How can you tell what needs fixing??
InfoSec and Compliance – With 20 years of blogging experience, DISC InfoSec blog is dedicated to providing trusted insights and practical solutions for professionals and organizations navigating the evolving cybersecurity landscape. From cutting-edge threats to compliance strategies, this blog is your reliable resource for staying informed and secure. Dive into the content, connect with the community, and elevate your InfoSec expertise!
Nov 02 2022
33N Ventures is fundraising €150 million for investing in cybersecurity and infrastructure software companies across Europe, Israel, and the US. The fund will mostly target investments at Series A and B, with an average ticket size of around €10 million, and has an investment capacity of €20 million already committed by Alantra and its strategic partners.
Co-founders and managing partners Carlos Alberto Silva and Carlos Moreira da Silva have made more than 20 investments in cybersecurity and infrastructure software over the past 10 years, across Europe, Israel and the US – including most notably Arctic Wolf.
In this Help Net Security interview, they discuss the cybersecurity investment landscape in Europe, the strategies for finding the right companies, and more.
Carlos Alberto Silva: There’s no doubt that the US and Israeli startup ecosystems get more attention when it comes to cybersecurity. But that’s not to say there haven’t been success stories in Europe. Take IriusRisk, for example: the automated threat modeling platform raised a $28.7M Series B round just a few weeks ago.
By rights, Europe should be a world leader in this space. Talent is abundant here, and there is a very large addressable market. The challenge for companies in Europe is that, unlike their peers in the US and Israel, they often don’t get the specialized support they need to compete.
While there are a few specialized funds in Europe, most focus naturally only on one country or region and tend to invest in very early-stage companies. As a result, most entrepreneurs face the choice of working with a US investor (that lacks on-the-ground local knowledge) or working with a generalist fund that may not be able to open the right doors for them.
That’s why we’ve decided to create a fund with a truly pan-European focus. There’s such a large opportunity here for firms that are underserved by the current market. We’ll still be investing in some companies in the US and Israel – simply put, there are some amazing opportunities that we just don’t want to miss out on – but we’re most excited about capitalising on this relatively untapped opportunity in Europe.
Carlos Alberto Silva: Given that we only launched the fund last week, we’ve not run into too many challenges yet! That being said, of course, the economic climate is not the best. This is a challenge that every venture capital fund and company must face.
Cybersecurity as a whole is also well insulated from the economic downturn. That’s because strong cybersecurity is not a ‘nice-to-have’ – but critical. That’s not going to change – from digital transformation to national security, cyber will continue being a top priority for governments, institutions, companies, and investors across the globe, and the market is expected to reach $162 billion in 2022, with robust annual double-digit growth forecast for the coming years – and so the companies we’ll be looking at have some in-built resilience.
Carlos Moreira da Silva: This is not generally something we struggle with. This is probably because we follow a thesis-driven approach that means we spend a lot of time looking at which spaces we want to cover before making any investment decisions.
Of course, we stay up to date with the industry, look at all publicly available sources, and attend the most relevant cybersecurity events across Europe, Israel, and the US. This is all fairly common sense.
But we do rely heavily on our proprietary network of close VCs and advisors. Our network is always totally invaluable when we are looking to identify the best leads for future investments. Our strategic advisors – including leading entrepreneurs, experts, and cybersecurity decision-makers such Brian NeSmith (Arctic Wolf), Eyal Hayardeny (Reblaze), Nuno Sebastião (Feedzai), and Pierre Polette (Hackuity) – all founders of companies we’ve invested in in the past – possess an incredible depth and breadth of sector-specific knowledge and experience that, added to our own, really helps us identify and support the founders and companies with the biggest breakthrough and scaling potential.
We spend a long time talking to prospective investee companies, ideally as early in their journey as possible, and working out where we can help them. If we can make an introduction to a potential customer, for example, we will do so even before we have made any investment. We’ve worked hard to build a reputation in the industry for being supportive of the whole industry – that’s really important to us.
Carlos Alberto Silva: For most first-time funds the process of identifying the right companies to invest in across such a large geographic area would be difficult. But our team has been together for many years now. We may be a first-time fund, but we’re far from a first-time team.
We know this space well and we have a strong network that reaches across the US, Europe, and Israel. In fact, much of the research you refer to has in effect already been done. We already have a list of companies that we’re interested in, and in many cases have already started the conversation.
We want to back visionary companies in emerging sectors. We want to invest in those who are the very first or one of the very first to solve a particular problem. In our view, jumping on bandwagons or entering already saturated markets will inevitably lead to meagre returns. Get in on the ground floor and you’ve got a lot more room to grow into.
Carlos Moreira da Silva: Beyond the obvious – how much are they willing to invest – there are a couple of really important things for founders to look at. Firstly, look at their track record. Cybersecurity is a space where deep technical knowledge is really important. Think of it this way: if you have to explain what your company does through metaphors and hand-holding, then they probably aren’t going to be much help beyond providing cash stimulus.
The second thing to look at is their network. Well-connected investors with the right contacts in cybersecurity will prove invaluable. Most venture capital investors will have a long list of contacts. You can pick that up by going to the right events and spending enough time in the space. But the investors that will provide you with real benefit are those who have a long list of friends – with deep and genuine relationships. The right introduction can be game-changing for a company, so it’s vital your investor’s network is robust.
Carlos Moreira da Silva: It may sound obvious, but in our experience, the most important thing for building rapport is having a solid understanding of the business. It is important to be there for the founders during the good times, but especially during the challenging times, when they really need that extra help. Of course, you must understand how the company’s key product or service works.
But beyond that, you must understand everything from the pain points of their customers to the market for talent in their sector to the opportunities for growth. This is not stuff you can pick up overnight, and entrepreneurs are good at picking those with genuine knowledge out from the blaggers.
And, in our case, we can share our global perspective regarding the wider market environment. You can provide an enormous amount of value here.
We also think it helps that we’ve been in their position before. We’re not just investors, we’ve held senior executive roles in cybersecurity companies and effectively built them from the ground up. So, we understand the nuances of the day-to-day running of a business, and that helps us build a foundation of trust – which really is essential to a successful relationship.

