AI in Cybersecurity
Artificial intelligence is reshaping cybersecurity by shifting defenses from reactive protection to proactive and adaptive resilience. Instead of only responding after an breach occurs, AI enables organizations to continuously monitor systems, detect emerging threats, and respond in real time. By combining advanced analytics with machine learning, AI strengthens every layer of cybersecurity—from threat detection to fraud prevention—creating a more intelligent and responsive security posture.
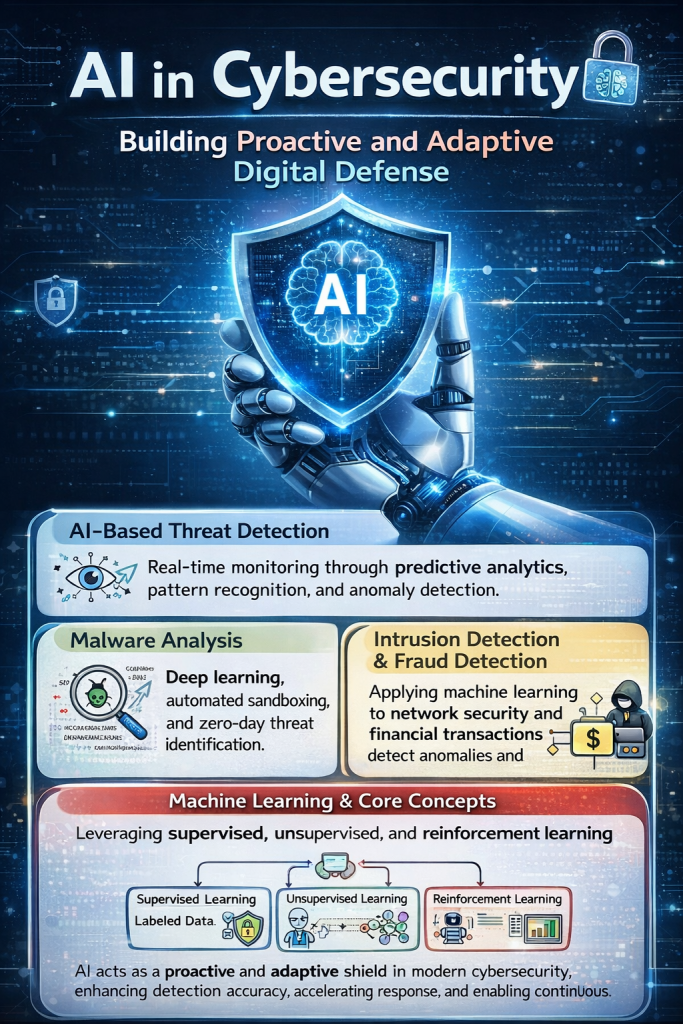
AI-Based Threat Detection
AI-powered threat detection focuses on real-time monitoring and early identification of suspicious behavior. Using predictive analytics, pattern recognition, and behavioral anomaly detection, AI systems learn what “normal” activity looks like and quickly flag deviations. This allows security teams to catch threats that traditional rule-based tools might miss. In my view, AI significantly improves this category by reducing detection time and helping organizations move from reactive incident response to continuous, intelligent threat hunting.
Malware Analysis
In malware analysis, AI uses deep learning and automated sandboxing to examine suspicious files and behaviors without relying solely on known signatures. This enables the identification of previously unseen or zero-day threats. By analyzing how software behaves rather than just matching patterns, AI can uncover sophisticated attacks faster. I see AI as a force multiplier here—it accelerates analysis, reduces manual workload, and improves the ability to defend against rapidly evolving malware.
Intrusion Detection Systems (IDS) and Fraud Detection
AI enhances intrusion detection systems by applying machine learning to network security monitoring. These systems identify unusual traffic patterns and suspicious activities that may indicate an intrusion. Similarly, in fraud detection—especially in financial transactions—AI evaluates transaction behavior, risk scores, and user authentication signals to detect anomalies. From my perspective, AI’s strength in this area lies in its ability to process massive volumes of data and uncover subtle patterns, making defenses more scalable and precise.
Machine Learning Models and Core Concepts
At the core of AI in cybersecurity are machine learning approaches such as supervised learning, unsupervised learning, and reinforcement learning. Supervised learning uses labeled data for classification and prediction tasks, unsupervised learning discovers hidden structures and clusters in unlabeled data, and reinforcement learning improves decisions through trial and feedback. Together, these methods form the technical backbone that enables adaptive and intelligent security systems. I believe understanding these models is essential, as they drive the innovation that allows cybersecurity tools to evolve alongside emerging threats.
Overall, AI acts as a proactive and adaptive shield for modern cybersecurity. By improving detection accuracy, accelerating response times, and enabling continuous learning, AI helps organizations stay ahead of increasingly complex threats and maintain a stronger security posture.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- AI-Accelerated Offense: Why Security Programs Must Move Now, Not Later
- AI Governance Explained: Accountability, Trust, and Control in the Age of AI
- Measure What Matters: Security & AI Readiness Scorecard
- Security Is a People Problem: Culture, Behavior, and Decisions Drive Cyber Resilience
- Security Driven by Business Value: Focus, Prioritize, Protect What Matters Most