Risk Management Vocabulary: A Comprehensive Overview
Risk management is a structured discipline that enables organizations to identify, assess, and address potential threats before they cause harm. At its broadest level, Total Risk Management (TRM) provides a comprehensive, organization-wide approach to handling all categories of risk, ensuring no threat goes unaddressed. Supporting this is Enterprise Risk Management (ERM), a framework that systematically identifies, assesses, and mitigates risks across every business unit, helping organizations align their risk appetite with strategic objectives. Together, these two approaches form the backbone of a mature risk culture.
To prepare for worst-case scenarios, organizations rely on a Business Continuity Plan (BCP) — a documented strategy for maintaining critical operations during disruptions such as cyberattacks, natural disasters, or system failures. This is further reinforced by ISO 22301, the international standard for business continuity, which provides certified guidelines ensuring that continuity plans are robust, tested, and auditable. On the governance side, the Committee of Sponsoring Organizations (COSO) framework establishes best practices for internal control and risk management, helping organizations build accountability and reduce fraud or operational failures. Complementing this is Operational Risk Management (ORM), which focuses specifically on risks arising from internal processes, human error, and system failures — areas commonly exploited in cybersecurity incidents.
Effective risk management also depends on the right standards and frameworks. ISO 31000 is the globally recognized standard offering universal guidelines for risk management practices, applicable across industries and risk types. The Risk Management Framework (RMF) provides a specific set of criteria and structured steps — particularly relevant in government and regulated industries — for selecting, implementing, and monitoring security controls. These frameworks are complemented by Risk and Control Self-Assessment (RCSA), a process by which teams internally evaluate the effectiveness of their controls and identify gaps in risk exposure, fostering a proactive rather than reactive security posture.
Once risks are identified, they must be documented and tracked. The Risk Register (RR) serves as a centralized record of all identified risks, their owners, likelihood, impact, and treatment status — making it an essential tool for accountability and audit readiness. Risk Assessment (RA) is the analytical process of identifying and evaluating those risks, determining which threats pose the greatest danger based on probability and potential damage. To stay ahead of emerging threats, organizations monitor Key Risk Indicators (KRIs) — quantifiable metrics that signal when risk levels are approaching critical thresholds, enabling early intervention before a risk materializes into a breach or loss.
When risks are identified and evaluated, organizations must act on them through Risk Treatment (RT) — the application of methods such as mitigation, transfer, avoidance, or acceptance to reduce risk to an acceptable level. The effectiveness of these treatments is sustained through Risk Monitoring (RM), which involves the continuous tracking and reviewing of risks to ensure controls remain effective as the threat landscape evolves. Tying everything together, the Risk Management Framework (RMF) ensures that all these processes operate cohesively within a structured governance model.
In summary, these terms collectively define the lifecycle of risk management — from establishing enterprise-wide strategy, to identifying and assessing threats, implementing treatments, and continuously monitoring outcomes. For security professionals, understanding and applying this vocabulary is foundational to building resilient organizations that can withstand, adapt to, and recover from an ever-changing threat environment.