Nov 01 2022
There is an unofficial patch from 0patch for a Zero-Day flaw in Microsoft Windows that allows bypassing the MotW (Mark-of-the-Web) protections that are built into the operating system and at moment it’s actively exploited.
By utilizing files signed with malformed signatures, this zero-day flaw is able to bypass MotW protections. Various legacy Windows versions as well as all versions that are supported by Microsoft are affected by the issue.
It has been determined by cybersecurity analysts that the Magniber ransomware was being installed on victims’ devices with the help of stand-alone JavaScript files by threat actors.
0patch released this unofficial security patch to fix this flaw since it’s a critical zero-day vulnerability and is exploited by threat actors vigorously in the wild.
Why this patch has been tagged as “Unofficial”?
This patch is tagged as unofficial due to its release source, in short, this patch has not been released by Microsoft itself.
But, until the release of any official patch from Microsoft, users can use this security patch to keep their systems protected against threat actors exploiting this zero-day flaw.
Due to this zero-day vulnerability, multiple Windows versions are affected and here below we have mentioned all the affected versions of Windows that are eligible for the free micropatches:-
The installation process for this micropatch will require an account on the 0patch website, and it can be created for free. Once done, you’ll need to download its agent for your Windows device which will automatically install this patch.

Oct 31 2022
During recent research, Microsoft has discovered evidence of a complex interconnected malware ecosystem that is associated with the Raspberry Robin worm.
With other malware families, there are several root links to the Raspberry Robin worm were identified. Even security experts have detected that it uses alternate infection tactics as well.
Infections like these lead to a variety of complications and here below we have listed them:-
In the past 30 days, on more than 1000 organizations’ 3000 devices, the Raspberry Robin worm has initiated payload alerts. There have been instances where the Raspberry Robin worm has been installed on the victims’ systems with malware called FakeUpdates.
Raspberry Worm is also known as QNAP Worm, as for command-and-control, it uses the compromised QNAP storage servers. Through infected USB drives containing malicious. LNK files, Raspberry Robin spreads to other devices.
The worm will spawn a msiexec process using cmd[.]exe as soon as a USB device is attached.
In order to communicate with its C2 servers, the malware communicates with compromised Windows devices.
Microsoft Security Threat Intelligence Center (MSTIC) observed Raspberry Robin in October 2022, and it’s being used by DEV-0950, which is another actor who was also involved in the post-compromise activity.
As a result of the DEV-0950 activity, the Cobalt Strike was compromised through hands-on keyboard activity. The majority of the victims of DEV-0950 are traditionally acquired via phishing scams.
However, the operators of DEV-0950 have moved to use Raspberry Robin instead of the traditional method. The advantage of this approach is that the payloads can be delivered to existing infections and the campaigns can move to the stage of ransomware more quickly.
To mitigate the impact of this threat, it is also possible for defenders to apply the following mitigation measures:-

Oct 30 2022
In this Help Net Security video, Dmitry Bestuzhev, Most Distinguished Threat Researcher at BlackBerry, talks about some of the most interesting tactics, techniques, and procedures employed by cybercriminals in recent months.
These are:
Oct 27 2022
A new version of Wireshark has been released recently by the Wireshark Team, it’s Wireshark 4.0.1, which contains several enhancements, new updates, and bug fixes.
Wireshark is one of the most widely used open-source free software packet analyzers that are currently available on the market, and it is available in a variety of options for different platforms.
There are many people who use Wireshark packet analyzers for the analysis of packets, not just network administrators only. As security analysts also use Wireshark packet analyzers for packet analysis purposes.
Several organizations make use of this tool to manage and monitor all the activities of their business operations on a regular basis.
Wireshark recently released its Wireshark 4.0.0 and the current Wireshark 4.0.1 is a quick update from the previous one.
For all the major platforms or operating systems, the Wireshark 4.0.1 packet analyzer is available and here below we have mentioned them:-
There are several primary purposes for using Wireshark as a network protocol analyzer, including:-
Wireshark 4.0 and later do not have any official 32-bit Windows packages that you can install on your computer. Qt 5.12.2 is now the standard version that ships with Windows installers. The previous version of these packages was Qt 6.2.3, which was shipped by default.
This release removes the experimental syntax for the display filter used in Wireshark 4.0.0 that allowed literals to be displayed just using angle brackets <…>. You can use the colon prefix instead while dealing with byte arrays.

