Information Security Breaches: Avoidance and Treatment based on ISO27001
If you are running a business, you learn to expect the unexpected. Even if you have taken all the right precautions, your company might still find itself confronted with an information security breach. How would your business cope then?
There are lots of books that will tell you what to do to prevent an information security breach. This book is different. It tells you what you have to do if a security breach occurs.
Security breaches sometimes occur because computers containing sensitive information are not returned to their owners. NATO laptops have been spotted in flea markets, and US government computers were put up for sale on Ebay. Security breaches may also be the result of data theft. A bad apple in your company may be tempted to sell your confidential data to a rival firm.
If something happens, your company needs to be ready to take prompt and decisive action to resolve the issue. This book tells you the plans and procedures you need to put in place to tackle an information security breach should it occur. In particular, the book gives you clear guidance on how to treat an information security breach in accordance with ISO27001.
If a breach occurs, the evidence needs to be secured professionally. You need to know the rules on evidence gathering, and you need to be capable of isolating the suspect laptops right from the start. If you want your company to respond rapidly to an information security breach, you need to make sure that the responsibilities and roles in your company are clearly defined.
Benefits to business include:
Recover faster
An information security breach can have crippling consequences. However, with the right emergency measures in place, you will be able to recover quickly from the incident and resume normal operations.
Preserve customer confidence
An information security breach can result in loss of records and disruption to service. This can do serious damage to your relationship with your customers. It is vital for you to be prepared for an information security breach, so that if it ever happens you can preserve customer confidence.
Assist the investigation
Uncovering the root causes of an information security breach requires detective work. If an information security breach occurs, the investigators will need to be able to identify the problem. You can help them to do that by keeping proper records.
Catch the criminals
In the event of data theft, you will want to be in a position to act promptly and decisively. So you should set up an incident management system. This will mean that in the event of data theft, the police will have a greater chance of getting hold of the incriminating evidence they need to secure a conviction.
As Michael Krausz warns, “It is the prudence of management that decides on a company’s fate once a serious incident occurs, not only the size.”
What others are saying about this book …
‘…I recommend this pocket guide to anyone implementing ISO27001, and indeed to anyone who is concerned about the risks of security breaches, and who wants to know how best to prepare their organization for the unpleasant events that are bound to happen from time to time…’
Willi Kraml, Global Information Security Officer
‘…The author thankfully narrows down some important vocabulary to a practical usage in real life situations. The book gives what it advertises: a quick pocket guide to avoidance and treatment of security breaches with references to ISO27001…’
Sascha-A Beyer, Senior Manager
‘…Michael Krausz has created a valuable tool for both professional as well as less knowledgeable persons in respect to the ISO27001 Standard… Written in plain English, this handbook is easy to follow even by a novice in the Information Technology Field. Therefore “Information Secuirty Breaches” is a must within the ‘tool box’ of anyone who deals with IT issues on an every-day basis…’
Werner Preining, Interpool Security Ltd
‘Michael Krauz did a good job. His pocket guide is small enough to be read in only a few minutes, yet is packed full of valuable information presented in a structured way. The case studies especially help to understand the topic. As former CIO of a large company I can recommend it.’
Christian H Leeb, Holistic Business Development
About the author: Michael Krausz is an IT expert and experienced professional investigator. He has investigated over a hundred cases of information security breaches. Many of these cases have concerned forms of white-collar crime. Michael Krausz studied physics, computer science and law at the University of Technology in Vienna, and at Vienna and Webster universities. He has delivered over 5000 hours of professional and academic training and has provided services in eleven countries to date.
Don’t let your organisation fall victim to a security incident … download your copy today!
Information Security Breaches: Avoidance and Treatment based on ISO27001
Tags: information security brecahes, iso 27001, Michael Krausz, NATO laptops, Security Breach











![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=a3168449-b81f-45c3-8b23-5ed61d6b8845)
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=75ca6076-5285-4eaa-9251-01afd6576cbb)
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=1119f164-7e48-4ad2-b112-d80cd3808a1d)
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=7df2ef1d-242f-4110-8903-59f134349e57)
 The goal is to address the organization security needs as a whole, and assess how different departments and business functions are addressing the current business security requirements. The CMMI has five levels and evaluate security controls based on levels, not on specific objectives. Each level provides the basis for the next level where it is not possible to get to the next level without complying with previous level.
The goal is to address the organization security needs as a whole, and assess how different departments and business functions are addressing the current business security requirements. The CMMI has five levels and evaluate security controls based on levels, not on specific objectives. Each level provides the basis for the next level where it is not possible to get to the next level without complying with previous level. 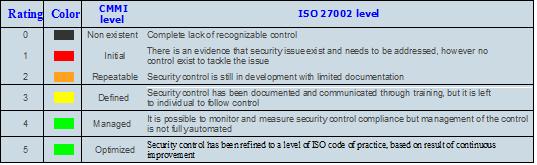


![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=2590b94c-4c68-4b01-a367-028d2bdde031)


