Yesterday was the first Patch Tuesday of 2022, with more than 100 security bugs fixed.
We wrote up an overview of the updates, as we do every month, over on our sister site news.sophos.com: First Patch Tuesday of 2022 repairs 102 bugs.
For better or for worse, one update has caught the media’s attention more than any other, namely
This bug was one of seven of this month’s security holes that could lead to remote code execution (RCE), the sort of bug that means someone outside your network could trick a computer inside your network into running some sort of program without asking for permission first.
No need to log in up front; no pop-up warning at the other end; no Are you sure (Y/N)? questions.
Just give the order, and the malware runs.
That’s the theory, anyway.
RCE bugs considered wormable
One thing to remember about most RCE vulnerabilities is that if you can attack someone else’s computer from outside and instruct it to run a malicious program of your choice…
…then it’s possible, perhaps even probable, that you could tell it to run the very same program that you yourself just used to launch your own attack.
In other words, you might be able to use the vulnerability to locate and infect Victim 1 with malicious program W that instructs Victim 1 to locate and infect Victim 2 with malicious program W that instructs Vicitm 2 to locate Victim 3… and so on, perhaps even ad infinitum.
In an attack like this, we give the program W a special name: we call it a worm.
Worms form a proper subset of a type of malicious software (or malware for short) known generally as computer viruses, the overarching term for self-replicating malware of any sort.
This means that most RCE bugs are, in theory at least, wormable, meaning that they could potentially be exploited to initiate a chain of automatic, self-spreading and self-sustaining malware infections.
The reasoning here is obvious: if an RCE bug allows you to run an arbitrary program of your own choice, such as CALC.EXE or NOTEPAD, then it almost certainly allows you to run a specific program of your choice, such as a worm.
Some bugs are more wormable than others…
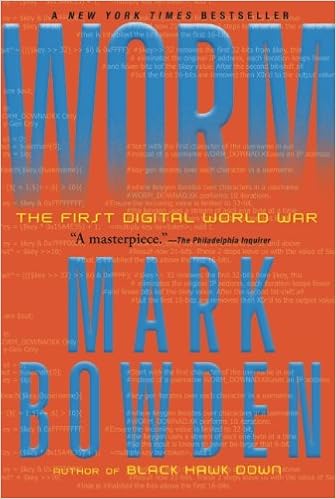
The Conficker worm infected its first computer in November 2008 and within a month had infiltrated 1.5 million computers in 195 countries. Banks, telecommunications companies, and critical government networks (including the British Parliament and the French and German military) were infected. No one had ever seen anything like it. By January 2009 the worm lay hidden in at least eight million computers and the botnet of linked computers that it had created was big enough that an attack might crash the world.