Advanced Persistent Threats’ are top infosecurity challenge for businesses in 2013
Mitigating Advanced Persistent Threats (APT) is going to be a main challange and should be the highest of information security priorities for businesses in 2013, according to governance, risk management and compliance firm IT Governance.
Latest APT threats should be taken into account in an organization risk assessment process and depending on the current vulnerabilities, these threats should be treatetd based on the organization risk appetite. Risk appetite or risk threshold is where an organization draw a line to accept or treat any given risk to an organization.
Alan Calder, Chief Executive of IT Governance, says: “Today, through benign neglect, staff carelessness or insufficient preparation, every business, large and small, is vulnerable to cyberattack. ITG Top 10 identifies the biggest online threats to your business in the coming year and shows how you can tackle these.”
1. Advanced Persistent Threats: APTs refer to coordinated cyberactivities by sophisticated criminals and state-level entities. With the aim of stealing information or compromising information systems, these target governments and corporations which have valuable intellectual property. By their very nature, manufacturing and the high-tech, oil and gas, finance and pharmaceutical industries all come under the greatest threat of attack by APTs. While there’s no single, stand-alone solution, coordinated and integrated preparations can help you rebuff, respond to and recover from possible attacks. Adopting ISO27001, the best practice infosecurity standard, is the most practical way for companies to develop and implement a tailor-made and comprehensive cybersecurity management system to counter the APT threat.
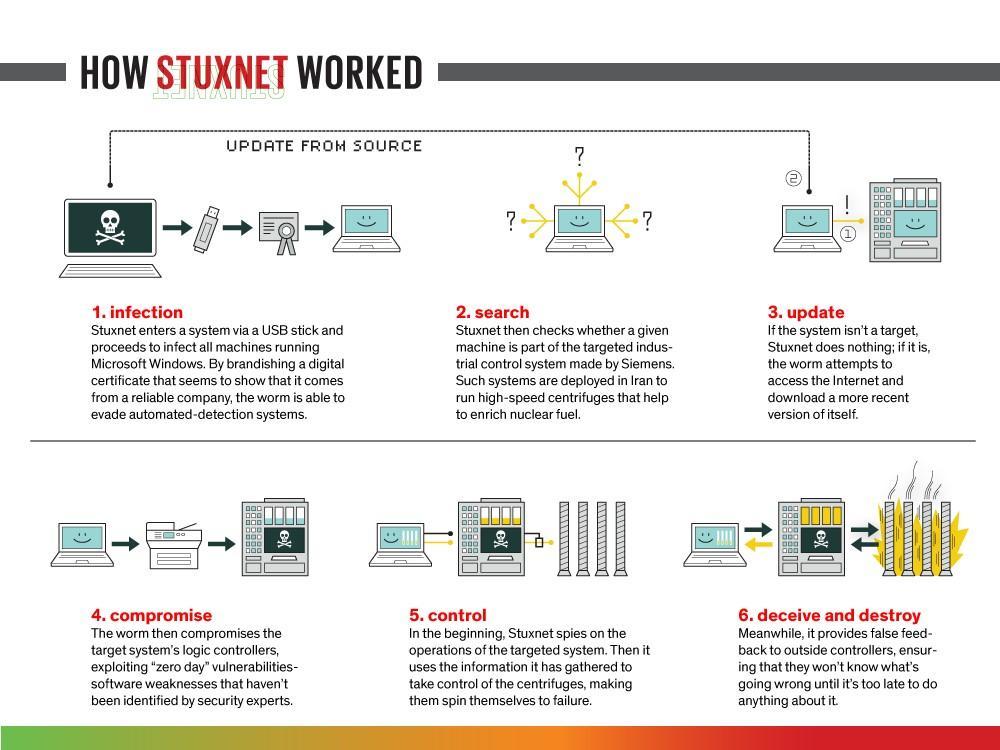
2. Cyberwar: Cyberespionage and cyberterrorism have become a major threat to UK and US governments. In the form of high-profile malware attacks, state-backed entities are seeking commercial advantage against international competitors, as well as preparing for a new front in modern warfare. China is the best known example of a state believed to engage in such activities, so much so that many larger corporations now forbid employees from taking their laptops on business trips into China for fear of data loss. Effective, enterprise-wide cyber-defence must therefore be in place at all levels, to provide strategic, tactical and operational protection, alongside linkages between operational management, operational processes and technical controls.
3. Cybercrime: As opposed to APTs or cyberwar, cybercrime is a threat to every individual and organisation, no matter how small. Cybercriminals exploit modern technologies in order to commit criminal activities, ranging from identity theft to the penetration of online financial services. All businesses should implement an integrated cybersecurity strategy which, among other issues, includes securing your cyber-perimeter to making sure that your staff are trained to recognise and respond to social engineering attacks and follow a well-thought-out social media strategy.
4. Personal data protection: 2012 has seen a slew of data breaches involving the theft of customers’ personal information. This trend will continue unless businesses change their approach to handling personal data. The proposed new EU Data Protection regulation aims to strengthen individual rights and tackle the challenges of globalisation and new technologies. The EU Commission is also putting pressure on businesses to tighten information security measures. Again, the most logical and sensible way to do this is via ISO27001 implementation and certification.
5. Mobile security: USB devices, laptops, tablets and mobile phones make it very easy for employees to transport massive amounts of information out of the door – potentially to your rivals. Also, whenever employees save username and password data onto their mobile devices, they make it exceptionally easy for fraudsters to crack the passwords of a range of applications, thereby increasing cyber risk. All confidential information stored on these devices must be encrypted to avoid data breaches as a result of theft or loss.
6. Data security: Given that many data breaches are due to human error, insider threats play a significant role. Continuous staff awareness training is essential, but companies also need to manage access to data as part of the overall information security management system. For example, restrict access to people with a ‘business need to know’, or set up a unique ID for users which, combined with logging and audits, protects against the ‘insider’.
7. Bring Your Own Device: BYOD policies are becoming the norm at a growing number of both companies and state organisations. Protecting and controlling company data on your staff’s personal mobile devices poses a stiff challenge – best answered by implementing a mobile device management policy.
8. Identity theft: Identity fraud, which involves someone pretending to be somebody else for financial or other gain, is rife. We all need to be aware of ‘phishing’ and ‘pharming’ emails, but we also need to be wary of how we use social media and how much personal information we provide. Antivirus software and spyware removal software alone cannot protect against these attacks. Effort also needs to go into user education to cut exposure to risk.
9. Payment Card Security: Ever-growing numbers of payment cards are being threatened as a result of the migration of payment apps onto mobile devices. Companies should apply regular website security testing, known as ‘vulnerability scanning’, which should be conducted by qualified ethical hackers. It’s also important to regularly apply all relevant patches, and to have a basic understanding of common hacking techniques and new threats and computer viruses.
10. Cloud continuity and security: If you are using a Cloud provider for mission-critical applications and data storage, check the contract carefully. What security policies does the provider have in place? Do they have ISO27001 certification? Evaluate the risks of using a Cloud provider and make them part of your own information security management system.
Tags: Advanced persistent threat, APT, Corporate governance of information technology, Information Security, iso 27001, threat