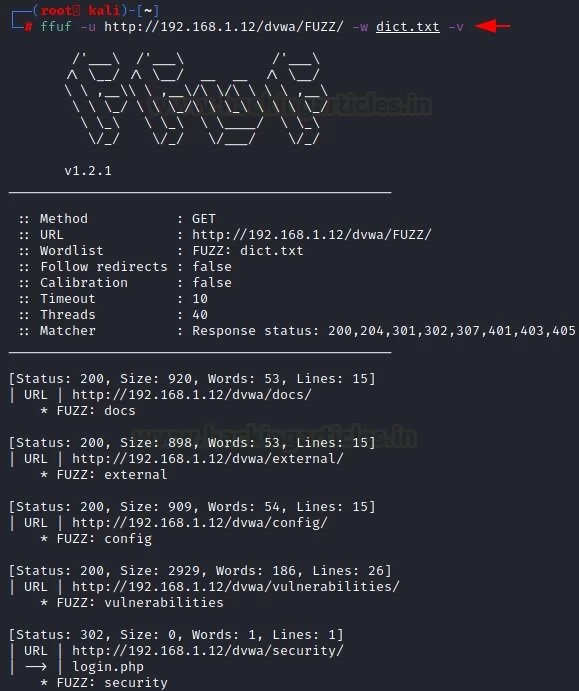
Verbose Mode is a feature used in many operating systems that provide additional information about what the computer does and what drivers and applications it loads when initialized. In programming, this mode provides accurate output for debugging purposes, making it easier to debug the program itself. To access this mode, the “-v” parameter is applied.
| 1 | Ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt –v |
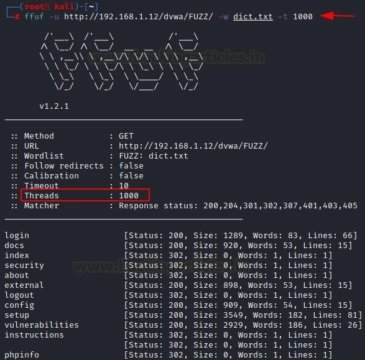
The “-t” parameter is used to speed up or slow down the process. By default, it is set to 40. If you want to speed up the process, you need to increase its value.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -t 1000 |
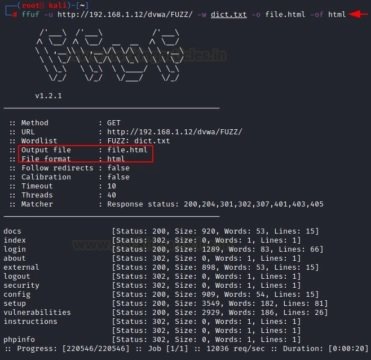
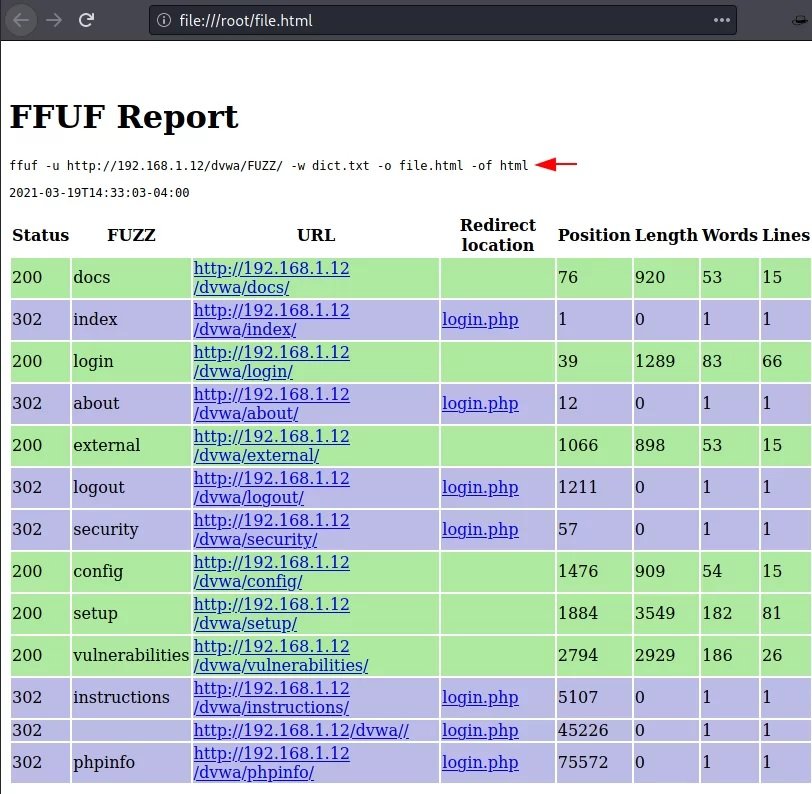
We may save the results of attacks carried out in order to keep records, improve readability and find possible links. Enter the “-o” parameter to save the output, but you must specify its format using the “-of” parameter.