My Perspective on the Risk Management Vocabulary Post
Overall, this is a solid foundational reference — the kind of content that bridges the gap between technical security practitioners and business stakeholders. Here are my honest thoughts:
What It Does Well
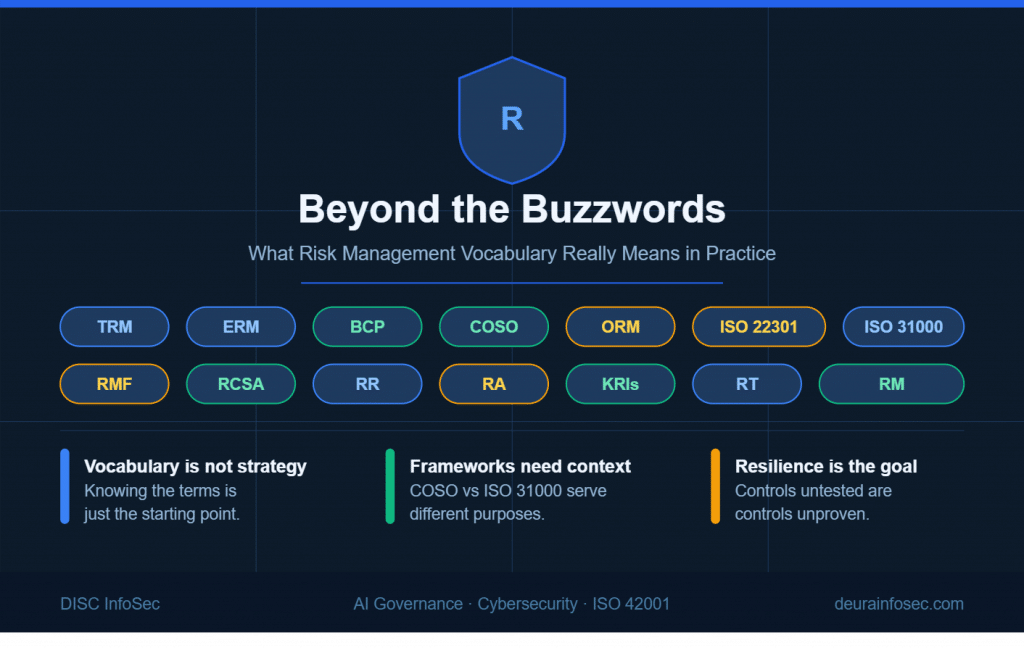
The post succeeds in making risk management accessible. By condensing complex frameworks like COSO, ISO 31000, and RMF into digestible definitions, it lowers the barrier for entry-level professionals or non-technical executives who need to speak the language of risk without necessarily being deep practitioners. The visual format of the original infographic also makes it easy to reference quickly — something useful in training or awareness campaigns.
Where It Falls Short
Honestly, the definitions are surface-level at best. Listing what an acronym stands for is not the same as understanding how it functions operationally. For example:
- Defining a Risk Register as simply “a centralized record” understates its role as a living governance document that drives accountability, audit trails, and board-level reporting.
- KRIs are described as metrics that “identify potential risks,” but their real power lies in being leading indicators — they tell you a risk is developing, not just that it exists. That distinction is critical in a security operations context.
- The post treats COSO and ISO 31000 as parallel concepts, when in practice they serve different purposes — COSO is governance and internal control-oriented, while ISO 31000 is a pure risk management process standard. Conflating them can create confusion during actual framework implementation.
The Missing Pieces
From a cybersecurity and AI governance standpoint — which is increasingly where risk management is headed — the post notably omits several critical concepts:
- Threat Modeling — arguably more actionable than a generic risk assessment in security contexts
- Residual Risk vs. Inherent Risk — a distinction that matters enormously when presenting risk posture to boards or auditors
- Risk Appetite and Risk Tolerance — without these, organizations have no objective baseline for deciding what level of risk is acceptable
- Third-Party and Supply Chain Risk — one of the most significant and undermanaged risk vectors today, especially relevant for organizations handling sensitive data
- AI-specific risk concepts like algorithmic bias, model drift, and data provenance risk — none of which map cleanly onto traditional frameworks like COSO or ISO 31000 without deliberate adaptation
The Bigger Picture
What this post represents is risk management vocabulary without risk management thinking. Knowing what “Risk Treatment” means is useful. Understanding when to accept risk versus transfer it versus mitigate it — and being able to defend that decision to a regulator or client — is what actually builds organizational resilience.
The vocabulary is the starting point, not the destination. For organizations genuinely serious about risk — particularly those in regulated industries like financial services, healthcare, or AI-driven businesses — these terms need to be lived and operationalized, not just defined. A risk register that nobody updates is just a document. A BCP that has never been tested is just a plan on paper.
Bottom line: It’s a useful primer, but practitioners should treat it as a glossary, not a playbook. The real skill in risk management lies in the judgment calls made between the definitions.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- The Adversary Already Adopted AI. Did Your Defense?
- When the Most Safety-Focused AI Company Misses the Basics: A Governance Wake-Up Call
- Claude Security Goes Public: A Turning Point for AI-Driven DevSecOps—and a New Governance Challenge
- The AI Oversight Gap: When Confidence Outpaces Control
- The AI Governance Quick-Start: Defensible in 10 Days, Not 4 Quarters




