Google Project Zero experts disclosed details of a 5-Year-Old Apple Safari flaw actively exploited in the wild.
Researchers from the Google Project Zero team have disclosed details of a vulnerability in Apple Safari that was actively exploited in the wild.
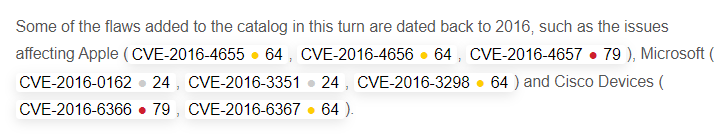
The vulnerability, tracked as CVE-2022-22620, was fixed for the first time in 2013, but in 2016 experts discovered a way to bypass the fix.
“Whenever there’s a new in-the-wild 0-day disclosed, I’m very interested in understanding the root cause of the bug. This allows us to then understand if it was fully fixed, look for variants, and brainstorm new mitigations.” reads the post published by Google Project Zero. “This blog is the story of a “zombie” Safari 0-day and how it came back from the dead to be disclosed as exploited in-the-wild in 2022. CVE-2022-22620 was initially fixed in 2013, reintroduced in 2016, and then disclosed as exploited in-the-wild in 2022.”
Apple has addressed a zero-day vulnerability, tracked as CVE-2022-22620 (CVSS score: 8.8), in the WebKit affecting iOS, iPadOS, macOS, and Safari that may have been actively exploited in the wild.
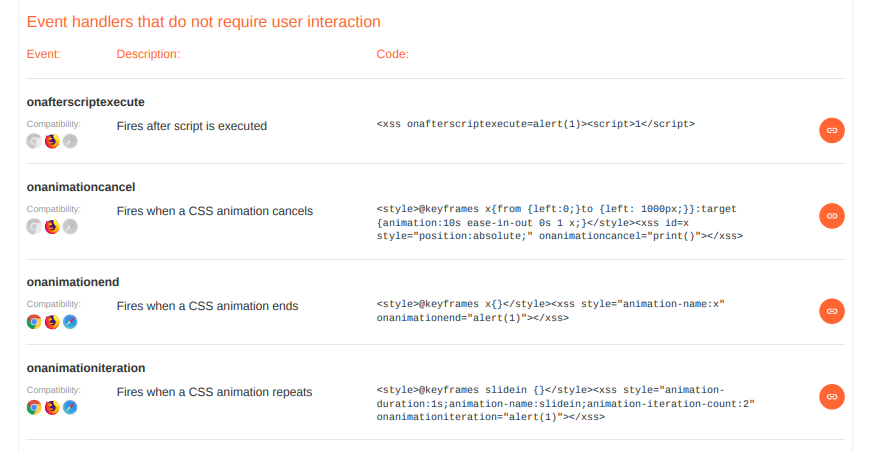
The zero-day vulnerability was fixed by Apple in February, it is a use-after-free issue that could be exploited by processing maliciously crafted web content, leading to arbitrary code execution
“Processing maliciously crafted web content may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited.” reads the security advisory published by Apple. “A use after free issue was addressed with improved memory management.” the google researcher Maddie Stone added. “The vulnerability then continued to exist for 5 years until it was fixed as an in-the-wild 0-day in January 2022.”
The vulnerability was reported by an anonymous researcher and the company addressed it by improving memory management.
Stone analyzed the changes to the software over the years, she started by analyzing the code of the patch shared by Apple and the description of the issue from the security bulletin stating that the vulnerability is a use-after-free.
“Whenever I’m doing a root cause analysis on a browser in-the-wild 0-day, along with studying the code, I also usually search through commit history and bug trackers to see if I can find anything related. I do this to try and understand when the bug was introduced, but also to try and save time.” she said.
The researcher noticed that the commits dated October 2016 and December 2016 were very large, she discovered that the commit in October changed 40 files with 900 additions and 1225 deletions. The commit in December changed 95 files with 1336 additions and 1325 deletions.
“Usually when we talk about variants, they exist due to incomplete patches: the vendor doesn’t correctly and completely fix the reported vulnerability. However, for CVE-2022-22620 the vulnerability was correctly and completely fixed in 2013. Its fix was just regressed in 2016 during refactoring. We don’t know how long an attacker was exploiting this vulnerability in-the-wild, but we do know that the vulnerability existed (again) for 5 years: December 2016 until January 2022.” concludes the expert. “There’s no easy answer for what should have been done differently. The developers responding to the initial bug report in 2013 followed a lot of best-practices.”

The Art of Mac Malware: The Guide to Analyzing Malicious Software
DISC InfoSec
#InfoSecTools and #InfoSectraining











![CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY: Actions Needed to Ensure Organizational Changes Result in More Effective Cybersecurity for Our Nation by [United States Government Accountability Office]](https://m.media-amazon.com/images/I/51FIzAXr-CL._SX260_.jpg)