Once the attack is complete, it should be checked whether the file with the output data corresponds to this format or not, mention the experts of the Cyber Security 360 course. As you can see, the file itself refers to HTML.
Similarly, we can create CSV files using the “-of” parameter, where csv are comma-separated values. For example:
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -o file.html -of html |
When the attack is complete, you need to check whether the file with the output data corresponds to this format or not. As you can see, the file itself belongs to the CSV.
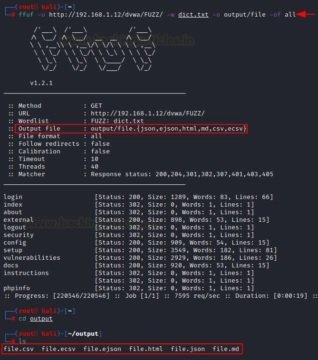
Similarly, if you want to recover data in all formats, use the “-of all” parameter. For example, it can be json, ejson, html, md, csv, ecsv.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -o output/file -of all |
Now, once the attack is complete, you need to check all the files. We can see that they were saved in various formats.
Sometimes the fuzzing process requires details such as an HTTP request, cookies, and an HTTP header, mention the experts of the Cyber Security 360 course.
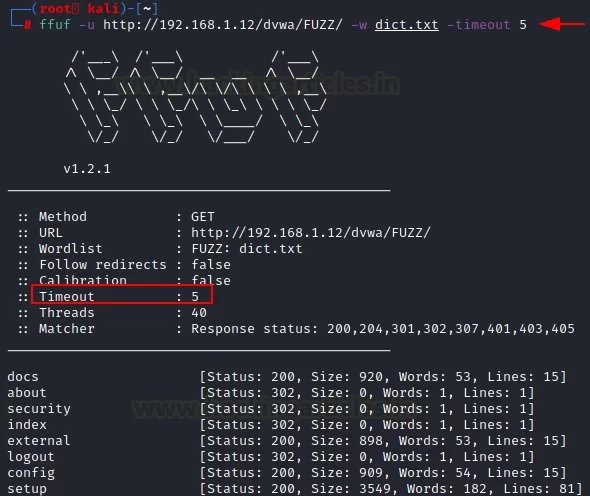
This feature acts as a deadline for the event to complete. The “-timeout” parameter helps to activate this option.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -timeout 5 |
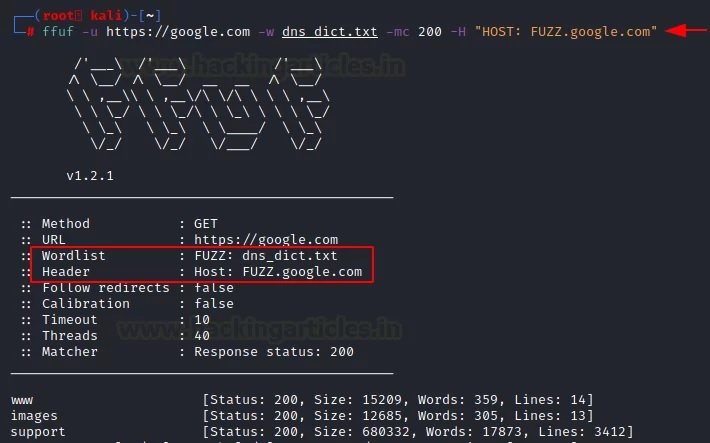
If you want to fuzz out subdomains, you can use the “-H” parameter along with the word list of the domain name.
