
PowerShell Cheat Sheet
Mastering PowerShell Scripting: Automate and manage your environment using PowerShell
Infosec books | InfoSec tools | InfoSec services
InfoSec and Compliance – With 20 years of blogging experience, DISC InfoSec blog is dedicated to providing trusted insights and practical solutions for professionals and organizations navigating the evolving cybersecurity landscape. From cutting-edge threats to compliance strategies, this blog is your reliable resource for staying informed and secure. Dive into the content, connect with the community, and elevate your InfoSec expertise!
Jan 02 2023
Dec 31 2022
Dec 26 2022
Cybersecurity awareness is no longer a “nice to have”; in fact, it has become a fundamental part of your corporate training process across all levels and aspects of your business.
Would you leave your business unlocked and open to all comers? Of course not – but if you don’t have solid cybersecurity in place, that’s effectively what you’re doing! As the business world becomes a digital space, security has also become a digital matter.
One cybercriminal can wreak havoc if unchecked, and our potential flashpoints for vulnerabilities are growing daily. Nor is this something you can achieve alone – a great IT security team is one thing, but if one of your other workers leaves the metaphorical door unlocked, you’ll still be in trouble.
With top-down training boosted with the power of video, however, security can become a simple matter.
The average cost-per-company of a data breach is over $4 million. Cybercrime currently costs companies globally $8.4 trillion a year- and that is expected to soar to $23 trillion (or more) by 2027. Fortunately, there’s a lot you can do to mitigate your risk and keep your company out of those stats.
Humans are and will remain, the weakest link in any business’s digital security. Just as a thoughtless individual can leave a door unlocked and bypass your multi-million dollar security system in a heartbeat, one wrong move from an employee and even the best cybersecurity comes tumbling down.
It’s critical that all people in your organization are aware of cybersecurity risks, know the best practices for data and network security, and understand the consequences of laziness leading to cybersecurity failures.
It’s a simple idea – using a technical approach to proactively educate employees, ensuring awareness of data privacy, identity, and digital assets permeates every level of your organization. This will immensely reduce your risk of cybersecurity breaches. In turn, that means fewer financial losses from this type of crime, making it a solid return on investment.
And being cybersecurity-aware will have knock-on positives in your reputation with consumers, making you seem more trustworthy and desirable. Prevention of security issues means no loss of brand reputation, too.
Of course, your training is only as good as its retention rate. Cybersecurity training for employees can’t be some dull, dusty lecture or 500-page word document that’s unengaging, boring, and packed with jargon, or you may as well not waste your time. It’s critical that staff feel both empowered with their new skills, and that it comes over as simple to understand and easy to implement.
We all know that video is one of the most powerful storytelling formats out there. From the power of video shorts and reels for marketing to the way a great TV program can unite us, it’s a format that delivers punchy messages in an engaging way.
Unlike text, where aspects like reading level can play a role, everyone can engage with video. Plus you have the benefit of being able to condense a lot of information into short, pithy, and easy-to-retain factoids. You can power that up further with the power of AI, making videos simple to create, engaging, and easy to update and adapt without a huge financial outlay.
Using a simple text-to-speech format, you can create compelling, entertaining, and educational content that will help keep every member of your organization aware of cybersecurity risks and qualified to prevent them from occurring.
Cybersecurity awareness is no longer a ‘nice to have’. It’s an absolutely essential part of your corporate training process, across all levels and aspects of your business. With the power of simple-to-use AI video on your side, creating engaging learning programs to keep staff informed and ahead of cyber criminals is a simple matter, so don’t delay in addressing this critical aspect of business security today.

Learn cybersecurity fundamentals, including how to detect threats, protect systems and networks, and anticipate potential cyber attacks.
Infosec books | InfoSec tools | InfoSec services
Dec 16 2022
Microsoft revised the severity rate for the CVE-2022-37958 vulnerability, the IT giant now rated it as “critical” because it discovered that threat actors can exploit the bug to achieve remote code execution.
The CVE-2022-37958 was originally classified as an information disclosure vulnerability that impacts the SPNEGO Extended Negotiation (NEGOEX) security mechanism.
The SPNEGO Extended Negotiation Security Mechanism (NEGOEX) extends Simple and Protected GSS-API Negotiation Mechanism (SPNEGO) described in [RFC4178].
The SPNEGO Extended Negotiation (NEGOEX) Security Mechanism allows a client and server to negotiate the choice of security mechanism to use.
The issue was initially rated as high severity because the successful exploitation of this issue required an attacker to prepare the target environment to improve exploit reliability.
Microsoft addressed the vulnerability with the release of Patch Tuesday security updates for September 2022.
IBM Security X-Force researcher Valentina Palmiotti demonstrated that this vulnerability is a pre-authentication remote code execution issue that impacts a wide range of protocols. It has the potential to be wormable and can be exploited to achieve remote code execution.
“The vulnerability could allow attackers to remotely execute arbitrary code by accessing the NEGOEX protocol via any Windows application protocol that authenticates, such as Server Message Block (SMB) or Remote Desktop Protocol (RDP), by default.” reads the post published by IBM. “This list of affected protocols is not complete and may exist wherever SPNEGO is in use, including in Simple Message Transport Protocol (SMTP) and Hyper Text Transfer Protocol (HTTP) when SPNEGO authentication negotiation is enabled, such as for use with Kerberos or Net-NTLM authentication.”
Unlike the CVE-2017-0144 flaw triggered by the EternalBlue exploit, which only affected the SMB protocol, the CVE-2022-37958 flaw could potentially affect a wider range of Windows systems due to a larger attack surface of services exposed to the public internet (HTTP, RDP, SMB) or on internal networks. The expert pointed out that this flaw can be exploited without user interaction or authentication.
IBM announced it will release full technical details in Q2 2023 to give time organizations to apply the security updates.

Mastering Windows Security and Hardening: Secure and protect your Windows environment from intruders, malware attacks, and other cyber threats
Dec 13 2022
Aikido is the wiper tool that has been developed by the Or Yair of SafeBreach Labs, and the purpose of this wiper is to defeat the opponent by using their own power against them.
As a consequence, this wiper can be run without being given privileges. In addition, it is also capable of wiping almost every file on a computer, including the system files, in order to make it completely unbootable and unusable.
EDRs are responsible for deleting malicious files in two main ways, depending on the following contexts:-

