WHY CHANGE THE MAC ADDRESS?
The MAC address is (should be) unique to each network interface. By the way, if the device has several network interfaces, then each of them has its own MAC address. For example, laptops have at least two network interfaces: wired and Wi-Fi – each of them has an MAC address. Desktop computers are usually the same. When we talk about “changing MAC addresses”, we need to understand that there are several of these addresses. By the way, each port has its own unique MAC address, if the device supports wireless networks, then each wireless interface (2.4 GHz and 5 GHz) also has its own MAC address.
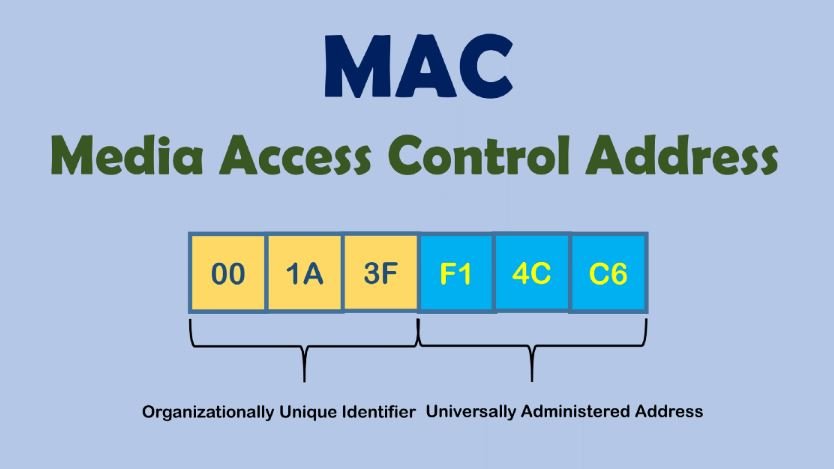
So, since the MAC address must be unique, it allows you to uniquely identify the network device. And since this network device is part of your computer, this allows you to uniquely identify your computer. Moreover, the MAC address (also called a hardware, physical address) does not change when the operating system changes.
In short, the replacement of the MAC address is needed so that it is not possible to track and identify the device by the MAC address. But there is a more important reason (than paranoia) to learn about MAC addresses and about methods from substitution, or prohibiting changes in your system. Based on MAC addresses, user identification can be performed when connected via the Intercepting Portal. A few words about the Intercepting Portal. Captive Portal). This is a way to force the user to comply with certain conditions for providing Internet access. You can most often encounter examples of Intercepting Portals in public places that provide Internet access services via Wi-Fi to an indefinite circle of people, but who want to identify the user and / or allow access only to persons with credentials. For example, at the airport you may need to confirm your phone number via SMS to access the free Wi-Fi network. The hotel will provide you with a username and password for accessing the Internet via Wi-Fi – this ensures that only hotel customers can use Wi-Fi services.
Due to the features of the Intercepting Portal, user identification is based on MAC addresses. And starting with NetworkManager 1.4.0 (a popular program for managing network connections on Linux), an automatic MAC-address spoofing is now present. And in case of incorrect settings, you may encounter an Internet access problem running through the Intercepting Portal. There are also problems with customized filtering by MAC on the router.
Well, for pentesting experts , of course, there are reasons to change the MAC address: for example, to pretend to be another user, and take advantage of its open access to the magical world of the Internet, or to increase anonymity.
Who can see my MAC address?
The MAC address is used to transfer data on a local network. That is, it is not transmitted when connecting to websites and when accessing the global network. Although there are exceptions: some vulnerabilities allow a person who is not on your local network to find out your MAC address.
If you connect to the router via the local network, then the router knows your MAC address, but if you open the site on the Internet, the site owner cannot find out your MAC address.