| 1 | Ffuf -u https://google.com -w dns_dict.txt -mc 200 -H “HOST: FUZZ.google.com” |
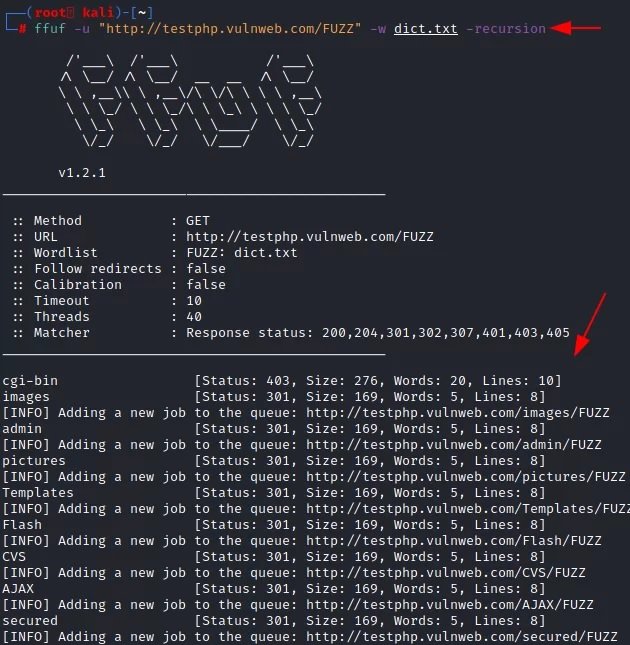
According to the experts of the Cyber Security 360 course, this is a mechanism for reusing objects; if a program requires the user to access a function within another function, this is called a recursive call to the function. Using the “-recursion” parameter, the user can implement this functionality in their attacks.
| 1 | ffuf -u "http://testphp.vulnweb.com/FUZZ/" -dict.txt –recursion |
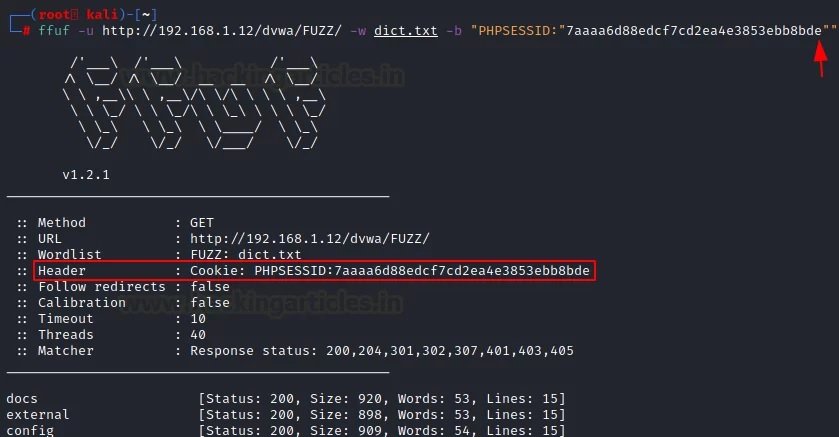
There are times when fuzzing is not effective on a site where authentication is required. In these cases, we may use the “-b” parameter to use session cookies.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -b "PHPSESSID:"7aaaa6d88edcf7cd2ea4e3853ebb8bde"" |
There are speed limits when using the Intruder feature in the free version of Burp (Community Edition). The attack slowed down a lot, and each new “order” slowed it down even more.
In this case, the user uses the Burp Suite proxy server to get the results and evaluate them. First, you need to install the localhost proxy server on port number 8080.
