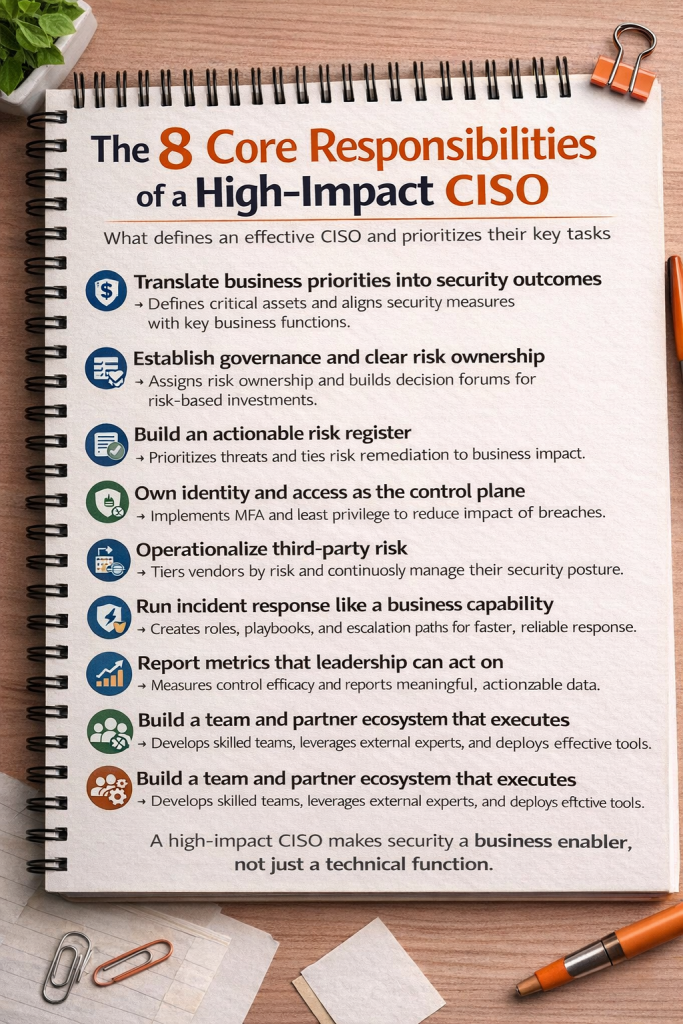
1. Translate business priorities into security outcomes
A CISO’s first responsibility is to convert business goals into concrete security protections. This means understanding what assets are mission-critical and identifying scenarios that could seriously damage revenue, operations, safety, or regulatory standing. Security becomes a business enabler rather than a technical afterthought.
Priority tasks include identifying crown-jewel assets, mapping them to business processes, and modeling high-impact loss scenarios. The CISO should then align controls and investments directly with business objectives—protecting uptime, customer trust, and compliance exposure. Regular executive discussions ensure security strategy evolves with business priorities.
2. Establish governance and clear risk ownership
Effective governance ensures that cybersecurity risk is shared and owned across the organization, not isolated within IT. The CISO builds a structure where executives understand and accept accountability for risks tied to their domains.
Key priorities are defining risk ownership across departments, creating formal decision forums where risk and investment are reviewed, and embedding cybersecurity into enterprise governance processes. Clear escalation paths and accountability frameworks help transform security from advisory guidance into organizational action.
3. Build an actionable risk register
An actionable risk register turns abstract threats into prioritized, manageable work. It allows leadership to see which risks matter most and what actions will reduce them.
The CISO should prioritize evaluating risks based on likelihood and business impact, ranking them transparently, and linking each item to a funded remediation roadmap. The focus is on measurable risk reduction rather than isolated projects, ensuring investments produce visible resilience gains.
4. Own identity and access as the control plane
Identity and access management acts as the organization’s primary defensive layer. By controlling who can access what, the CISO limits the damage of inevitable breaches.
Priority actions include enforcing multi-factor authentication, implementing least-privilege access, and maintaining disciplined joiner-mover-leaver processes. Continuous access reviews and lifecycle automation reduce attack surfaces and shrink the blast radius of compromised accounts.
5. Operationalize third-party risk
Third-party relationships extend the organization’s attack surface. The CISO must treat vendor risk as an ongoing operational function, not a one-time assessment.
Critical tasks include tiering vendors by risk level, embedding security requirements into contracts, and establishing onboarding and offboarding controls. Continuous monitoring and reassessment ensure vendor security posture keeps pace with changing threats and business dependencies.
6. Run incident response like a business capability
Incident response should function as a rehearsed organizational capability rather than an ad hoc reaction. It protects operational continuity and reputation.
The CISO prioritizes defining clear roles, developing tested playbooks, and conducting tabletop exercises with executive leadership. Structured escalation and communication processes enable faster containment, minimize business disruption, and accelerate recovery.
7. Report metrics that leadership can act on
Security metrics must inform decisions, not just decorate dashboards. The CISO translates operational data into insights leadership can use.
Priority work includes tracking actionable indicators such as detection and containment times, patch cycles, control coverage, and vendor exposure. Reporting should demonstrate trends and measurable improvements in security posture, supporting informed investment and governance decisions.
8. Build a team and partner ecosystem that executes
A strong execution engine requires skilled people and effective partnerships. The CISO creates an operating model that turns strategy into results.
Key priorities are defining clear roles and responsibilities, strengthening engineering and operational capabilities, and selecting tools that demonstrably improve detection and response. External partners and platforms should complement internal strengths and scale execution.
Perspective:
A modern CISO’s value lies in building a system where security is embedded in business decision-making. When the role is reduced to technical firefighting, organizations lose strategic leverage. A high-impact CISO establishes governance, accountability, and measurable outcomes—transforming security from reactive theater into proactive business resilience.
#Cybersecurity #CISO #RiskManagement

InfoSec services | InfoSec books | Follow our blog | DISC llc is listed on The vCISO Directory | ISO 27k Chat bot | Comprehensive vCISO Services | ISMS Services | AIMS Services | Security Risk Assessment Services | Mergers and Acquisition Security
At DISC InfoSec, we help organizations navigate this landscape by aligning AI risk management, governance, security, and compliance into a single, practical roadmap. Whether you are experimenting with AI or deploying it at scale, we help you choose and operationalize the right frameworks to reduce risk and build trust. Learn more at DISC InfoSec.
- MITRE ATT&CK: Turning Blind Spots into Real-World Cyber Defense
- When AI Hacks Faster Than Humans: The Coming Collapse of Traditional Cybersecurity Value
- SOC 2 Isn’t Enough: Moving Beyond Compliance Theater to Real Risk Management
- When AI Becomes the Attack Surface: Lessons from the McKinsey Lilli Incident
- Why Every Company Needs a CISO (or at Least vCISO-Level Leadership)