As soon as a malicious file is detected and the user attempts to delete it, the Aikido wiper takes advantage of a moment of opportunity.
This wiper makes use of a feature in Windows allowing users to create junction point links (symlinks) regardless of the privileges of the users’ accounts, which is abused by this wiper.
A user who does not have the required permissions to delete system files (.sys) will not be able to delete those files according to Yair. By creating a decoy directory, he was able to trick the security product to delete the file instead of preventing it from being deleted.
Likewise, he placed a string inside the group that resembled the path intended for deletion, for example, as follows:-
Here below we have mentioned all the general qualities of the Aikido Wiper:-
It was found that six out of 11 security products tested by Or Yair were vulnerable to this exploit. In short, over 50% of the products in this category that is tested are vulnerable.
Here below we have mentioned the vulnerable ones:-
Here below we have mentioned the products that are not vulnerable:-
Between the months of July and August of this year, all the vulnerabilities have been reported to all the vendors that have been affected. There was no arbitrary file deletion achieved by the researcher in the case of Microsoft Defender and Microsoft Defender for Endpoint products.
In order to cope with the vulnerabilities, three of the vendors have issued the following CVEs:-
This exploit was also addressed by three of the software vendors by releasing updated versions of their software to address it:-
This type of vulnerability should be proactively tested by all EDR and antivirus vendors to ensure that their products are protected from similar attacks in the future.
For organizations using EDR and AV products, the researcher strongly recommends that they consult with their vendors for updates and patches immediately.
Dec 08 2022
Before selling or trading in your laptop, it is important to prepare the device for its new owner as this will help ensure all of your personal data remains safe.
In an age when every day, a new version of a laptop with better features, sleek design, and improved performance hits the market, it is no wonder that you also wish to buy a new laptop to achieve excellence in performance and enjoy new features.
You have money, you can buy a new laptop, great! But what about your previous laptop? If you are thinking of selling it, then…stop.
If you think selling a laptop is all about saving your data, finding a seller, and selling it, then you need to think again. It goes beyond this! It is not all about getting a fair price, but also saving your personal information and private data from reaching a stranger – that might cost you a lot if that stranger is fraudulent or malicious.
Before selling or trading in your laptop, it is important to prepare the device for its new owner. This can be done by taking several simple precautions that will help ensure all of your personal data remains safe.
It goes without saying that your first step should be keeping a backup of your essential data, including personal and work-related files and folders, containing documents, presentations, emails, plans, strategies, or anything else that you have prepared with so much hard work.
If you don’t want to see your data slipping from your fingers, then this should be your number one step.
You can save your data on a data drive or upload it to a reliable cloud service. Or send them to your own email address (well, this is my favorite way of saving my data!). Do whatever suits you, but saving data is a must before selling your laptop.
However, this can only work if you have a few GB of data. In case you have terabytes of data then owning a workstation from companies like Western Digital (WD) is a good way to go.
Nobody wants the passwords of important accounts to get leaked. Full stop! But have you ever thought about how to save your passwords before giving your laptop? What — did you just say you can do it by signing off from all your accounts and deleting history and cookies? Ah, I wish it was really that easy, but it is not.
Where technology has brought so much ease into our lives, there it has also become a trouble in many ways — like this one. Unfortunately, some software can extract passwords even if you log out from your accounts.
That is where you should act smartly if you don’t want someone to sneak into your Facebook and start sending weird messages through your accounts to your friends. It could trigger so many controversies – eh. So, cut iron with iron.
You can also use apps such as password generators. One such example is the IPVanish password generator which lets users delete passwords permanently from their browsers. If you wish to do that manually, follow these easy steps:
For Chrome browser: First, open Chrome and click on the three-dot menu icon located in the top right corner. Then select “Settings” and click on “Passwords” under Autofill. Here you will find a list of all the websites that have saved credentials, along with their usernames and passwords.
Select an entry to see the details, then click on the three-dot menu icon next to it and select “Remove.” You’ll be asked to confirm by clicking “remove” again; once confirmed all login information for that website will be deleted from your computer. (Read more on Google.)
For Firefox: First, launch the Firefox browser on your device. Then, click the ‘Menu’ icon (three lines in the upper right corner) and select ‘Options’ or ‘Preferences’. In this menu, you will see a section for ‘Logins & Passwords. You can then scroll through all of your saved logins and passwords until you find the one that needs to be deleted.
For Safari Browser: To begin, open up the Safari browser on your computer and click the ‘Safari’ menu at the top left corner. In that menu option, select ‘Preferences’ and then navigate to the ‘Passwords’ tab. (Read more on Mozilla.)
Here you will see a list of all of your stored passwords that have been saved by Safari. To delete one or more of these passwords, simply check off each box next to each entry that you wish to remove and hit delete in the bottom right corner. (Read more on Apple.)
Have you saved your important data? Great! Now, what about data that is still on your laptop? Obviously, you can’t leave it like this for others to see your private information and confidential data. No, just deleting data files and clearing Recycle Bin or Shift + Delete might not work. It can still keep the issue of data leakage and privacy breaches there.
In this condition, most people go for drive formatting that cleans up your laptop and makes it data free. However, this method works if your files are overwritten and you are using a solid-state drive (SSD) with TRIM enabled.
With HDD or TRIM disabled, you would have to overwrite the hard drive if you don’t want cheap software to recover your data – yes, even after formatting. It is very easy to recover a permanently deleted file through even cheap software. So, be safe than sorry!
Once you are done saving your information, next, it is time to prepare your laptop for sale at a good price. The price of your gadget also depends on its model, functionalities, current market price, and a lot more. However, improving the outer condition, and speed, upgrading Windows, and enhancing the memory storage can enhance the price of your laptop.
So, work on the following things to get good bucks:

Nov 29 2022
On the morning of August 4, 2022, Advanced, a supplier for the UK’s National Health Service (NHS), was hit by a major cyberattack. Key services including NHS 111 (the NHS’s 24/7 health helpline) and urgent treatment centers were taken offline, causing widespread disruption. This attack served as a brutal reminder of what can happen without a standardized set of controls in place. To protect themselves, organizations should look to ISO 27001.
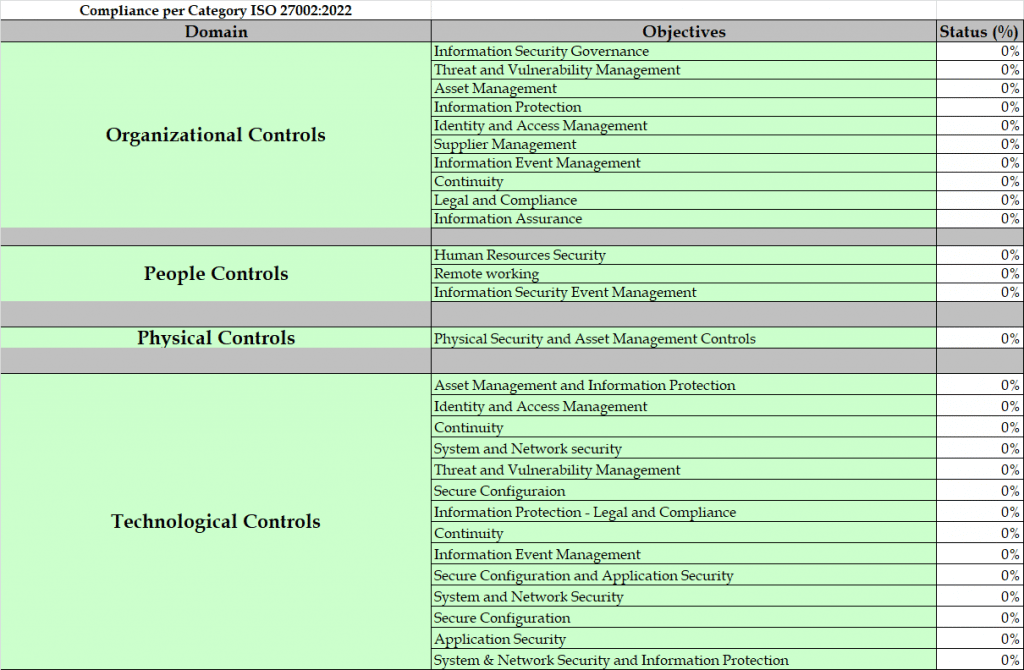
ISO 27001 is an internationally recognized Information Security Management System standard. It was first published in 2005 to help businesses implement and maintain a solid information security framework for managing risks such as cyberattacks, data leaks and theft. As of October 25, 2022, it has been updated in several important ways.
The standard is made up of a set of clauses (clauses 4 through 10) that define the management system, and Annex A which defines a set of controls. The clauses include risk management, scope and information security policy, while Annex A’s controls include patch management, antivirus and access control. It’s worth noting that not all of the controls are mandatory; businesses can choose to use those that suit them best.
It’s been nine years since the standard was last updated, and in that time, the technology world has changed in profound ways. New technologies have grown to dominate the industry, and this has certainly left its mark on the cybersecurity landscape.
With these changes in mind, the standard has been reviewed and revised to reflect the state of cyber- and information security today. We have already seen ISO 27002 (the guidance on applying the Annex A controls) updated. The number of controls has been reduced from 114 to 93, a process that combined several previously existing controls and added 11 new ones.
Many of the new controls were geared to bring the standard in line with modern technology. There is now, for example, a new control for cloud technology. When the controls were first created in 2013, cloud was still emerging. Today, cloud technology is a dominant force across the tech sector. The new controls thus help bring the standard up to date.
In October, ISO 27001 was updated and brought in line with the new version of ISO 27002. Businesses can now achieve compliance with the updated 2022 controls, certifying themselves as meeting this new standard, rather than the now-outdated list from 2013.
Implementing ISO 27001 brings a host of information security advantages that benefit companies from the outset.
Companies that have invested time in achieving ISO 27001 certification will be recognized by their customers as organizations that take information security seriously. Companies that are focused on the needs of their customers should want to address the general feeling of insecurity in their users’ minds.
Moreover, as part of the increasingly rigorous due-diligence processes that many companies are now undertaking, ISO 27001 is becoming mandatory. Therefore, organizations will benefit from taking the initiative early to avoid missing out commercially.
In the case of cyber-defense, prevention is always better than cure. Attacks mean disruption, which almost always proves costly for an organization, in regard to both reputation and finances. Therefore, we might view ISO 27001 as a form of cyber-insurance, where the correct steps are taken preemptively to save organizations money in the long term.
There’s also the matter of education. Often, an organization’s weakest point, and thus the point most often targeted, is the user. Compromised user credentials can lead to data breaches and compromised services. If users were more aware of the nature of the threats they face, the likelihood of their credentials being compromised would decrease significantly. ISO 27001 offers clear and cogent steps to educate users on the risks they face.
Ultimately, whatever causes a business to choose implementation of ISO 27001, the key to getting the most out of it is ingraining its processes and procedures in their everyday activity.
A lot of companies have already implemented many controls from ISO 27001, including access control, backup procedures and training. It might seem at first glance that, as a result, they’ve already achieved a higher standard of cybersecurity across their organization. However, what they continue to lack is a comprehensive management system to actually manage the organization’s information security, ensuring that it is aligned with business objectives, tied into a continuous improvement cycle, and part of business-as-usual activities.
While the benefits of ISO 27001 may be obvious to many in the tech industry, overcoming obstacles to certification is far from straightforward. Here are some steps to take to tackle two of the biggest issues that drag on organizations seeking ISO 27001 certification:
While making this all a reality for your business can seem daunting, with the right plan in place, businesses can rapidly benefit from all that ISO 27001 certification has to offer.
It’s also important to recognize that this October was not the cutoff point for businesses to achieve certification for the new version of the standard. Businesses will have a few months before certification bodies will be ready to offer certification, and there will likely then be a two-year transition period after the new standard’s publication before ISO 27001:2013 is fully retired.
Ultimately, it’s vital to remember that while implementation comes with challenges, ISO 27001 compliance is invaluable for businesses that want to build their reputations as trusted and secure partners in today’s hyper-connected world.
Source: https://wordpress.com/read/blogs/126020344/posts/2830377
ISO 27001 Risk Assessment and Gap Assessment
ISO 27001 Compliance and Certification
Nov 19 2022
Given that we’re getting into peak retail season, you’ll find cybersecurity warnings with a “Black Friday” theme all over the internet…
…including, of course, right here on Naked Security!
As regular readers will know, however, we’re not terribly keen on online tips that are specific to Black Friday, because cybersecurity matters 365-and-a-quarter days a year.
Don’t take cybersecurity seriously only when it’s Thanksgiving, Hannukah, Kwanzaa, Christmas or any other gift-giving holiday, or only for the New Year Sales, the Spring Sales, the Summer sales or any other seasonal discount opportunity.
As we said when retail season kicked off earlier this month in many parts of the world:
The best reason for improving your cybersecurity in the leadup to Black Friday is that it means you will be improving your cybersecurity for the rest of the year, and will encourage you to keep on improving through 2023 and beyond.
Having said that, this article is about a PayPal-branded scam that was reported to us earlier this week by a regular reader who thought it would be worth warning others about, especially for those with PayPal accounts who may be more inclined to use them at this time of year than any other.
The good thing about this scam is that you should spot it for what it is: made-up nonsense.
The bad thing about this scam is that it’s astonishingly easy for criminals to set up, and it carefully avoids sending spoofed emails or tricking you to visit bogus websites, because the crooks use a PayPal service to generate their initial contact via official PayPal servers.
Here goes.
A spoofed email is one that insists it’s from a well-known company or domain, typically by putting a believable email address in the From: line, and by including logos, taglines or other contact details copied from the brand it’s trying to impersonate.
Remember that the name and email address shown in an email next to the word From are actually just part of the message itself, so the sender can put almost anything they like in there, regardless of where they really sent the message from.
A spoofed website is one that copies the look and feel of the real thing, often simply by ripping off the exact web content and images from the original site to make it look as pixel-perfect as possible.
Scam sites may also try to make the domain name that you see in the address bar look at least vaguely realistic, for example by putting the spoofed brand at the left-hand end of the web address, so that you might see something like paypal.com.bogus.example, in the hope that you won’t check the right-hand end of the name, which actually determines who owns the site.
Other scammers try to acquire lookalike names, for example by replacing W (one W-for-Whisky character) with VV (two V-for Victor characters), or by using I (writing an upper case I-for-India character) in place of l (a lower case L-for-Lima).
But spoofing tricks of this sort can often be spotted fairly easily, for example by:
Email scammers therefore often go out of their way to ensure that their first contact with potential victims involves messages that really do come from genuine sites or online services, and that link to servers that really are run by those same legitimate sites…
…as long as the scammers can come up with some way of maintaining contact after that initial message, in order to keep the scam going.
Nov 17 2022
The most prominent CMS today is WordPress which is being used by over 455 million across the globe.
As the internet becomes increasingly integral to daily life, website security is more important than ever. Hackers can gain access to sensitive information, like credit card numbers and social security numbers, through websites with weak security. This can lead to identity theft and financial fraud.
Your website’s CMS (content management system) works as the backbone of your entire setup. The most prominent CMS today is WordPress which is being used by over 455 million across the globe. Naturally, WordPress is a lucrative target for cybercriminals and highlights the fact why WordPress security should never be ignored.
WordPress or another other CMS, while 100% security may be a myth, there are a few things you can do to ensure your website is secure from external and internal threats.
A website is a powerful tool that can help businesses of all sizes reach new customers and grow. However, a website is only as secure as the hosting provider that it uses. That’s why it’s important to choose a secure website hosting provider when setting up your website. Here are two things to look for in a secure website hosting provider:
1. Industry-Leading Security Measures: A good web hosting provider will have industry-leading security measures in place to protect your website from hackers and other online threats. This includes things like firewalls, DDoS protection, and malware scanning.
2. Regular Backups: In the event that your website is hacked or compromised, regular backups will ensure that you can quickly restore your site to its previous state. A good web hosting provider will perform regular backups of your site automatically.
According to studies, around 8 percent of hacked WordPress websites are due to weak passwords. However, as the largest self-hosted blogging tool in the world, WordPress has a responsibility to its users to keep their information safe. One way it does this is by natively offering two-factor authentication (2FA).
Two-factor authentication is an extra layer of security that requires not only a username and password but also something that the user has on them, like a phone. This makes it much harder for someone to hack into a WordPress account, even if they have the login credentials.
WordPress offers 2FA through several different methods, including SMS text messages, email, and authenticator apps. Which method you choose is up to you, but we recommend using an authenticator app like Authy or Google Authenticator.
The reason why WordPress powers millions of websites and blogs is its user-friendliness and free plugins. Although WordPress is good at adding new features and constantly issues security patches, zero-day vulnerabilities can be a calamity.
Therefore, always keep your plugins up to date because newer versions of plugins often fix security vulnerabilities that older versions had. Outdated plugins can cause compatibility issues with other plugins or with WordPress itself.
Additionally, newer versions of plugins usually have new features and improvements that can make your site run better. So next time you see a plugin update available, don’t ignore it – go ahead and update!
There are a few reasons webmasters might want to change the default WordPress login URL. By doing so, you can help keep your site more secure from hackers and bots who try to gain access by brute force. Additionally, it can also deter casual users from trying to snoop around areas of your site they shouldn’t be.
If you’re running a membership site or online community, you may also want to change the login URL to something more branded and memorable for your users. By making it easy for them to find and login, you can reduce frustration and increase adoption.
Whatever your reason for wanting to change the WordPress login URL, it’s actually quite easy to do. There are a few different methods you can use, including plugins and editing code directly.
As a website owner, it’s important to make sure that your site is secure. One way to do this is by using a WordPress login limit plugin. This type of plugin will help to protect your site by limiting the number of failed login attempts.
There are many benefits of using a WordPress login limit plugin. By limiting the number of failed login attempts, you can help to prevent hackers from gaining access to your site. Additionally, this plugin can also help to improve the security of your password.
If you’re looking for a way to improve the security of your website, then we recommend that you consider using a WordPress login limit plugin.
Using a security plugin is a must. There are many security plugins available for WordPress, but not all of them are created equal. Do some research and find a plugin that suits your needs. (We recommend looking into Wordfence or Sucuri.)
Once you’ve found a plugin, install it and activate it. Follow the instructions on the plugin’s settings page to configure it properly.
Most security plugins will offer features like blocking IP addresses, two-factor authentication, malware scanning, and more. Choose the features that are most important to you and make sure they’re enabled.
Keep your security plugin up to date by installing new versions when they’re released.
If you’re planning on giving someone else access to your WordPress admin panel, there are a few security precautions you should take first.
For starters, be sure to create a separate user account for the person to whom you’re granting access. That way, if their account is ever compromised, your main admin account will remain safe.
Next, be sure to set strong passwords for both your main admin account and the new user account. Use a combination of letters, numbers, and symbols to make it as difficult as possible for hackers to guess.
Malicious actors are continuously coming up with new ways to use a company’s online presence against them, while cyber security specialists are always coming up with new ways to resist them.