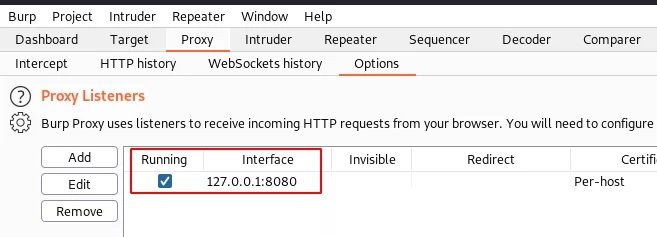
Now let’s use “-replay-proxy”, which helps to get the local proxy server of the host, installed in the previous step on port number 8080.
| 1 | ffuf -u http://192.168.1.12/dvwa/FUZZ/ -w dict.txt -replay-proxy http://127.0.0.1:8080 -v -mc 200 |
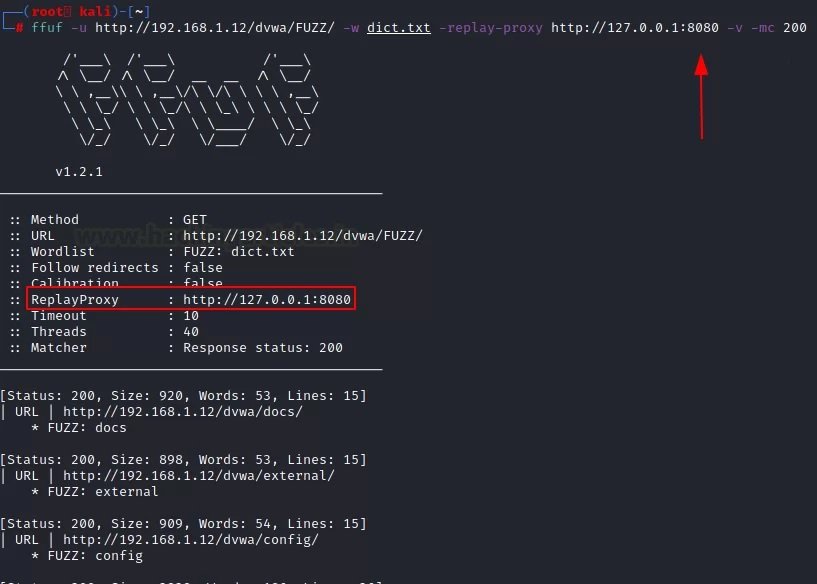
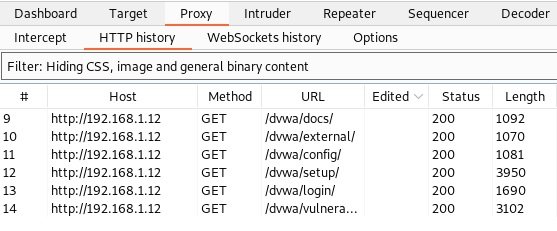
This attack will show results on two platforms. The first platform is in the Kali Linux terminal and the second is in the “HTTP history” tab in Burp Suite. With the help of various methods, you will be able to better understand the target and analyze the results of the attack.
It is common to compare ffuf with other tools such as dirb or dirbuster. While ffuf can be used for deploying brute-force attacks, its real appeal lies in simplicity.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, information technologies, and to know more details about the Cyber Security 360 course

Jan 30 2023
The MAC address is (should be) unique to each network interface. By the way, if the device has several network interfaces, then each of them has its own MAC address. For example, laptops have at least two network interfaces: wired and Wi-Fi – each of them has an MAC address. Desktop computers are usually the same. When we talk about “changing MAC addresses”, we need to understand that there are several of these addresses. By the way, each port has its own unique MAC address, if the device supports wireless networks, then each wireless interface (2.4 GHz and 5 GHz) also has its own MAC address.