Oct 22 2022
As part of the criminal case against a former student of the University of Puerto Rico (UPR), a judge in Puerto Rico sentenced him to serve 13 months in federal prison.
The former student, Iván Santell-Velázquez (aka Slay3r_r00t) was accused of hacking over a dozen of the university’s female classmates’ email and Snapchat accounts.
On July 13, Ivan pled guilty to being a cyberstalker, admitting that he had targeted over 100 students in his online campaign. He also engaged in other schemes to steal information such as using spoofing and phishing.
He has been accused of harassing women and in some cases, he has published pictures that he has stolen from them in their nudist states between 2019 and 2021.
Apart from hacking student email accounts, he also managed to get access to multiple university email accounts by spoofing and phishing attempts through which he gathered personal information.
The appellant, Iván Santell-Velázquez targeted 15 female students in total at the University of Puerto Rico. A victim of cyberstalking may experience a significant amount of emotional distress as a result of it.
Here’s what U.S. Attorney Muldrow stated:-
“The prosecution of cyber criminals is a top priority in the Justice Department. Cybercrimes not only cause financial losses to corporate victims but also result in financial and psychological harm to vulnerable victims, oftentimes children or the elderly. This conduct will not be tolerated.”
“This case also demonstrates the importance of safeguarding personal information and passwords, and the care we must take when responding to suspicious e-mails and text messages.”
As a result of his illicit crimes, Iván Santell-Velázquez was sentenced to 13 months of rigorous imprisonment along with 2 years of supervised release for cyberstalking by Silvia Carreño Coll, the U.S. District Court Judge.

Cyber Crime
Oct 21 2022
As data breaches’ financial and reputational costs continue to reach new heights, cybersecurity should be on top of mind for leadership across every industry.
Recent Proofpoint research found that 65% of board members believe their organization is at risk of material cyber attack in the next 12 months. Worryingly, 47% feel their organization is unprepared to cope with a targeted attack.
In this Help Net Security interview, Chris Konrad, Area Vice President of Security, Global Accounts at World Wide Technology, offers advice to CISOs that are increasingly under pressure, discusses using a security maturity model, discusses interesting security technologies, and more.

CISOs can no longer focus strictly on developing technical capabilities and protecting their organizations. Executives and boards are looking to CISOs to make investments that drive growth with a holistic security framework.
First, every CISO needs to know what their board’s mission and vision are, as well as what their risk appetite and tolerance are. You can’t secure what you can’t see. No security program can fully eliminate risk or human error, but a mature approach to cybersecurity can mitigate the risks that pose the most danger to organizational objectives and success.
The next step is conducting a comprehensive cybersecurity program assessment to know at what level of risk you are operating. This type of analysis provides rich insights that can be actioned to increase your security program maturity. This analysis also helps to maximize the use of people, processes and technology to reduce risk and increase efficiencies.
Risk management should be a C-suite priority because it is one of the single most important determinants of business value realization. Risk management is the system by which an organization’s portfolio is directed and controlled.
A security maturity model can help CISOs measure, communicate and visualize improvements and investments in the security program. There are many different maturity models available to help you measure a security program. One I like is the Capability Maturity Model Integration (CMMI), a process improvement maturity model for the development of products and services, developed and published by the Software Engineering Institute of Carnegie Mellon University in Pittsburgh.
Using CMMI in combination with the National Institute of Standards and Technology (NIST), an organization can have one axis measuring people, process and technology and the other axis measuring maturity from nonexistent capability to optimized.
Of course, there is not a one-size-fits-all approach – so security teams must also work with the business to understand what is key to success, and ultimately, growth.
Most organizations are doing some form of tools rationalization or platform consolidation to get a better handle on their investments and reduce overlapping capability and spend. However, there are a few technologies that have caught my eye.
For me, I love seeing how AIOps can help organizations detect, assess and eliminate potential security vulnerabilities — before they are exploited by adversaries or those acting in bad faith. AIOps is starting to transform the way organizations tackle the complex cybersecurity ecosystem.
Innovative organizations, like Cribl, can receive machine data from any source and cleanse and enrich your data before routing it to any logging or SIEM platform, like Splunk, to reduce the total amount of data that needs to be managed. CrowdStrike is enhancing observability through modern log management with LogScale, which is built to ingest and retain streaming data as quickly as it arrives, regardless of volume. Alerts, scripts and dashboards are updated in real-time, and Live Tail and retained data searches have virtually no latency.
Among the biggest challenges are that our adversaries are getting smarter, and they are leveraging much of the same technology that we use to defend ourselves. There is also a wider, and perhaps more concerning, issue around the shortage of skilled resources at a global level. Cybersecurity is one of the most important industries to safeguard our democratic value but more often than not, it’s seen as an overly technical, and therefore, not attractive career. We need to be shining the light on more routes into cyber roles and also accelerating diversity.
One area that’s often overlooked is identifying people within your organization and up-leveling them. Of course, those with earned experience have the hard skills to succeed, but I think an enthusiasm and drive to achieve is just as important. And by prioritizing STEM in early education, we further raise awareness of the field.
World Wide Technology employs thousands of professionals in the STEM fields across the globe and understands the urgency of supporting future tech leaders. WWT annually hosts its STEM Student Forum, an initiative dedicated to educating high school students on the importance of STEM disciplines and the opportunities they present, while also creating positive change in the St. Louis metropolitan area, where WWT’s global headquarters is located.
Oct 20 2022
At its Dash 2022 conference, Datadog shared a report that found the primary security challenge organizations encounter in the Amazon Web Services (AWS) cloud is lax management of credentials.
Based on data collected from more than 600 organizations that rely on the Datadog platform to monitor their AWS cloud computing environments, the report also noted the complexity of the AWS identity and access management (IAM) service may lead organizations to publicly expose sensitive resources by accident.
Access keys are a static type of credential that do not expire. The Datadog report found 75% of AWS IAM users have an active access key that’s older than 90 days, while 25% have an active access key that’s older than one year and hasn’t been used in the past 30 days.
A total of 40% have also not used their credentials in the past 90 days, while 40% of organizations have at least one IAM user that has AWS Console access without multifactor authentication (MFA) enabled.
Andrew Krug, lead technical evangelist for security at Datadog, said managing cloud credentials is challenging because organizations often lack any offboarding processes to limit access when, for example, an employee leaves the company. As a result, cybercriminals that steal credentials are then able to easily gain access to cloud environments simply because organizations don’t rotate access keys, he added.
Datadog also noted that, by default, AWS provisions users at a root level that provides them with unlimited administrative permissions. Datadog found approximately 10% of organizations have an active root user access key. Some of these keys are up to 13 years old. A quarter of organizations (25%) had someone use root user credentials in the 30 days prior to the Datadog study. There may be a legitimate need for that level of access, but Krug noted the best practice is to employ least-privilege access whenever possible.
Other issues surfaced by Datadog pertain to how organizations configure cross-account access by using a resource-based IAM policy attached to the resource itself. The report found 18% of organizations that use the Amazon Simple Queue Service, for example, have at least one publicly exposed queue that enables anyone to receive or publish messages to those queues. More than a third of organizations that use the AWS S3 cloud storage service have at least one publicly exposed bucket.
Krug said it needs to be less complex to create secure IAM policies that grant least-privilege, granular permissions. It’s simply too easy to make a mistake, he added.
A fourth cloud security issue that’s widely overlooked is continued reliance on the first version of a EC2 Instance Metadata Service (IMDS) service that has known vulnerabilities. AWS has made available a more secure version, but Datadog found the vast majority of EC2 instances (93%) are not enforcing the usage of IMDSv2. Overall, 95% of organizations that use EC2 have at least one vulnerable instance. The second version of IMDS should be the default configuration, said Krug.
Finally, Datadog found at least 41% of organizations have adopted a multi-account strategy in AWS, with 6% of organizations using more than 10 AWS accounts. Datadog recommended centralizing accounts to make it easier to monitor who has gained access to a cloud computing environment.
Despite these issues, cloud platforms are still fundamentally more secure than on-premises IT environments. However, it’s also clear there is plenty of opportunity for mistakes to be made.