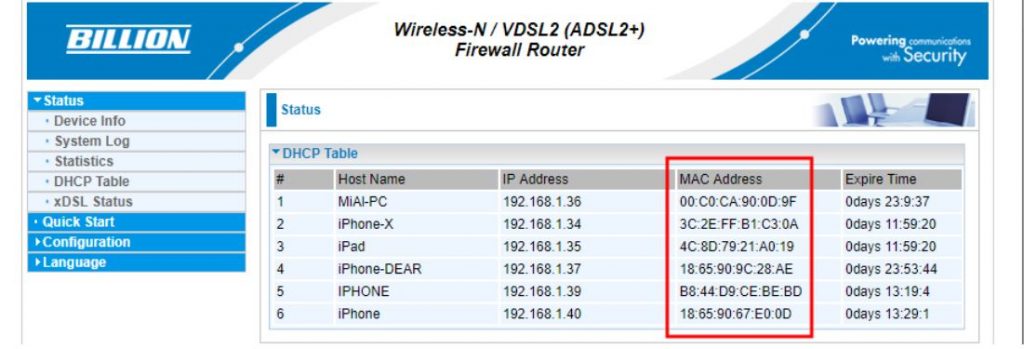
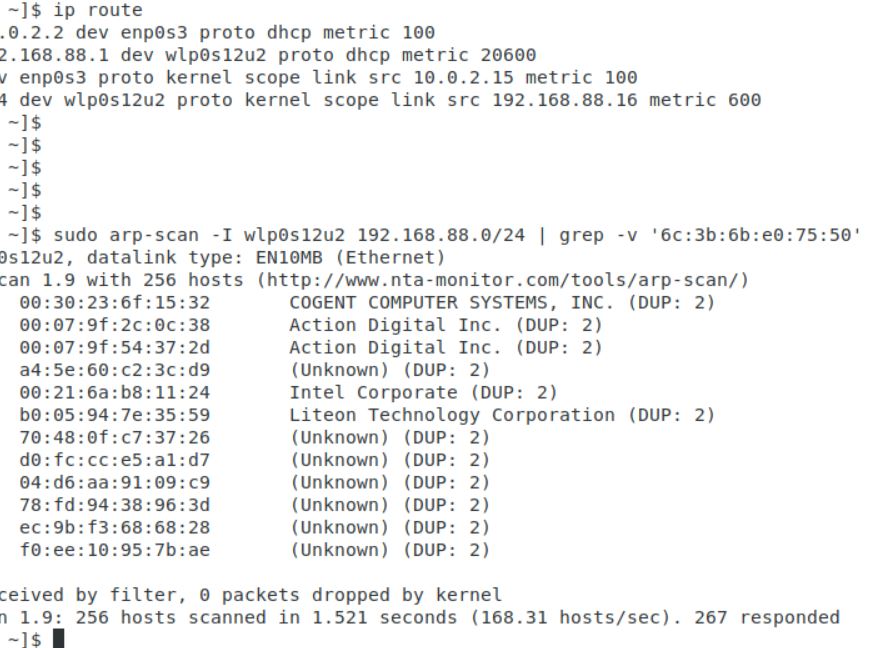
All devices located on the local network can see each other’s MAC addresses (there are many scanners that can get this data). An example of a local network scan made using arp-scan. A slightly different situation with wireless network interfaces. If you are connected to an access point (router), then all the rules of the local network work: the router and other devices can find out your MAC address. But also any person who is within the reach of your Wi-Fi signal (from the phone, laptop) can find out your MAC address.
SPOOFING MAC ADDRESSES IN NETWORKMANAGER
NetworkManager may reassign MAC installed by other programs
Starting with NetworkManager 1.4.0, this program supports MAC spoofing, and has many different options.
So that we can understand them, we need to understand some concepts
First, network adapters are :
- wired (ethernet);
- wireless (wifi).
For each group, MAC rules are customized separately.
Secondly, a wireless adapter can be in two states:
- scanning (search, not connected to the network) – is set using the property wifi.scan-rand-mac-address, default set to yes, which means that during scanning it sets an arbitrary MAC address. Another acceptable value is no;
- connected to the network – installed using the property wifi.cloned-mac-address, the default value is preserve.
For wired interface (installed by property ethernet.cloned-mac-address) and the wireless interface in the connection state (installed by the property wifi.cloned-mac-address) the following values are available (regimes):
- clearly specified MAC address (t.e. you can write the desired value that will be assigned to the network interface)
- permanent: use the MAC address sewn into the device
- preserve: do not change the device’s MAC address after activation (for example, if the MAC has been changed by another program, the current address will be used)
- random: generate a random variable for each connection
- stable: similar to random – i.e. for each connection to generate a random variable, NO when connecting to the same network, the same value will be generated
- NULL / not installed: This is the default value that allows you to roll back to global settings by default. If global settings are not set, then NetworkManager rolls back to the value preserve.
If you are trying to change the MAC in other ways and you are failing, it is entirely possible that NetworkManager, which changes the MAC in its own rules, is to blame. Since most Linux distributions with a NetworkManager graphical interface are installed and running by default, to solve your problem, you must first understand how NetworkManager works and by what rules.
NETWORKMANAGER CONFIGURATION FILES
NetworkManager settings, including settings related to MAC, can be done in a file /etc/NetworkManager/NetworkManager.conf or adding an additional file with the extension . . . .conf to the directory /etc/NetworkManager/conf.d
The second option is highly recommended, since when updating NetworkManager usually replaces the main one . . . . . . . . . .conf file and if you made changes to /etc/NetworkManager/NetworkManager.conf, then the settings you made will be overwritten.