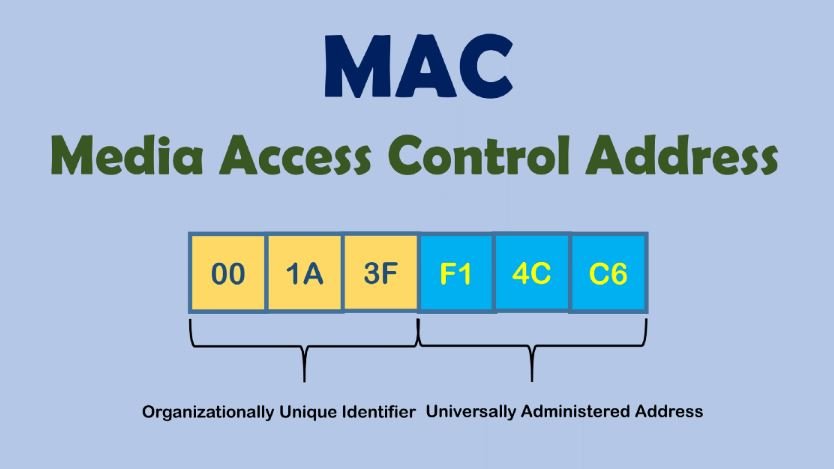
So, since the MAC address must be unique, it allows you to uniquely identify the network device. And since this network device is part of your computer, this allows you to uniquely identify your computer. Moreover, the MAC address (also called a hardware, physical address) does not change when the operating system changes.
In short, the replacement of the MAC address is needed so that it is not possible to track and identify the device by the MAC address. But there is a more important reason (than paranoia) to learn about MAC addresses and about methods from substitution, or prohibiting changes in your system. Based on MAC addresses, user identification can be performed when connected via the Intercepting Portal. A few words about the Intercepting Portal. Captive Portal). This is a way to force the user to comply with certain conditions for providing Internet access. You can most often encounter examples of Intercepting Portals in public places that provide Internet access services via Wi-Fi to an indefinite circle of people, but who want to identify the user and / or allow access only to persons with credentials. For example, at the airport you may need to confirm your phone number via SMS to access the free Wi-Fi network. The hotel will provide you with a username and password for accessing the Internet via Wi-Fi – this ensures that only hotel customers can use Wi-Fi services.
Due to the features of the Intercepting Portal, user identification is based on MAC addresses. And starting with NetworkManager 1.4.0 (a popular program for managing network connections on Linux), an automatic MAC-address spoofing is now present. And in case of incorrect settings, you may encounter an Internet access problem running through the Intercepting Portal. There are also problems with customized filtering by MAC on the router.
Well, for pentesting experts , of course, there are reasons to change the MAC address: for example, to pretend to be another user, and take advantage of its open access to the magical world of the Internet, or to increase anonymity.
Who can see my MAC address?
The MAC address is used to transfer data on a local network. That is, it is not transmitted when connecting to websites and when accessing the global network. Although there are exceptions: some vulnerabilities allow a person who is not on your local network to find out your MAC address.
If you connect to the router via the local network, then the router knows your MAC address, but if you open the site on the Internet, the site owner cannot find out your MAC address.
