The MITRE ATT&CK framework is fundamentally about understanding the blind spots within your environment. It provides a structured, real-world playbook of how attackers actually operate—far beyond theoretical security models. Instead of guessing what threats might look like, it helps organizations see how adversaries move, persist, and exploit weaknesses across systems.
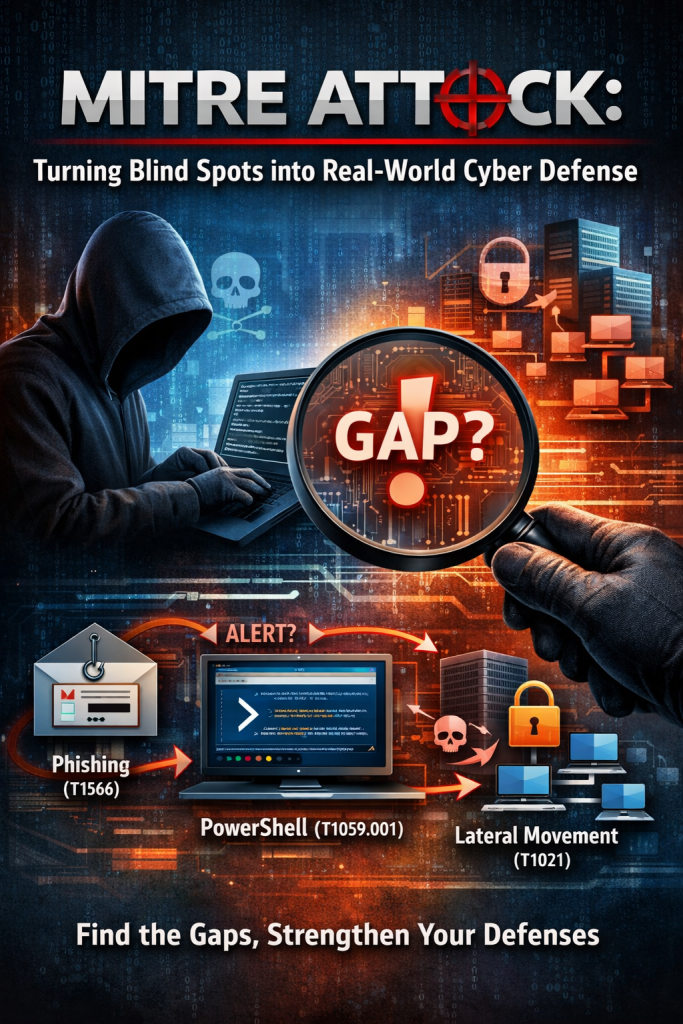
At its core, ATT&CK exposes gaps in your defenses. For every listed technique, the key question becomes: Could this happen in my environment without triggering an alert? If the answer is even “maybe,” that uncertainty signals a control weakness. This approach shifts security teams from compliance-driven checkbox exercises to a more honest evaluation of detection and response capabilities.
For example, when you detect suspicious PowerShell activity tied to T1059.001 PowerShell, the framework guides your investigation. You don’t just look at the isolated event—you analyze the full attack chain. What came before, such as phishing via T1566 Phishing? What might follow, like credential dumping using T1003 Credential Dumping or lateral movement through T1021 Remote Services? This interconnected view allows defenders to anticipate attacker behavior rather than simply react to alerts.
By mapping real adversary techniques against your actual security controls, ATT&CK turns abstract security strategies into practical defense mechanisms. It forces alignment between what you think you can detect and what you actually can detect in real-world scenarios.
Perspective:
Most organizations today claim ATT&CK alignment, but in practice, they only map controls on paper—this is compliance theater. The real value comes from operationalizing it through testing (e.g., purple teaming or adversary simulation). For instance, a company may have endpoint detection tools in place and believe they can detect PowerShell abuse. But when a simulated attacker runs obfuscated scripts, no alerts fire. That’s the gap ATT&CK is meant to uncover.
A practical example: imagine a mid-sized SaaS company that has email security and endpoint protection deployed. On paper, phishing (T1566) and credential dumping (T1003) are “covered.” However, during a red team exercise, a phishing email bypasses filters, a user executes a macro, and PowerShell is used to pull credentials—without detection. The organization realizes their logging is incomplete and alerting rules are too weak. That insight—not the framework itself—is where ATT&CK delivers value.
Bottom line: ATT&CK isn’t about documentation—it’s about visibility. Once you truly understand where you’re blind, you can finally start seeing—and defending—clearly.
OWASP Top 10 Web Application Security Risks ↔ MITRE ATT&CK Mapping
MITRE ATT&CK v18: A Modular Leap Toward Smarter, Traceable Threat Detection
Why Security Leaders Should Prioritize the MITRE ATT&CK Evaluation
Threat Hunting with MITRE ATT&CK
MITRE ATT&CK project leader on why the framework remains vital for cybersecurity pros
How to Apply MITRE ATT&CK to Your Organization
‘DECIDER’ AN OPEN-SOURCE TOOL THAT HELPS TO GENERATE MITRE ATT&CK MAPPING REPORTS
The Top 10 Most Prevalent MITRE ATT&CK Techniques used by Adversaries
Top 10 free MITRE ATT&CK tools and resources
Cybersecurity – Attack and Defense Strategies
blog post coming out later this week with more about these changes (watch this space!), but in the meantime Cat Self’s ATT&CKcon 6.0 talk covered many of the details.

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- MITRE ATT&CK: Turning Blind Spots into Real-World Cyber Defense
- When AI Hacks Faster Than Humans: The Coming Collapse of Traditional Cybersecurity Value
- SOC 2 Isn’t Enough: Moving Beyond Compliance Theater to Real Risk Management
- When AI Becomes the Attack Surface: Lessons from the McKinsey Lilli Incident
- Why Every Company Needs a CISO (or at Least vCISO-Level Leadership)




