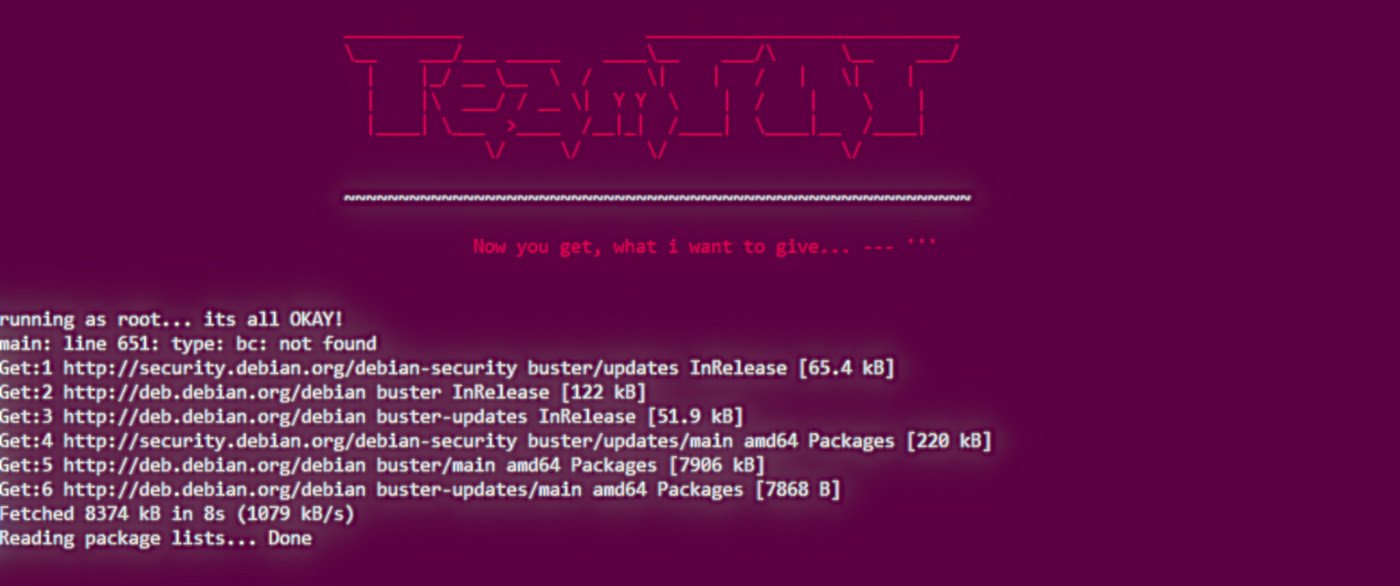
In a recent attack, cybercrime group TeamTNT relied on a legitimate tool to avoid deploying malicious code on compromised cloud infrastructure and still have a good grip on it.
Source: Hackers use legit tool to take over Docker, Kubernetes platforms
Misusing tool of the trade
Analyzing the attack, researchers at Intezer discovered that TeamTNT installed Weave Scope open-source tool to gain full control of the victim’s cloud infrastructure.
According to them, this may be the first time a legitimate third-party tool is abused to play the part of a backdoor in a cloud environment, also indicating the evolution of this particular group.
Weave Scope integrates seamlessly with Docker, Kubernetes, and the Distributed Cloud Operating System (DC/OS), and AWS Elastic Compute Cloud (ECS). It provides a complete map of processes, containers, and hosts on the server and control over installed applications.
“The attackers install this tool in order to map the cloud environment of their victim and execute system commands without deploying malicious code on the server,” Intezer notes in a report today.
Download a Security Risk Assessment Steps paper!
Security Risk assessment Quiz – Find Out How Your security risk assessment Stands Up!
DISC InfoSec 🔒 securing the business 🔒 via latest InfoSec titles
Subscribe to DISC InfoSec blog by Email
👉 Download a Virtual CISO (#vCISO) and Security Advisory Fact Sheet & Cybersecurity Cheat Sheet