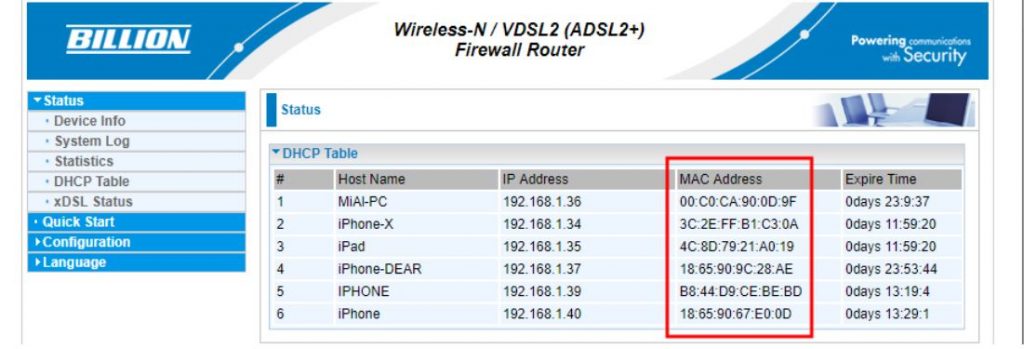
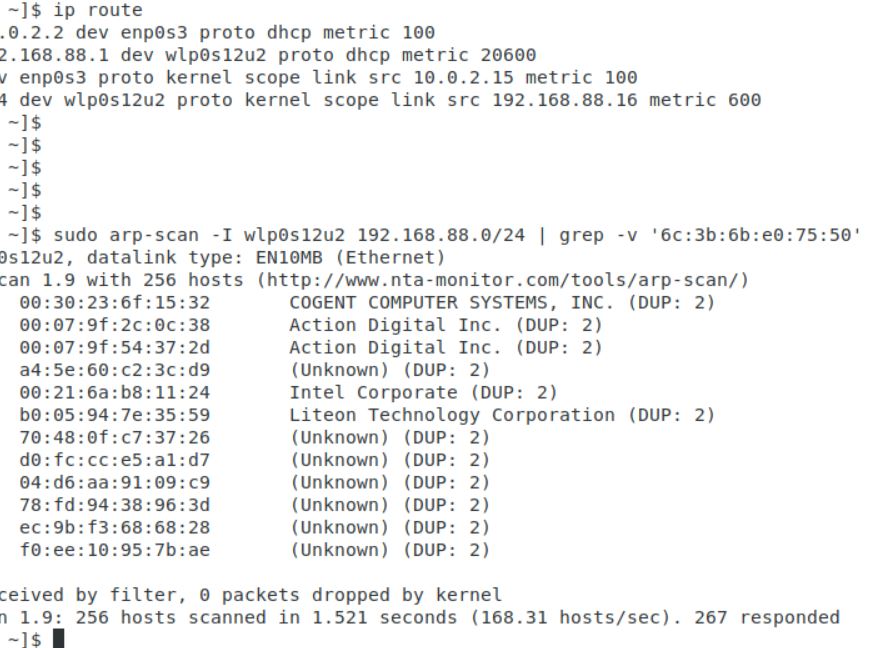
All devices located on the local network can see each other’s MAC addresses (there are many scanners that can get this data). An example of a local network scan made using arp-scan. A slightly different situation with wireless network interfaces. If you are connected to an access point (router), then all the rules of the local network work: the router and other devices can find out your MAC address. But also any person who is within the reach of your Wi-Fi signal (from the phone, laptop) can find out your MAC address.
NetworkManager may reassign MAC installed by other programs
Starting with NetworkManager 1.4.0, this program supports MAC spoofing, and has many different options.
So that we can understand them, we need to understand some concepts
First, network adapters are :
For each group, MAC rules are customized separately.
Secondly, a wireless adapter can be in two states:
For wired interface (installed by property ethernet.cloned-mac-address) and the wireless interface in the connection state (installed by the property wifi.cloned-mac-address) the following values are available (regimes):
If you are trying to change the MAC in other ways and you are failing, it is entirely possible that NetworkManager, which changes the MAC in its own rules, is to blame. Since most Linux distributions with a NetworkManager graphical interface are installed and running by default, to solve your problem, you must first understand how NetworkManager works and by what rules.
NetworkManager settings, including settings related to MAC, can be done in a file /etc/NetworkManager/NetworkManager.conf or adding an additional file with the extension . . . .conf to the directory /etc/NetworkManager/conf.d
The second option is highly recommended, since when updating NetworkManager usually replaces the main one . . . . . . . . . .conf file and if you made changes to /etc/NetworkManager/NetworkManager.conf, then the settings you made will be overwritten.
If you want the MAC address to be replaced with each connection, but the same MAC is used in the connection to the same network, then the file /etc/NetworkManager/conf.d/mac.conf:
| 1 | sudo gedit /etc/NetworkManager/conf.d/mac.conf |
Add lines :
| 123 | [connection]ethernet.cloned-mac-address=stablewifi.cloned-mac-address=stable |
Lines with ethernet.cloned-mac-address & wifi.cloned-mac-address can be added individually or together.
