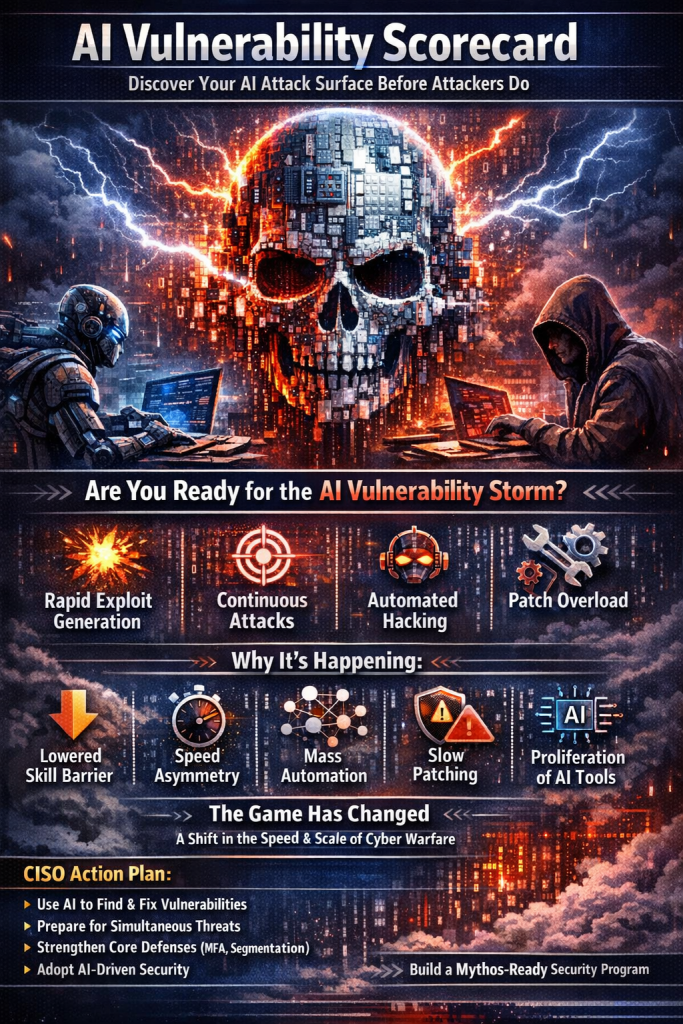
What is an “AI Vulnerability Storm”?
An AI Vulnerability Storm is a rapid, large-scale surge in vulnerability discovery, exploitation, and attack execution driven by advanced AI systems. These systems can autonomously find flaws, generate exploits, and launch attacks faster than organizations can respond.
Why it’s happening (root causes)
- AI lowers the skill barrier → more attackers can find and exploit vulnerabilities
- Speed asymmetry → discovery → exploit cycle has collapsed from weeks to hours
- Automation at scale → thousands of vulnerabilities can be found simultaneously
- Patch limitations → defenders still rely on slower, human-driven processes
- Proliferation of AI tools → offensive capabilities are spreading quickly
Bottom line: This is not just more vulnerabilities—it’s a fundamental shift in the tempo and economics of cyber warfare.
I. Initial Thoughts
AI is dramatically increasing the volume, speed, and sophistication of cyberattacks. While defenders also benefit from AI, attackers gain a stronger advantage because they can automate discovery and exploitation at scale.
The first wave (e.g., Project Glasswing) signals a future where:
- Vulnerabilities are discovered continuously
- Exploits are generated instantly
- Attacks are orchestrated autonomously
Organizations must:
- Rebalance risk models for continuous attack pressure
- Prepare for patch overload and faster remediation cycles
- Strengthen foundational controls like segmentation and MFA
- Use AI internally to keep pace
II. CISO Takeaways
CISOs must shift from reactive security to AI-augmented operations.
Key priorities:
- Use AI to find and fix vulnerabilities before attackers do
- Prepare for multiple simultaneous high-severity incidents
- Update risk metrics to reflect machine-speed threats
- Double down on basic controls (IAM, segmentation, patching)
- Accelerate teams using AI agents and automation
- Plan for burnout and capacity constraints
- Build collective defense partnerships
Core message: You cannot scale humans to match AI—you must scale with AI.
III. Intro to Mythos
AI-driven vulnerability discovery has been evolving, but systems like Mythos represent a step-change in capability:
- Autonomous exploit generation
- Multi-step attack chaining
- Minimal human input required
The key disruption:
- Time-to-exploit has dropped to hours
- Attack capability is becoming widely accessible
This creates a structural imbalance:
- Attackers move faster than patching cycles
- Risk models and processes are now outdated
Organizations that succeed will:
- Adopt AI deeply
- Rebuild processes for speed
- Accept continuous disruption as the new normal
IV. The Mythos-Aligned Security Program
A modern security program must evolve into a continuous, AI-driven resilience system.
Core shifts:
- From periodic defense → continuous operations
- From prevention → containment and recovery
- From manual work → automated workflows
Key realities:
- Patch volumes will surge dramatically
- Risk management becomes less predictable
- Governance must accelerate technology adoption
Strategic focus:
- Build minimum viable resilience
- Measure:
- Cost of exploitation
- Detection speed
- Blast radius containment
Human factor:
- Security teams face:
- Burnout
- Skill anxiety
- Increased workload
But also:
- Opportunity to become AI-augmented operators
Critical insight:
Every security role is evolving into an “AI-enabled builder role.”
V. Board-Level AI Risk Briefing
AI is now a board-level risk and opportunity.