Oct 20 2022
Third-party risk assessments are often described as time-consuming, repetitive, overwhelming, and outdated. Think about it: organizations, on average, have over 5,000 third parties, meaning they may feel the need to conduct over 5,000 risk assessments. In the old school method, that’s 5,000 redundant questionnaires. 5,000 long-winded Excel sheets. No wonder they feel this way.
The reason why risk assessments have become so dreaded is that it has always been a process of individual inspection and evaluation. For perspective, that’s roughly 14 risk assessments completed per day in the span of one year. How can we expect security, risk, and procurement professionals to get any other work done with this type of task on their plate? With the state of today’s threat landscape, wouldn’t you rather your security team be focused on actual analysis and mitigation, rather than just assessing? And, not to mention the fact that a tedious risk assessment process will contribute to burnout that can lead to poor employee retention within your security team. With how the cybersecurity job market is looking now, this isn’t a position any organization wants to be in.
So, now that you know how the people actually with their ‘hands in the pot’ feel about risk assessments, let’s take a look at why this approach is flawed and what organizations can do to build a better risk assessment process.
The key to defeating cybercriminals is to be vigilant and proactive. Not much can be done when you’re reacting to a security incident as the damage is already done. Unfortunately, the current approach to risk management is reactive, and full of gaps that do not provide an accurate view into overall risk levels. How so? Current processes only measure a point-in-time and do not account for the period while the assessment is being completed–or any breaches that occurred after the assessment was submitted. In other words, assessments will need to be routinely refilled out, a never-ending carousel ride, which is not feasible.
It should come to no surprise that assessments are not updated nearly as much as they should be, and that’s to no one’s fault. No one has the time to continually fill out long, redundant Excel sheets. And, not to mention, unless the data collected is standardized, very little can be done with it from an analysis point of view. As a result, assessments are basically thrown in a drawer and never see the light of day.
Every time a third-party breach occurs there is a groundswell of concern and company executives and board members immediately turn to their security team to order risk assessments, sending them on a wild goose chase. What they don’t realize is that ordering assessments after a third-party breach has occurred is already too late. And the organizations that are chosen for a deeper assessment are most likely not the ones with the highest risk. Like a never-ending carousel ride, the chase for risk assessments will never stop unless you hop off the ride now.
The secret ingredient for developing a better risk management collection process is standardized data. You can’t make bread without flour, and you can’t have a robust risk management program without standardized data. Standardized data is the process of gathering data in a common format, making it easier to conduct an analysis and determine necessary next steps. Think of it this way, if you were looking at a chart comparing student test grades and they were all listed in various formats (0.75, 68%, 3/16, etc.), you would have a difficult time comparing these data points. However, if all the data is listed in percentages (80%, 67%, 92%, etc.), you could easily identify who is failing and needs more support in the classroom. This is the way using standardized data in the risk assessment process works. All data collected from assessments would be in the same format and you can understand which third parties are high risk and require prioritized mitigation.
CISOs who are still focused on point-in-time assessments are not getting it right. Organizations need to understand that risk assessment collection alone does not in fact equal reduced risk. While risk assessments are important, what you do with the risk assessment after it is complete is what really matters. Use it as a catalyst to create a larger, more contextual risk profile. Integrate threat intelligence, security ratings, machine learning, and other data sources and you’ll find yourself with all the data and insights you need and more to proactively reduce risk. You’ll be armed with the necessary information to mitigate risk and implement controls before the breach occurs, not the rushed patchwork after. A data-driven approach to third-party risk assessment will provide a more robust picture of risk and put an end to chasing assessments once and for all.