Check the current values :
| 1 | ip link |
Restart the service :
| 1 | sudo systemctl restart NetworkManager |
We will make connections to wired and wireless networks. Now check the values of MAC again
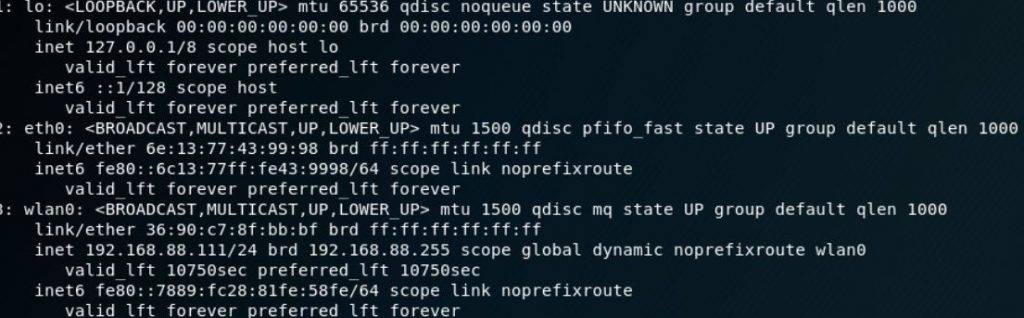
As you can see, MAC is replaced for both the wired and wireless interfaces.
As already mentioned, the same addresses will be generated for the same networks, if you want different MACs each time even for the same networks, then the lines should look like this:
| 123 | [connection]ethernet.cloned-mac-address=randomwifi.cloned-mac-address=random |
Ubuntu and Linux Mint use NetworkManager versions that support automatic MAC configuration. However, if you connect a Wi-Fi card to Ubuntu or Linux Mint, you will see a real MAC. This is due to the fact that in the file /etc/NetworkManager/NetworkManager.conf indicated not to spoof :
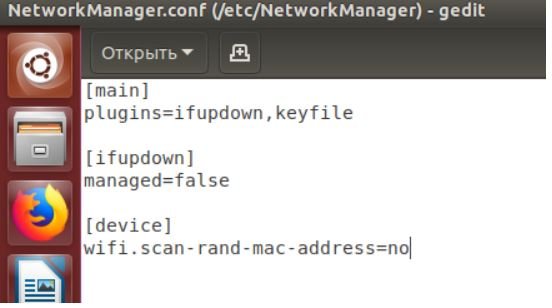
To change this, open the file :
| 1 | sudo gedit /etc/NetworkManager/NetworkManager.conf |
And delete the lines :
| 12 | [device]wifi.scan-rand-mac-address=no |
or comment on them to make it happen :
| 12 | #[device]#wifi.scan-rand-mac-address=no |
or change no on yes:
| 12 | [device]wifi.scan-rand-mac-address=yes |
And restart NetworkManager :
| 1 | sudo systemctl restart NetworkManager |
Similarly, you can add lines to replace MAC (these settings create a new address for each connection, but when connecting to the same networks, the same address is used):
| 123 | [connection]ethernet.cloned-mac-address=stablewifi.cloned-mac-address=stable |
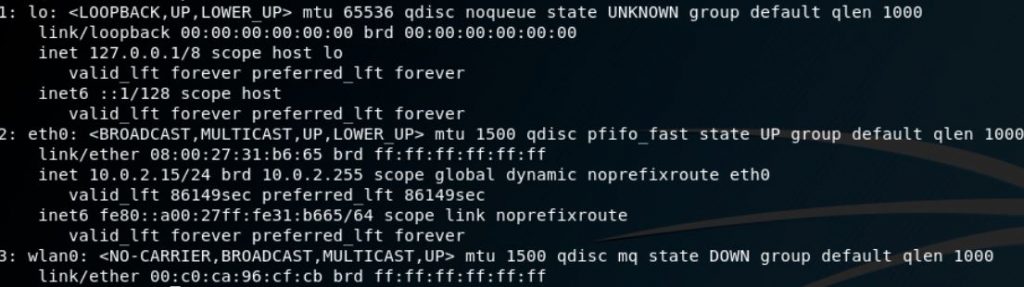
We will use the program ip, which is included in the package iproute2.
