LONDON — Western countries risk losing control of technologies that are key to internet security and economic prosperity to nations like China and Russia if they don’t act to deal with the threat, one of the UK’s top spy chiefs warned Friday.
“Significant technology leadership is moving east” and causing a conflict of interests and values, Jeremy Fleming, director of government electronic surveillance agency GCHQ, said in a speech.
Singling out China as a particular threat, he said the country’s “size and technological weight means that it has the potential to control the global operating system.”
China is an early adopter of emerging technologies but it also has a “competing vision for the future of cyberspace,” and it’s playing an influential role in the debate around international rules and standards, he said.
He raised the possibility of countries with “illiberal values” like China building them into technical standards that the world ends up relying on, and using their state power to control and dominate technology markets, turning them into arenas of geopolitical competition.
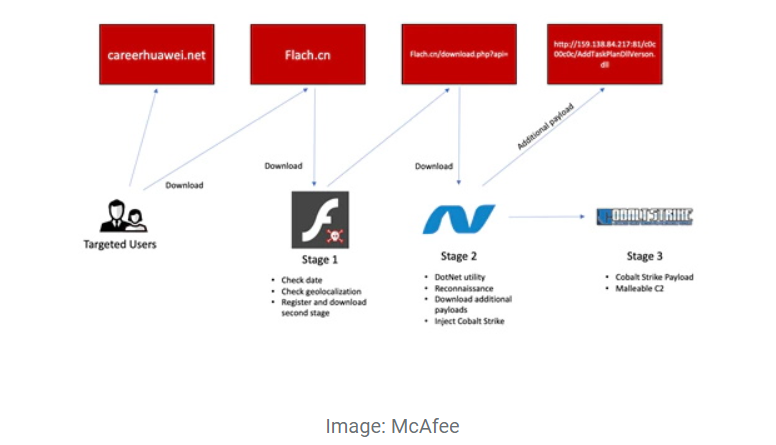
Russian hacking and other nefarious online activity, meanwhile, poses the most acute threat to the UK but, like a smartphone app vulnerability, could be avoided.
China’s Foreign Ministry blasted the remarks, saying they were “totally groundless and unreasonable.”
“Western countries, such as the UK and US, are actually the true empires of hacking and tapping,” ministry spokesman Zhao Lijian said at a briefing in Beijing.
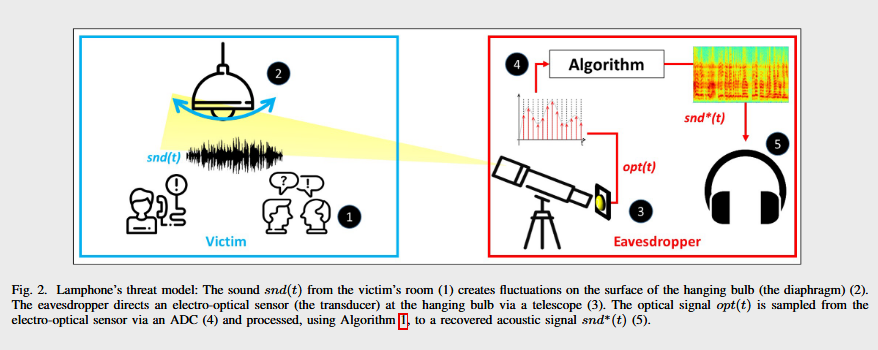
Left unchecked, foreign adversaries could threaten the design and freedom of the internet, Fleming said. He citied as examples the security for emerging technologies like “smart city” sensors used to manage services more efficiently or digital currencies, saying they could be hardwired for data collection or other intrusive capabilities that go against open and democratic societies.
Britain and other Western countries face “a moment of reckoning,” Fleming said.
“The rules are changing in ways not always controlled by government,” Fleming said in his speech at Imperial College London. “And without action it is increasingly clear that the key technologies on which we will rely for our future prosperity and security won’t be shaped and controlled by the West.”
Britain should not take its status as a cyber power for granted, and it should work on developing “sovereign technologies” such as high-speed quantum computing and cryptographic technology to protect sensitive information, Fleming said.
China’s focus on establishing information dominance as a key component of its military efforts.