Dirty Frag: A Second Linux Privilege Escalation Crisis in Two Weeks
Barely a week after the Copy Fail disclosure rattled Linux administrators, the kernel community is contending with another local privilege escalation chain — this one branded “Dirty Frag.” The disclosure landed on May 8, 2026, alongside a working proof-of-concept exploit, and it represents two separate kernel flaws that, when combined, hand an attacker root on most mainstream distributions.
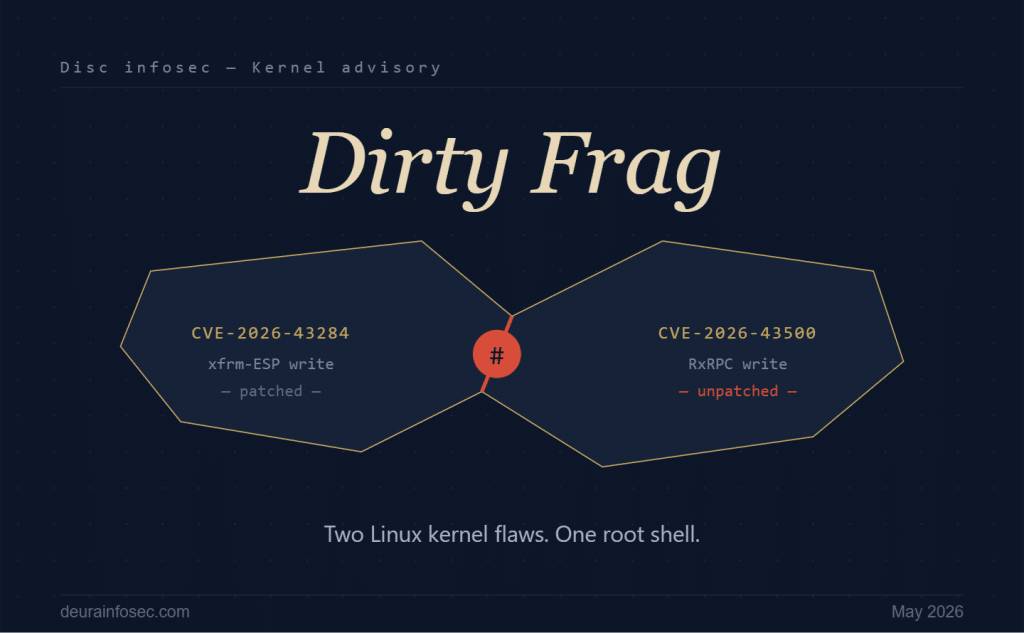
Dirty Frag is technically a pair of vulnerabilities. The first, tracked as CVE-2026-43284 and informally called Copy Fail 2.0, is an xfrm-ESP page-cache write bug in the kernel modules supporting one of the IPsec protocols; this one has already been patched upstream. The second, CVE-2026-43500, is an RxRPC page-cache write flaw affecting the modules that implement support for the AFS distributed file system. As of disclosure, the RxRPC bug remains unpatched.
Both issues were discovered by vulnerability researcher Hyunwoo Kim — known in the community as “V4bel” — who responsibly reported them to Linux kernel maintainers on April 29 and 30, 2026. Kim also submitted candidate patches to the netdev mailing list, the venue where Linux kernel networking changes are reviewed and merged.
On May 7, Kim shared the full technical details and exploit on the closed, members-only mailing list that Linux distributions use to coordinate embargoed security disclosures. Unfortunately, that same day an unrelated third party publicly released the details and exploit code for one of the flaws. With the embargo effectively broken, distribution maintainers cleared Kim to publish the full Dirty Frag write-up.
The most interesting technical observation comes from SANS Internet Storm Center handler Yee Ching Tok, who pointed out that the two sub-vulnerabilities cover one another’s blind spots. Neither the xfrm-ESP nor the RxRPC bug provides a sufficiently reliable primitive for full root escalation on its own. Chained together, however, the exploit reliably elevates to root across a wide swath of distributions — a textbook example of why single-CVE scoring often understates real-world risk.
The footprint is broad. Red Hat Enterprise Linux, AlmaLinux, Debian, Ubuntu, Fedora, Arch Linux, CentOS, CloudLinux, Amazon Linux, and several others have published advisories, with kernel image updates rolling out at varying speeds. Because the third-party leak compressed the timeline, not every distribution had a patched kernel ready when public disclosure occurred, leaving administrators in a familiar window of exposure.
In the meantime, the recommended mitigation is straightforward: blacklist the affected modules to prevent them from loading, or unload them if they are already in use. Operators should be aware that this can disrupt workloads that legitimately depend on IPsec or AFS — though for many enterprise environments, RxRPC in particular sees little real-world use. Once patched kernels are installed and systems rebooted, the temporary mitigations should be reversed.
The Copy Fail precedent is what makes Dirty Frag urgent rather than merely interesting. A PoC for the original Copy Fail (CVE-2026-31431) was published on April 29, and CISA added it to the Known Exploited Vulnerabilities catalog by May 1 — meaning the gap between public exploit and observed in-the-wild use was effectively zero. Tok’s recommendation to treat Copy Fail and Dirty Frag as a combined remediation effort is the right call given their similarity and overlapping mitigation steps.
My perspective
Two things stand out for anyone running a governance or risk program rather than just patching kernels.
First, the disclosure failure here is arguably the bigger story. Coordinated disclosure across the Linux distribution ecosystem is held together by trust and a private mailing list — a single leaker collapsed the entire embargo and pushed Kim into accelerated public disclosure before all distros had patched kernels staged. For ISO 27001 and ISO 42001 practitioners, this is a live case study in supplier risk and incident-coordination dependencies that most risk registers under-model. Your patching SLA is only as good as the upstream coordination process feeding it.
Second, Dirty Frag is another reminder that exploit chaining has quietly become the dominant pattern in serious kernel attacks. Each individual bug is, on its own, an incomplete primitive — neither would warrant emergency patching in isolation under most CVSS-driven prioritization regimes. Combined, they deliver immediate root. Vulnerability management programs that still triage strictly by CVSS base score will continue to miss this class of risk; the practical defense is reducing kernel attack surface (RxRPC is unloaded by default in most enterprise builds for a reason) and shrinking the window between PoC publication and patch deployment. Given Copy Fail’s one-day journey from PoC to KEV, that window is now the metric that actually matters.
The AI Governance Quick-Start: Defensible in 10 Days, Not 4 Quarters
DISC InfoSec is an active ISO 42001 implementer and PECB Authorized Training Partner specializing in AI governance for B2B SaaS and financial services organizations.
AI Vulnerability Scorecard: Discover Your AI Attack Surface Before Attackers Do
Your Shadow AI Problem Has a Name-And Now It Has a Score
Most AI Security Tools Won’t Pass an Audit. Here’s a 15-Minute Way to Find Out.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
- The Bus Factor Just Inverted: Governing the Agents Your Engineers Leave Behind
- ISO 42001 Just Got Easier to Prove: Anthropic Opens Claude to 28 Security and Compliance Tools
- Modern GRC Maturity: Connecting Governance, Risk, Controls, and Technology
- The One Security Book That Got Louder With Every Passing Year
- Microsoft Just Made AI Agent Security a CI/CD Problem — Here’s Why That Matters




