BYOD security controls for mobility
These days smart phones certainly add additional risk to Bring Your Own Device (BYOD) to office. Like it or not Bring Your Own Device is a growing trend at all scales and levels. An important thing to understand is that today’s user like and prefer to use their own devices and applications at work.
As we know some organizations have pretty strict policies around Bring Your Own Device. When it comes to BYOD, it should be addressed in structured manner considering information security policies and procedures. Utilize IT Governance framework to align the with business goals. In this regard, an organization may have to amend some of their own policies to allow BYOD instead of making user to circumvent the potential existing policies. Security professional must reassess their current Bring Your Own Device policies to find new balance which work for users and also match the organization business objectives and security needs.
Organizations of all sizes are dealing with the – mobility – before they even have had adequate time to manage the risks: How do we secure the systems and data accessed broadly by employees’ mobile devices?
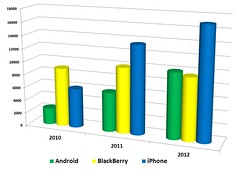
- State of Security – Which mobile platforms will organizations support in 2013, and how do they rate their state of mobile security? Perform a thorugh risk assessment with mobility in scope
- Policy – What formal policies do organizations have in place for concerns such as inventory, mobile device/application management and data/device encryption? Update your policies and procedures to cover mobility
- Controls – What security controls are in place to manage and secure identity and access management, content and the use of third-party applications? Implement mobility controls based on risk assessment
- Metrics – How do organizations measure the tangible business results of mobile initiatives, including cost-savings and improved productivity? Metrics measures improvement and effectiveness of controls. Best way to show you are maintaining and improving mobility controls over time to auditor and business suite.
Considerations for BYOD Policies, Controls and Metrics
• Address the allowed and supported mobile platform for user community
• Address stolen and misplaced devices to avoid data loss
• Address remote access to corporate resources which should be secure using (TLS, SSL)
• Also address exceptions in remote access where application does not support TLS or SSL
• Address the use Implicit authorization instead of traditional explicit authorization
• Implicit authorization uses SIM based Extensive Auth Protocol (EAP)
• Implicit authorization is less risky than explicit authorization in BYOD
Related articles









March 11th, 2013 9:40 pm
[…] BYOD security measures for mobility […]