Security Risk Assessment

How to do an information security risk assessment for ISO27001
Oct 20 2022
When moving to a cloud infrastructure, businesses should be looking toward a Zero Trust strategy. This security model protects the cloud from the inside out using the principle of least privilege to grant secure access to any company resource. Eliminating implicit trust helps prevent cloud-related data breaches and provides a security shield for remote workers that use BYOD (Bring Your Own Devices) to access corporate resources.
Cloud environments are dynamic and require a lot of security, especially in a public cloud, where all data might not be protected and phishing attacks run rampant. In fact, 80% of cloud security incidents are due to stolen or lost credentials. Just earlier this year, the Lapsus$ ransomware group managed to breach a third party provider’s Okta authentication and even published screenshots for all to see.
This is where Zero Trust comes into the picture. Zero Trust helps mitigate unauthorized access in cloud environments by enforcing granular access to each user or device attempting to access a workload or resource. This added measure is essential for securing remote workers and third parties from any potential data leaks.
Organizations must adopt Zero Trust principles when building on cloud architectures. Here’s how your organization can successfully leverage the principles to keep cloud environments safe.
With traditional security methods, there’s no cause for concern until a threat is detected. And by that time, it’s too late. Zero trust automatically assumes by default that everyone using the network is a threat until verified.
Following the ‘never trust, always verify’ motto, users will be continuously asked to verify themselves. Not on a one-time basis, but each time they require access to a cloud resource. Multi-Factor Authentication (MFA) technology is an integral component of a successful Zero Trust strategy.
Zero Trust also monitors how many different devices are in the network as well as those trying to gain access at any given time. A proper Device Posture Check will ensure that every device is assessed for risk without any exposure to the network.
Microsegmentation is another way that Zero Trust protects cloud environments. It divides the infrastructure into smaller zones that require additional verification for access. This is also called minimizing the blast radius of a threat.
Lateral movement can occur when an attacker infiltrates the outside barrier and moves within the network. Even when the entry point is discovered with a traditional security method, it can be difficult to detect the threat. During the time it takes to find them, they can move laterally and exfiltrate data. Every user in the network is required to be verified when they enter different zones, drastically reducing the possibility of a breach.
Having several methods of verification means nothing without constant monitoring. Inspect and log all traffic to identify any suspicious behavior or anomalies. Analyzing the log data can help quickly identify threats and improve security policies.
.png?ssl=1)
Zero Trust Security: An Enterprise Guide
Oct 19 2022
October is Security Awareness Month, an exciting time as organizations around the world train people how to be cyber secure, both at work and at home. But what exactly is security awareness and, more importantly, why should we care about it?
Organizations, cybersecurity leaders and the cybersecurity community will all tell you the same thing: People represent the greatest security risk in today’s highly connected world. Organizations see it in their own incidents, and we see it in global data sets.
The most recent Verizon Data Breach Investigations Report (DBIR)- one of the industry’s most trusted reports – has pointed out that people were involved in over 80% of breaches globally. These incidents may involve people being targeted with phishing emails or smishing attacks, or people making mistakes (e.g., IT admins misconfiguring their cloud accounts and accidentally sharing sensitive data with the entire world).
If people represent such a high risk, what should we be doing about it?
The traditional approach has been (and often continues to be) to throw more technology at the problem. If cyber attackers are successfully phishing people with email, we will deploy security technologies that filter and stop phishing email attacks. If cyber attackers are compromising people’s passwords, we will implement multi-factor authentication. The problem is that cyber attackers bypass these technologies by targeting people.
As we get better at identifying and stopping phishing email attacks, cyber attackers target people’s mobile phones with smishing (SMS or message-based) attacks. As more and more organizations deploy MFA, cyber attackers began pestering people with MFA requests until they approve one (as recently happened at Uber).
This is where we also run into our second challenge: Security teams far too often blame people as the root cause of the human risk problem – as evidenced in often used phrases such as “People are the weakest link,” and “If our employees did what we told them to do, they and we would be secure.”
But when we look at cybersecurity from the average employee’s perspective, it turns out that the security community is often to blame. We have made cybersecurity so confusing, scary, and overwhelming that we have set people up for failure. People often have no idea what to do or, if they do know what to do, doing the right thing has become so difficult that they get it wrong or simply choose another option.
Just look at passwords, one of the biggest drivers of breaches. We’ve been saying for years that people continue to use weak passwords in an insecure manner, but the problem persists because the password policies we teach are confusing and constantly changing. For example, many organizations or websites have policies requiring complex passwords of 15 characters, including having upper and lower case letters, symbols, and numbers. Then we require people to change those passwords every ninety days but don’t provide a secure way to secure all those long, complex, and changing passwords.
Then we roll out MFA to help secure people but, once again, this is extremely confusing (even for me!). First, we have multiple different names for MFA, including two-factor authentication, two-step verification, strong authentication, or one-time passwords. Then we have multiple different ways to implement it including push notification, text messaging, FIDO token-based, authentication apps, etc. Every website you go to has a different name and implementation of this technology, and then we once again blame people for not using it.
Security awareness training has been the traditional approach, and it involves communicating to and training your workforce on how to be cyber secure. While a step in the right direction, we need to take this one step further: We need to manage human risk.
Managing human risk requires a far more strategic approach. It builds on security awareness, to include:
Managing human risk is becoming a fundamental part of every security leader’s strategy. Security awareness is the first step in the right direction as we attempt to communicate to, engage and train our workforce, but we need a more dedicated, strategic effort to truly manage human risk. Perhaps one day we will even grow and replace the role of the Security Awareness Officer with the Human Risk Officer.