This is the never-ending cycle of cybersecurity, and we’re all trapped in its center. Your WordPress site is just like any other website on the internet when it comes to cyber-attacks. However, by following the above-recommended tips and hacks, you can secure your WordPress website from cyber criminals or at least reduce the risk of being attacked.
As the internet becomes increasingly integral to daily life, website security is more important than ever. Hackers can gain access to sensitive information, like credit card numbers and social security numbers, through websites with weak security. This can lead to identity theft and financial fraud.
Your website’s CMS (content management system) works as the backbone of your entire setup. The most prominent CMS today is WordPress which is being used by over 455 million across the globe. Naturally, WordPress is a lucrative target for cybercriminals and highlights the fact why WordPress security should never be ignored.
WordPress or another other CMS, while 100% security may be a myth, there are a few things you can do to ensure your website is secure from external and internal threats.
A website is a powerful tool that can help businesses of all sizes reach new customers and grow. However, a website is only as secure as the hosting provider that it uses. That’s why it’s important to choose a secure website hosting provider when setting up your website. Here are two things to look for in a secure website hosting provider:
1. Industry-Leading Security Measures: A good web hosting provider will have industry-leading security measures in place to protect your website from hackers and other online threats. This includes things like firewalls, DDoS protection, and malware scanning.
2. Regular Backups: In the event that your website is hacked or compromised, regular backups will ensure that you can quickly restore your site to its previous state. A good web hosting provider will perform regular backups of your site automatically.
According to studies, around 8 percent of hacked WordPress websites are due to weak passwords. However, as the largest self-hosted blogging tool in the world, WordPress has a responsibility to its users to keep their information safe. One way it does this is by natively offering two-factor authentication (2FA).
Two-factor authentication is an extra layer of security that requires not only a username and password but also something that the user has on them, like a phone. This makes it much harder for someone to hack into a WordPress account, even if they have the login credentials.
WordPress offers 2FA through several different methods, including SMS text messages, email, and authenticator apps. Which method you choose is up to you, but we recommend using an authenticator app like Authy or Google Authenticator.
The reason why WordPress powers millions of websites and blogs is its user-friendliness and free plugins. Although WordPress is good at adding new features and constantly issues security patches, zero-day vulnerabilities can be a calamity.
Therefore, always keep your plugins up to date because newer versions of plugins often fix security vulnerabilities that older versions had. Outdated plugins can cause compatibility issues with other plugins or with WordPress itself.
Additionally, newer versions of plugins usually have new features and improvements that can make your site run better. So next time you see a plugin update available, don’t ignore it – go ahead and update!
There are a few reasons webmasters might want to change the default WordPress login URL. By doing so, you can help keep your site more secure from hackers and bots who try to gain access by brute force. Additionally, it can also deter casual users from trying to snoop around areas of your site they shouldn’t be.
If you’re running a membership site or online community, you may also want to change the login URL to something more branded and memorable for your users. By making it easy for them to find and login, you can reduce frustration and increase adoption.
Whatever your reason for wanting to change the WordPress login URL, it’s actually quite easy to do. There are a few different methods you can use, including plugins and editing code directly.
As a website owner, it’s important to make sure that your site is secure. One way to do this is by using a WordPress login limit plugin. This type of plugin will help to protect your site by limiting the number of failed login attempts.
There are many benefits of using a WordPress login limit plugin. By limiting the number of failed login attempts, you can help to prevent hackers from gaining access to your site. Additionally, this plugin can also help to improve the security of your password.
If you’re looking for a way to improve the security of your website, then we recommend that you consider using a WordPress login limit plugin.
Using a security plugin is a must. There are many security plugins available for WordPress, but not all of them are created equal. Do some research and find a plugin that suits your needs. (We recommend looking into Wordfence or Sucuri.)
Once you’ve found a plugin, install it and activate it. Follow the instructions on the plugin’s settings page to configure it properly.
Most security plugins will offer features like blocking IP addresses, two-factor authentication, malware scanning, and more. Choose the features that are most important to you and make sure they’re enabled.
Keep your security plugin up to date by installing new versions when they’re released.
If you’re planning on giving someone else access to your WordPress admin panel, there are a few security precautions you should take first.
For starters, be sure to create a separate user account for the person to whom you’re granting access. That way, if their account is ever compromised, your main admin account will remain safe.
Next, be sure to set strong passwords for both your main admin account and the new user account. Use a combination of letters, numbers, and symbols to make it as difficult as possible for hackers to guess.
Malicious actors are continuously coming up with new ways to use a company’s online presence against them, while cyber security specialists are always coming up with new ways to resist them.
This is the never-ending cycle of cybersecurity, and we’re all trapped in its center. Your WordPress site is just like any other website on the internet when it comes to cyber-attacks. However, by following the above-recommended tips and hacks, you can secure your WordPress website from cyber criminals or at least reduce the risk of being attacked.
Nov 17 2022
If you’re like most modern organizations, you rely on third-parties to help you run and grow your business. Yet the vendors, partners and suppliers that make up your supply chain are also a significant component of your cloud environment attack surface. While you can’t (and shouldn’t) cut third-parties off completely, you can (and should) enforce the principle of least privilege when providing them with permissions into your single and multicloud environment. Read on to learn how to implement this essential modern security practice and tips for getting started.
Third parties, including suppliers, contractors, vendors, partners and even your cloud provider are a fundamental part of your organization’s business ecosystem. They help with any and all aspects of business growth, from engineering and IT to marketing and business development, and legal and strategy. Many of these third parties have other third parties they work with to help run their own businesses, and so on. This natural business reality creates a supply chain of companies and networks interlinked in various ways.
But all this help has a dark side: third parties and supply chains create considerable vulnerabilities in your cloud environment. According to IBM’s 2022 Cost of a Data Breach Report, 19% of breaches were caused by a supply chain compromise. The average total cost of a third-party breach was $4.46M, which is 2.5% higher than the average cost of a breach. In addition, identifying and containing third-party breaches took an average of 26 days longer compared to the global average for other kinds of breaches.
The vulnerability of third parties arises from the different security hygiene practices and controls each business in your ecosystem employs. In many cases, their standards are less stringent than your own, creating inconsistency and an increase in their relative security vulnerability.
In May 2021, U.S. President Biden dedicated an entire section in his monumental CyberSecurity Executive Order to the hardening of the supply chain and mitigation of risks of vendor attacks. The order states that “the development of commercial software often lacks transparency, sufficient focus on the ability of the software to resist attack, and adequate controls to prevent tampering by malicious actors.” In short, the order notes that since it is easier for an attacker to breach, third-party software is more susceptible to exploitation.
Third-party vulnerabilities are not just software-related. Security practices that are different, mismatched and/or below your organization’s standard also create vulnerabilities. For example, some third parties may not practice password hygiene. In other cases, they may be reusing credentials or accidentally misconfiguring their environments.
Once they gain access to your supplier, attackers may find it easier to access your environments as well. Unlike malicious attackers, for which organizations are on the alert, organizations tend to treat third-parties as trusted entities. As such, third-parties are granted access and control over sensitive resources. Sometimes, this access is required for them to perform their work. Too often, though, permissions are intentionally or unintentionally over-privileged – due to manual errors, oversight or not knowing better. As a result, attackers that access your vendors can exploit this trust and breach your environments as well. Overprivileged permissions put your critical systems and data at risk, and can disrupt your compliance with regulations.
In the cloud, excessive trust of third parties and supply chain actors is riskier than on-premises environments – not just because one’s guard is down but due to the nature of cloud architecture and how it differs from on-premises.
On-premises, local servers and components enabled delineating network borders and implementing security controls to protect those borders, like firewalls. But in the cloud, infrastructure is distributed and resides on public infrastructure, making surrounding it with security controls impossible. This means that previously used security tactics and solutions, like third-party PAMs, are no longer helpful.
In addition, the distributed nature of the cloud, alongside the workforce’s reliance on cloud-based resources for their work (e.g, on SaaS apps), has changed connectivity needs. Businesses going through cloudification now rely on identities and credentials as the main means for providing access to company resources, making identity the new security perimeter.
It’s not only human users that require identities for access. The cloud has transformed many architectures from monoliths to microservices to support more development agility. These cloud services now also need digital identities as their main means for resource access. In some cases even your cloud provider can be a third party with access, often authorized, to your environment. Still, maintaining a list of CSP-managed accounts can be a difficult task.
In the cloud, IT, DevOps, Security and DevSecOps are now managing thousands of new digital organizational identities, each with a complex sub-set of permissions that determines which resources they can access and the actions they can take on those resources. In the recent 2022 Trends in Security Digital Identities survey, by the independent group Identity Defined Security Alliance (IDSA), 52% of identity and security professionals identified cloud adoption as the driver of the growth of organizational identities.
Managing and monitoring these identities and their permissions is extremely complicated. The combination of the high volumes of identities and the intricacies of their permissions makes it almost impossible to avoid oversights and manual errors.
This extreme difficulty in avoiding permissions error has dangerous security implications. Verizon’s 2022 Data Breach Investigations Report (DBIR) finds that credentials are the number one organizational security weakness. When it comes to third-parties, the same research finds that the use of stolen credentials and ransomware are the top two “action varieties” leading to incidents. Per Ermetic research, ransomware potential is the cause of misconfigured identities, publicly exposed machines, risky third-party identities and risky access keys. In other words, third-party credentials are a focus point of violation for attacking companies and breaching their data. Protecting third-party credentials needs to be part of everyone’s security strategy.
Businesses operating in a legacy-security mindset tend to block any risk or threat. But modern security strategies require security teams to act as business enablers. This means security needs to be maintained without slowing down business productivity and performance. Overcoming the third-party business vs. security dilemma is challenging, since while the supply chain is an inherent risk, it is also essential to a business’s success. Shutting down third-party operations is equivalent to shutting down business operations.
But the risk speaks for itself: third-party access in the cloud requires a dedicated security approach to permissions management. Fortunately, the principle of least-privilege is the modern security practice that can answer identity-management complexity – including that of third parties – in the cloud. By minimizing user and service permissions to only those deemed necessary for business operations, organizations can reduce their blast radius and attack surface in case of an attack. When it comes to third parties, the principle of least privilege – including its implementation via tools like Just in Time access – enables providing third parties only with the necessary access for the business while minimizing the risk these entities pose.
Let’s look into the various options for managing the risk of third-party permissions with least privilege.
To secure third-party access to resources, IT and security need to find a way to keep track of all identities and their permissions. Some businesses rely on manual tracking in spreadsheets or other similar means. This quickly turns into long lists of identity names, the resources they have access to and their permissions.
However, manual maintenance in spreadsheets or by other means cannot capture the complexity of permissions management requirements. Many identities have access to a large number of resources, each with different authorization requirements. These all need to be meticulously tracked – spreadsheets are not equipped for presenting this information in a consumable fashion.
In addition, permissions can be inherited. This means that if service A has permissions to control service B, and service B has permissions for service C, service A will have permissions for service C. This creates a complex chain of permissions that is hard to create and visualize manually.