HOW TO MAKE KALI LINUX REPLACE WITH EACH CONNECTION
If you want the MAC address to be replaced with each connection, but the same MAC is used in the connection to the same network, then the file /etc/NetworkManager/conf.d/mac.conf:
| 1 | sudo gedit /etc/NetworkManager/conf.d/mac.conf |
Add lines :
| 123 | [connection]ethernet.cloned-mac-address=stablewifi.cloned-mac-address=stable |
Lines with ethernet.cloned-mac-address & wifi.cloned-mac-address can be added individually or together.
Check the current values :
| 1 | ip link |
Restart the service :
| 1 | sudo systemctl restart NetworkManager |
We will make connections to wired and wireless networks. Now check the values of MAC again
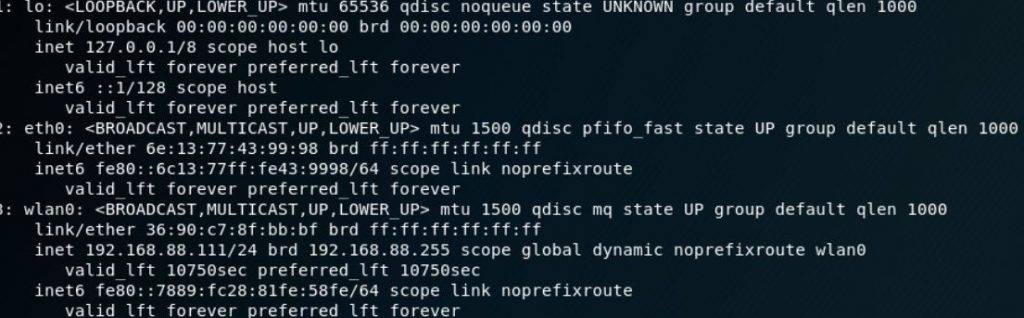
As you can see, MAC is replaced for both the wired and wireless interfaces.
As already mentioned, the same addresses will be generated for the same networks, if you want different MACs each time even for the same networks, then the lines should look like this:
| 123 | [connection]ethernet.cloned-mac-address=randomwifi.cloned-mac-address=random |
HOW TO CONFIGURE AUTOMATIC MAC SPOOFING IN UBUNTU AND LINUX MINT
Ubuntu and Linux Mint use NetworkManager versions that support automatic MAC configuration. However, if you connect a Wi-Fi card to Ubuntu or Linux Mint, you will see a real MAC. This is due to the fact that in the file /etc/NetworkManager/NetworkManager.conf indicated not to spoof :
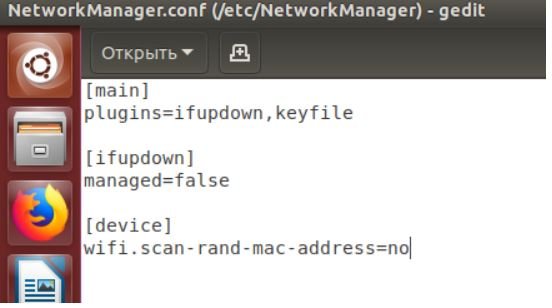
To change this, open the file :
| 1 | sudo gedit /etc/NetworkManager/NetworkManager.conf |
And delete the lines :
| 12 | [device]wifi.scan-rand-mac-address=no |
or comment on them to make it happen :
| 12 | #[device]#wifi.scan-rand-mac-address=no |
or change no on yes:
| 12 | [device]wifi.scan-rand-mac-address=yes |
And restart NetworkManager :
| 1 | sudo systemctl restart NetworkManager |
Similarly, you can add lines to replace MAC (these settings create a new address for each connection, but when connecting to the same networks, the same address is used):
| 123 | [connection]ethernet.cloned-mac-address=stablewifi.cloned-mac-address=stable |
OTHER WAYS TO CHANGE THE MAC ADDRESS
CHANGE MAC USING IPROUTE2
We will use the program ip, which is included in the package iproute2.