Key message to leadership:
- AI accelerates business—but also accelerates attackers
- Time to major incidents is shrinking rapidly
- Risk must shift from prevention → resilience and recovery
What leadership must support:
- Increased staffing and capacity
- Deployment of AI-driven security tooling
- Faster procurement and governance cycles
- Infrastructure hardening (Zero Trust, segmentation)
- Updated incident response playbooks
90-day focus:
- Scale people
- Deploy AI
- Harden environment
- Accelerate decisions
- Track measurable progress
VI. Recommendations
AI-driven attacks represent a permanent structural shift, not a temporary spike.
What “Mythos-ready” means:
- Build resilient architectures that limit damage
- Discover vulnerabilities before attackers do
- Respond to incidents at scale and speed
- Use AI across the security lifecycle
Strategic takeaway:
This is similar to Y2K-level urgency, but:
- Faster
- More complex
- Continuous (no fixed deadline)
The goal is not perfection—it’s closing the speed gap between attackers and defenders.
Source: Building a Mythos-ready Security Program
Perspective (Practical + Strategic)
1. This is NOT a vulnerability problem — it’s a velocity problem
Traditional security assumes:
- You have time to assess → decide → act
That assumption is now broken.
👉 Strategy shift:
- Optimize for decision speed, not just control coverage
2. Vuln Management → “VulnOps” is inevitable
Quarterly scans and patch cycles are dead.
👉 You need:
- Continuous discovery
- AI triage
- Automated remediation pipelines
This is essentially:
DevSecOps → VulnOps (AI-native)
3. Your biggest gap is NOT tools — it’s operational design
Most orgs fail because:
- Governance is slow
- Teams are siloed
- AI adoption is optional
👉 Fix:
- Mandate AI usage in security workflows
- Redesign processes for machine-speed execution
4. The real risk: security team collapse
The document hints at it, but undersells it.
- Alert fatigue → exponential
- Patch volume → unsustainable
- Talent → limited
👉 If you don’t automate:
You don’t just fall behind—you burn out your team and lose capability
5. New Strategy Blueprint (What I’d implement)
Immediate (0–30 days)
- AI-driven vulnerability scanning (LLM agents)
- Rapid attack surface inventory
- Patch prioritization automation
Mid (30–90 days)
- Build AI-assisted SOC workflows
- Introduce automated incident playbooks
- Implement segmentation + Zero Trust
Strategic (90+ days)
- Stand up VulnOps function
- Create AI Security Scorecard (your product opportunity)
- AI Attack Surface Assessments (huge market gap)
Final Thought
This isn’t just another evolution in cybersecurity.
It’s the moment where:
Security stops being human-scaled and becomes machine-scaled.
Organizations that adapt will operate faster than attackers.
Those that don’t will be permanently behind.
💰 $49 AI Vulnerability Scorecard
Identify Your AI Attack Surface in 15 Minutes
🔍 What It Is
The AI Vulnerability Scorecard is a rapid, expert-designed assessment that identifies where your organization is exposed to AI-driven attacks, agent risks, and API vulnerabilities—before attackers do.
Built for speed, this 20-question assessment maps your security posture against:
- AI attack surface exposure
- LLM / agent risks
- API and application vulnerabilities
- Third-party and supply chain weaknesses
⚠️ Why This Matters (Right Now)
We are in the middle of an AI Vulnerability Storm:
- Vulnerabilities are discovered faster than you can patch
- Exploits are generated in hours, not weeks
- AI agents are expanding your attack surface silently
👉 If you’re using AI tools, APIs, or automation—you already have exposure.
📊 What You Get
✔️ AI Risk Score (0–100)
Clear snapshot of your current exposure
✔️ 10-Page Executive Scorecard (PDF)
- Top vulnerabilities
- Risk heatmap
- Business impact summary
✔️ AI Attack Surface Breakdown
- APIs
- AI agents
- Shadow AI usage
- Third-party dependencies
✔️ Top 5 Immediate Fixes
What to prioritize in the next 30 days
✔️ Mapped to Industry Frameworks
Aligned to:
- ISO 27001
- NIST CSF
- ISO 42001 (AI Governance)
🎯 Who It’s For
- Startups using AI tools or APIs
- SaaS companies and product teams
- Mid-size businesses without a dedicated AI security strategy
- CISOs needing a quick risk snapshot for leadership
⚡ How It Works
- Answer 20 simple questions (10–15 mins)
- Get instant AI risk scoring
- Receive your detailed report within 24 hours
💡 Sample Questions
- Do you use AI agents with access to internal systems?
- Are your APIs protected against automated abuse?
- Do you scan AI-generated code before deployment?
- Can you detect AI-driven attacks in real time?
💵 Pricing
👉 $49 (one-time)
No subscriptions. No complexity. Immediate value.
Identify Your AI Attack Surface in 15 Minutes
After the scorecard, offer:
- $499 Deep-Dive Assessment
- $2,500 AI Security Gap Analysis
- $5K–$15K vCISO / AI Governance Program
🔥 Position
“Most companies don’t know their AI attack surface.
We show you—in 24 hours—for $49.”

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
Is your AI strategy truly audit-ready today?
AI governance is no longer optional. Frameworks like ISO/IEC 42001 AI Management System Standard and regulations such as the EU AI Act are rapidly reshaping compliance expectations for organizations using AI.
DISC InfoSec brings deep expertise across AI, cybersecurity, and regulatory compliance to help you build trust, reduce risk, and stay ahead of evolving mandates—with a proven track record of success.
Ready to lead with confidence? Let’s start the conversation.
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- AI Vulnerability Scorecard: Discover Your AI Attack Surface Before Attackers Do
- API Security in the Age of AI: Why Vulnerability Assessment Is Non-Negotiable
- AI Attack Surface ScoreCard
- AI-Accelerated Offense: Why Security Programs Must Move Now, Not Later
- AI Governance Explained: Accountability, Trust, and Control in the Age of AI




