Traditional security schemes are incapable of meeting new security challenges of today’s business requirements. Most security architectures are perimeter centric and lack comprehensive internal controls. Organizations which are dependent on firewall security might be overtaxing (asking security mechanism to do more than it can handle). Some of the old firewalls rule set stay intact for years, which might be a liability when the firewall rule set neither represent current business requirements and nor are protecting critical assets appropriately.
“Firewalls are typically managed by a succession of administrators who create their own rules, which then accumulate over a period of years. This creates rule duplication, which can impinge on performance, but also brings risks such as the use default or open passwords.”
The first step in defense in depth is designing a corporate network segmentation policy which describes which departments, application, services and assets should reside on a separate network. Network segmentation will assure that threats are localized with minimal impact on the organization. NIST, ISO27002, and PCI emphasis the importance of network segmentation but does not mandate the requirement. At the same time PCI Standard committee emphasize in new standards that the compliance scope can be significantly minimized by placing all the related assets in the same segment. Network segmentation is not only a common sense in today’s market but also one of the most effective and economical control to implement, simply a great return on investment.
Network segmentation benefits:
o Improve network performance and reduce network congestion
o Contain attacks (viruses, worms, trojans, spam, adware) from overflowing into other networks.
o Improve security by ensuring that nodes are not visible to unauthorized networks. Reduce the size of broadcast domain
Basic idea behind defense in depth is to protect your crown jewel in multiple layers of defense, should one fail, another will provide crucial protection. Another important thing to remember is that we cannot defend everything, so our defense in depth approach should be asset centric rather than perimeter or technology centric. Perform a thorough risk assessment to find out your most important assets and apply the defense in depth approach to protect the confidentiality, integrity and availability of those critical assets. Examples of network segmentation include wireless network, where you place the wireless network users in their own segment behind a firewall with their own rule set. This rule set will help to contain the users on wireless network as well as any potential attacks on the organization. To get to the content of another segment in the network, the wireless users has to pass through all the layers of protection.
Defense in depth diagram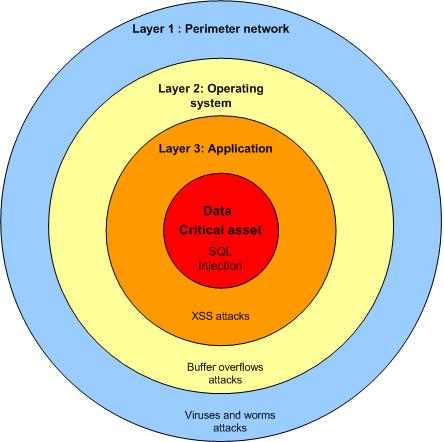
Different attacks will be handled by different layers. In the outer layer 1 will handle most of the network related attacks while the layer 2 will handle most of the script based attacks which target the operating system. Layer 3 will handle most of the application attacks which are complex and only utilized by skilled attackers. Layer 4 is your final frontier where you protect your crown jewel by moving many of the tools and techniques used at the perimeter closer to critical assets.
Related article
• Network segmentation is a common sense
Defense in depth
httpv://www.youtube.com/watch?v=zTJSMjYd9c4&feature=related





April 13th, 2009 8:33 am
Nice info in your site, I will bookmark your blog ASAP
May 14th, 2009 5:50 am
Clear your computer of all the same bugs.
When you are searching for antispyware there is one that you can always depend on, it’s called Search-and-destroy Antispyware. The antispyware solution from Search-and-destroy can provide you with a scan that can find and clear your computer of all the same bugs that the more expensive scans can a much lower price. You can’t beat that, keep your computer running great for less. Visit their site at http://www.Search-and-destroy.com to download this scan and get all the benefits it has to offer. If you’re like me, it will be the best decision you made in a long time.
August 15th, 2010 10:57 pm
[…] Network Segmentation -via the DISC InfoSec Blog https://blog.deurainfosec.com/defense-in-depth-and-network-segmentation […]
January 19th, 2025 10:55 am
… [Trackback]
[…] Find More Informations here: blog.deurainfosec.com/defense-in-depth-and-network-segmentation/ […]