Finally, permissions need to be continuously monitored. Creating a one-time picture of permissions does not reflect the mercurial nature of the cloud or legitimate needs that come up requiring elevated or expanded permissions be granted for a certain amount of time.
Scanning and reviewing all these permissions takes time and concentration, which many IT and security teams don’t have. In addition, understanding the complexity, depth and how permissions are intertwined requires cloud security expertise, which not all security and IT teams have or have had time to develop. Even if they did, is this the best use of their time?
Here’s an example of one JSON permissions doc. Imagine having to comb through thousands of these and identifying any errors or issues:

Constantly updating manual spreadsheets while also being able to pinpoint any excessive or toxic permissions requires painstaking tracking, which resembles the type of analysis a machine would perform, not a human. The required level of detail, the scope of data and the speed of decision-making required when managing and monitoring the principle of least privilege screams “automation.” Doing so in a multicloud, let alone single cloud, environment is daunting.
Here are six tips for ensuring your automated mechanism can protect you from third-party risk with least privilege:
As we’ve established, permissions in the cloud are convoluted by nature. An automated, multicloud monitoring mechanism will check third-party credentials for excessive permissions or toxic combinations and identify if these permissions violate the principle of least privilege by providing them with the unnecessary ability to access sensitive data and modify infrastructure. This information will be visualized by its risk severity, and any attacker reconnaissance capabilities will be highlighted. The evaluation of severity will take into account any risk offsetting covered by other policy definitions, including network related, along the permissions chain.
Modern security strategies are business enablers and growth enthusiasts. Therefore, security controls need to be applied in a contextual manner. Rather than blocking any potentially vulnerable activity, actions need to be implemented intelligently. With permissions, it is essential to provide context of permissions scope. Not all third-party capabilities are dangerous for the business. Excessive permissions, i.e., those that exceed the principle of least-privilege, are the ones that should be mitigated. Automated security controls provide mechanisms for marking accounts and services as trusted, reducing false alerts.
Engineering, IT and security teams are busy and have alert fatigue. A helpful automated solution does not just highlight the problem but also helps solve it. Instead of adding more tasks to the teams’ full plate, take care to choose a solution that can provide a recommended substitute policy and auto-remediate into your organization’s workflows, and even shift left with optimized policies through infrastructure as code, while leaving more advanced issues to human judgment.
Guardrails limit the actions an identity can perform. This helps minimize the blast radius by capping the potential of what a user or principal can do. Determining automated guardrails are especially important with third-parties, since it is often easier for IT teams to provide them with excessive access or accepting the cloud vendor’s default configurations rather than having to go into the weeds and figuring out how to limit their permissions to the resources they actually need.
Automation should support you, not make your daily flow more difficult. A helpful automated solution will integrate with the security and engineering teams’ workflows. This can be done through easy to understand dashboards, clear instructions, integrations into the CI/CD cycle and integrations with tools like Slack or PagerDuty.
JIT (Just-in-Time) access is a security principle that provides access to users for a limited period of time and then revokes it. JIT is useful for when users need permissive entitlements to complete a certain task, such as when developers need to fix a bug in production.
A secure automated solution will support JIT access for third-parties as well. That way, if your vendor needs to access a sensitive environment for an important work-related issue, you can provide them with such access without leaving attackers with a permanent window of opportunity for reconnaissance.
From a business perspective, third parties are as much a part of your business as any internal department. But from a security perspective, these entities need to be approached intentionally and with strategic caution. Third parties carry huge risks since their security practices are beyond your control.
The answer to managing these vulnerabilities is through an automated security solution that enforces least privilege and JIT access. Automated permissions management and monitoring reduces access risk by assigning third-parties, including developers, with only the access they need. This is the best way to balance and ensure business continuity and security in your cloud.
The post 6 Tips for Understanding 3rd-Party Risk in the Cloud appeared first on Ermetic.