The Security Culture Playbook: An Executive Guide To Reducing Risk and Developing Your Human Defense Layer
Oct 19 2022
The cybersecurity company Kaspersky detected almost 900 servers being compromised by sophisticated attackers leveraging the critical Zimbra Collaboration Suite (ZCS), which at the time was a zero-day without a patch for nearly 1.5 months.
“We investigated the threat and was able to confirm that unknown APT groups have actively been exploiting this vulnerability in the wild, one of which is systematically infecting all vulnerable servers in Central Asia”, Kaspersky
The vulnerability tracked as (CVE-2022-41352) is a remote code execution flaw that allows attackers to send an email with a malicious archive attachment that plants a web shell in the ZCS server while, at the same time, bypassing antivirus checks.
Kaspersky researchers say that various APT (advanced persistent threat) groups actively exploited the flaw soon after it was reported on the Zimbra forums.
Reports say a proof of concept for this vulnerability was added to the Metasploit framework, laying the groundwork for massive and global exploitation from even low-sophistication attackers.
Zimbra released a patch for this vulnerability; With ZCS version 9.0.0 P27, replacing the vulnerable component (cpio) with Pax and removing the weak part that made exploitation possible. Hence, update your devices immediately.
Researchers say performing disinfection on Zimbra is extremely difficult, since the attacker had access to configuration files containing passwords used by various service accounts.
Therefore, these credentials can be used to regain access to the server if the administrative panel is accessible from the internet.
Volexity stated that they identified approximately 1,600 ZCS servers that they believe were compromised by threat actors leveraging CVE-2022-41352 to plant webshells.
Reports say the initial attacks started in September, targeting vulnerable Zimbra servers in India and some in Turkey. Therefore, it was probably a testing wave against low-interest targets to assess the effectiveness of the attack.
Notably, Kaspersky assessed that the threat actors compromised 44 servers during this initial wave. Later on the threat actors began to carry out mass targeting to compromise as many servers worldwide before admins patched the systems and close the door to intruders.
At present, the second wave had a greater impact, infecting 832 servers with malicious webshells. Hence, it is recommended to update your devices immediately.

#ZeroDay
Oct 18 2022
While knowing full well that human lives may be at stake, criminal gangs have been increasingly targeting the healthcare sector with high-impact attacks like ransomware.
Healthcare providers should set up numerous layers of defense for a variety of email-borne threats. A good email security solution should be the first layer but will only be effective if it is able to detect multiple malicious signals (malicious IPs, suspicious URLs, hidden malware files, etc.).
Training staff to recognize malicious emails can be useful, but personnel should not bear the brunt of responsibility when it comes to catching signs of attack. Instead, training should focus on the importance of proper policies, such as confirming payments and transfers with a second channel outside of email.
Obtaining login credentials is a primary goal in most cyberattacks, and many threat actors now specialize in selling information on to others. Investigations by the Trustwave SpiderLabs team found a large quantity of stolen login credentials and browser sessions enabling access to healthcare facilities advertised on dark web markets.
In addition to following best practices around phishing emails, all employees should be using complex passwords that can’t be easily guessed. When storing passwords, organizations must make sure to use modern and robust password hashing algorithms. Two-factor authentication should also be implemented across the organization as a priority (Note: SMS 2FA should not be considered secure).
While the responsibility of spotting and stopping cyberattacks should not rest on ordinary healthcare personnel, a well-trained workforce can make a real difference in averting disaster. Attackers will be counting on healthcare staff being too busy and focused on supporting their patients to concentrate on security.
Security training is often limited to a few one-off PowerPoint-driven seminars, but this will do little to increase awareness. Healthcare providers should instead consider more in-depth exercises that replicate serious incidents such as ransomware attacks. This will help decision makers to gain experience in making snap decisions under pressure, better equipping them for when a real crisis looms.
Ransomware is a threat to all sectors, but healthcare is particularly vulnerable to its disruptive effects. A paralyzed IT network will mean more than lost data or productivity – human lives may be on the line if data and equipment are locked down. Callous criminals are counting on healthcare providers caving and paying up to restore systems quickly. Further, attackers increasingly exfiltrate data to pile on more pressure and secure additional profits from dark web buyers.
A strong email security system will stop most malicious emails, but not all – and organizations should be prepared for that. Effective managed detection and response (MDR) capabilities, backed by a skilled team of threat hunters, will help identify and stop ransomware quickly to reduce its impact. A managed security service provider (MSSP) is one of the most affordable ways of acquiring these capabilities on a limited budget.
Internet of Things (IoT)-enabled equipment has been hugely beneficial in enabling healthcare providers to automate and facilitate remote working. But if not properly monitored and patched, these connected devices can also provide threat actors with an easy attack path.
Hospitals are likely to have hundreds of devices deployed across their facilities, so keeping them all updated and patched can be an extremely resource-heavy task. Many health providers also struggle to accommodate the required downtime to update vital equipment.
Automating device discovery and update processes will make it easier to keep devices secured. Providers should also vet future purchases to ensure they have key security functionality and are accessible for maintenance and updates.
Healthcare providers sit in the center of extremely large and complex supply networks. Suppliers for medical materials, consultants, hardware, and facilities maintenance are just a few examples, alongside a growing number of digital services.
These suppliers often have a large degree of network connectivity or access to data, making them a prime target for threat actors seeking a way into the healthcare provider’s network. Organizations can also become the victim of a second-hand breach if a firm trusted to host or manage their data is attacked.
Supply chain risk can be reduced by vetting the security level of all third-party connections. This can be achieved without invasive network scans through publicly available information such as DNS server configurations and the presence of insecure ports open to the internet (e.g., MS-TERM-SERV, SMB, etc.).
Security is never a one-and-done affair. Even if the right solutions are in place, the workforce has been well-trained and processes are watertight, it is important to continually test defenses and look for ways to improve them.
Regular vulnerability scans are essential for keeping up with the shifting IT and cyber threat landscape. Application and network penetration tests will take things a step further by leveraging the ingenuity of experienced security personnel to look for a crack that can be found and exploited.
Larger healthcare providers such as hospitals may also consider physical penetration tests to determine if their facility’s IT infrastructure is vulnerable to an intruder on their grounds.
Hospitals and other frontline healthcare providers are used to dealing with medical emergencies. Personnel have the equipment and processes they need in place, and they have the training to adopt the cool head needed to handle a crisis.
As attackers continue to target the sector, the same level of preparation is increasingly essential for cyber threats.
Criminal gangs are counting on budget cuts and staffing shortages to leave healthcare organizations vulnerable to their attacks. By focusing on these seven steps, providers will be able to present a hardened target that sends these callous opportunists in search of easier prey.

