Defenders Coordinate Slowly. Adversaries Move at Machine Speed.
Microsoft just confirmed what every CISO has been quietly bracing for:
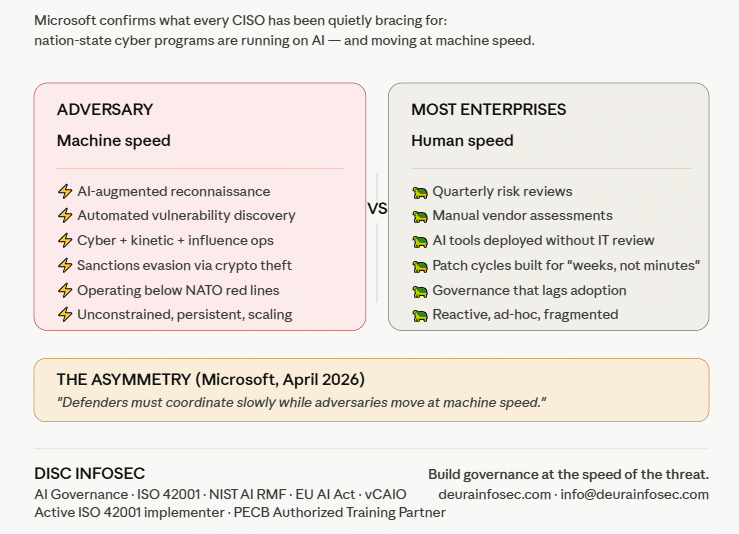
Nation-state cyber programs are now running on AI — and they’re moving at machine speed.
In a sharp new interview with Help Net Security, Microsoft’s Kaja Ciglic (Senior Director, Cybersecurity Policy & Diplomacy) lays out the three structural shifts of the past three years:
🔻 Cyber is no longer a specialist tool. It’s now a core instrument of state power — sitting alongside military, economic, and diplomatic capabilities.
🔻 Cyber operations are integrated with kinetic warfare, influence ops, and economic pressure. Ukraine. The Middle East. The playbook is no longer “espionage OR disruption.” It’s everything, simultaneously.
🔻 AI and automation have collapsed operational tempo. State actors are scaling reconnaissance, vulnerability exploitation, and influence operations more persistently than ever — and the barrier to sustained activity just dropped.
The most uncomfortable line in the entire interview?
“Defenders must coordinate slowly while adversaries move at machine speed.”
That sentence should be on every boardroom wall.
And here’s where it gets even more interesting for enterprise leaders:
→ North Korea’s cyber program now functions as a state-directed criminal enterprise — crypto theft, supply-chain compromise, illicit IT worker schemes funding state priorities. The clean lines between espionage, crime, and warfare are gone.
→ Sanctions and indictments alone aren’t deterring anyone. Ciglic argues for conditional, reversible economic pressure and holding states accountable for ransomware safe havens.
→ NATO’s Article 5 ambiguity around cyber? Useful — until adversaries learn to operate just below the red line. Which they have.
So what does this mean for you — the CISO, the GRC lead, the board member of a B2B SaaS or financial services firm that isn’t a defense contractor?
It means you are no longer outside the blast radius.
When AI lets nation-state actors scale operations against the entire enterprise software supply chain — your vendors, your SaaS stack, your AI integrations — every organization becomes a soft target. Especially the ones who haven’t governed their AI adoption.
The asymmetry is brutal: ⚡ Adversaries: AI-augmented, machine-speed, unconstrained 🐢 Most enterprises: Quarterly risk reviews, manual vendor assessments, AI tools deployed without IT review
This is exactly the gap DISC InfoSec exists to close.
✅ AI Governance built on ISO 42001, NIST AI RMF, and EU AI Act — not paperwork, but operational control over what your AI systems and vendors are actually doing
✅ Vendor AI assurance — because when nation-state actors target your supply chain, “we have their SOC 2” is not a defense
✅ Active ISO 42001 implementation at ShareVault (M&A virtual data room platform)
✅ PECB Authorized Training Partner — equipping your teams with the same frameworks regulators are now using
✅ vCAIO (virtual Chief AI Officer) services for organizations adopting AI faster than their governance can keep up
✅ Integrated GRC across ISO 27001 + ISO 42001 + NIST — because AI risk and cyber risk are no longer separate disciplines
The threat actors are using AI to compress their attack cycles from weeks to minutes.
Your governance program needs to keep up.
📖 Read Ciglic’s full interview: https://www.helpnetsecurity.com/2026/04/24/kaja-ciglic-microsoft-nation-state-cyber-programs/
📩 Ready to build governance that operates at the speed of the threat? DM me or reach out at info@deurainfosec.com
The adversary already adopted AI. The question is whether your defense did.
#AIGovernance #ISO42001 #NISTAIRMF #EUAIAct #CISO #NationStateThreats #CyberSecurity #AIRiskManagement #VendorRisk #SupplyChainSecurity #vCAIO #vCISO #BoardGovernance #CyberPolicy #AICompliance
The AI Governance Quick-Start: Defensible in 10 Days, Not 4 Quarters
DISC InfoSec is an active ISO 42001 implementer and PECB Authorized Training Partner specializing in AI governance for B2B SaaS and financial services organizations.
AI Vulnerability Scorecard: Discover Your AI Attack Surface Before Attackers Do
Your Shadow AI Problem Has a Name-And Now It Has a Score
Most AI Security Tools Won’t Pass an Audit. Here’s a 15-Minute Way to Find Out.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
- The One Security Book That Got Louder With Every Passing Year
- Microsoft Just Made AI Agent Security a CI/CD Problem — Here’s Why That Matters
- Free AI Governance Maturity Calculator for Modern Enterprises
- Why ISO 42001 Will Be the Next SOC 2
- Managing AI Risk: A Practical Approach to Secure, Responsible, and Effective AI Adoption