Nov 16 2022
“By implementing sound #management of our #risks and the threats and opportunities that flow from them we will be in a stronger position to deliver our organisational objectives, provide improved services to the community, achieve better value for money and demonstrate compliance with the Local Audit and Accounts Regulations. #Riskmanagement will therefore be at the heart of our good management practice and corporate governance arrangements.”

Nov 15 2022

As we continue to rely on technology more and more, we should also be increasingly thinking about protection. According to Cyber Security Hub, two-thirds of companies are spending more on cybersecurity in 2022 than last year — a pattern that should only continue.
On the heels of National Cybersecurity Awareness Month, it is the perfect time for business leaders and organizations to consider the cybersecurity safeguards they use to protect sensitive information. Cybersecurity can be a complex task for many organizations. Businesses, educational institutions and government entities often struggle to navigate the available options. Aside from IT professionals, finding the right solution requiressubject matter experts, a group of leaders who represent different lines of business, C-suite representatives and a thorough risk assessment to determine where to strike a balance between security and productivity.
Security is a constant discipline of due care and due diligence over time. It requires a mindset shift for employees and extends far beyond computers. Printers, scanners, fax machines, document management systems and other hardware and software solutions must contain the latest security features as well. While updating these devices may not be top of mind, neglecting them can pose a serious threat to your organization if compromised.
If you are just getting started, or need a refresher on cybersecurity, here are some of the first steps you should take:
Layered security Standard Requirements
Nov 14 2022
BatLoader has spread rapidly to roost in systems globally, tailoring payloads to its victims.

BatLoader has spread rapidly to roost in systems globally, tailoring payloads to its victims.
Nov 14 2022

Going into 2023, cybersecurity is still topping the list of CIO concerns. This comes as no surprise. In the first half of 2022, there were 2.8 billion worldwide malware attacks and 236.1 ransomware attacks. By year end 2022, it is expected that six billion phishing attacks will have been launched.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
Here are eight top security threats that IT is likely to see in 2023.
Malware is malicious software that is injected into networks and systems with the intention of causing disruption to computers, servers, workstations and networks. Malware can extract confidential information, deny service and gain access to systems.
IT departments use security software and firewalls to monitor and intercept malware before it gains entry to networks and systems, but malware bad actors continue to evolve ways to elude these defenses. That makes maintaining current updates to security software and firewalls essential.
Ransomware is a type of malware. It blocks access to a system or threatens to publish proprietary information. Ransomware perpetrators demand that their victim companies pay them cash ransoms to unlock systems or return information.
So far in 2022, ransomware attacks on companies are 33% higher than they were in 2021. Many companies agree to pay ransoms to get their systems back, only to be hit again by the same ransomware perpetrators.
Ransomware attacks are costly. They can damage company reputations. Many times ransomware can enter a corporate network through a channel that is open with a vendor or a supplier that has weaker security on its network.
One step companies can take is to audit the security measures that their suppliers and vendors use to ensure that the end-to-end supply chain is secure.
Almost everyone has received a suspicious email, or worse yet, an email that appears to be legitimate and from a trusted party but isn’t. This email trickery is known as phishing.
Phishing is a major threat to companies because it is easy for unsuspecting employees to open bogus emails and unleash viruses. Employee training on how to recognize phony emails, report them and never open them can really help. IT should team with HR to ensure that sound email habits are taught.
In 2020, 61% of companies were using IoT, and this percentage only continues to increase. With the expansion of IoT, security risks also grow. IoT vendors are notorious for implementing little to no security on their devices. IT can combat this threat by vetting IoT vendors upfront in the RFP process for security and by resetting IoT security defaults on devices so they conform to corporate standards.
If your organization is looking for more guidance on IoT security, the experts at TechRepublic Premium have put together an ebook for IT leaders that is filled with what to look out for and strategies to deal with threats.
Disgruntled employees can sabotage networks or make off with intellectual property and proprietary information, and employees who practice poor security habits can inadvertently share passwords and leave equipment unprotected. This is why there has been an uptick in the number of companies that use social engineering audits to check how well employee security policies and procedures are working. In 2023, social engineering audits will continue to be used so IT can check the robustness of its workforce security policies and practices.
An IBM 2022 study found that 35% of companies were using AI in their business and 42% were exploring it. Artificial intelligence is going to open up new possibilities for companies in every industry. Unfortunately, the bad actors know this, too.
Cases of data poisoning in AI systems have started to appear. In a data poisoning, a malicious actor finds a way to inject corrupted data into an AI system that will skew the results of an AI inquiry, potentially returning an AI result to company decision makers that is false.
Data poisoning is a new attack vector into corporate systems. One way to protect against it is to continuously monitor your AI results. If you suddenly see a system trending significantly away from what it has revealed in the past, it’s time to look at the integrity of the data.
Organizations are adopting new technology like biometrics. These technologies yield enormous benefits, but they also introduce new security risks since IT has limited experience with them. One step IT can take is to carefully vet each new technology and its vendors before signing a purchase agreement.
How much security is enough? If you’ve firewalled your network, installed security monitoring and interception software, secured your servers, issued multi-factor identification sign-ons to employees and implemented data encryption, but you forgot to lock physical facilities containing servers or to install the latest security updates on smartphones, are you covered?
There are many layers of security that IT must batten down and monitor. IT can tighten up security by creating a checklist for every security breach point in a workflow.