Let’s start by checking the current MAC address with the command :
| 1 | ip link show interface_name |
Where Interface_name – This is the name of a particular network interface that you want to see. If you do not know the name, or want to see all the interfaces, then the command can be started like this :
| 1 | ip link show |
At the moment, we are interested in the part that follows after link / ether“and represents a 6-byte number. It will look something like this :
| 1 | link/ether 00:c0:ca:96:cf:cb |
The first step for spoofing MAC addresses is to transfer the interface to a state down. This is done by the team
| 1 | sudo ip link set dev interface_name down |
Where Interface_name replaces the real name. In my case, this wlan0, then the real team looks like this:
| 1 | sudo ip link set dev wlan0 down |
Next, we go directly to the MAC spoofing. You can use any hexadecimal value, but some networks may be configured not to assign IP addresses to customers whose MAC address does not match any known vendor (producer). In these cases, so that you can successfully connect to the network, use the MAC prefix of any real vendor (first three bytes) and use arbitrary values for the next three bytes.
To change the MAC, we need to run the command :
| 1 | sudo ip link set dev interface_name address XX:XX:XX:XX:XX:XX |
Where XX: XX: XX: XX: XX: XX – This is the desired new MAC .
For example, I want to set the hardware address EC: 9B: F3: 68: 68: 28 for my adapter, then the team looks like this:
| 1 | sudo ip link set dev wlan0 address EC:9B:F3:68:68:28 |
In the last step, we return the interface to the state up. This can be done by a team of the form :
| 1 | sudo ip link set dev interface_name up |
For my system, a real team:
| 1 | sudo ip link set dev wlan0 up |
If you want to check if the MAC is really changed, just run the command again:
| 1 | ip link show interface_name |
Value after “link / ether“should be the one you installed.
Another method uses macchanger (also known as the GNU MAC Changer). This program offers various functions, such as changing the address so that it matches a particular manufacturer, or its complete randomization.
Set macchanger – it is usually present in official repositories, and in Kali Linux it is installed by default.
At the time of the change of the MAC, the device should not be used (be connected in any way, or have status up). To transfer the interface to a state down:
| 1 | sudo ip link set dev interface_name down |
For spoofing, you need to specify the name of the interface, and replace in each next command wlan0 in the name of the interface that you want to change the MAC.
To find out the values of MAC, execute the command with the option -s:
| 1 | sudo macchanger -s wlan0 |
Something like:
| 12 | Current MAC: 00:c0:ca:96:cf:cb (ALFA, INC.)Permanent MAC: 00:c0:ca:96:cf:cb (ALFA, INC.) |
The “Current MAC” line means the address at the moment, and “Permanent MAC” means a constant (real) address.
For spoofing the MAC address to a completely arbitrary address (option -r):
| 1 | sudo macchanger -r wlan0 |
About the following will be displayed :
| 123 | Current MAC: 00:c0:ca:96:cf:cb (ALFA, INC.)Permanent MAC: 00:c0:ca:96:cf:cb (ALFA, INC.)New MAC: be:f7:5a:e7:12:c2 (unknown) |
The first two lines are already explained, the line “New MAC” means a new address.
For randomization, only bytes that determine the uniqueness of the device, the current MAC address (i.e.e. if you check the MAC address, it will register as from the same vendor) run the command (option -e):
| 1 | sudo macchanger -e wlan0 |
To set the MAC address to a specific value, execute (option -m):
| 1 | sudo macchanger -m XX:XX:XX:XX:XX:XX wlan0 |
Here XX: XX: XX: XX: XX: XX – This is the MAC you want to change to.
Finally, to return the MAC address to the original, constant value prescribed in the iron (option -p):
| 1 | sudo macchanger -p wlan0 |
NetworkManager currently provides a wealth of MAC spoofing capabilities, including a change to a random address, or to a specific one. A feature of NetworkManager is the separation of “scanning” and “connected” modes, i.e. you may not see that the settings made have already entered into force until you connect to any network.
If after the change of MAC you have problems with connecting (you cannot connect to networks – wired or wireless), this means that there is a ban on connecting with MAC from an unknown vendor (producer). In this case, you need to use the first three octets (bytes) of any real vendor, the remaining three octets can be arbitrary says pentesting experts.
The Art of Mac Malware: The Guide to Analyzing Malicious Software