Let’s start by checking the current MAC address with the command :
| 1 | ip link show interface_name |
Where Interface_name – This is the name of a particular network interface that you want to see. If you do not know the name, or want to see all the interfaces, then the command can be started like this :
| 1 | ip link show |
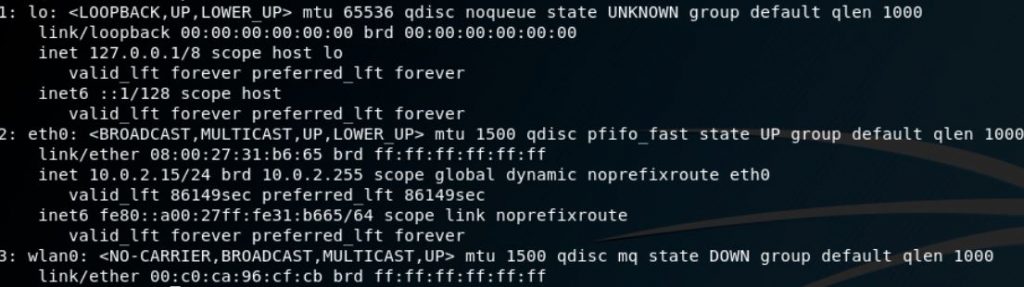
At the moment, we are interested in the part that follows after link / ether“and represents a 6-byte number. It will look something like this :
| 1 | link/ether 00:c0:ca:96:cf:cb |
The first step for spoofing MAC addresses is to transfer the interface to a state down. This is done by the team
| 1 | sudo ip link set dev interface_name down |
Where Interface_name replaces the real name. In my case, this wlan0, then the real team looks like this:
| 1 | sudo ip link set dev wlan0 down |
Next, we go directly to the MAC spoofing. You can use any hexadecimal value, but some networks may be configured not to assign IP addresses to customers whose MAC address does not match any known vendor (producer). In these cases, so that you can successfully connect to the network, use the MAC prefix of any real vendor (first three bytes) and use arbitrary values for the next three bytes.
To change the MAC, we need to run the command :
| 1 | sudo ip link set dev interface_name address XX:XX:XX:XX:XX:XX |
Where XX: XX: XX: XX: XX: XX – This is the desired new MAC .
For example, I want to set the hardware address EC: 9B: F3: 68: 68: 28 for my adapter, then the team looks like this:
| 1 | sudo ip link set dev wlan0 address EC:9B:F3:68:68:28 |
In the last step, we return the interface to the state up. This can be done by a team of the form :
| 1 | sudo ip link set dev interface_name up |
For my system, a real team:
| 1 | sudo ip link set dev wlan0 up |
If you want to check if the MAC is really changed, just run the command again:
| 1 | ip link show interface_name |
Value after “link / ether“should be the one you installed.
CHANGE MAC WITH MACCHANGER
Another method uses macchanger (also known as the GNU MAC Changer). This program offers various functions, such as changing the address so that it matches a particular manufacturer, or its complete randomization.
Set macchanger – it is usually present in official repositories, and in Kali Linux it is installed by default.
At the time of the change of the MAC, the device should not be used (be connected in any way, or have status up). To transfer the interface to a state down:
| 1 | sudo ip link set dev interface_name down |
For spoofing, you need to specify the name of the interface, and replace in each next command wlan0 in the name of the interface that you want to change the MAC.
To find out the values of MAC, execute the command with the option -s:
| 1 | sudo macchanger -s wlan0 |
Something like:
| 12 | Current MAC: 00:c0:ca:96:cf:cb (ALFA, INC.)Permanent MAC: 00:c0:ca:96:cf:cb (ALFA, INC.) |
The “Current MAC” line means the address at the moment, and “Permanent MAC” means a constant (real) address.
For spoofing the MAC address to a completely arbitrary address (option -r):
| 1 | sudo macchanger -r wlan0 |
About the following will be displayed :
| 123 | Current MAC: 00:c0:ca:96:cf:cb (ALFA, INC.)Permanent MAC: 00:c0:ca:96:cf:cb (ALFA, INC.)New MAC: be:f7:5a:e7:12:c2 (unknown) |
The first two lines are already explained, the line “New MAC” means a new address.
For randomization, only bytes that determine the uniqueness of the device, the current MAC address (i.e.e. if you check the MAC address, it will register as from the same vendor) run the command (option -e):
| 1 | sudo macchanger -e wlan0 |
To set the MAC address to a specific value, execute (option -m):
| 1 | sudo macchanger -m XX:XX:XX:XX:XX:XX wlan0 |
Here XX: XX: XX: XX: XX: XX – This is the MAC you want to change to.
Finally, to return the MAC address to the original, constant value prescribed in the iron (option -p):
| 1 | sudo macchanger -p wlan0 |
CONCLUSION
NetworkManager currently provides a wealth of MAC spoofing capabilities, including a change to a random address, or to a specific one. A feature of NetworkManager is the separation of “scanning” and “connected” modes, i.e. you may not see that the settings made have already entered into force until you connect to any network.
If after the change of MAC you have problems with connecting (you cannot connect to networks – wired or wireless), this means that there is a ban on connecting with MAC from an unknown vendor (producer). In this case, you need to use the first three octets (bytes) of any real vendor, the remaining three octets can be arbitrary says pentesting experts.
The Art of Mac Malware: The Guide to Analyzing Malicious Software