Oct 18 2022
If you’re a security practitioner dealing with ISO 27001, you’re probably wondering what new things you will need to implement as part of the changes that will be made to this standard during 2022.
In this article, I’ll focus on 11 new controls that are set to be introduced in ISO 27001. For general information about the changes, see this article: Most important facts about changes in ISO 27001/ISO 27002.
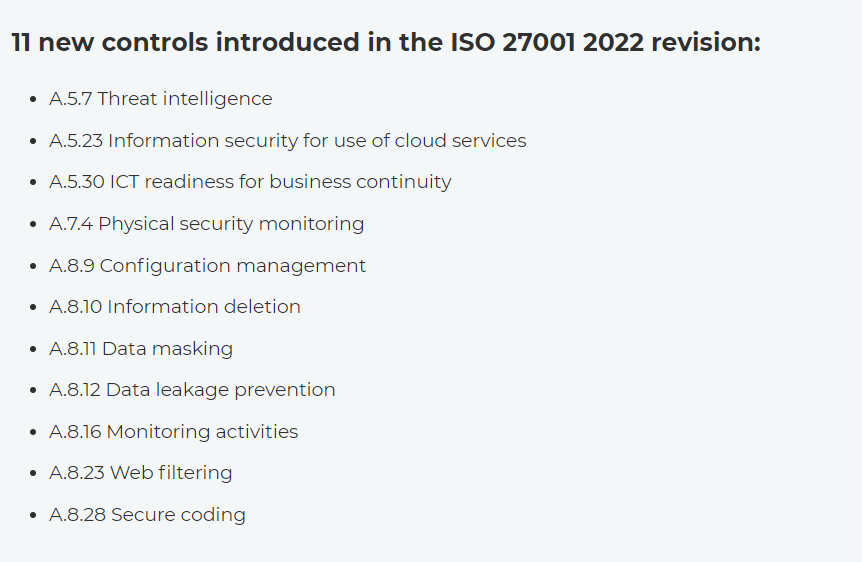
What you’ll notice is that some of these new controls are very similar to old controls from the 2013 revision; however, because these controls were categorized as new in ISO 27002:2022, I have listed all 11 in this article.
As the main source for this article, I’ve used guidelines from ISO 27002:2022 – I’ve given an overview of requirements, technology, people, and documentation, but if you’d like to learn about these controls in more depth, you can purchase the ISO 27002 2022 standard.
Finally, keep in mind that these controls are not mandatory – ISO 27001 allows you to exclude a control if (1) you identified no related risks, and (2) there are no legal/regulatory/contractual requirements to implement that particular control.
So, let’s review the 11 controls in more detail…
Oct 18 2022
A new open-source analytical tool dubbed RedEye designed to make it easier for operators to visualize and report activities associated with C2 communication has been released by CISA.
Both the red and blue teams can benefit from RedEye, as it provides an easy way to gauge data, leading to specific decisions that can be made with confidence.

A collaborative effort between CISA and DOE’s Pacific Northwest National Laboratory has given birth to this analytical tool.
A graphically displayed log of all servers and hosts associated with each campaign can be retrieved by RedEye users by correlating historical records of each campaign log.
In order to view relevant information about a campaign, users can upload campaign data via RedEye to view information such as:-
During the process of parsing log files, such as those generated by Cobalt Strike, the tool presents the information in a format that can be easily understood.
As a result, users are able to tag activities displayed within the tool and comment on them. Operators can present findings and workflow to stakeholders using the presentation mode that is available on the RedEye application.
To discover the payload activity analysts can also analyze all the key events in a selected campaign. In addition to using RedEye to check the raw data received after an assessment, blue teams can also use it to understand it better.
This data can be used by them to see the attack path and the compromised hosts to take the appropriate action based on what they have learned.
RedEye offers a wide range of features and all its key features are presented in the below video made by CISA:-
Apart from RedEye, the CISA have also released several other open-source tools like:-
The following major platforms have been tested and proved to be compatible with RedEye:-
Moreover, the CISA’s repository on GitHub hosts the tool, and it is available for download via the repository.
Oct 17 2022