Nov 14 2022
Data-deletion service’s patent covers removing personal information such as geolocation, biometrics, and phone records from a vehicle by using a user-computing device
— Privacy4Cars, the first privacy-tech company focused on solving the privacy and security issues posed by vehicle data to protect consumers and automotive businesses, announced today that it has secured a new patent, further expanding its patent coverage for removing privacy information from a vehicle by using a user computing device. This patent grant marks the fourth patent that the U.S. Patent & Trademark Office has awarded to Privacy4Cars in the past three years and provides further evidence that the company is the leading innovator in the vehicle data privacy and security field.
Since its launch in 2018, Privacy4Cars has emerged as the industry standard across auto finance companies (including captives, national and regional banks, auto lenders, and credit unions), fleets and fleet management companies, and franchised and independent dealerships. Many of today’s top companies in the automotive space — including the three largest OEM’s captives — have adopted the data-deletion service powered by the Privacy4Cars platform, and a growing number of industry associations have begun speaking out about the need to clear personal information from cars, and tapping Privacy4Cars as a resource to educate members.
“Used vehicles are akin to large, unencrypted hard drives full of consumers’ sensitive Personal Information, including identifiers, geolocation, biometrics, and phone records,” said Andrea Amico, CEO and founder of Privacy4Cars. “This creates service, reputation, and increasingly major regulatory challenges, including the obligations companies face under the new Safeguards Rule (coming into effect on Dec. 9, 2022) and a host of existing and new state laws. At the same time, federal and local agencies are increasingly concerned about the personal information vehicles capture and store — which is driving more and more auto businesses to look for reliable solutions to simply and effectively delete data from vehicles while creating by design detailed compliance logs that prove their efforts,” he continued. “This new patent demonstrates Privacy4Cars’ commitment to meet the growing compliance and service needs of our partners. Privacy4Cars has established itself as the clear leader in the vehicle privacy space and companies increasingly recognize the superior efficiency, effectiveness, and compliance outcomes our proprietary solution offers, making Privacy4Cars the only obvious choice”.
Privacy4Cars’ newly awarded U.S. Patent No. 11,494,514 expands the scope of patent protection for the vehicle data privacy and security innovations of Privacy4Cars’ U.S. Patent No. 11,256,827, U.S. Patent No. 11,157,648 and U.S. Patent No. 11,113,415. The new patent covers the use of a user computing device to remove privacy information from a vehicle and to create feedback about the information removal activity, including deletion logs for use in legal compliance applications.
Privacy4Cars is currently available in the US, Canada, UK, EU, Middle East, India, and Australia, and plans to further expand its geographical reach to address the growing number of countries that have comprehensive privacy and data security laws. Privacy4Cars is available to consumers as a free-to-download app, and to businesses as a subscription service. Businesses can use Privacy4Cars’ stand-alone app or choose to integrate Privacy4Cars’ Software Development Kit to easily embed its patented data deletion solution as a feature inside their own apps.
For more information about Privacy4Cars, please visit: https://privacy4cars.com.ABOUT PRIVACY4CARS
Privacy4Cars is the first and only technology company focused on identifying and resolving data privacy issues across the automotive ecosystem. Our mission, Driving Privacy, means offering a suite of services to expand protections for individuals and companies alike, by focusing on privacy, safety, security, and compliance. Privacy4Cars’ patented solution helps users quickly and confidently clear vehicle users’ personal information (phone numbers, call logs, location history, garage door codes, and more) while building compliance records. For more information, please visit: https://privacy4cars.com/
SOURCE: Privacy4Cars
Nov 14 2022
A new version of ISO 27001 was published this week, introducing several significant changes in the way organisations are expected to manage information security.
The Standard was last revised almost a decade ago (although a new iteration of the supplementary standard ISO 27002 was published in February 2022), meaning that the release of ISO 27001:2022 has been much needed and highly anticipated.
The good news for organisations is that ISO 27001:2022 doesn’t drastically overhaul their compliance requirements. There are new requirements on planned changes and how your organisation should deal with them, as well as a greater focus on how you must deal with the needs and expectations of interested parties.
Annex A of ISO 27001 now refers to the updated information security controls in ISO 27002:2022, and the Standard requires organisations to document and monitor objectives.
It also aligns its terminology with that used across other ISO management system standards.
Another notable aspect of its terminology is that ISO 27002:2022 no longer refers to itself as a “code of practice”. This better reflects its purpose as a reference set of information security controls.
However, the most significant changes with the 2022 version of ISO 27002 are in its structure. It is no longer divided into 14 control categories, and is instead split into four ‘themes’: organisational, people, physical and technological.
Meanwhile, although the 2022 version of ISO 27002 is significantly longer than its predecessor, the total number of controls has decreased from 114 to 93.
This is because many of its controls have been reordered and merged. Only 35 controls are unchanged, while 11 completely new requirements have been added. These are:
The new and amended controls are also categorised according to five types of ‘attribute’: control type, operational capabilities, security domains, cybersecurity concepts and information security properties.
This change is intended to make it easier to highlight and view all controls of a certain type, such as all preventive controls, or all controls related to confidentiality.
The introduction of ISO 27001:2022 won’t have an immediate effect on organisations that are currently certified to ISO 27001:2013 or are in the process of achieving certification.
For the time being, organisations should continue to follow the 2013 version of the Standard. This means, for example, that the SoA (Statement of Applicability) should refer to the controls listed in Annex A of ISO 27001:2013, while the 2022 version of the Standard should be used only as a reference.
Indeed, the reason that the updated version is being published now is to give organisations time to familiarise themselves with the new controls before embarking on an implementation project.
The controls listed in ISO 27002:2022 can be considered an alternative control set that you will have to compare with the existing Annex A – just as you would with any other alternative control set.
ISO 27002:2022 has an annex that compares its controls with the 2013 iteration of the Standard, so this should be relatively straightforward.
There is a three-year transition period for certified organisations to revise their management system to conform to a new version of a standard, so there will be plenty of time to make the necessary changes.

