
Phishing and Countermeasures: Understanding the Increasing Problem of Electronic Identity Theft
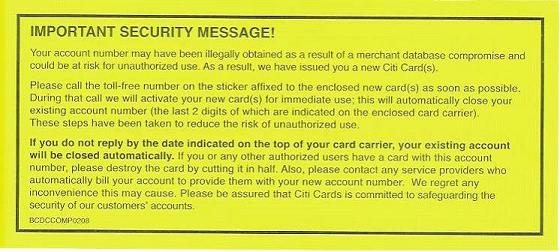
Phishing is a practice of luring unsuspecting Internet users to a fake Web site by using authentic-looking email with the real organization’s logo, in an attempt to steal passwords, financial or personal information. In daily life people advise to retrace your steps when you lose something. The question is how you retrace your steps on cyberspace where some uber hackers know how to erase their footsteps to avoid detection. It is difficult to find phishers in cyberspace, and jurisdictional issues make it even harder to prosecute them. Then there is an issue of trust that phishers dupe people to believe that their web site is not fraudulent to collect personal/financial information.
Below is an example of sophisticated phishing attack
Link to phishing email
It looks very legit, with all the correct data, logos, graphics and signatures.
One giveaway: the TSA rule change has nothing to do with rental cars. It only affects your airline ticket vs your photo ID (drivers license, passport, whatever.)
To verify that this is bad stuff, right click on the links. You get “http://click.avis.com/r/GDYHH9/16HY8/6V5I29/M93XX4/YCCJP/A5/h”, which looks OK on first glance, since it says “avis.com”. But myAvis should not send me to “click.avis.com”. I also noticed that all the other links send you to the same location.
The clincher (here comes the geeky stuff:)
To open a terminal window, press the “Windows key” and the letter “R”.
You will see the “Run Dialog Box”. Type “cmd”, and press “OK
Open a terminal window and run nslookup:
C:\> nslookup
> www.avis.com <<< check IP address of the real AVIS web site
Server: 4.2.2.3
Address: 4.2.2.3#53
Non-authoritative answer:
www.avis.com canonical name = www.avis.com.edgekey.net.
www.avis.com.edgekey.net canonical name = e2088.c.akamaiedge.net.
Name: e2088.c.akamaiedge.net
Address: 96.6.248.168 <<< get IP address of the real AVIS web site
> click.avis.com <<< now check IP address of the bogus AVIS web site
Server: 4.2.2.3
Address: 4.2.2.3#53
Non-authoritative answer:
click.avis.com canonical name = avis.ed10.net.
Name: avis.ed10.net <<< not the same domain as the real AVIS domain
Address: 208.94.20.19 <<< note IP address is in a totally different sub net
> 208.94.20.19 <<< now do a reverse lookup of the fake AVIS web site
Server: 4.2.2.3
Address: 4.2.2.3#53
** server can't find 19.20.94.208.in-addr.arpa.: NXDOMAIN <<< it should give you the web site name
> avis.ed10.net <<< bogus AVIS web site name
Server: 4.2.2.3
Address: 4.2.2.3#53
Non-authoritative answer:
Name: avis.ed10.net
Address: 208.94.20.19
> 208.94.20.19
Moral of the story: be very careful with links in emails and web pages. To check the authenticity of the link, right click on the link, copy that to a text file and take a good look.
Don’t click on the phisher’s email. Type URL into web browser yourself
——————————————————————————————————————————–
In the table below are the 12 threats to your online identity which can be manipulated in phishing scams, and possible countermeasures to protect your personal and financial information. Some threats are inadequate or no security controls in place. The last row of the table is a monitoring control to identify the warning signs of identity theft.
——————————————————————————————————————————–
[TABLE=7]
Download a free guide for the following cloud computing solutions
Hosted email solution
Hosted email archiving
Hosted web monitoring
Hosted online backup


![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=f0daa4e0-f026-4af4-8494-36325d4cff42)

![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=c0f0d90e-bec6-4fb0-8cc1-da10b6d29d91)
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=28dcae72-914e-4823-9632-cd34145194b7)