In recent weeks, cybercrime and data breaches have become unavoidable topics in Australia. Many citizens have been forced to confront – for the first time – the reality of living in a disrupted digital world, where our personal data has become the most valuable commodity.
Of course, as tech leaders, this is a topic that keeps us awake at night. No part of our economy has proven immune from the impacts of cybercrime and data breaches.. Government agencies at all levels, large organisations, critical infrastructure providers, small-to-medium enterprises, families and individuals have all been targets.
Our customers sleep soundly at night in the knowledge there will be no unauthorised access to their physical digital infrastructure located in our data centres.
However, it’s not just CISOs who should be worried, particularly when considering this key question: What is the true cost to our economy of cybercrime?
It’s a $33 billion question because that’s how much Australian organisations self-reported in cybercrime losses during FY21. And that doesn’t even cover the hefty financial penalties that apply to companies that fail to protect their customer data.
The cost extends far beyond the financial. Aside from the financial costs there are the non-financial costs to individual companies that are victims of these attacks. This includes reputational damage, remedial distraction, service interruptions and process breakdowns. Cybercrime also poses a major threat to consumer trust, innovation, and growth across the digital economy.
In other words, security risk management is fast becoming every business leader’s problem – not just for CISOs and CSOs.
At NEXTDC, we’ve been talking for some time about the importance of an integrated approach to security risk management around digital infrastructure. The conversation so far has been focused on how there must be a ‘mesh’ or integrated approach to physical and cyber security. These are the first two pillars of robust security risk management and, , they have converged to the point where you can’t have one without the other.
As I like to say, securing your internal critical infrastructure is only half the story. You can have the most advanced cyber security systems in place and still be compromised by a physical breach of your facility.
However, there are two additional pillars to security risk management. These are less well-known but are no less important – people and processes, and supply chain and business continuity. And responsibility for those extends far beyond the technology department.
The remainder of this article will focus on the people and processes pillar. A subsequent blog will address supply chains and business continuity.
Most of us are familiar with the terms converged or integrated security risk management, but what does that really mean from a people and process perspective? For most organisations, it comes down to what it is you’re trying to protect against. In general, that will fall into one of two categories: accidental or deliberate (malicious) human actions.
While it’s usually the malicious actors who get the most airtime (put your hand up if you immediately visualise a shadowy figure in a hoodie hunched over a laptop when you hear the word ‘hacker’!) – the evidence suggests we should be far more worried about accidental actions.
Malicious actors are everywhere, constantly active and becoming increasingly sophisticated, but human error is still the greatest cause of data breaches. Robust physical environments – supported by cutting edge technology, education to create awareness amongst people and the right processes to support them – are still the most important component of holistic security strategy.
As pressure continues to mount around data protection and sovereignty, an enhanced security posture is best achieved by partnering strategically with a trusted provider. A supply chain partner who will take on not only the heavy lifting that gets you to your ideal state, faster and safely, but also without significant capital investment in infrastructure, personnel and meeting compliance.
Your provider’s security risk management must be completely aligned with yours, so ensure you ask the right questions during the evaluation process. Make sure you dig deep into factors such as:
Your customers, regulators, investors and partners are depending on you to get security risk management right and the consequences of falling short in this area can be very expensive and long lasting.
Oct 17 2022
Cybersecurity researcher Scott Scheferman reported that a new Windows UEFI rootkit, dubbed Black Lotus, is advertised on underground criminal forums. The powerful malware is offered for sale at $5,000, with $200 payments per new updates.
The researcher warns that the availability of this rootkit in the threat landscape represents a serious threat for organizations due to its evasion and persistence capabilities.
“Considering this tradecraft used to be relegated to APTs like the Russian GRU and APT 41 (China nexus), and considering prior criminal discoveries we’ve made (e.g. Trickbot‘s #Trickboot module), this represents a bit of a ‘leap’ forward, in terms of ease of use, scalability, accessibility and most importantly, the potential for much more impact in the forms of persistence, evasion and/or destruction.” wrote Scheferman.
Black Lotus is written in assembly and C and is only 80kb in size, the malicious code can be configured to avoid infecting systems in countries in the CIS region.
The malware supports anti-virtualization, anti-debugging, and code obfuscation. Black Lotus is able to disable security solutions, including Hypervisor-protected Code Integrity (HVCI), BitLocker, and Windows Defender. The rootkit is able to bypass security defenses like UAC and Secure Boot, it is able to load unsigned drivers used to perform a broad range of malicious activities.
The threat is very stealth, it can achieve persistence at the UEFI level with Ring 0 agent protection.
Black Lotus supports a full set of backdoor capabilities, it could be also used to potential target IT and OT environments.
Black Lotus is bringing APT capabilities to malicious actors in the threat landscape.

Oct 17 2022
With the release of the PhaaS platform called ‘Caffeine’, threat actors can now easily launch their own sophisticated phishing attacks. Anyone who wants to start their own phishing campaign will be able to register on this platform through an open registration process.
Caffeine has been thoroughly tested by the analysts at Mandiant. This is a free and open-source platform that does not require any specific requirements like the following to use its portal for launching Phishing campaigns:-
Phishing Scam