However, it’s never wise to put off the planning process until the last minute. Implementation will take several months, and it’s worth knowing what’s expected of you as soon as possible.
You can begin by reading the Standard for yourself. You can purchase a digital copy of ISO 27001:2022 from our website, and we recommend comparing the updated version to the 2013 edition and your current compliance practices to determine what adjustments you’ll have to make.
If you’re unsure how to proceed, our team of experts are here to help. Having led the world’s first ISO 27001 certification project, we understand what it takes to implement the Standard.
Speak to one of our experts for more information on how we can support you.
Nov 10 2022
Nov 09 2022
nformation Security Risks assisted Business models for banking & financial services(BFS) institutions have evolved from being a monolithic banking entity to multi-tiered service entity.
What this means to BFS companies is that they need to be more updated and relevant with regards to technology & the quality of all services provided to their clients. The most opted methodology to do that today is by means of outsourcing services to vendors & 3rd parties.
Though outsourcing is cost beneficial to companies, this approach comes with its own set of drawbacks. It is judicious to say that every outsourcing enterprise should be aware of the risks that vendors bring to the table.
Though vendors bring in a lot of operational Information Security Risks depending on the business engagement, a methodology to manage only the 3rd party Information Security Risks are discussed here.
Just to provide a sense of the impact that vendor Information Security Risks brings to organizations, below are some of the facts from surveys conducted by Big 4 consulting companies like PwC & Deloitte.
“The Number of data breaches attributed to 3rd party vendors has increased by 22% since 2015”- Source PwC
According to Deloitte “94.3% of executives have low to moderate confidence in their third-party risks management tools & technology, and 88.6% have low to moderate confidence in the quality of the underlying Information Security Risks management process” .
A perfect place to begin is with the sourcing team and /or procurement team depending on how your organization is set up. In an ideal world, these teams are expected to have an inventory of all vendors, 3rd parties & Partners of your organization.
Once we have this inventory in place, the IT vendor risk management (IT- VRM) team needs to segregate the IT vendors from the non-IT ones. This is a onetime activity. For future needs, it is recommended to have the sourcing team segregate vendors basis on their business engagement (IT vs Non-IT).

One of the simplest & efficient way to understand your vendors is by having a scoping checklist, that details the vendor business with your organization, kind of data touchpoints & exchanges, kind of Information Security Risks that your organization is exposed by this outsourced business.
This information is usually available with the vendor manager representing your organization in the vendor relationships.
Below is the list of Information Security Risks pointers (not limited to) that you might want to consider asking your vendor manager.
For understanding the level of assessment to be performed with the vendor, you will need to understand the vendor’s business operating model.
Below is an indicative list of themes that you might want to discuss with vendor manager to understand the scope of the vendor assessment.

Nov 02 2022
33N Ventures is fundraising €150 million for investing in cybersecurity and infrastructure software companies across Europe, Israel, and the US. The fund will mostly target investments at Series A and B, with an average ticket size of around €10 million, and has an investment capacity of €20 million already committed by Alantra and its strategic partners.
Co-founders and managing partners Carlos Alberto Silva and Carlos Moreira da Silva have made more than 20 investments in cybersecurity and infrastructure software over the past 10 years, across Europe, Israel and the US – including most notably Arctic Wolf.
In this Help Net Security interview, they discuss the cybersecurity investment landscape in Europe, the strategies for finding the right companies, and more.
Carlos Alberto Silva: There’s no doubt that the US and Israeli startup ecosystems get more attention when it comes to cybersecurity. But that’s not to say there haven’t been success stories in Europe. Take IriusRisk, for example: the automated threat modeling platform raised a $28.7M Series B round just a few weeks ago.
By rights, Europe should be a world leader in this space. Talent is abundant here, and there is a very large addressable market. The challenge for companies in Europe is that, unlike their peers in the US and Israel, they often don’t get the specialized support they need to compete.
While there are a few specialized funds in Europe, most focus naturally only on one country or region and tend to invest in very early-stage companies. As a result, most entrepreneurs face the choice of working with a US investor (that lacks on-the-ground local knowledge) or working with a generalist fund that may not be able to open the right doors for them.
That’s why we’ve decided to create a fund with a truly pan-European focus. There’s such a large opportunity here for firms that are underserved by the current market. We’ll still be investing in some companies in the US and Israel – simply put, there are some amazing opportunities that we just don’t want to miss out on – but we’re most excited about capitalising on this relatively untapped opportunity in Europe.
Carlos Alberto Silva: Given that we only launched the fund last week, we’ve not run into too many challenges yet! That being said, of course, the economic climate is not the best. This is a challenge that every venture capital fund and company must face.
Cybersecurity as a whole is also well insulated from the economic downturn. That’s because strong cybersecurity is not a ‘nice-to-have’ – but critical. That’s not going to change – from digital transformation to national security, cyber will continue being a top priority for governments, institutions, companies, and investors across the globe, and the market is expected to reach $162 billion in 2022, with robust annual double-digit growth forecast for the coming years – and so the companies we’ll be looking at have some in-built resilience.
Carlos Moreira da Silva: This is not generally something we struggle with. This is probably because we follow a thesis-driven approach that means we spend a lot of time looking at which spaces we want to cover before making any investment decisions.
Of course, we stay up to date with the industry, look at all publicly available sources, and attend the most relevant cybersecurity events across Europe, Israel, and the US. This is all fairly common sense.
But we do rely heavily on our proprietary network of close VCs and advisors. Our network is always totally invaluable when we are looking to identify the best leads for future investments. Our strategic advisors – including leading entrepreneurs, experts, and cybersecurity decision-makers such Brian NeSmith (Arctic Wolf), Eyal Hayardeny (Reblaze), Nuno Sebastião (Feedzai), and Pierre Polette (Hackuity) – all founders of companies we’ve invested in in the past – possess an incredible depth and breadth of sector-specific knowledge and experience that, added to our own, really helps us identify and support the founders and companies with the biggest breakthrough and scaling potential.
We spend a long time talking to prospective investee companies, ideally as early in their journey as possible, and working out where we can help them. If we can make an introduction to a potential customer, for example, we will do so even before we have made any investment. We’ve worked hard to build a reputation in the industry for being supportive of the whole industry – that’s really important to us.
Carlos Alberto Silva: For most first-time funds the process of identifying the right companies to invest in across such a large geographic area would be difficult. But our team has been together for many years now. We may be a first-time fund, but we’re far from a first-time team.
We know this space well and we have a strong network that reaches across the US, Europe, and Israel. In fact, much of the research you refer to has in effect already been done. We already have a list of companies that we’re interested in, and in many cases have already started the conversation.
We want to back visionary companies in emerging sectors. We want to invest in those who are the very first or one of the very first to solve a particular problem. In our view, jumping on bandwagons or entering already saturated markets will inevitably lead to meagre returns. Get in on the ground floor and you’ve got a lot more room to grow into.
Carlos Moreira da Silva: Beyond the obvious – how much are they willing to invest – there are a couple of really important things for founders to look at. Firstly, look at their track record. Cybersecurity is a space where deep technical knowledge is really important. Think of it this way: if you have to explain what your company does through metaphors and hand-holding, then they probably aren’t going to be much help beyond providing cash stimulus.
The second thing to look at is their network. Well-connected investors with the right contacts in cybersecurity will prove invaluable. Most venture capital investors will have a long list of contacts. You can pick that up by going to the right events and spending enough time in the space. But the investors that will provide you with real benefit are those who have a long list of friends – with deep and genuine relationships. The right introduction can be game-changing for a company, so it’s vital your investor’s network is robust.
Carlos Moreira da Silva: It may sound obvious, but in our experience, the most important thing for building rapport is having a solid understanding of the business. It is important to be there for the founders during the good times, but especially during the challenging times, when they really need that extra help. Of course, you must understand how the company’s key product or service works.
But beyond that, you must understand everything from the pain points of their customers to the market for talent in their sector to the opportunities for growth. This is not stuff you can pick up overnight, and entrepreneurs are good at picking those with genuine knowledge out from the blaggers.
And, in our case, we can share our global perspective regarding the wider market environment. You can provide an enormous amount of value here.
We also think it helps that we’ve been in their position before. We’re not just investors, we’ve held senior executive roles in cybersecurity companies and effectively built them from the ground up. So, we understand the nuances of the day-to-day running of a business, and that helps us build a foundation of trust – which really is essential to a successful relationship.
